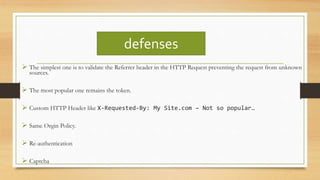
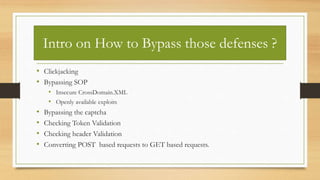
The document provides an overview of Cross-Site Request Forgery (CSRF) attacks, including their definition, impact, and testing methods. It outlines various defenses against CSRF and common misconceptions regarding their effectiveness, as well as techniques for bypassing these defenses. Additionally, it highlights the vulnerabilities of home DSL routers to CSRF exploits and mentions references for further reading.