iSecurity Data Sheet March 2016
•
0 likes•359 views
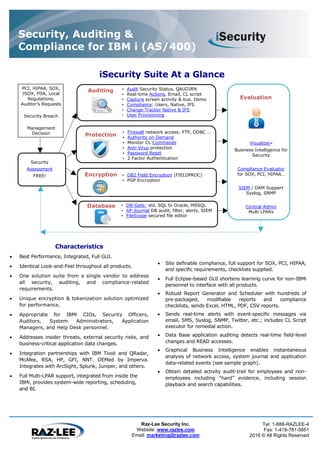
Raz-Lee Security Inc. provides a suite of security, auditing, and compliance products for IBM i (AS/400) systems. The suite includes solutions for auditing, protection, encryption, databases, and evaluation. It offers hundreds of customizable reports, real-time alerts and actions, user and system monitoring, firewalls, antivirus software, password management, and tools to evaluate compliance with regulations like SOX, PCI, and HIPAA. The suite is designed to address insider threats, external risks, application data changes, and assess an organization's overall IBM i security status.
Report
Share
Report
Share
Download to read offline
Recommended
Securing DevOps through Privileged Access Management

In this presentation from the webinar of Security MVP and Microsoft Security Trusted Advisor, Paula Januszkiewicz,get an overview of how privileged access management can help balance DevOps’ need for agility and speed with IT security’s need for visibility, access management, and compliance.
Key use cases covered include:
• Network Segmentation: Grouping assets, including application and resource servers, into logical units that do not trust one another
• Enforcing Appropriate Use of Credentials: IT organizations can leverage these controls to limit lateral movement in the case of a compromise and to provide a secure audit trail
• Elimination of Hard-Coded Passwords: Removing hardcoded passwords in DevOps tool configurations, build scripts, code files, test builds, production builds, etc.
You can watch the full, on-demand webinar here: https://www.beyondtrust.com/resources/webinar/securing-devops-privileged-access-management/
Identity and Access Management 101

Crash course in the fundamentals of identity and access management.
Recommended
Securing DevOps through Privileged Access Management

In this presentation from the webinar of Security MVP and Microsoft Security Trusted Advisor, Paula Januszkiewicz,get an overview of how privileged access management can help balance DevOps’ need for agility and speed with IT security’s need for visibility, access management, and compliance.
Key use cases covered include:
• Network Segmentation: Grouping assets, including application and resource servers, into logical units that do not trust one another
• Enforcing Appropriate Use of Credentials: IT organizations can leverage these controls to limit lateral movement in the case of a compromise and to provide a secure audit trail
• Elimination of Hard-Coded Passwords: Removing hardcoded passwords in DevOps tool configurations, build scripts, code files, test builds, production builds, etc.
You can watch the full, on-demand webinar here: https://www.beyondtrust.com/resources/webinar/securing-devops-privileged-access-management/
Identity and Access Management 101

Crash course in the fundamentals of identity and access management.
8-step Guide to Administering Windows without Domain Admin Privileges

In this presentation from his highly popular webinar, Windows security expert, Russell Smith, explains how to effectively administer Windows systems without using privileged domain accounts, enabling you to drastically reduce your organization’s threat surface.
What's New in EventLog Analyzer - Log Management Software

ManageEngine EventLog Analyzer 8 Released. EventLog Analyzer 8 provides the most cost-effective Security Information and Event Management (SIEM) in the market and provides many advanced & powerful features like Universal log parsing and indexing, machine-generated log search engine, log field extraction with interactive regular expression (regex) pattern builder, and many more.
Privileged Access Manager Product Q&A

Introduction to the business challenges of securely managing access to privileged accounts and the technical processes built into Privileged Access Manager to secure access to administrator, service and application-to-application IDs.
Enhancing your mobile enterprise security with ibm worklight tips

Enhancing your mobile enterprise security with ibm worklight tips
EventLog Analyzer - Product overview

A quick overview of MangeEngine EventLog Analyzer, the most cost-effective Log Management, Compliance Reporting software for Security Information and Event Management (SIEM). Using this Log Analyzer software, organizations can automate the entire process of managing terabytes of machine generated logs by collecting, analyzing, searching, reporting, and archiving from one central location. This event log analyzer software helps to mitigate security threats, archive data for conducting log forensics analysis, root cause analysis & more at http://www.manageengine.com/products/eventlog/
Technet System Center Mobile Device Manager Presentation

This is the presentation delivered at the 2 recent Technet events in Manchester and London as well as our EMEA Enterprise event in Dublin
Dell Quest TPAM Privileged Access Control

Dell One Privileged Password Manager. TPAM.Dell Quest TPAM Privileged Access Control
IBM Security Identity and Access Management - Portfolio

IBM Security Identity and Access Management - Products updates and what is coming
SECURE ACCESS GATEWAYS

AG Series secure access gateways provide scalable and
controlled remote and mobile access to corporate networks,
enterprise applications and cloud services for any user,
anywhere on any device.
Tänased võimalused turvalahendustes - Tarvi Tara

Event: Oracle Tartu päev
Date: 24.05.2011
Place: Ahhaa centre
A Single Strong Authentication Platform for Cloud and On-Premise Applications

