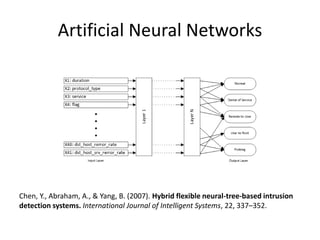
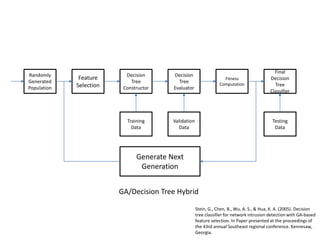
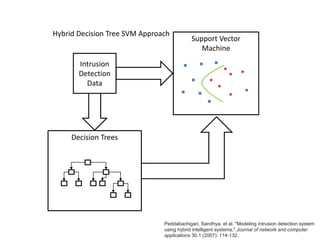
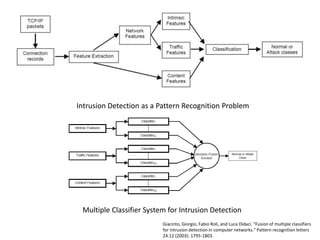
An intrusion detection system uses machine learning techniques to classify network traffic as either normal or anomalous. Common machine learning approaches for anomaly detection include single classifiers like k-nearest neighbors, support vector machines, neural networks, and decision trees. Hybrid and ensemble classifiers can also be used, which combine the outputs of multiple classifiers. Choosing the right machine learning technique requires considering factors like the costs of false positives and negatives, diversity of network traffic, lack of training data, and the need to explain detections to humans.