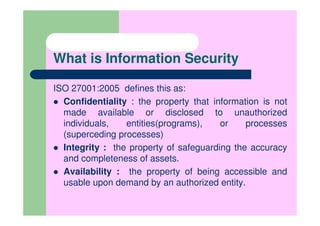
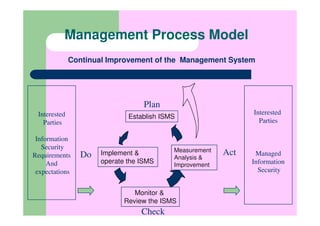
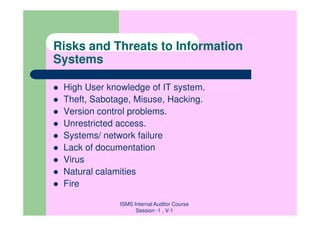
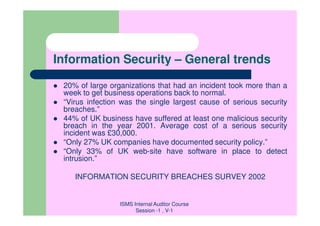
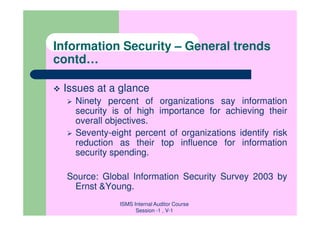
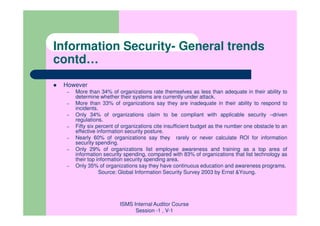
This document introduces a presentation on the direct and indirect advantages of implementing ISO 27001:2005 for an organization. It provides background on ISO 27001, including that it was published in 2005 and replaced BS7799-2. It also describes what an Information Security Management System (ISMS) is and the risks and challenges of information security.