Strong authentication and single sign-on for SaaS applications is available with SafeNet
Authentication Manager and SafeWord 2008.
With either platform, the enterprise security team retains complete control over the
configuration, deployment, and administration of the authentication infrastructure, which
remains in the enterprise’s IT domain.
Organizations can deploy either platform in their network’s DMZ, so users can authenticate
directly to cloud-based applications and services, rather than having to go through the corporate VPN. As a result, users have a faster, more seamless experience accessing on-premise and
cloud-based applications, while enterprises enjoy optimized security.
SSL VPN Evaluation Guide

Remote connectivity is crucial for enterprise productivity and SSL has gained fast popularity as a remote access
tool. In fact, SSL VPNs as a technology have shown promise in eliminating many of the client side issues associated
with IPSec, and other forms of remote access. Furthermore, SSL VPNs offer a smooth migration to a more costeffective,
easier to deploy remote access solution than IPSec. SSL VPN’s combination of flexibility and functionality
makes it competitive with IPSec even when deployed for enterprise’s “power users.”
In today’s crowded SSL VPN market, it’s easy to become overwhelmed by the wide range of solutions available.
Obviously, there are many factors to consider when purchasing an SSL VPN product, and you want to make the
best choice possible. This SSL VPN Evaluation Guide serves as an important resource in identifying, describing, and
prioritizing the criteria you should consider when selecting an SSL VPN provider that best fits the needs of your
organization.
Selection Criteria
In coming up with a selection criteria, the functions offered by SSL VPNs have to be evaluated against two key
aspects: security and user experience. A truly successful deployment of a secure access solution cannot be achieved
without taking both aspects into consideration. Look for an SSL VPN that can also serve the organization’s longterm
needs, integrates seamlessly with the network architecture, and provides powerful management tools. The
optimal provider will exceed in these key areas:
n Performance and scalability
n Security
n Ease of use
n Company reputation
n Technology leadership
Norton Zone File-Sharing Service

Norton Zone lets you deploy a safe and easy file-sharing service with the security expertise, visibility, and administrative controls you can only get from Symantec. With patented key encryption, Active Directory for SSO, automated two-factor authentication, and more, your employees can share files any time from any device—smartphone, computer or tablet.
HP ArcSight 

HP ArcSight solutions including logger, ESM and Express. with quick introduction about SIRM and SIEM platform. the presentation descrip information related to ArcSight smart Connector and flex connector
Tablet Access to Business Applications

The consumerization of IT is under way. Workers want tablet access to business applications, often from personal devices. Learn why VPNs are not ideal for mobile connectivity and why remote desktop is a more secure, less expensive approach to tablet access that is easier to deploy, manage and use.
Developing Secure IBM i Applications

Although IBM i is one of the most securable platforms available, the protection of critical data is often undermined by weak security design at the application level.
Avoid epic failure by designing your IBM i applications with these 5 security points in mind:
• Object ownership
• Adopted authority
• Public and private authorities
• Command line permission
• Client-server considerations
You’ll also learn why auditors are often deemed the programmer’s nemesis, and what it is they really need from you.
Fundamentals of performance tuning PHP on IBM i 

This presentation reviews of the many aspects of PHP performance that can impact day-to-day living. It explores basic concepts for resolution when PHP performance has got you down. The focus is on Zend Server configuration options including, but not limited to: caching, Apache settings, PHP syntax fundamentals, diagnosing bottlenecks, and DB2/SQL optimization.
Strategic Modernization with PHP on IBM i

You know you need to modernize your IBM i applications, but where to start? In this talk, Alan will inspire you with creative examples of modernization on IBM i that provided a strong return on investment while controlling risk. Learn how to choose projects with the best return on investment, and then complete them with confidence. We will lead an honest discussion of the most effective strategies. Can RPG programmers learn PHP? Yes. Can new PHP developers be integrated into an existing IT department? Yes. Both approaches have merit. See creative ways to use PHP, not only to create new GUI front-ends, but to enhance existing interactive RPG programs. Please your users and business people by incorporating PHP into your shop.
More Related Content
What's hot
8-step Guide to Administering Windows without Domain Admin Privileges

In this presentation from his highly popular webinar, Windows security expert, Russell Smith, explains how to effectively administer Windows systems without using privileged domain accounts, enabling you to drastically reduce your organization’s threat surface.
What's New in EventLog Analyzer - Log Management Software

ManageEngine EventLog Analyzer 8 Released. EventLog Analyzer 8 provides the most cost-effective Security Information and Event Management (SIEM) in the market and provides many advanced & powerful features like Universal log parsing and indexing, machine-generated log search engine, log field extraction with interactive regular expression (regex) pattern builder, and many more.
Privileged Access Manager Product Q&A

Introduction to the business challenges of securely managing access to privileged accounts and the technical processes built into Privileged Access Manager to secure access to administrator, service and application-to-application IDs.
Enhancing your mobile enterprise security with ibm worklight tips

Enhancing your mobile enterprise security with ibm worklight tips
EventLog Analyzer - Product overview

A quick overview of MangeEngine EventLog Analyzer, the most cost-effective Log Management, Compliance Reporting software for Security Information and Event Management (SIEM). Using this Log Analyzer software, organizations can automate the entire process of managing terabytes of machine generated logs by collecting, analyzing, searching, reporting, and archiving from one central location. This event log analyzer software helps to mitigate security threats, archive data for conducting log forensics analysis, root cause analysis & more at http://www.manageengine.com/products/eventlog/
Technet System Center Mobile Device Manager Presentation

This is the presentation delivered at the 2 recent Technet events in Manchester and London as well as our EMEA Enterprise event in Dublin
Dell Quest TPAM Privileged Access Control

