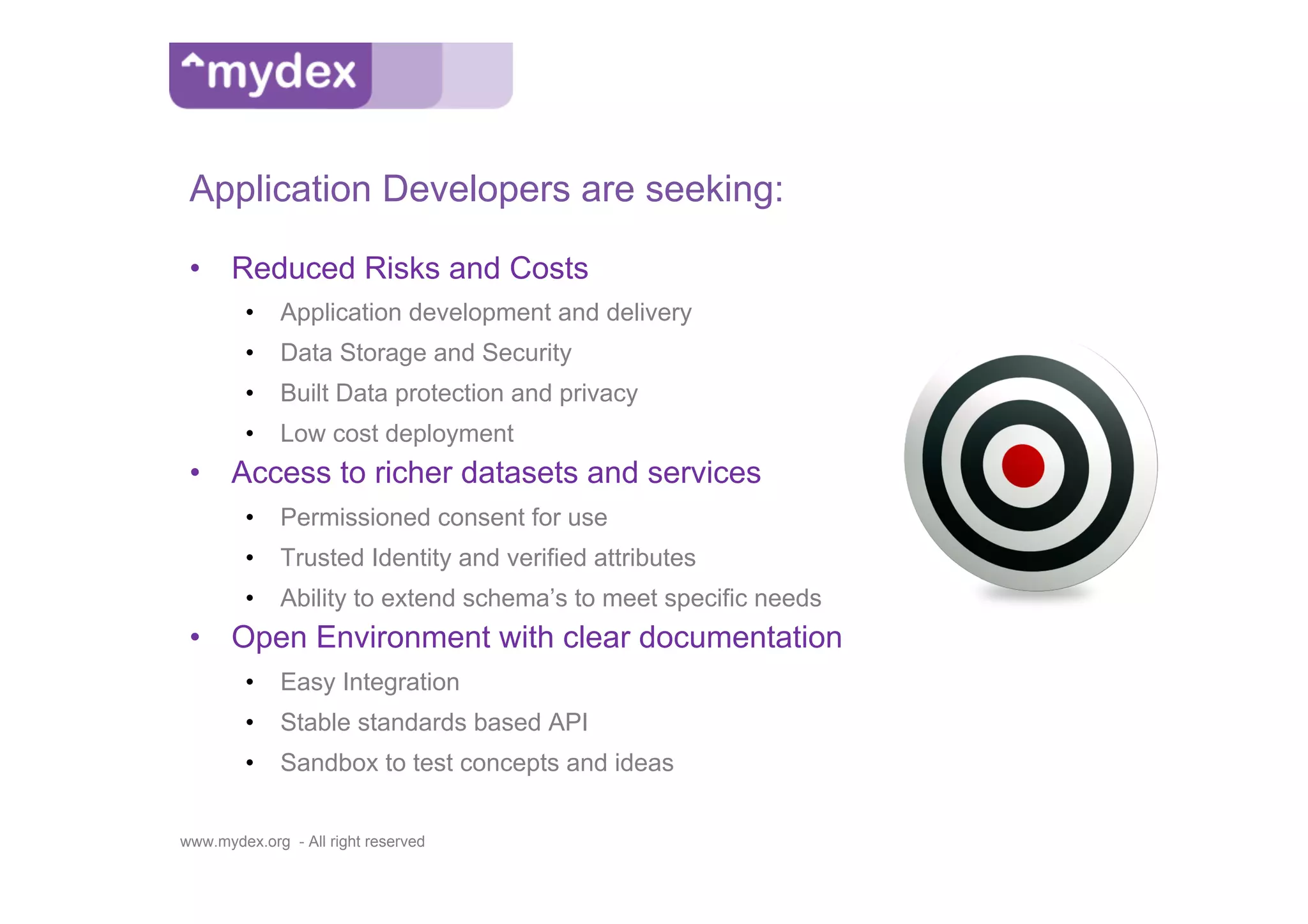
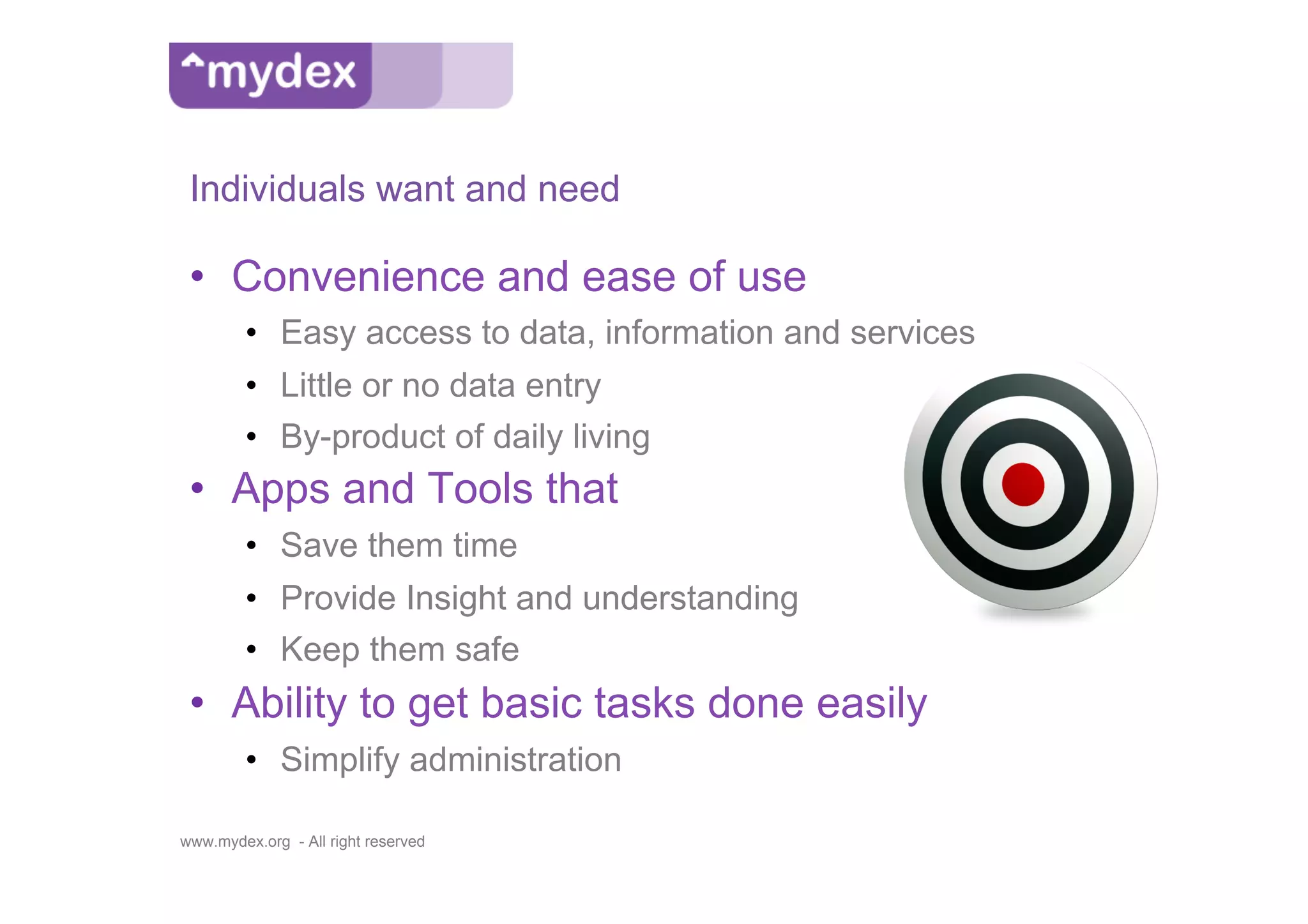
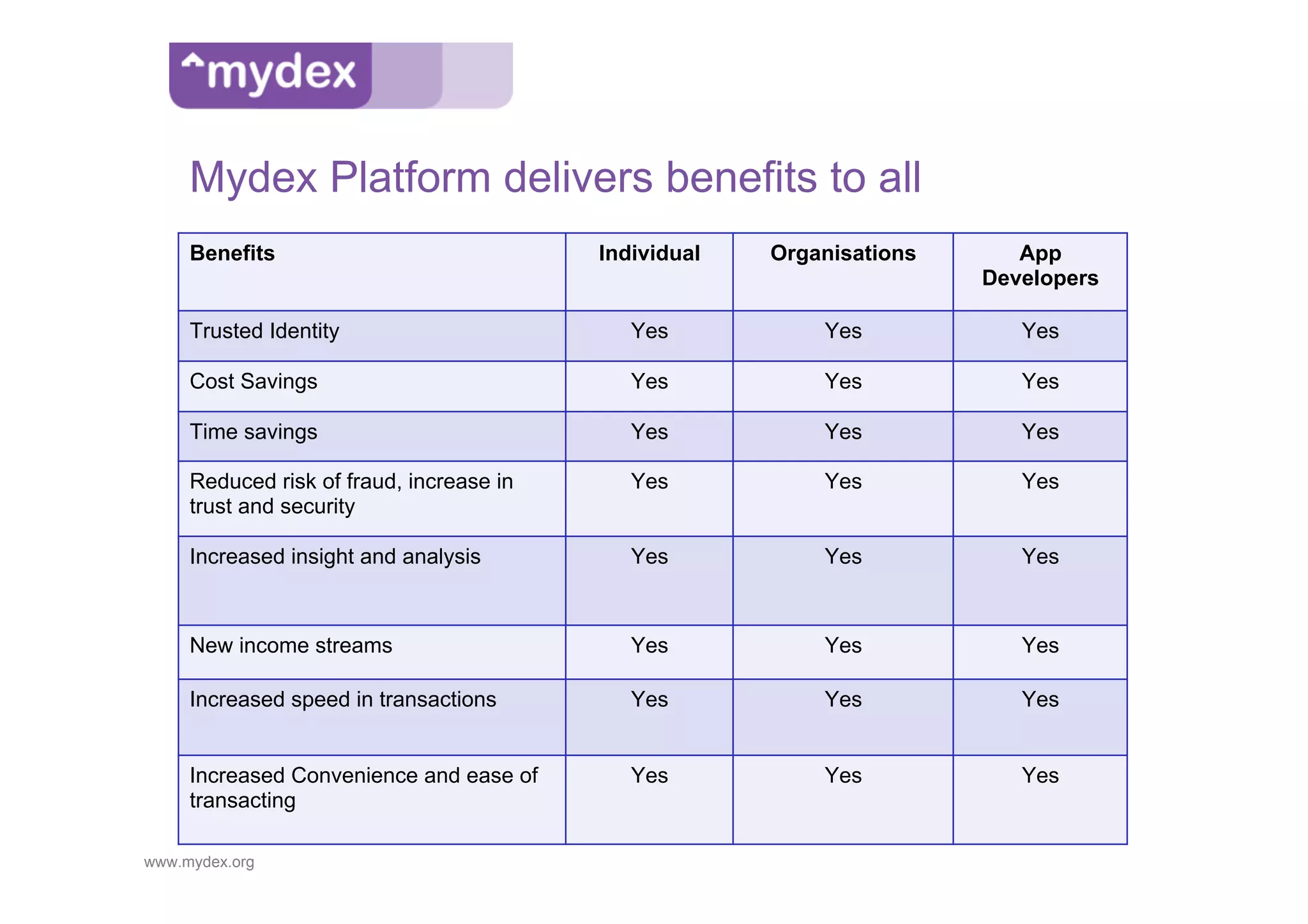
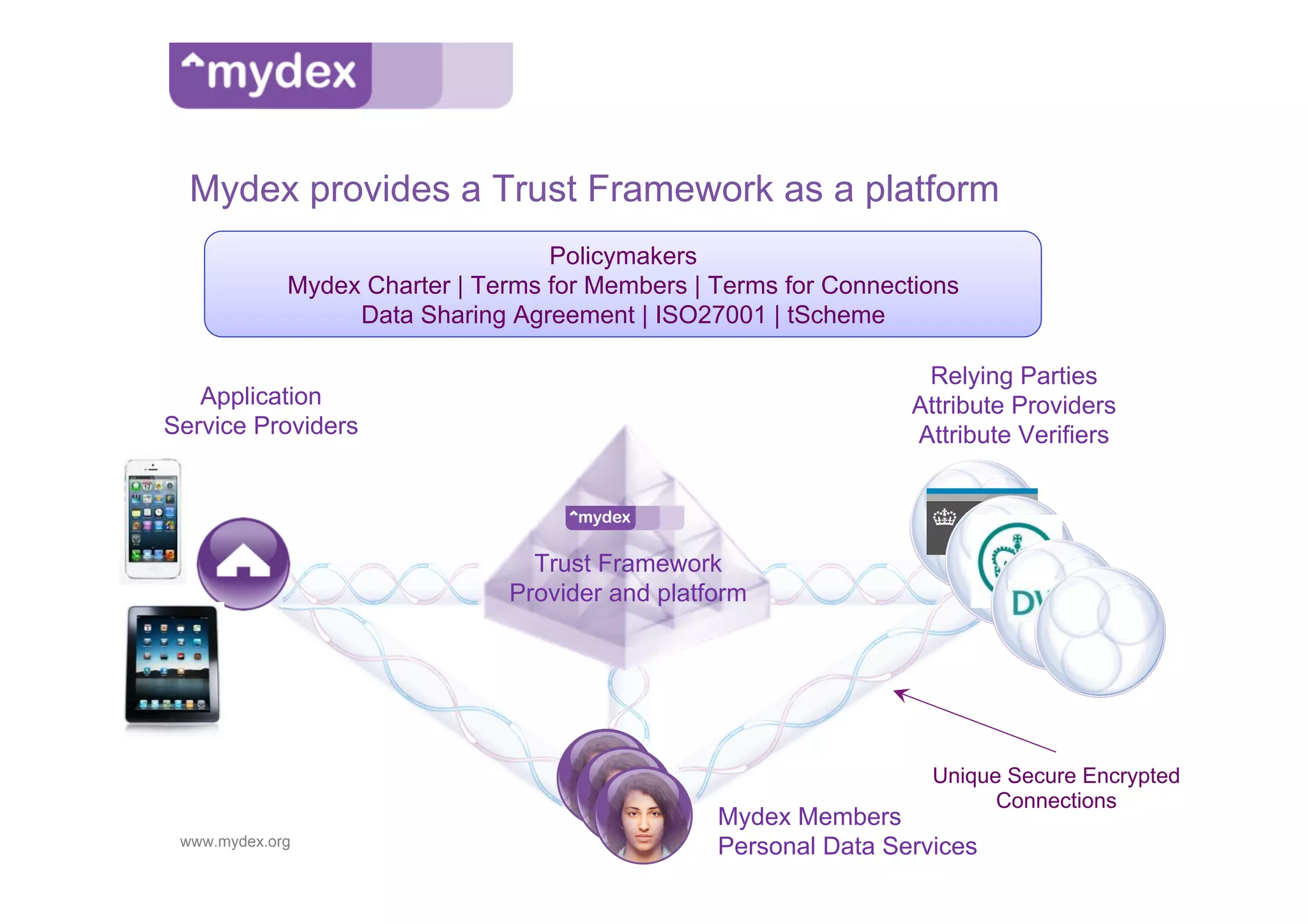
