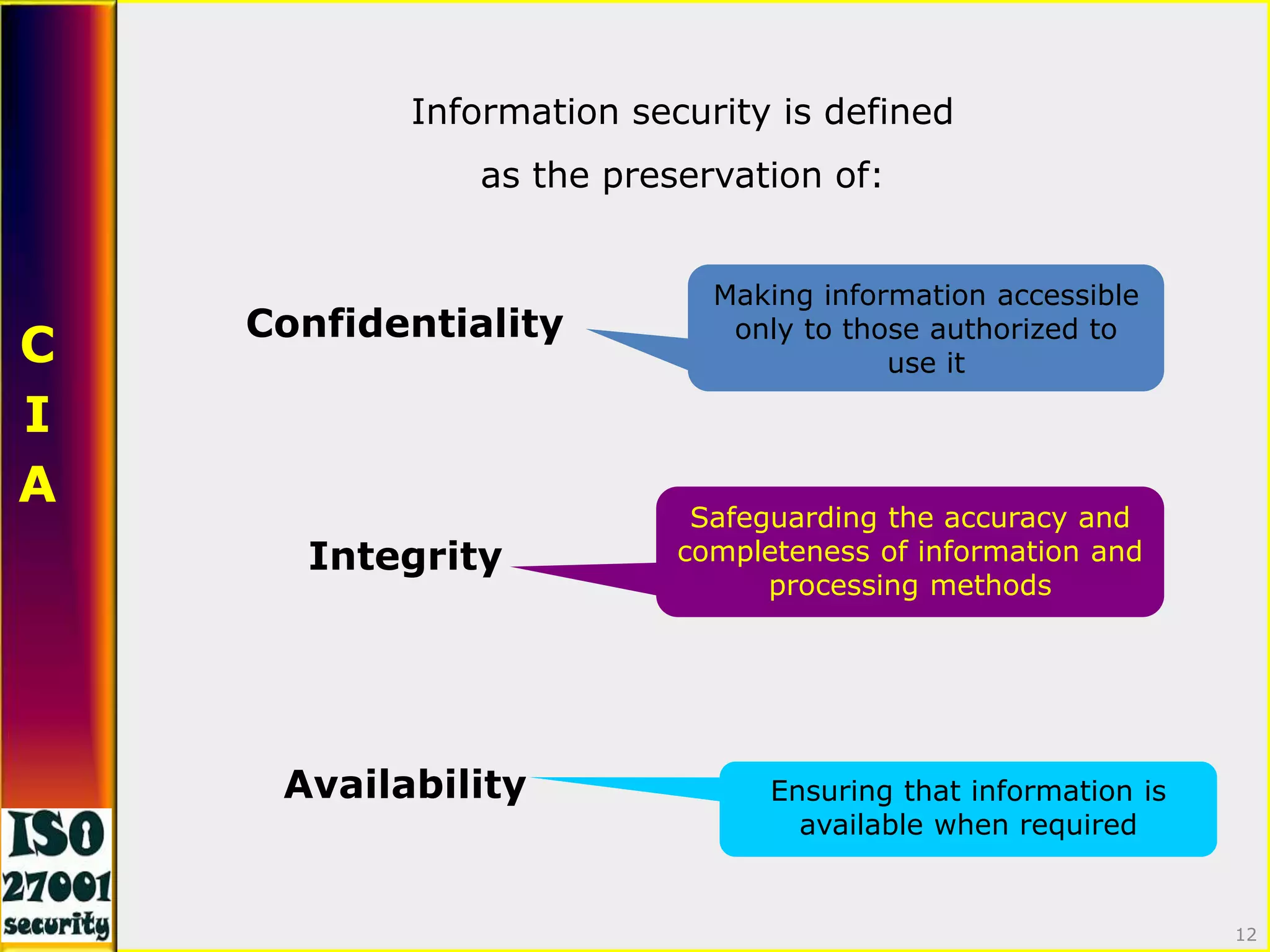
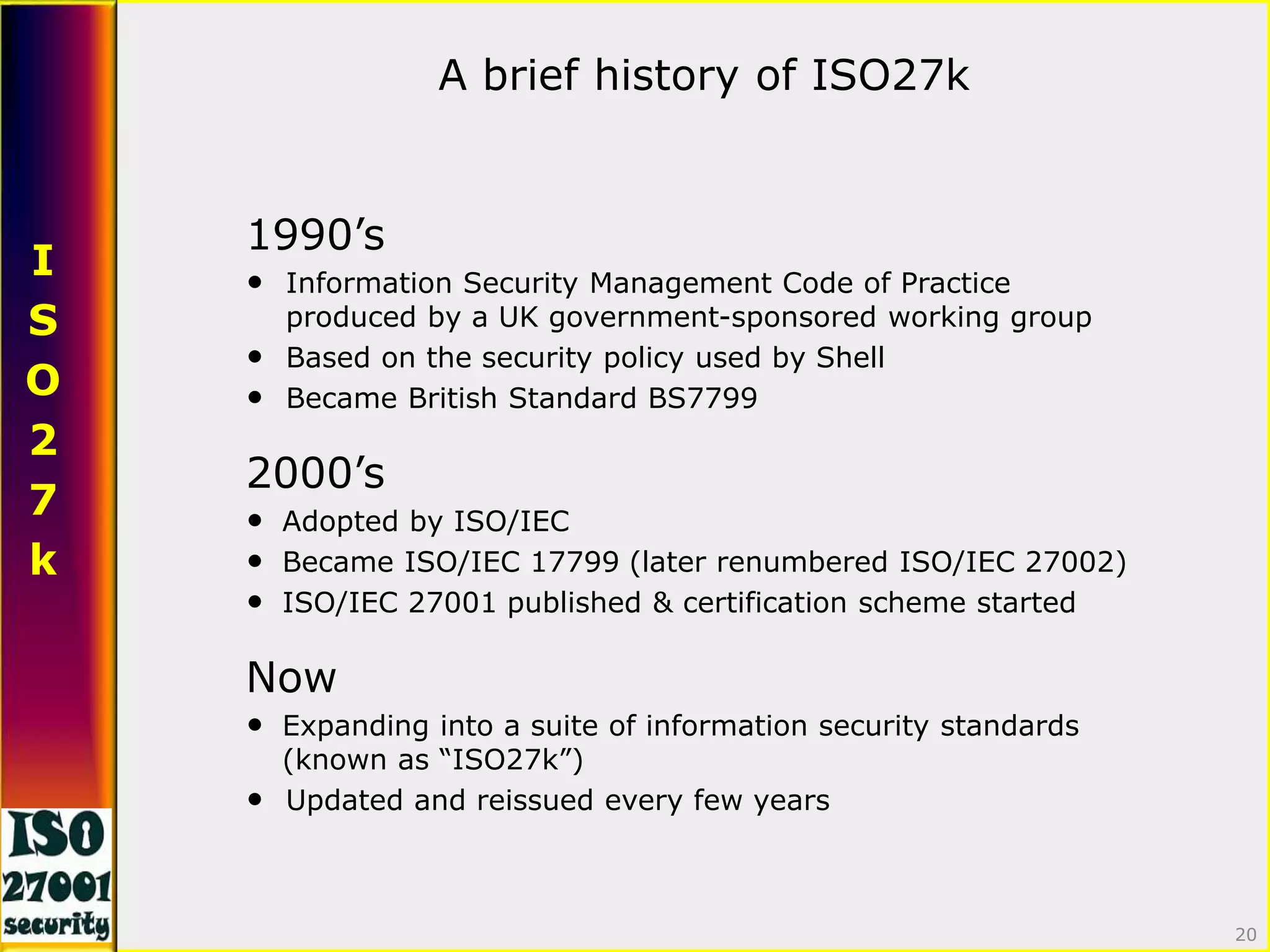
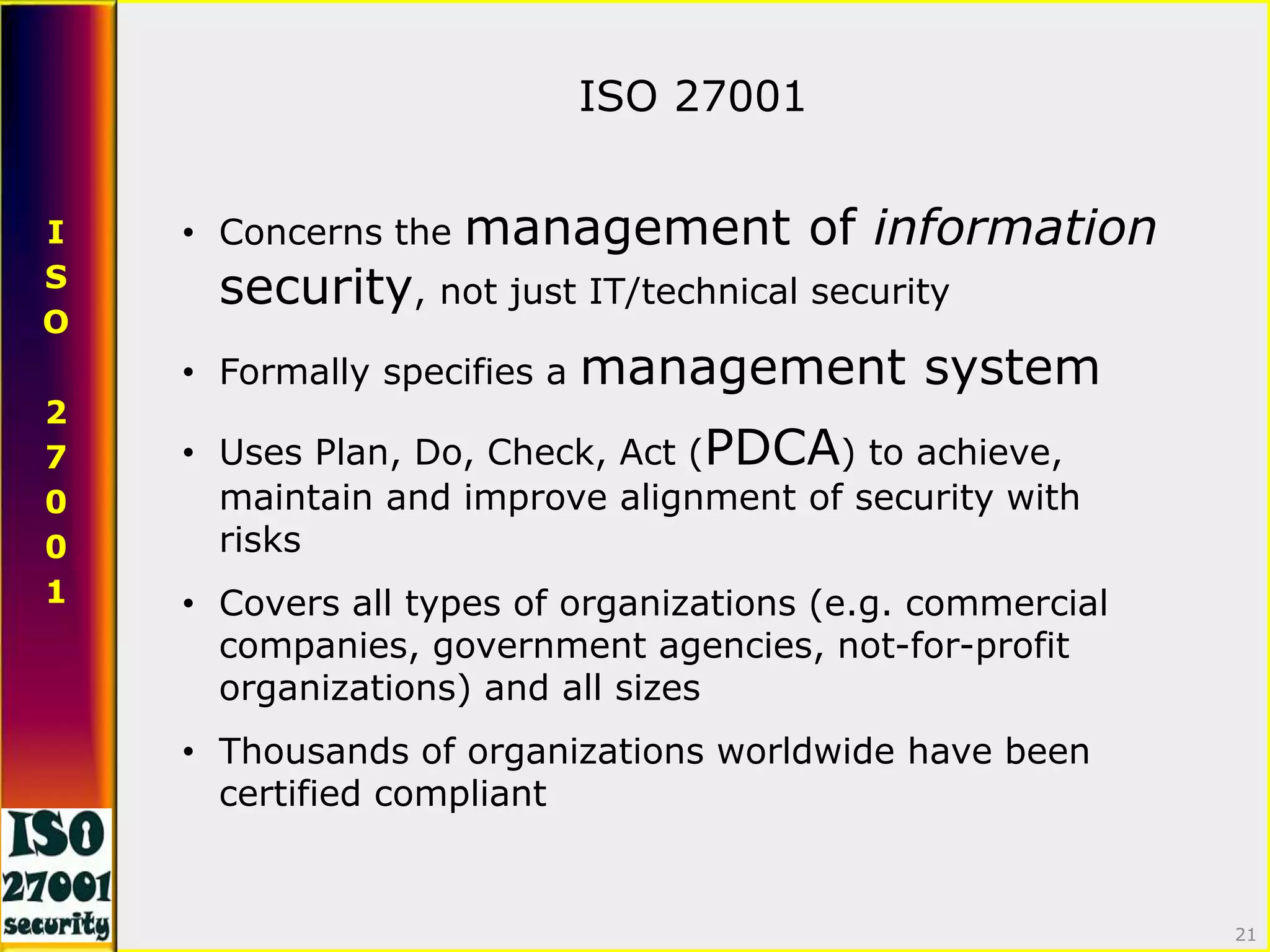