Dell One Privileged Password Manager. TPAM.Dell Quest TPAM Privileged Access Control
IBM Security Identity and Access Management - Portfolio

IBM Security Identity and Access Management - Products updates and what is coming
SECURE ACCESS GATEWAYS

AG Series secure access gateways provide scalable and
controlled remote and mobile access to corporate networks,
enterprise applications and cloud services for any user,
anywhere on any device.
Tänased võimalused turvalahendustes - Tarvi Tara

Event: Oracle Tartu päev
Date: 24.05.2011
Place: Ahhaa centre
A Single Strong Authentication Platform for Cloud and On-Premise Applications

Strong authentication and single sign-on for SaaS applications is available with SafeNet
Authentication Manager and SafeWord 2008.
With either platform, the enterprise security team retains complete control over the
configuration, deployment, and administration of the authentication infrastructure, which
remains in the enterprise’s IT domain.
Organizations can deploy either platform in their network’s DMZ, so users can authenticate
directly to cloud-based applications and services, rather than having to go through the corporate VPN. As a result, users have a faster, more seamless experience accessing on-premise and
cloud-based applications, while enterprises enjoy optimized security.
SSL VPN Evaluation Guide

Remote connectivity is crucial for enterprise productivity and SSL has gained fast popularity as a remote access
tool. In fact, SSL VPNs as a technology have shown promise in eliminating many of the client side issues associated
with IPSec, and other forms of remote access. Furthermore, SSL VPNs offer a smooth migration to a more costeffective,
easier to deploy remote access solution than IPSec. SSL VPN’s combination of flexibility and functionality
makes it competitive with IPSec even when deployed for enterprise’s “power users.”
In today’s crowded SSL VPN market, it’s easy to become overwhelmed by the wide range of solutions available.
Obviously, there are many factors to consider when purchasing an SSL VPN product, and you want to make the
best choice possible. This SSL VPN Evaluation Guide serves as an important resource in identifying, describing, and
prioritizing the criteria you should consider when selecting an SSL VPN provider that best fits the needs of your
organization.
Selection Criteria
In coming up with a selection criteria, the functions offered by SSL VPNs have to be evaluated against two key
aspects: security and user experience. A truly successful deployment of a secure access solution cannot be achieved
without taking both aspects into consideration. Look for an SSL VPN that can also serve the organization’s longterm
needs, integrates seamlessly with the network architecture, and provides powerful management tools. The
optimal provider will exceed in these key areas:
n Performance and scalability
n Security
n Ease of use
n Company reputation
n Technology leadership
Norton Zone File-Sharing Service

Norton Zone lets you deploy a safe and easy file-sharing service with the security expertise, visibility, and administrative controls you can only get from Symantec. With patented key encryption, Active Directory for SSO, automated two-factor authentication, and more, your employees can share files any time from any device—smartphone, computer or tablet.
HP ArcSight 

HP ArcSight solutions including logger, ESM and Express. with quick introduction about SIRM and SIEM platform. the presentation descrip information related to ArcSight smart Connector and flex connector
Tablet Access to Business Applications

The consumerization of IT is under way. Workers want tablet access to business applications, often from personal devices. Learn why VPNs are not ideal for mobile connectivity and why remote desktop is a more secure, less expensive approach to tablet access that is easier to deploy, manage and use.
What's hot (19)
8-step Guide to Administering Windows without Domain Admin Privileges

8-step Guide to Administering Windows without Domain Admin Privileges
What's New in EventLog Analyzer - Log Management Software

What's New in EventLog Analyzer - Log Management Software
Enhancing your mobile enterprise security with ibm worklight tips

Enhancing your mobile enterprise security with ibm worklight tips
Technet System Center Mobile Device Manager Presentation

Technet System Center Mobile Device Manager Presentation
IBM Security Identity and Access Management - Portfolio

IBM Security Identity and Access Management - Portfolio
A Single Strong Authentication Platform for Cloud and On-Premise Applications

A Single Strong Authentication Platform for Cloud and On-Premise Applications
Viewers also liked
Developing Secure IBM i Applications

Although IBM i is one of the most securable platforms available, the protection of critical data is often undermined by weak security design at the application level.
Avoid epic failure by designing your IBM i applications with these 5 security points in mind:
• Object ownership
• Adopted authority
• Public and private authorities
• Command line permission
• Client-server considerations
You’ll also learn why auditors are often deemed the programmer’s nemesis, and what it is they really need from you.
Fundamentals of performance tuning PHP on IBM i 

This presentation reviews of the many aspects of PHP performance that can impact day-to-day living. It explores basic concepts for resolution when PHP performance has got you down. The focus is on Zend Server configuration options including, but not limited to: caching, Apache settings, PHP syntax fundamentals, diagnosing bottlenecks, and DB2/SQL optimization.
Strategic Modernization with PHP on IBM i

You know you need to modernize your IBM i applications, but where to start? In this talk, Alan will inspire you with creative examples of modernization on IBM i that provided a strong return on investment while controlling risk. Learn how to choose projects with the best return on investment, and then complete them with confidence. We will lead an honest discussion of the most effective strategies. Can RPG programmers learn PHP? Yes. Can new PHP developers be integrated into an existing IT department? Yes. Both approaches have merit. See creative ways to use PHP, not only to create new GUI front-ends, but to enhance existing interactive RPG programs. Please your users and business people by incorporating PHP into your shop.
PHP Installed on IBM i - the Nickel Tour

