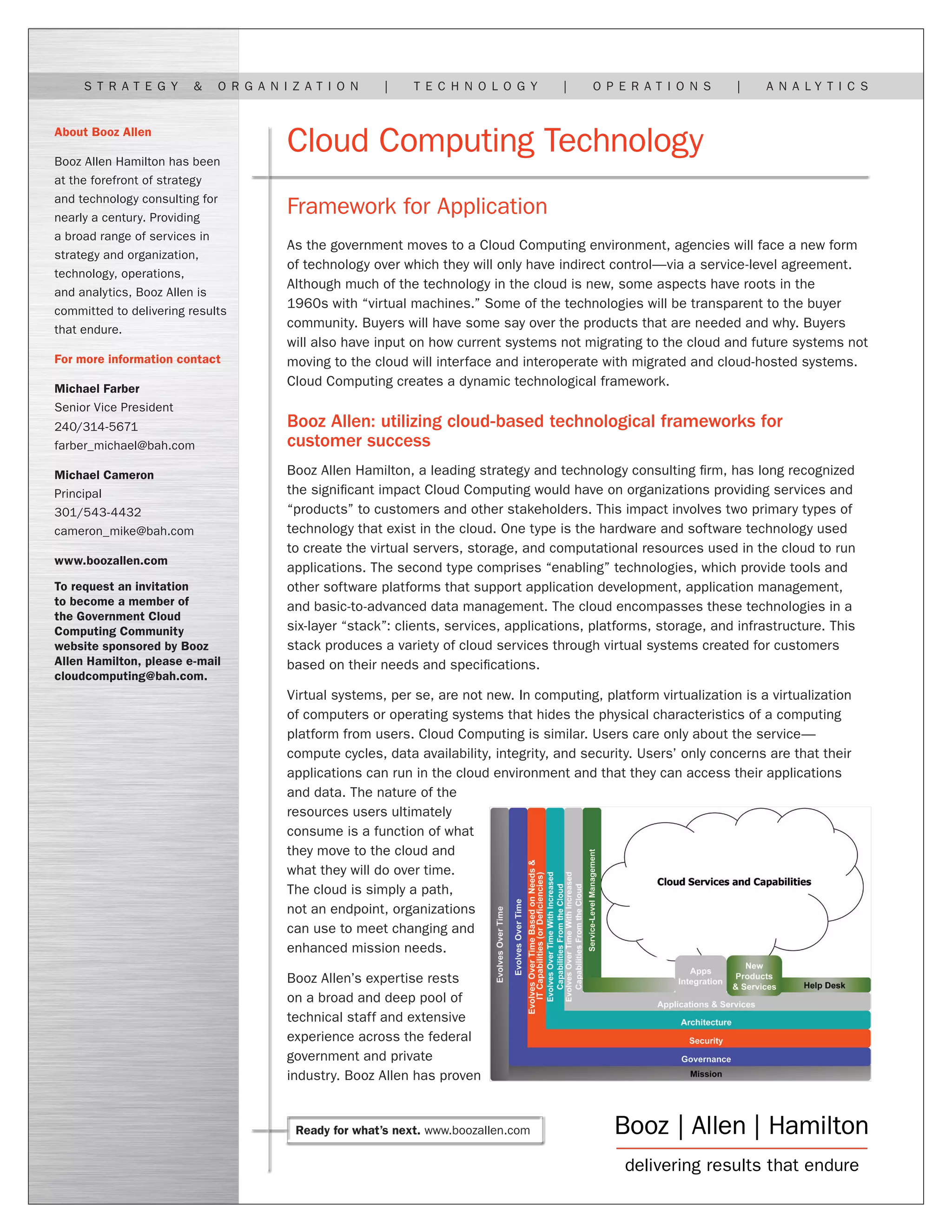
Booz Allen Hamilton highlights the impact of cloud computing on government agencies, explaining that organizations will primarily interact with cloud technologies through service-level agreements. The document outlines the technology stack of cloud computing and emphasizes Booz Allen's expertise in assisting clients with their cloud migration and operational needs across various layers and types of clouds. It stresses the importance of a structured approach in transitioning to cloud-based environments to meet evolving requirements and enhance organizational capabilities.