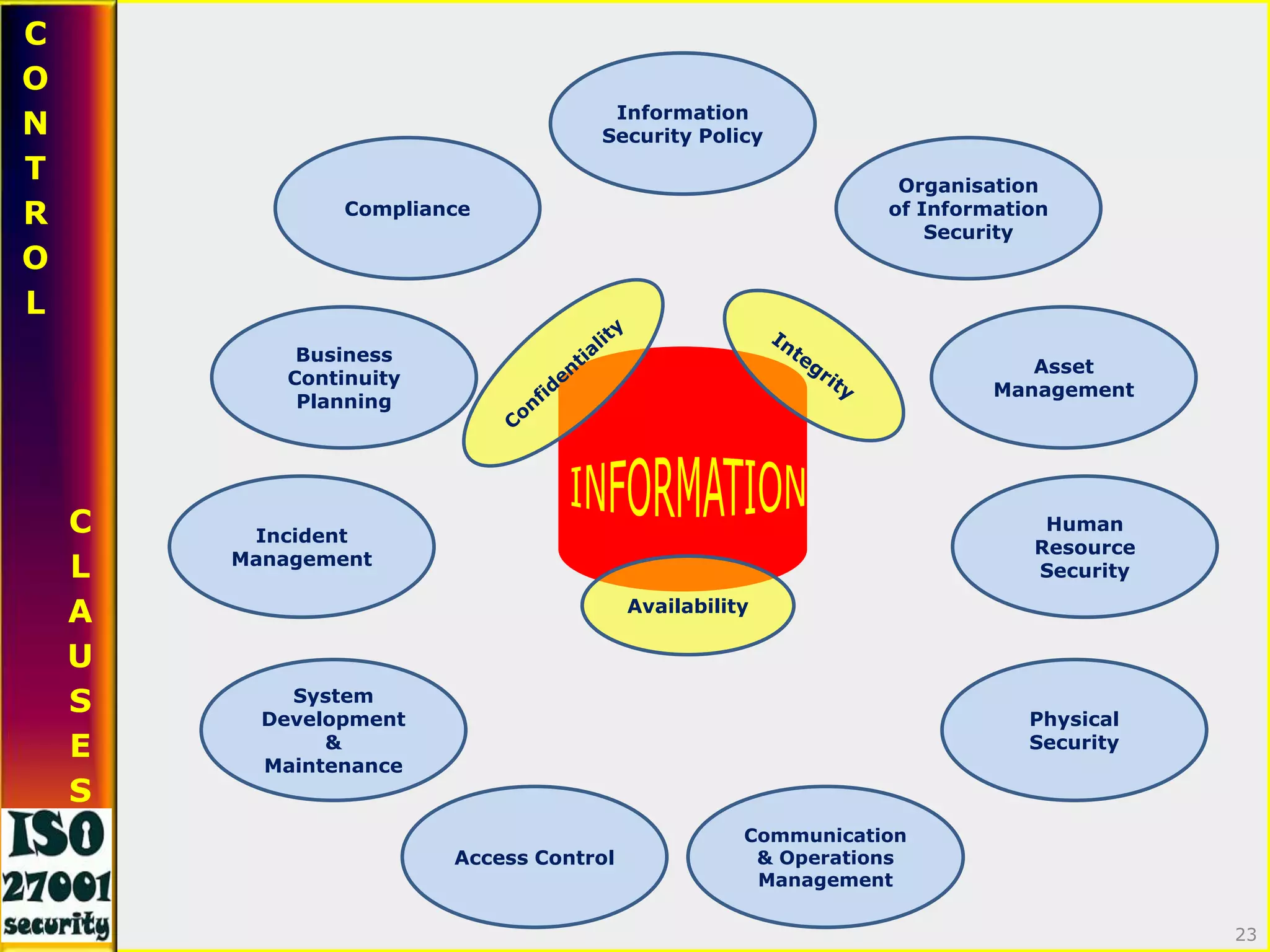
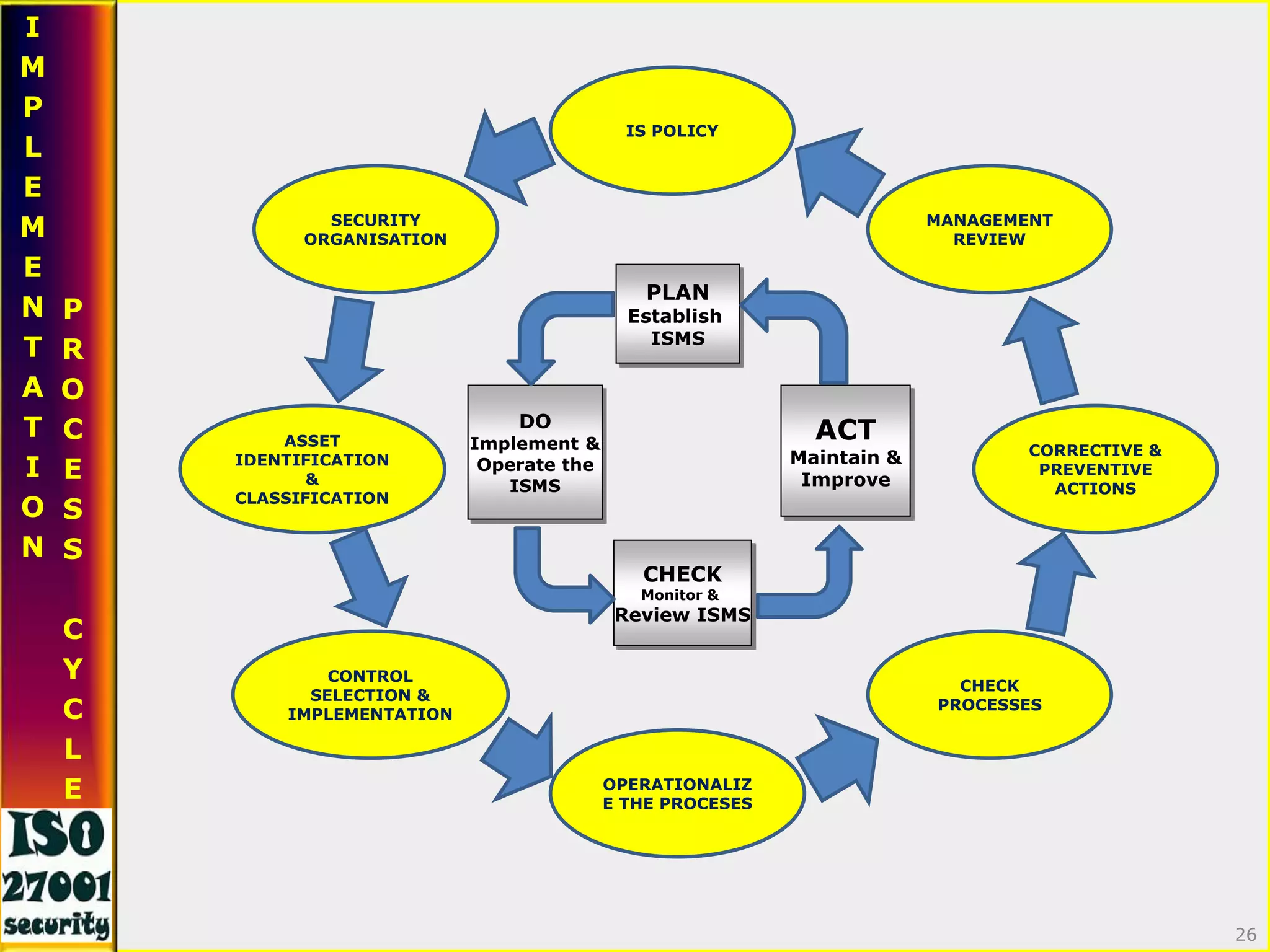