Everyone knows installing PHP on IBM i is easy. Just download the save file and run the RSTLICPGM command. But not everyone knows what that RSTLICPGM does. What is it putting on the machine? Where is it putting it? How does it all work together? In this session, we'll take a look at the IFS directories added by the Zend Server installer, to see what's in them. We'll see where PHP and PHP extensions, Apache and FastCGI configurations, log files, and more are kept. We'll also talk about how these new file objects interact with existing prerequisite software on the IBM i to present dynamic pages to the web. This session is for PHP developers and administrators interested in learning how PHP fits in with the unique operating environment of IBM i.
Install MariaDB on IBM i - Tips, troubleshooting, and more

MariaDB is the new open source drop-in replacement for MySQL that has been adopted by IBM for use on Power Linux and IBM i. ZendDBi is the installer provided by Zend for installation of MariaDB on the IBM i. In this session we'll show how to use ZendDBi to install MariaDB and provide some important tips for post-installation. We'll also demonstrate troubleshooting some common installation issues. While most installations of MariaDB are trouble free, the troubleshooting procedures will give us a chance to understand a bit more about the operation of MariaDB on the IBM i. It'll also give us the opportunity to explore some concepts on IBM i that may not be familiar to some RPG programmers.
From Zero to ZF: Your first zend framework project on ibm i

Step by step, I'll demonstrate the creation of a Zend Framework (ZF) project, with special attention to configuring the db2 adapter so it works well with IBM i.
Viewers also liked (7)
Install MariaDB on IBM i - Tips, troubleshooting, and more

Install MariaDB on IBM i - Tips, troubleshooting, and more
From Zero to ZF: Your first zend framework project on ibm i

From Zero to ZF: Your first zend framework project on ibm i
Similar to iSecurity Data Sheet March 2016
Change auditing: Determine who changed what, when and where

Change auditing: Who, What, When, Where details for every change with 'before' and 'after' values
Configuration assessment: State-in-time™ reports showing configuration settings at any point in time
More than 200 predefined reports and dashboards with filtering, grouping, sorting, exporting, email subscriptions, drill-down, web access, granular permissions and ability to create custom reports
AuditArchive™: scalable two-tiered storage (file-based + SQL database) holding consolidated audit data for up to and beyond 10 years
Unified platform to audit the entire IT infrastructure (including systems that do not produce logs), as opposed to multiple hard-to-integrate standalone tools from other vendors
Datapower Steven Cawn

Presentación sobre Datapower de IBM. Presentada por Steven Cawn en evento de Innovación y Conectividad de IBM. 25 de junio de 2015
How to Get IBM i Security and Operational Insights with Splunk

IBM i systems handle some of the most mission-critical transactions in your organization. In the past, they operated in relative isolation, but today they’re connected to other systems across your IT infrastructure to support mission-critical business services. They’re also connected to networks or the Internet, making them vulnerable to cybersecurity threats and incidents.
It’s critical that the operational and security data generated by your IBM i systems is visible in your Splunk platform for enterprise-wide analysis, but it’s difficult to capture it and make it usable for reporting.
View this webinar on-demand to learn how organizations like yours are using Ironstream to forward IBM i log data to Splunk, to gain insight into operations, security and service delivery for the ultimate success of their business. We will cover:
• Key use cases for IBM i log analysis
• Challenges of using IBM i data in Splunk
• How Ironstream and Splunk deliver key insight into IBM i operational health and security in the broader context of your enterprise
Webinar: Securing your data - Mitigating the risks with MongoDB

In this webinar, we walked through examples of the general security threats to databases. And we looked at how you can mitigate them for MongoDB deployments.
Blueprint for creating a Secure IoT Product

What is the right way to authenticate IoT devices? What is Security-First software design? What design patterns can comply as HIPAA? Those questions and more will be answered in my presentation.
Tips to Remediate your Vulnerability Management Program

In this presentation from her webinar, renowned cybersecurity expert Paula Januszkiewicz delves into what a truly holistic vulnerability management program should look like. When all parts are correctly established and working together, organizations can dramatically dial down their risk exposure. This presentation covers:
- The key phases and activities of the vulnerability management lifecycle
- The tools you need for an effective vulnerability management program
- How to prioritize your VM needs
- How an effective VM program can help you measurably reduce risk and meet compliance objectives
You can watch the full webinar here: https://www.beyondtrust.com/resources/webinar/tips-remediate-vulnerability-management-program
Securing Your MongoDB Deployment

Security is more critical than ever with new computing environments in the cloud and expanding access to the Internet. There are a number of security protection mechanisms available for MongoDB to ensure you have a stable and secure architecture for your deployment. We'll walk through general security threats to databases and specifically how they can be mitigated for MongoDB deployments.
Hitachi ID Identity and Access Management Suite

Overview of the Hitachi ID Identity and Access Management Suite.
See more at: http://hitachi-id.com/documents/
Syslog for SIEM using iSecurity 

This presentation reviews Raz-Lee's syslog solution for integrating with all SIEM solutions offered, and lists our business partners in this area.
Security Challenges in Cloud Integration - Cloud Security Alliance, Austin Ch...

Security Challenges in Cloud Integration, a presentation given at the Cloud Security Alliance, Austin Chapter meeting held on February 2, 2012.
Ironstream for IBM i - Enabling Splunk Insight into Key Security and Operatio...

