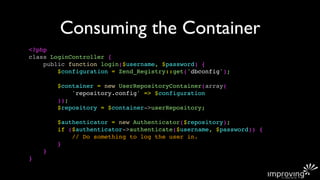
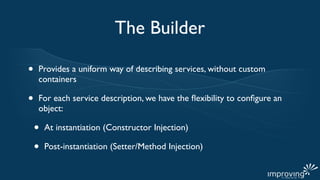
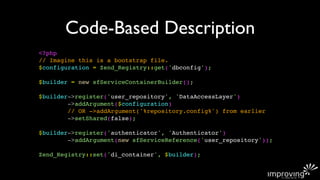
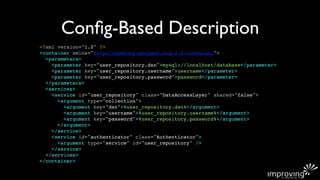
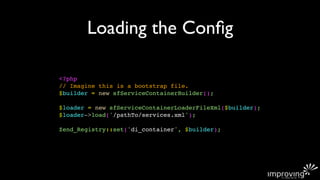
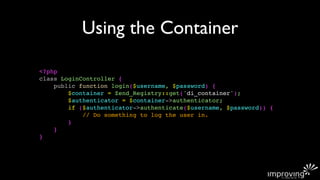
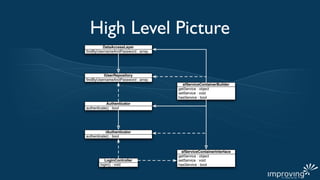
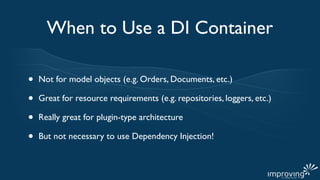
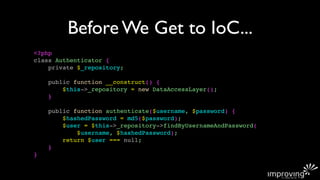
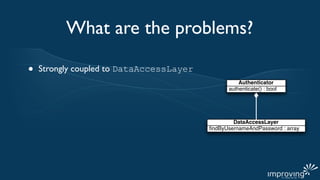
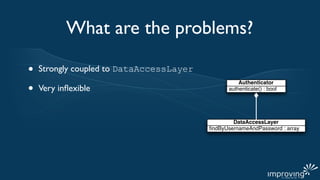
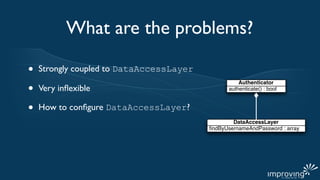
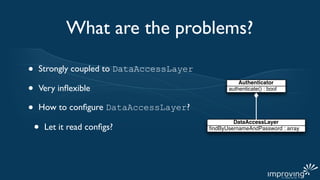
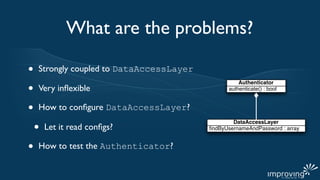
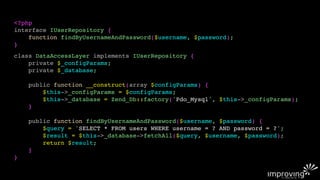
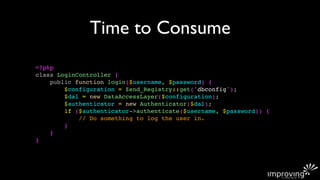
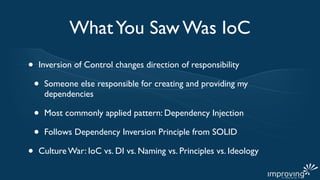
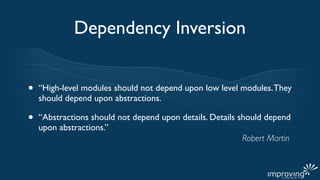
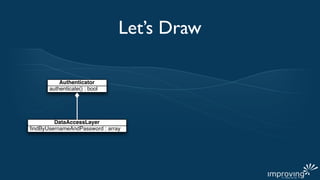
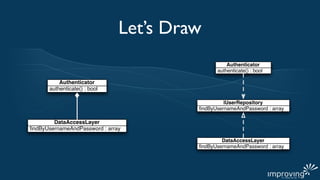
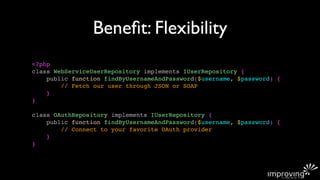
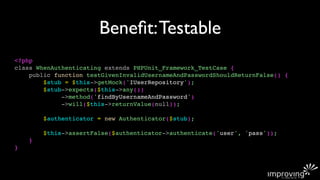
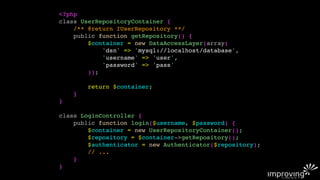
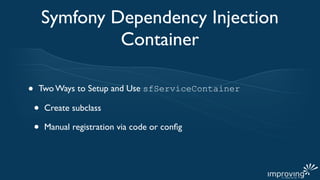
The document discusses using inversion of control (IoC) and dependency injection (DI) to decouple classes and make them more flexible and testable in PHP. It provides an example of refactoring an authenticator class to depend on a user repository interface rather than a concrete class. This decreases coupling and allows different repositories to be injected. It then discusses using a service container to further abstract object creation and injection of dependencies defined through code or configuration.








![sfServiceContainer Subclass
<?php
class UserRepositoryContainer extends sfServiceContainer {
protected function getUserRepositoryService() {
$container = new DataAccessLayer($this['repository.config']);
return $container;
}
}](https://image.slidesharecdn.com/iocwithphp-110812014234-phpapp01/85/IoC-with-PHP-32-320.jpg)