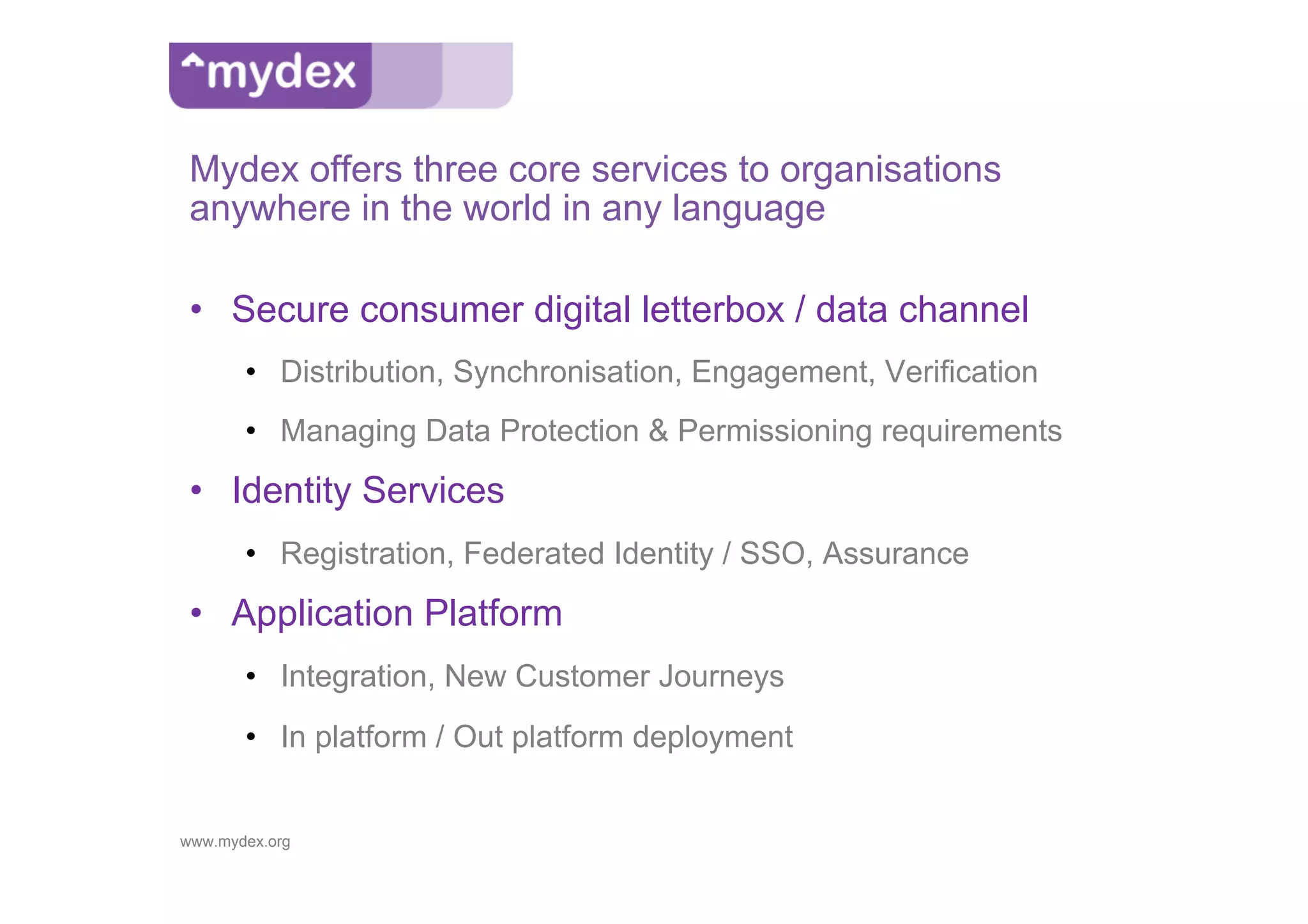
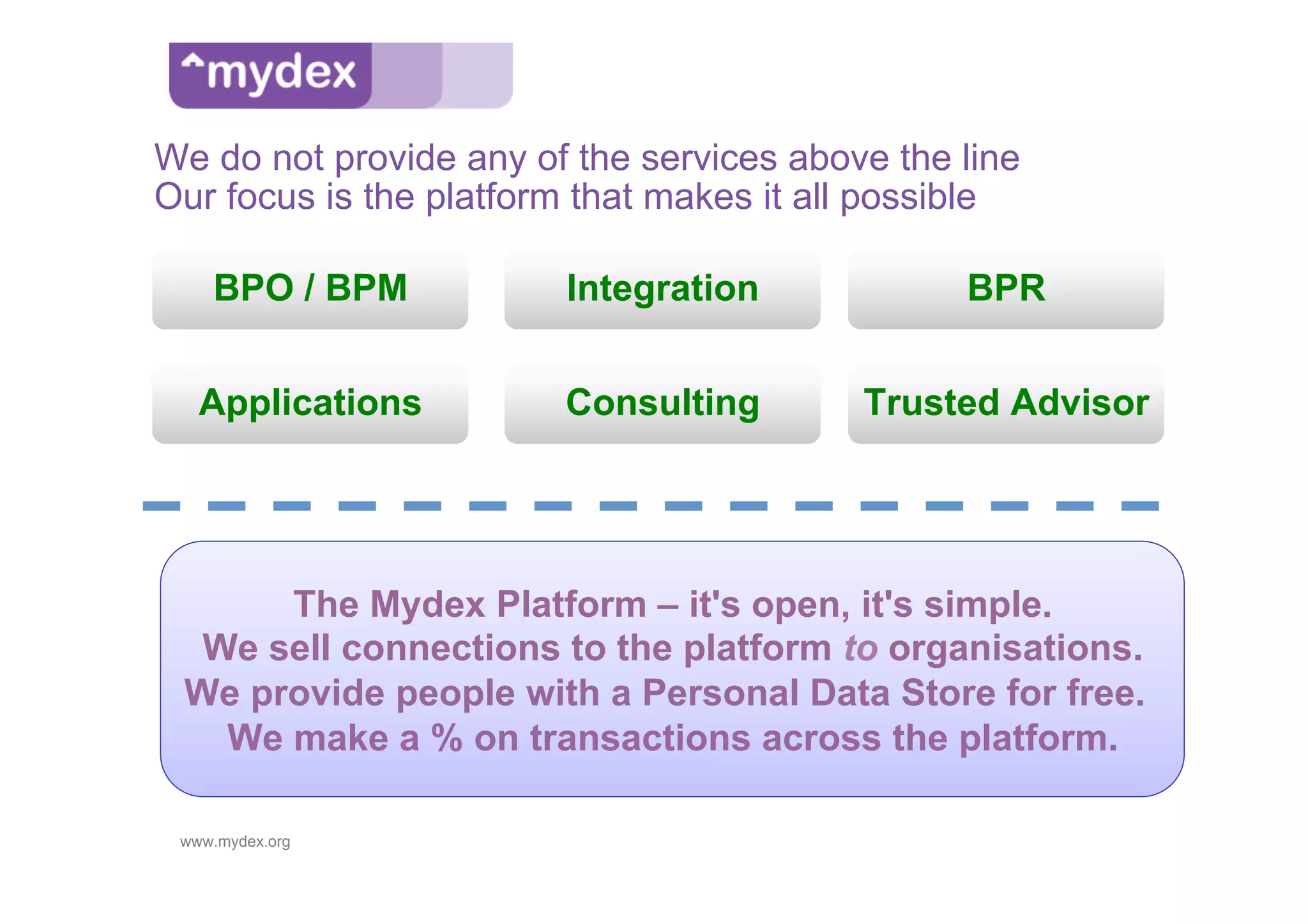
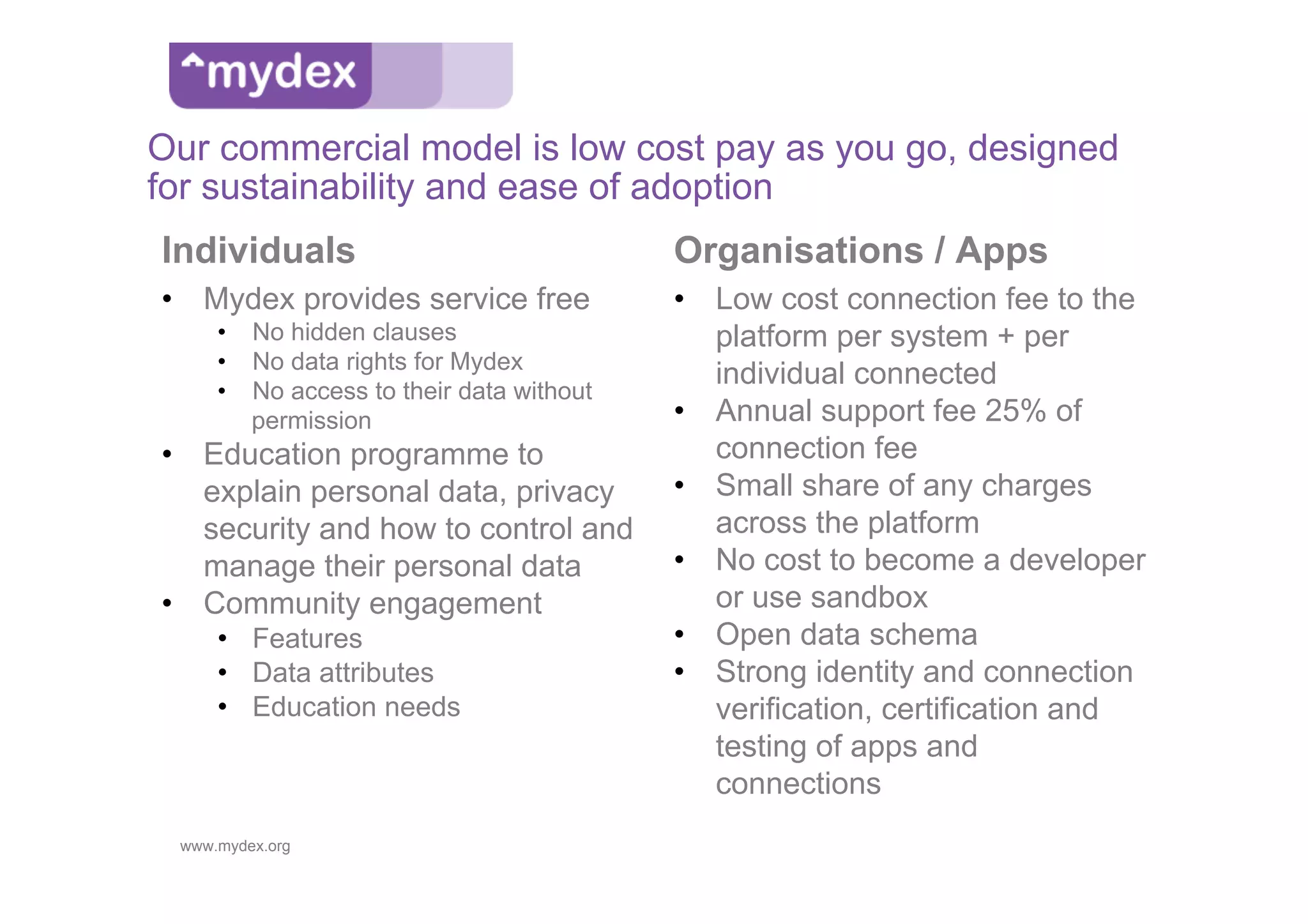
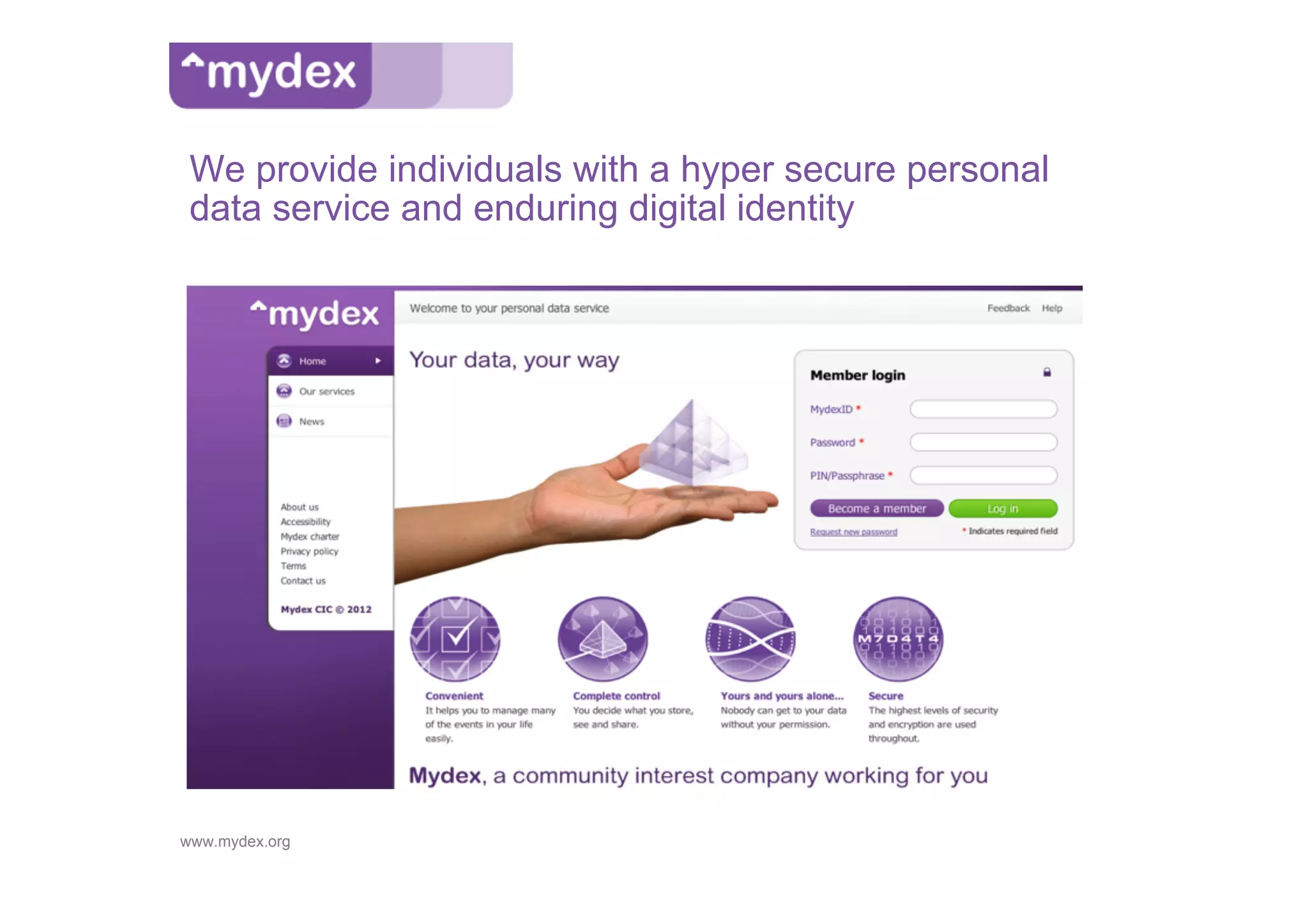
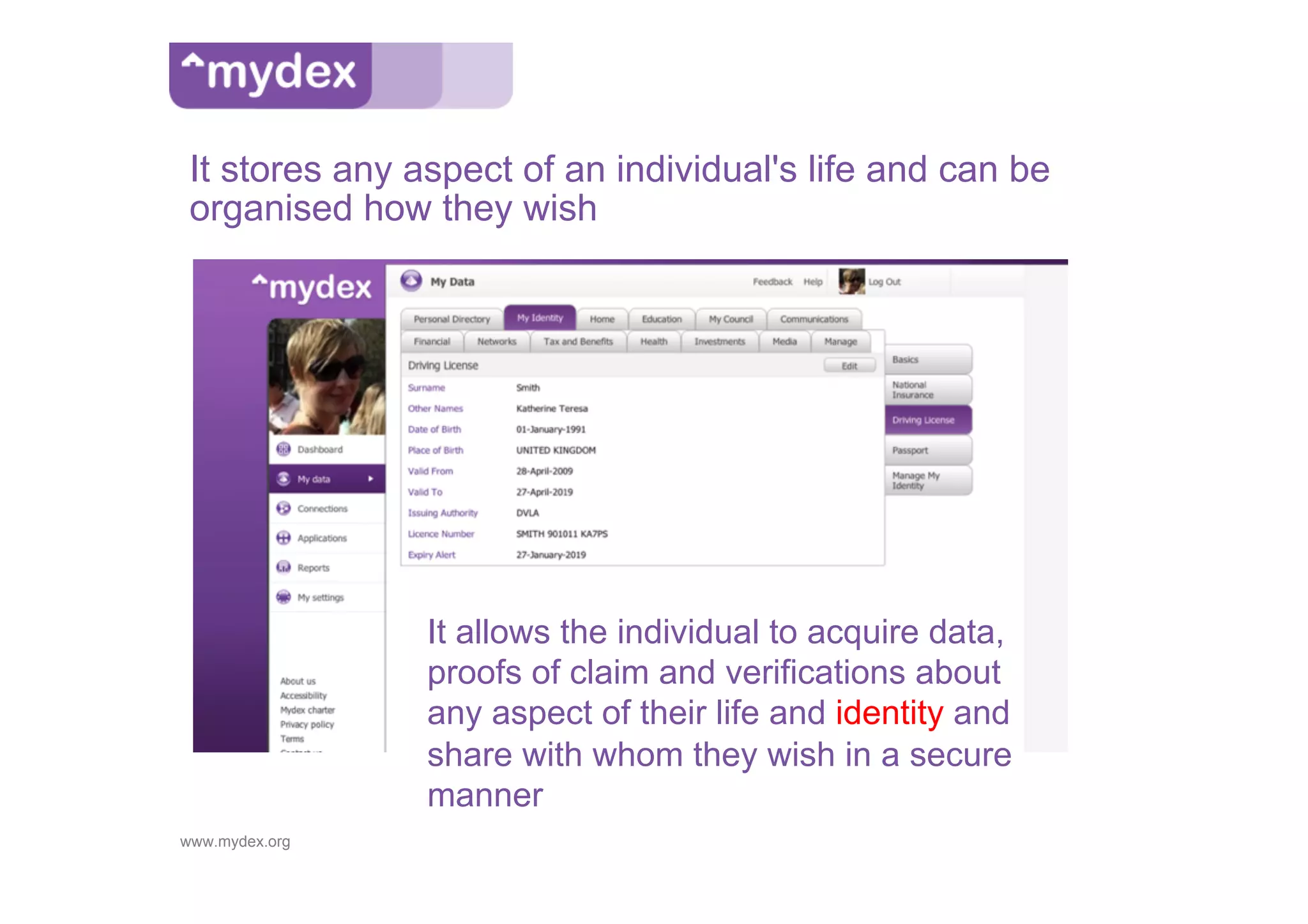