IBM i servers and workloads can produce large amounts of log data daily, but as it’s written in different formats, to different journals, queues and system logs, it’s difficult to access and make usable for reporting. Join us for a webinar as introduce the Syncsort Ironstream for IBM i: a new product that expands our machine data solutions for Splunk to the IBM i. Learn how Ironstream can help your organization gain insight into operations, security and service delivery for the ultimate success of your business.
View this webinar on-demand to learn:
• How to leverage Splunk Enterprise to gain insight into IBM i log data
• Ways to gain better insight into security threats
• How to discover and act upon operational and performance issues that impact service delivery
Bringing Mainframe Security Information Into Your Splunk Security Operations ...

In today’s always-on IT world, a single security breach can bring your business to a standstill. You rely on Splunk’s powerful platform for monitoring, integrating, analyzing and visualizing security data from across your enterprise to protect your organization from security threats and incidents. However, Splunk doesn’t natively interact with mainframe and IBM i systems, leaving a glaring blind spot.
Join us to learn how to effectively integrate Mainframe and IBM i security data into Splunk- providing you with a comprehensive view of your security operations landscape.
Topics will include:
- An overview of different types of security data and how to tap into mainframe & IBM i data in your Splunk Security Operations Center
- Unique and comparative differentiators across security data integration tools to be used within the Splunk Security Operations center
- Customer use cases and examples
MongoDB Days UK: Securing Your Deployment with MongoDB Enterprise

Presented by Mat Keep, Principal Product Manager, MongoDB
Security is more critical than ever with new computing environments in the cloud and expanding access to the Internet. There are a number of security protection mechanisms available for MongoDB to ensure you have a stable and secure architecture for your deployment. We'll walk through general security threats to databases and specifically how they can be mitigated for MongoDB deployments. Topics will include:
- General security tools
- How to configure those for MongoDB
- Security features available in MongoDB such as LDAP, SSL, x.509, authentication, and encryption
Securing Your Deployment with MongoDB Enterprise

Presented by Mat Keep, Principal Product Manager, MongoDB
Security is more critical than ever with new computing environments in the cloud and expanding access to the Internet. There are a number of security protection mechanisms available for MongoDB to ensure you have a stable and secure architecture for your deployment. We'll walk through general security threats to databases and specifically how they can be mitigated for MongoDB deployments. Topics will include:
- General security tools
- How to configure those for MongoDB
- Security features available in MongoDB such as LDAP, SSL, x.509, authentication, and encryption
DSS ITSEC 2012 Balabit_Security_Shell_Control_Box & Logging

Presentation from Riga, Latvia. "Data Security Solutions" Ltd. ITSEC Conference.
Similar to iSecurity Data Sheet March 2016 (20)
Change auditing: Determine who changed what, when and where

Change auditing: Determine who changed what, when and where
How to Get IBM i Security and Operational Insights with Splunk

How to Get IBM i Security and Operational Insights with Splunk
Webinar: Securing your data - Mitigating the risks with MongoDB

Webinar: Securing your data - Mitigating the risks with MongoDB
Tips to Remediate your Vulnerability Management Program

Tips to Remediate your Vulnerability Management Program
Security Challenges in Cloud Integration - Cloud Security Alliance, Austin Ch...

Security Challenges in Cloud Integration - Cloud Security Alliance, Austin Ch...
Ironstream for IBM i - Enabling Splunk Insight into Key Security and Operatio...

Ironstream for IBM i - Enabling Splunk Insight into Key Security and Operatio...
Bringing Mainframe Security Information Into Your Splunk Security Operations ...

Bringing Mainframe Security Information Into Your Splunk Security Operations ...
SIEM - Activating Defense through Response by Ankur Vats

SIEM - Activating Defense through Response by Ankur Vats
MongoDB Days UK: Securing Your Deployment with MongoDB Enterprise

MongoDB Days UK: Securing Your Deployment with MongoDB Enterprise
DSS ITSEC 2012 Balabit_Security_Shell_Control_Box & Logging

DSS ITSEC 2012 Balabit_Security_Shell_Control_Box & Logging
More from Raz-Lee Security
Raz-Lee Security Corporate Profile

This is a short corporate profile of Raz-Lee Security, the world's leading software solution suite for IBM i (AS/400) security, auditing and compliance.
Raz Lee Security supports IPv6 in iSecurity products!

This press releases announces the immediate availability of support for IPv6 in iSecurity products.
PCI Compliance White Paper

This White Paper analyzes PCI compliance requirements and presents the specific iSecurity solutions pertinent to each of the 12 PCI compliance categories and to the appropriate sub-categories.
iSecurity Visualizer Business Intelligence Demo

This is a demo of Raz-Lee Security's Visualizer Business Intelligence product for IBM i (AS/400) systems.
iSecurity Compliance Evaluator PCI Demo

Demo of Raz-Lee Security's Compliance Evaluator product, specifically for PCI compliance on IBM i (AS/400) systems.
More from Raz-Lee Security (6)
Raz Lee Security supports IPv6 in iSecurity products!

Raz Lee Security supports IPv6 in iSecurity products!
Recently uploaded
Developing Distributed High-performance Computing Capabilities of an Open Sci...

