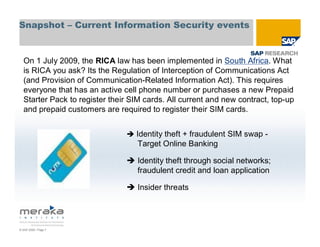
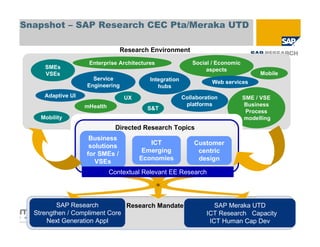
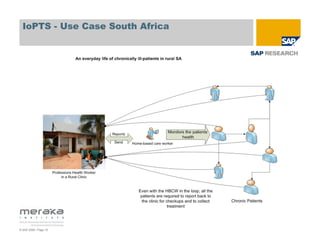
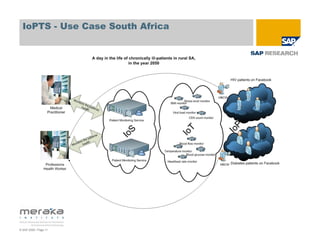
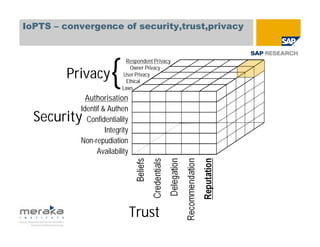
This document discusses Internet of People, Things and Services (IoPTS) security, trust and privacy from a South African perspective. It provides an overview of the current information security landscape and events in South Africa. It discusses how security, trust and privacy converge in IoPTS and outlines next steps for South Africa to create an IoPTS framework, including developing a research agenda and increasing international cooperation. The vision is to create a secure and trustworthy ICT environment that protects infrastructure and privacy while strengthening shared human values.