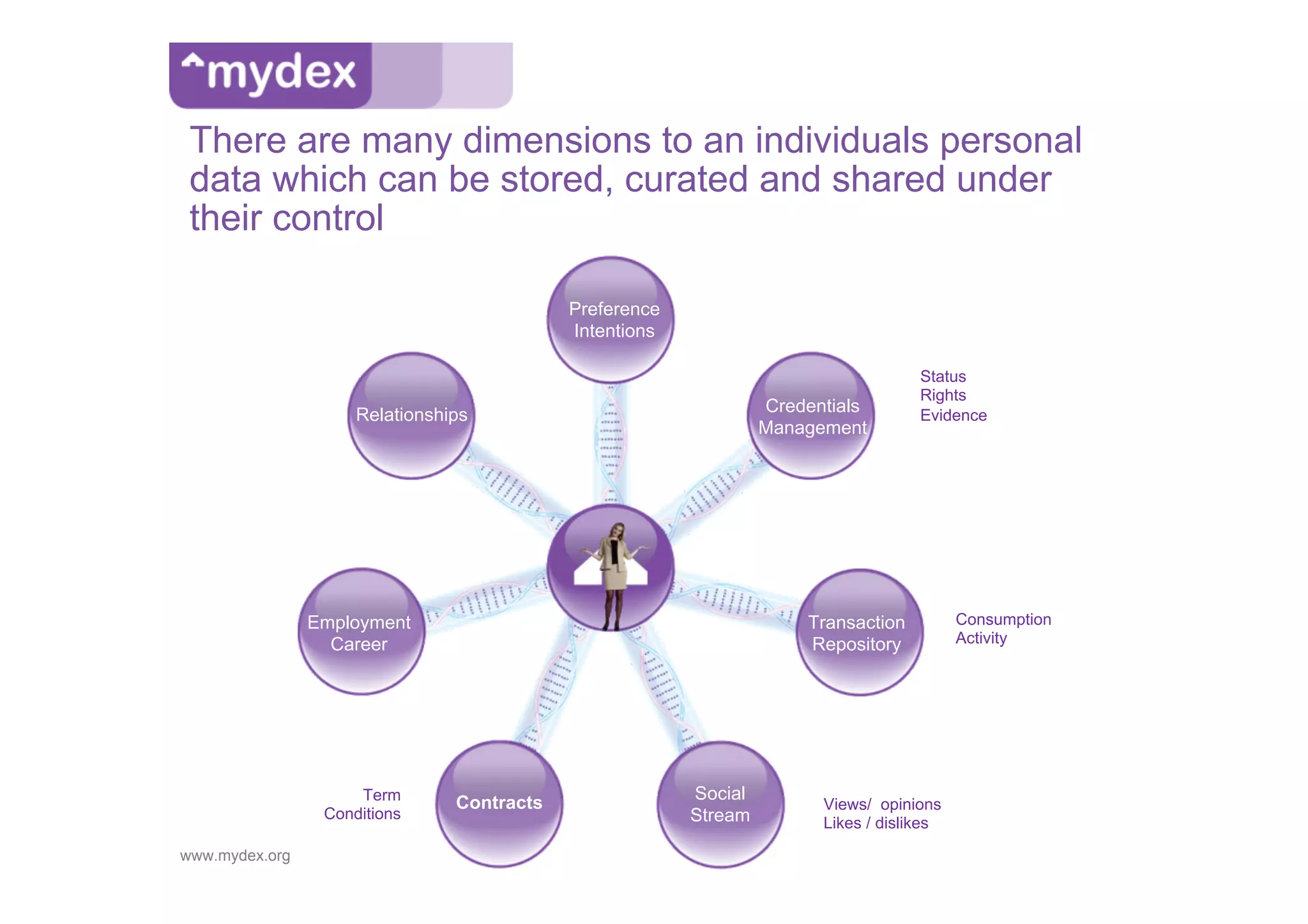
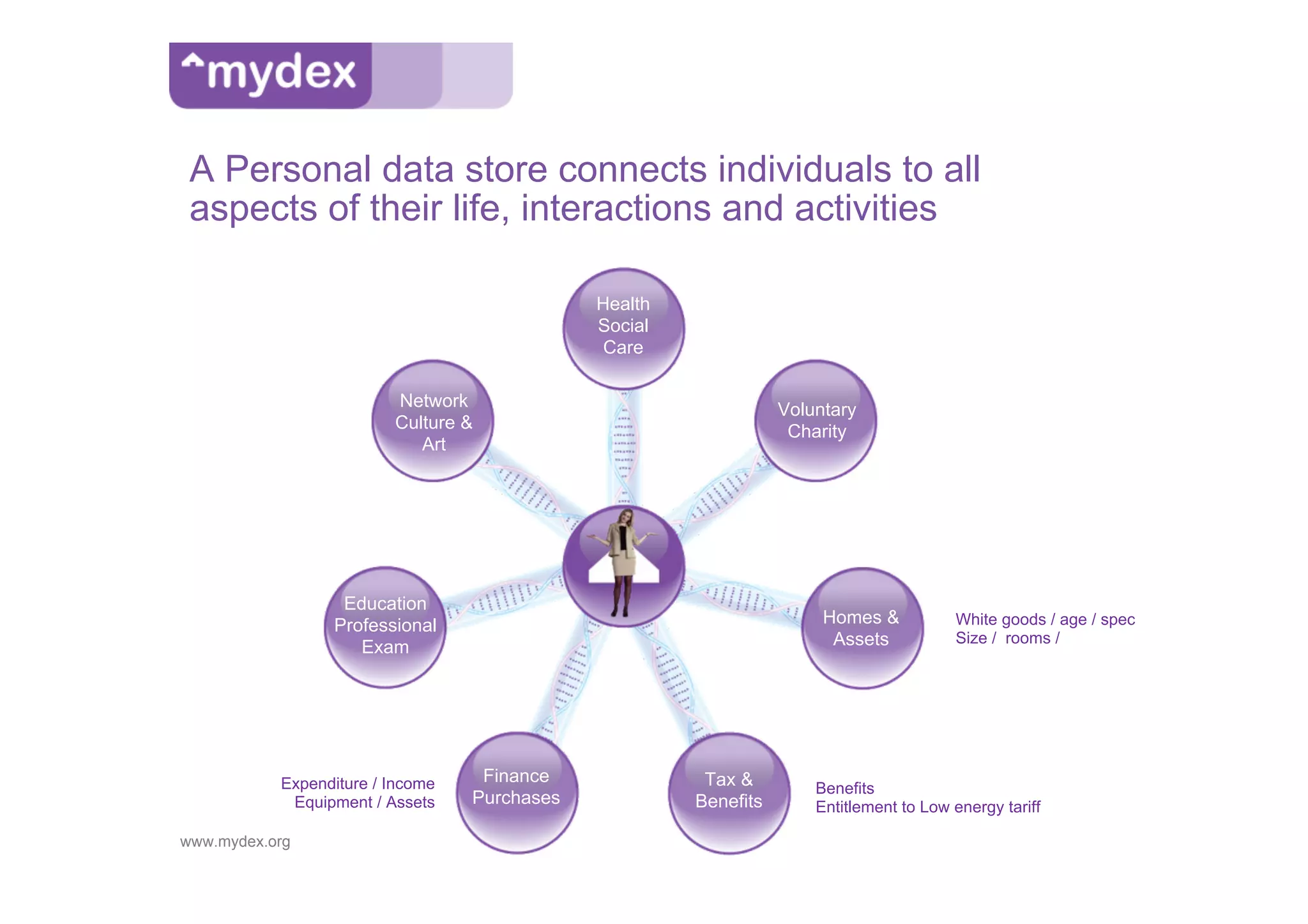
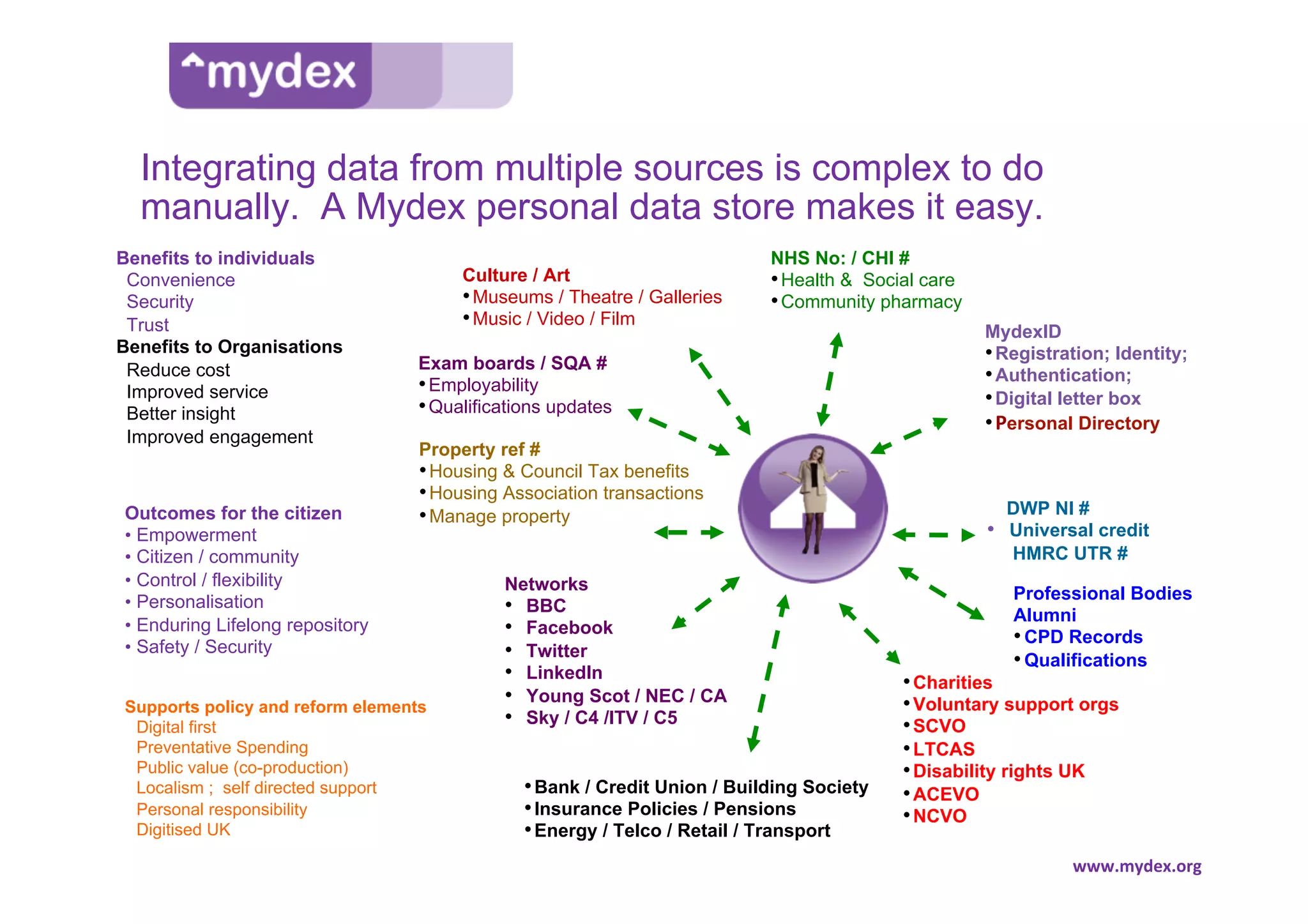
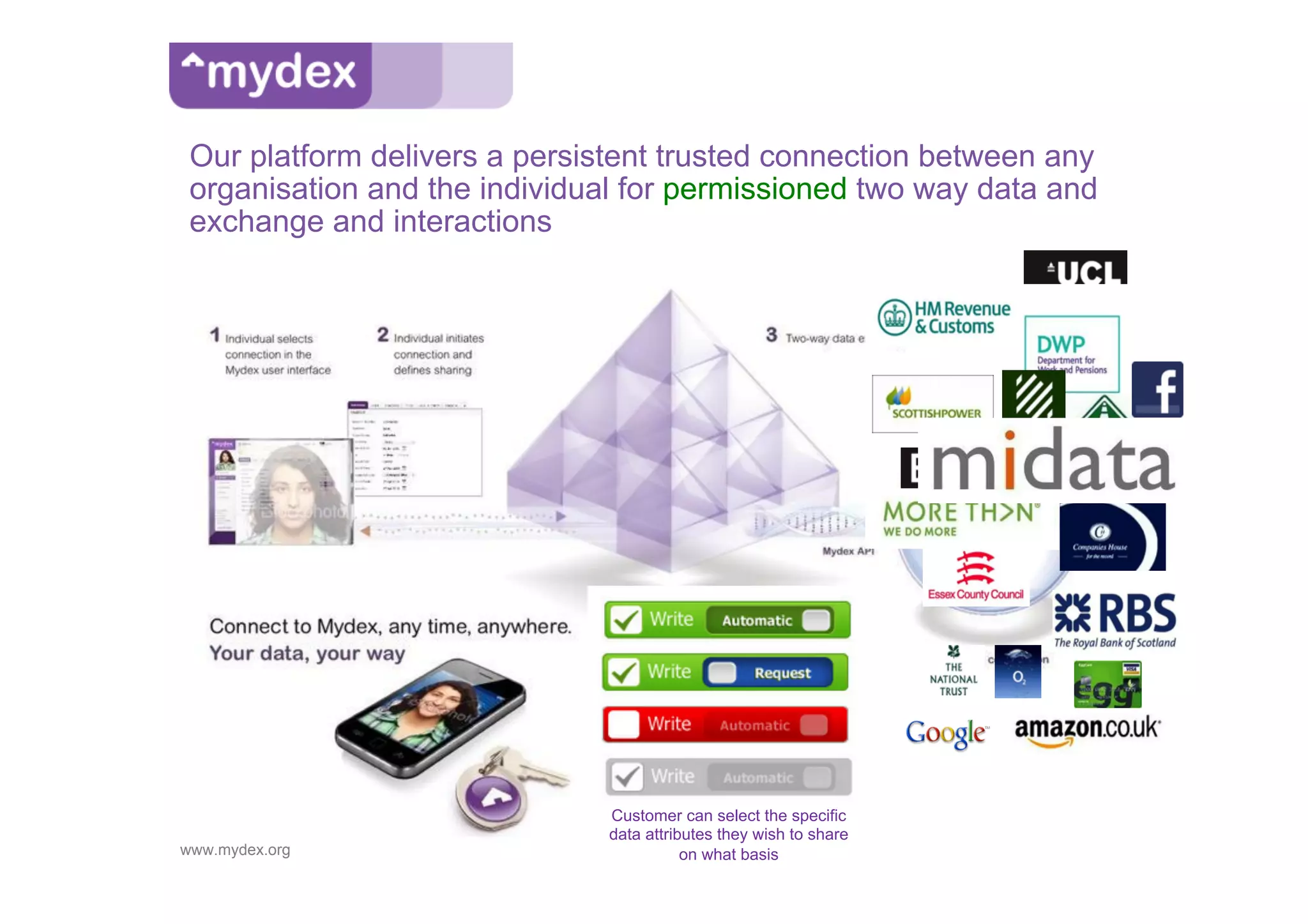