COVID-19 had an unprecedented impact on scientific collaboration. The pandemic and its broad response from the scientific community has forged new relationships among public health practitioners, mathematical modelers, and scientific computing specialists, while revealing critical gaps in exploiting advanced computing systems to support urgent decision making. Informed by our team’s work in applying high-performance computing in support of public health decision makers during the COVID-19 pandemic, we present how Globus technologies are enabling the development of an open science platform for robust epidemic analysis, with the goal of collaborative, secure, distributed, on-demand, and fast time-to-solution analyses to support public health.
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Large Language Models (LLMs) are currently the center of attention in the tech world, particularly for their potential to advance research. In this presentation, we'll explore a straightforward and effective method for quickly initiating inference runs on supercomputers using the vLLM tool with Globus Compute, specifically on the Polaris system at ALCF. We'll begin by briefly discussing the popularity and applications of LLMs in various fields. Following this, we will introduce the vLLM tool, and explain how it integrates with Globus Compute to efficiently manage LLM operations on Polaris. Attendees will learn the practical aspects of setting up and remotely triggering LLMs from local machines, focusing on ease of use and efficiency. This talk is ideal for researchers and practitioners looking to leverage the power of LLMs in their work, offering a clear guide to harnessing supercomputing resources for quick and effective LLM inference.
Enhancing Project Management Efficiency_ Leveraging AI Tools like ChatGPT.pdf

With the advent of artificial intelligence or AI tools, project management processes are undergoing a transformative shift. By using tools like ChatGPT, and Bard organizations can empower their leaders and managers to plan, execute, and monitor projects more effectively.
2024 RoOUG Security model for the cloud.pptx

How we've evolved the MySQL server security model from a single DBA to the cloud.
Quarkus Hidden and Forbidden Extensions

Quarkus has a vast extension ecosystem and is known for its subsonic and subatomic feature set. Some of these features are not as well known, and some extensions are less talked about, but that does not make them less interesting - quite the opposite.
Come join this talk to see some tips and tricks for using Quarkus and some of the lesser known features, extensions and development techniques.
SOCRadar Research Team: Latest Activities of IntelBroker

The European Union Agency for Law Enforcement Cooperation (Europol) has suffered an alleged data breach after a notorious threat actor claimed to have exfiltrated data from its systems. Infamous data leaker IntelBroker posted on the even more infamous BreachForums hacking forum, saying that Europol suffered a data breach this month.
The alleged breach affected Europol agencies CCSE, EC3, Europol Platform for Experts, Law Enforcement Forum, and SIRIUS. Infiltration of these entities can disrupt ongoing investigations and compromise sensitive intelligence shared among international law enforcement agencies.
However, this is neither the first nor the last activity of IntekBroker. We have compiled for you what happened in the last few days. To track such hacker activities on dark web sources like hacker forums, private Telegram channels, and other hidden platforms where cyber threats often originate, you can check SOCRadar’s Dark Web News.
Stay Informed on Threat Actors’ Activity on the Dark Web with SOCRadar!
Into the Box 2024 - Keynote Day 2 Slides.pdf

Into the Box Keynote Day 2: Unveiling amazing updates and announcements for modern CFML developers! Get ready for exciting releases and updates on Ortus tools and products. Stay tuned for cutting-edge innovations designed to boost your productivity.
A Sighting of filterA in Typelevel Rite of Passage

Slide deck home: https://fpilluminated.com/deck/220
Cracking the code review at SpringIO 2024

Code reviews are vital for ensuring good code quality. They serve as one of our last lines of defense against bugs and subpar code reaching production.
Yet, they often turn into annoying tasks riddled with frustration, hostility, unclear feedback and lack of standards. How can we improve this crucial process?
In this session we will cover:
- The Art of Effective Code Reviews
- Streamlining the Review Process
- Elevating Reviews with Automated Tools
By the end of this presentation, you'll have the knowledge on how to organize and improve your code review proces
RISE with SAP and Journey to the Intelligent Enterprise

RISE with SAP and Journey to the Intelligent Enterprise
Using IESVE for Room Loads Analysis - Australia & New Zealand

Roger Cladingboel showcases how IESVE can be used to undertake heating and cooling loads.
Accelerate Enterprise Software Engineering with Platformless

Key takeaways:
Challenges of building platforms and the benefits of platformless.
Key principles of platformless, including API-first, cloud-native middleware, platform engineering, and developer experience.
How Choreo enables the platformless experience.
How key concepts like application architecture, domain-driven design, zero trust, and cell-based architecture are inherently a part of Choreo.
Demo of an end-to-end app built and deployed on Choreo.
Large Language Models and the End of Programming

Talk by Matt Welsh at Craft Conference 2024 on the impact that Large Language Models will have on the future of software development. In this talk, I discuss the ways in which LLMs will impact the software industry, from replacing human software developers with AI, to replacing conventional software with models that perform reasoning, computation, and problem-solving.
Globus Compute Introduction - GlobusWorld 2024

We describe the deployment and use of Globus Compute for remote computation. This content is aimed at researchers who wish to compute on remote resources using a unified programming interface, as well as system administrators who will deploy and operate Globus Compute services on their research computing infrastructure.
How Recreation Management Software Can Streamline Your Operations.pptx

Recreation management software streamlines operations by automating key tasks such as scheduling, registration, and payment processing, reducing manual workload and errors. It provides centralized management of facilities, classes, and events, ensuring efficient resource allocation and facility usage. The software offers user-friendly online portals for easy access to bookings and program information, enhancing customer experience. Real-time reporting and data analytics deliver insights into attendance and preferences, aiding in strategic decision-making. Additionally, effective communication tools keep participants and staff informed with timely updates. Overall, recreation management software enhances efficiency, improves service delivery, and boosts customer satisfaction.
Enhancing Research Orchestration Capabilities at ORNL.pdf