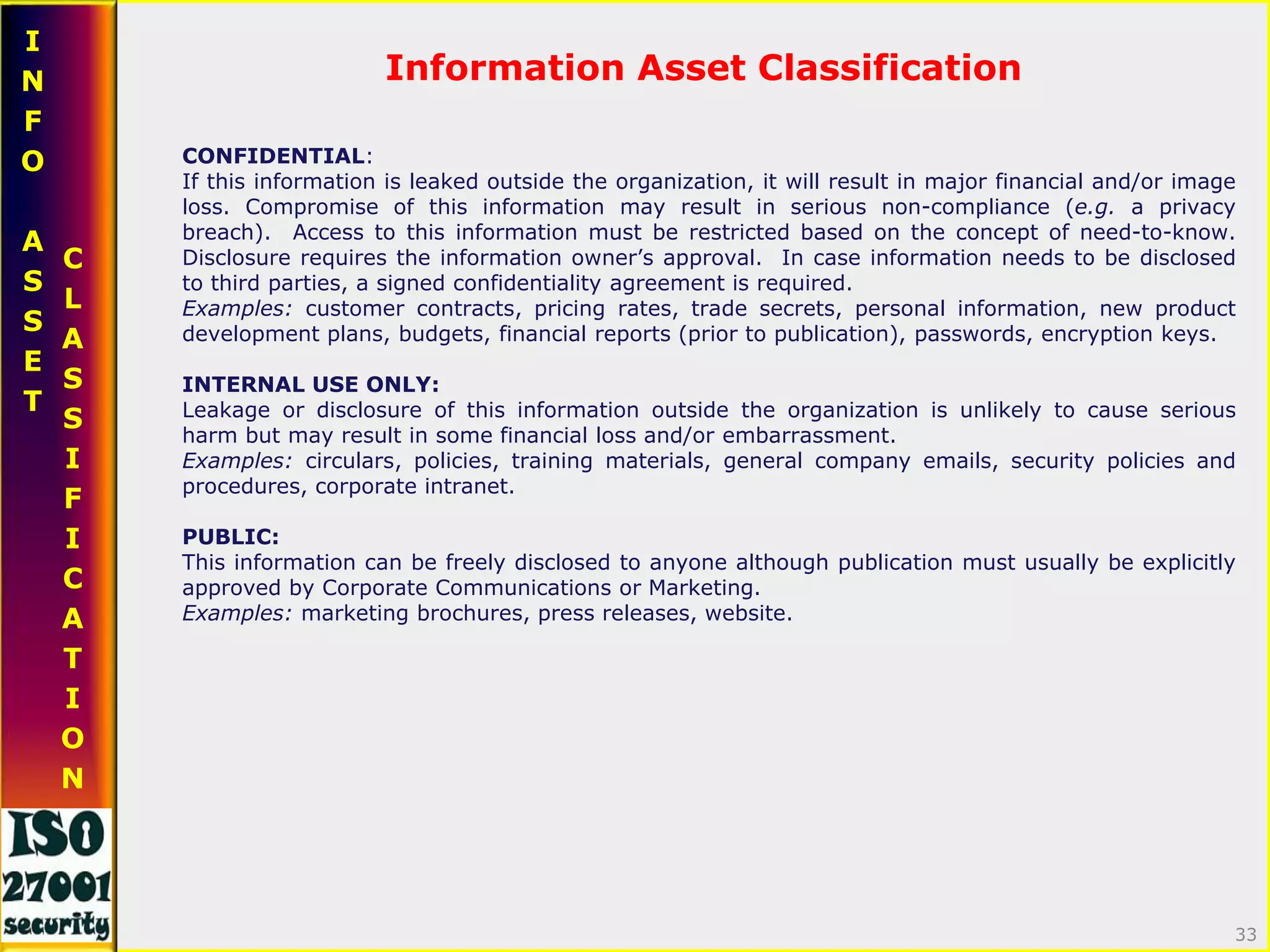
This document provides an overview of information security and ISO 27001. It discusses what information security is, the importance of protecting information assets, and introduces some of the key concepts from ISO 27001 such as risk management, the Plan-Do-Check-Act cycle, and control objectives. The document emphasizes that information security is everyone's responsibility.