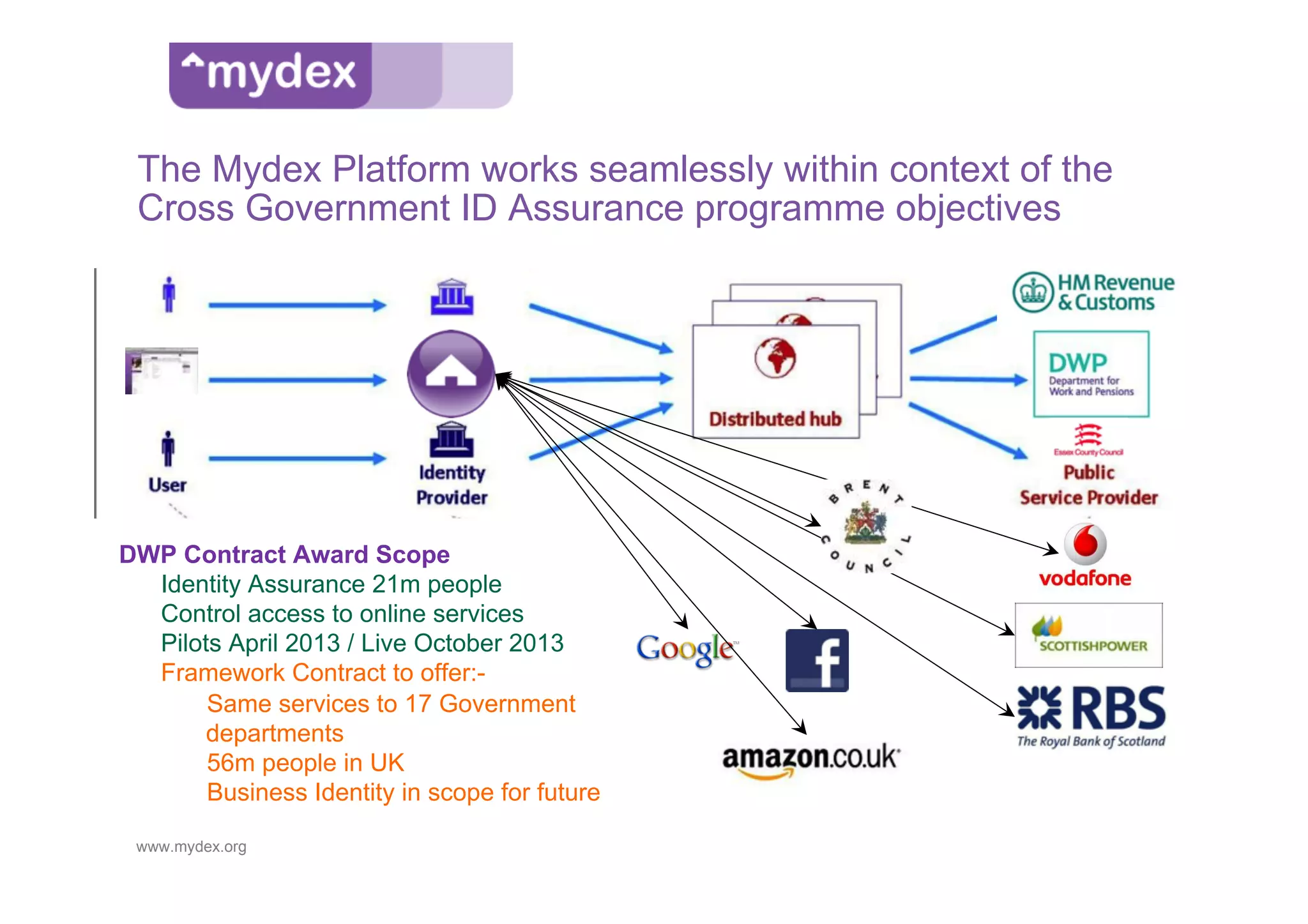
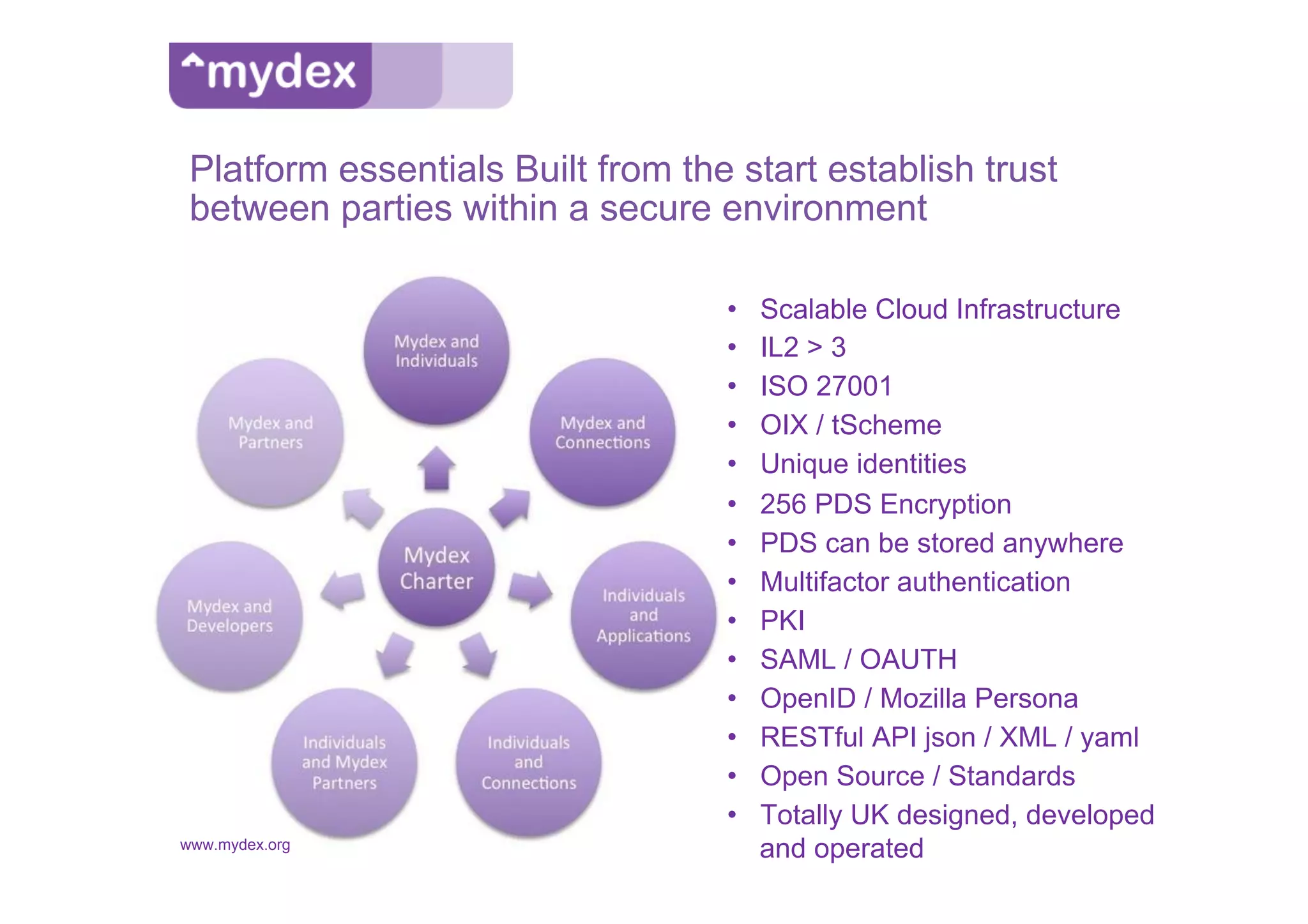
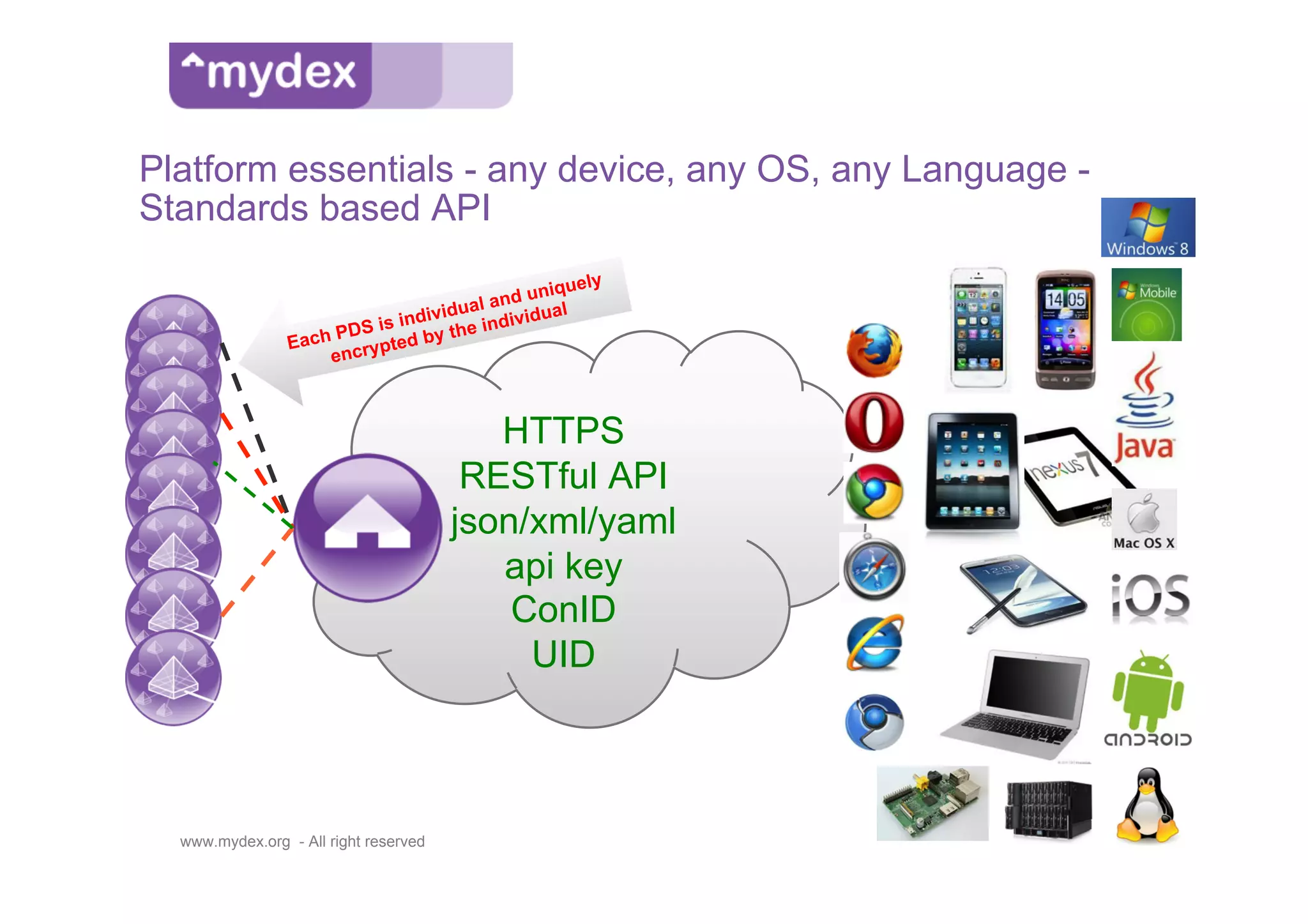
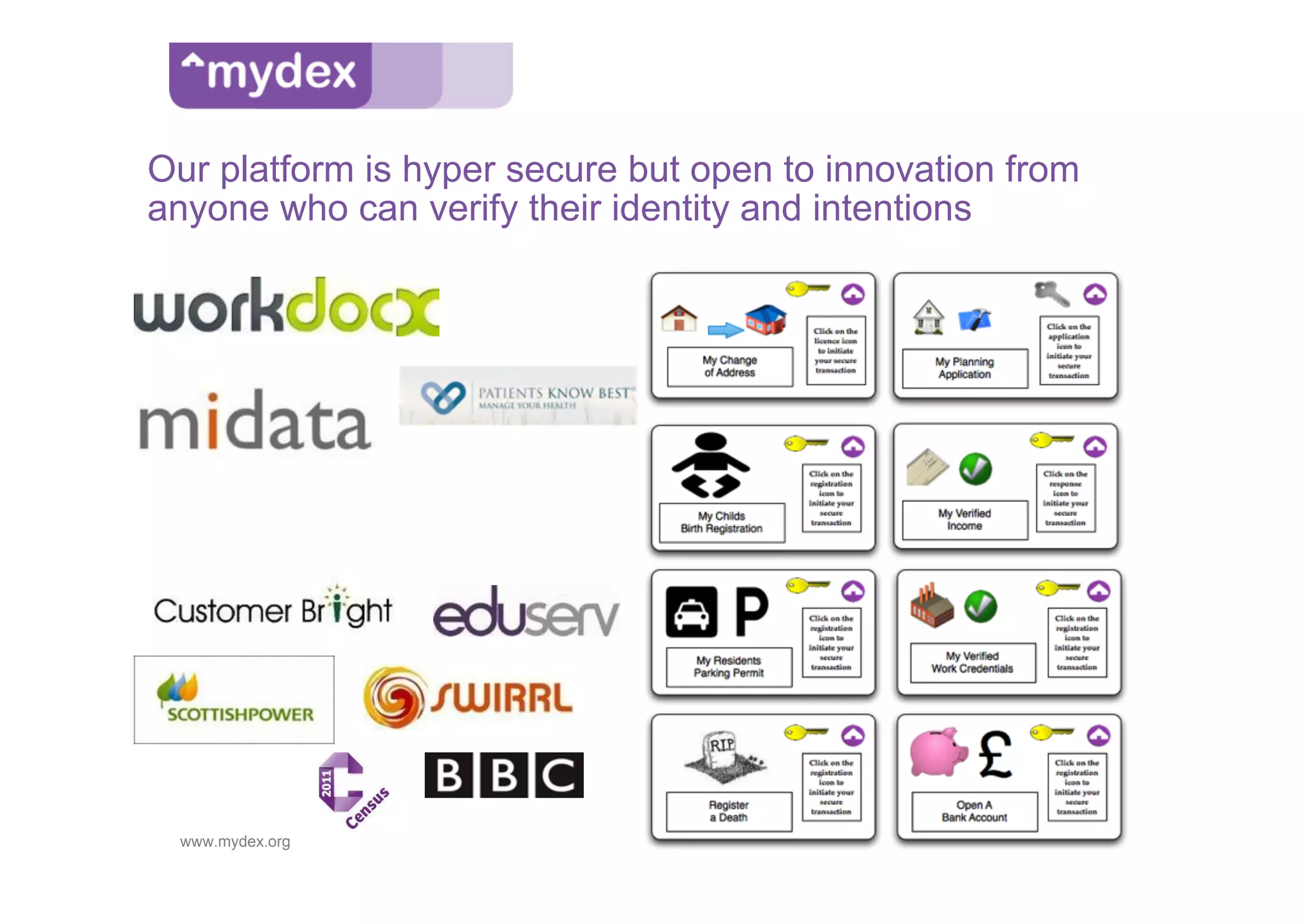