Cross-facility research orchestration comes with ever-changing constraints regarding the availability and suitability of various compute and data resources. In short, a flexible data and processing fabric is needed to enable the dynamic redirection of data and compute tasks throughout the lifecycle of an experiment. In this talk, we illustrate how we easily leveraged Globus services to instrument the ACE research testbed at the Oak Ridge Leadership Computing Facility with flexible data and task orchestration capabilities.
First Steps with Globus Compute Multi-User Endpoints

In this presentation we will share our experiences around getting started with the Globus Compute multi-user endpoint. Working with the Pharmacology group at the University of Auckland, we have previously written an application using Globus Compute that can offload computationally expensive steps in the researcher's workflows, which they wish to manage from their familiar Windows environments, onto the NeSI (New Zealand eScience Infrastructure) cluster. Some of the challenges we have encountered were that each researcher had to set up and manage their own single-user globus compute endpoint and that the workloads had varying resource requirements (CPUs, memory and wall time) between different runs. We hope that the multi-user endpoint will help to address these challenges and share an update on our progress here.
How to Position Your Globus Data Portal for Success Ten Good Practices

Science gateways allow science and engineering communities to access shared data, software, computing services, and instruments. Science gateways have gained a lot of traction in the last twenty years, as evidenced by projects such as the Science Gateways Community Institute (SGCI) and the Center of Excellence on Science Gateways (SGX3) in the US, The Australian Research Data Commons (ARDC) and its platforms in Australia, and the projects around Virtual Research Environments in Europe. A few mature frameworks have evolved with their different strengths and foci and have been taken up by a larger community such as the Globus Data Portal, Hubzero, Tapis, and Galaxy. However, even when gateways are built on successful frameworks, they continue to face the challenges of ongoing maintenance costs and how to meet the ever-expanding needs of the community they serve with enhanced features. It is not uncommon that gateways with compelling use cases are nonetheless unable to get past the prototype phase and become a full production service, or if they do, they don't survive more than a couple of years. While there is no guaranteed pathway to success, it seems likely that for any gateway there is a need for a strong community and/or solid funding streams to create and sustain its success. With over twenty years of examples to draw from, this presentation goes into detail for ten factors common to successful and enduring gateways that effectively serve as best practices for any new or developing gateway.
Vitthal Shirke Microservices Resume Montevideo

Software Engineering, Software Consulting, Tech Lead.
Spring Boot, Spring Cloud, Spring Core, Spring JDBC, Spring Security,
Spring Transaction, Spring MVC,
Log4j, REST/SOAP WEB-SERVICES.
Top Features to Include in Your Winzo Clone App for Business Growth (4).pptx

Discover the essential features to incorporate in your Winzo clone app to boost business growth, enhance user engagement, and drive revenue. Learn how to create a compelling gaming experience that stands out in the competitive market.
Recently uploaded (20)
Developing Distributed High-performance Computing Capabilities of an Open Sci...

Developing Distributed High-performance Computing Capabilities of an Open Sci...
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...
Enhancing Project Management Efficiency_ Leveraging AI Tools like ChatGPT.pdf

Enhancing Project Management Efficiency_ Leveraging AI Tools like ChatGPT.pdf
SOCRadar Research Team: Latest Activities of IntelBroker

SOCRadar Research Team: Latest Activities of IntelBroker
A Sighting of filterA in Typelevel Rite of Passage

A Sighting of filterA in Typelevel Rite of Passage
RISE with SAP and Journey to the Intelligent Enterprise

RISE with SAP and Journey to the Intelligent Enterprise
Using IESVE for Room Loads Analysis - Australia & New Zealand

Using IESVE for Room Loads Analysis - Australia & New Zealand
Accelerate Enterprise Software Engineering with Platformless

Accelerate Enterprise Software Engineering with Platformless
How Recreation Management Software Can Streamline Your Operations.pptx

How Recreation Management Software Can Streamline Your Operations.pptx
Enhancing Research Orchestration Capabilities at ORNL.pdf

Enhancing Research Orchestration Capabilities at ORNL.pdf
First Steps with Globus Compute Multi-User Endpoints

First Steps with Globus Compute Multi-User Endpoints
How to Position Your Globus Data Portal for Success Ten Good Practices

How to Position Your Globus Data Portal for Success Ten Good Practices
Top Features to Include in Your Winzo Clone App for Business Growth (4).pptx