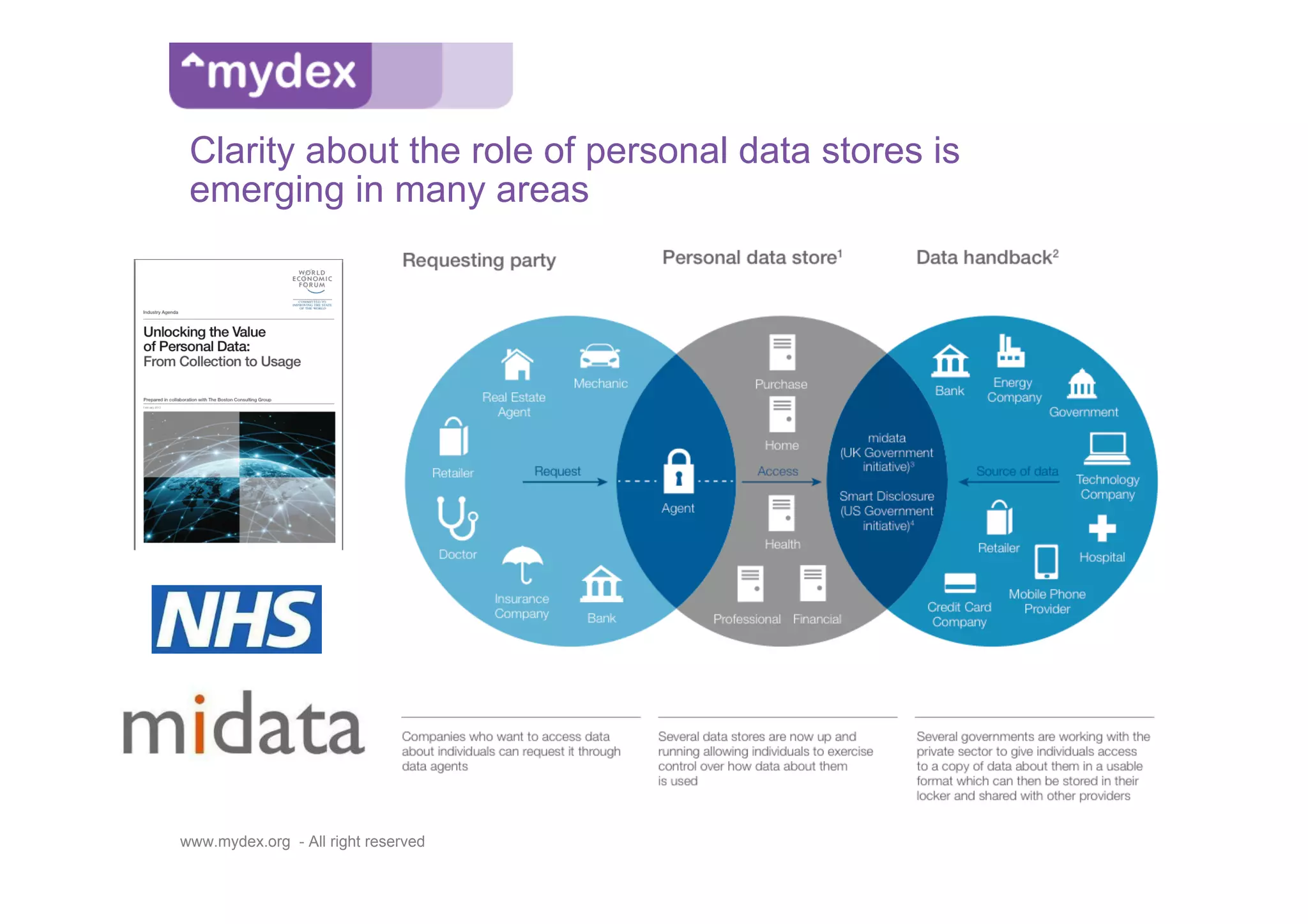
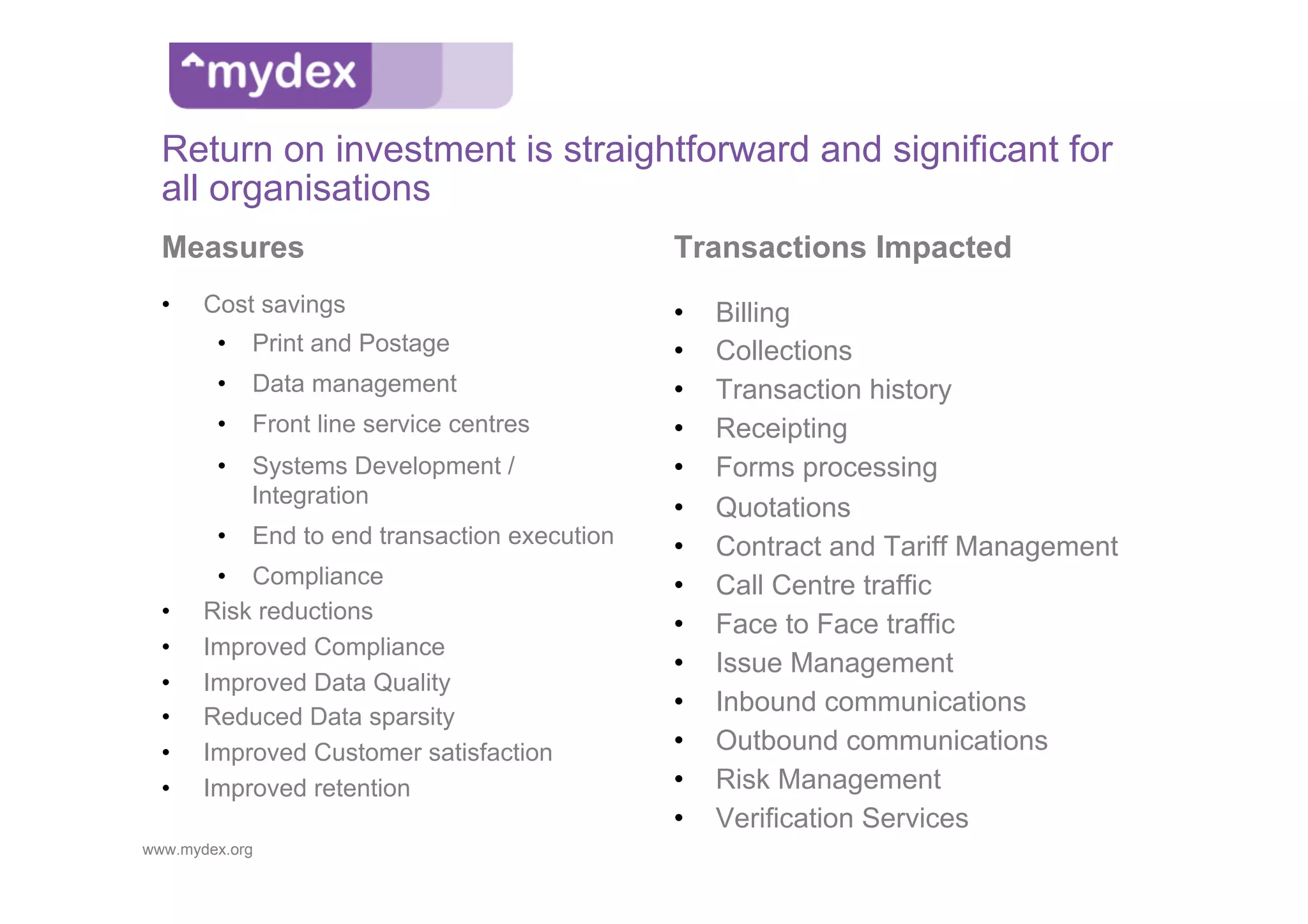
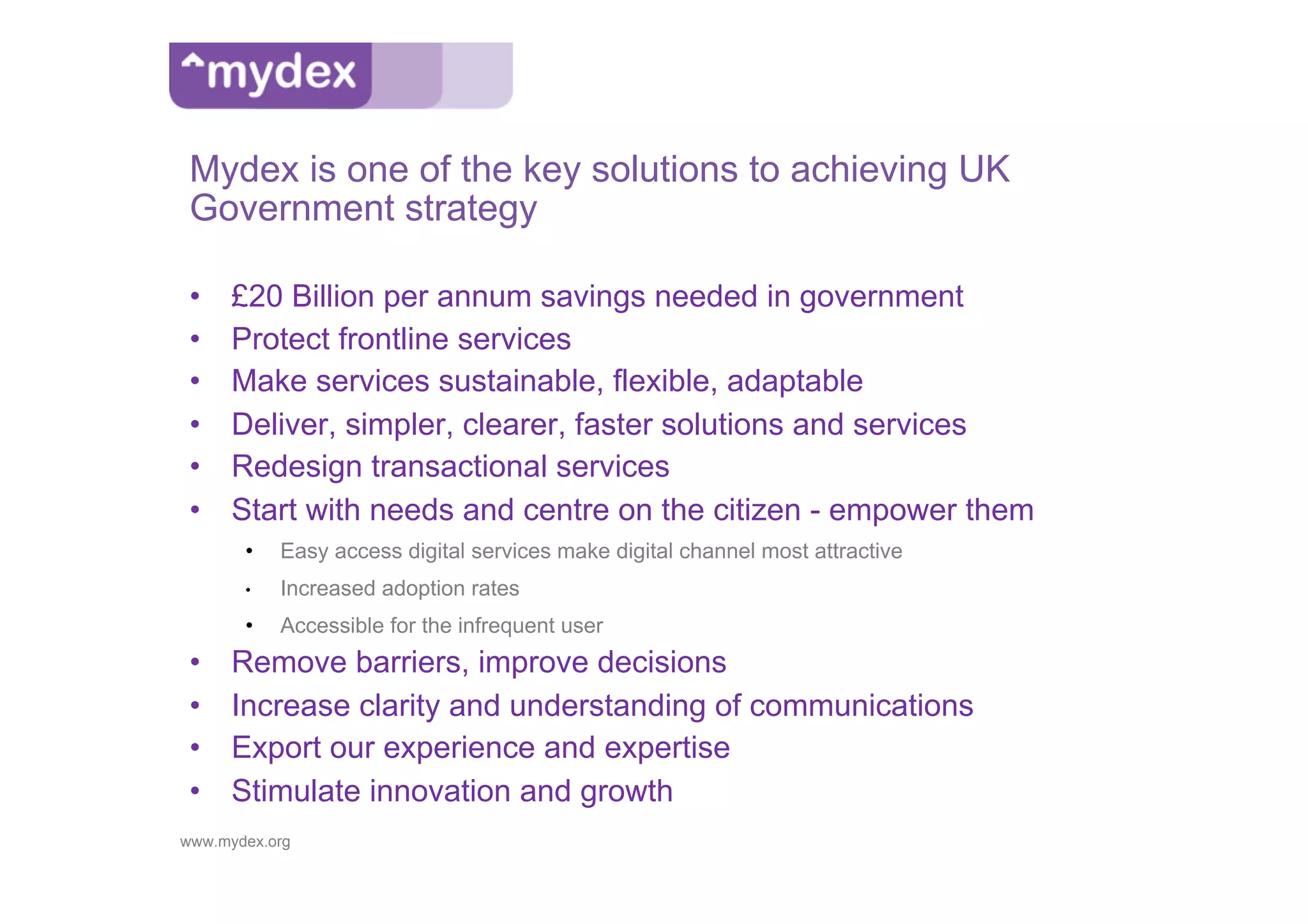
Mydex is a UK social enterprise established in 2007, focused on empowering individuals to manage their personal data securely while providing services to organizations and application developers. The platform offers a trusted identity framework, enabling streamlined customer engagement and effective data management through a personal data store, addressing challenges such as fraud prevention and data fragmentation. Mydex's commercial model is designed for sustainability, providing free services to individuals and low-cost connections for organizations, while ensuring data privacy and user control.