Top Features to Include in Your Winzo Clone App for Business Growth (4).pptx
iSecurity Data Sheet March 2016
- 1. Raz-Lee Security Inc. Website: www.razlee.com Email: marketing@razlee.com Tel: 1-888-RAZLEE-4 Fax: 1-419-781-5851 2016 © All Rights Reserved Security, Auditing & Compliance for IBM i (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) l Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) iSecurity Suite At a Glance Characteristics Best Performance, Integrated, Full GUI. Identical Look-and-Feel throughout all products. One solution suite from a single vendor to address all security, auditing, and compliance-related requirements. Unique encryption & tokenization solution optimized for performance. Appropriate for IBMi CIOs, Security Officers, Auditors, System Administrators, Application Managers, and Help Desk personnel. Addresses insider threats, external security risks, and business-critical application data changes. Integration partnerships with IBM Tivoli and QRadar, McAfee, RSA, HP, GFI, NNT. OEMed by Imperva. Integrates with ArcSight, Splunk, Juniper, and others. Full Multi-LPAR support, integrated from inside the IBMi, provides system-wide reporting, scheduling, and BI. Site definable compliance, full support for SOX, PCI, HIPAA, and specific requirements, checklists supplied. Full Eclipse-based GUI shortens learning curve for non-IBMi personnel to interface with all products. Robust Report Generator and Scheduler with hundreds of pre-packaged, modifiable reports and compliance checklists, sends Excel, HTML, PDF, CSV reports. Sends real-time alerts with event-specific messages via email, SMS, Syslog, SNMP, Twitter, etc.; includes CL Script executor for remedial action. Data Base application auditing detects real-time field-level changes and READ accesses. Graphical Business Intelligence enables instantaneous analysis of network access, system journal and application data-related events (see sample graph). Obtain detailed activity audit-trail for employees and non- employees including “hard” evidence, including session playback and search capabilities. Auditing Protection Database • DB-Gate: std. SQL to Oracle, MSSQL • AP-Journal DB audit, filter, alerts, SIEM • FileScope secured file editor Security Assessment FREE! PCI, HIPAA, SOX, JSOX, FDA, Local Regulations, Auditor’s Requests Security Breach Management Decision • Audit Security Status, QAUDJRN • Real-time Actions, Email, CL script • Capture screen activity & bus. Items • Compliance: Users, Native, IFS • Change Tracker Native & IFS • User Provisioning • Firewall network access: FTP, ODBC … • Authority on Demand • Monitor CL Commands • Anti-Virus protection • Password Reset • 2 Factor Authentication Encryption • DB2 Field Encryption (FIELDPROC) • PGP Encryption Evaluation Visualizer- Business Intelligence for Security Compliance Evaluator for SOX, PCI, HIPAA… SIEM / DAM Support Syslog, SNMP Central Admin Multi LPARs
- 2. Raz-Lee Security Inc. Website: www.razlee.com Email: marketing@razlee.com Tel: 1-888-RAZLEE-4 Fax: 1-419-781-5851 2016 © All Rights Reserved Security, Auditing & Compliance for IBM i (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) l Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) i Securiity, Audiitiing & Complliiance for IBM ii (AS/400) Auditing Audit – Hundreds of modifiable reports, report generator & scheduler, monitor QAUDJRN, Reports and Security status. Action – Pro-active support for real-time security events, via triggers to Email, SMS, Syslog, SNMP, Twitter, and CL command scripts, option to execute from report output. Capture – Silent 5250 screen capture for end-to-end audit trails with Playback, and Find. Isolates data for drill-down: eg. Loan No., Customer No., other specific data. Compliance for User Profiles, Native Objects and IFS- Plan, Check and Set parameters and authorities, with Artificial Intelligence (AI) wizard to plan rules. Change Tracker – Changes to production automatically logged. IFS at object / source levels. System Control - Monitors system status, active jobs, message queues and QHST, triggers alerts and reactions. Replication of User Profiles and System Values – Rule-based replication with full logging and reporting. User Provisioning – Simplifies onboarding and managing users via pre-defined templates, exposes exceptions. Multi System –Manage multiple systems from a single LPAR, cross-LPAR reporting, centralized upgrades. Protection Screen – Unattended rule-based screen protection.. Anti-Virus – On-access IFS virus checks and scans, Native Object Integrity checks, alert by email and by Syslog. Firewall – Network security with exceptional performance. Controlling Exit Points, Open DB’s and SSH. Simulation mode, Rule Wizards and graphical BI. 2-Step Password Verification - Non--trivial authentication procedures. 2 Factor Password Authentication- IBM i interface to RSA SecurID ensuring user identity via RSA token. Command - Control validity of System and User commands and their parameters, per user, IP, time, and more. Authority on Demand – Provides temporary extended authorization by Swap or by Adding authority. Full auditing including screen captures and DB updates. Password Reset – Self/Assisted password support, Native and Web-based. Encryption DB2 Field Encryption (FIELDPROC) – Performance optimized sophisticated identification of fields requiring encryption. Column-level field encryption based on IBM’s FIELDPROC, Encryption & Tokenization, never Locks user-files, Key manager serves multiple LPARs. PGP Encryption– Private and Public key technology for encrypting data files. Databases AP-Journal Business Analysis and Alerts – Real time DB activity including READ, compares values by fields, Alerts and Reports, stores selected Events, cross- application reports based on Customer, Account, Item. DB-Gate – Standard Native access to Oracle, MSSQL/MySQL, from STRSQL, RPG, COBOL. FileScope – SOX enabled File editor with UNDO capability. Evaluation Compliance Evaluator – Single-view network-wide PCI, SOX, HIPAA and site-defined compliance checks for multiple LPARS, sends color coded EXCEL via email. Visualizer– Intuitive Graphical Business Intelligence analysis of security data, supports “drill” to specific events. SIEM & DAM support - Syslog, SNMP, Twitter, JSON, CEF; easy to define and integrate with IBM QRadar, Tivoli, RSA, ArcSight, McAfee, OpenView, UniCenter, Splunk, Juniper, GFI, NNT, OEMed by Imperva. Assessment – PC-based, analyzes and scores IBM i security definitions and values, suggests corrections and solutions.
