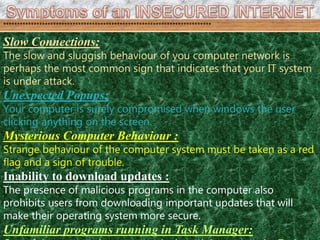
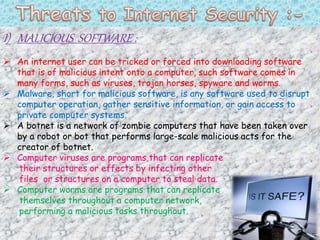
Internet security involves establishing rules and measures to protect against attacks over the Internet. It relates to securing browsers and network security across operating systems. The objective is to secure the exchange of information because the Internet represents an insecure channel with risks like phishing. Common signs of a compromised system include slow connections, popups, strange behavior, and inability to download updates. Malicious software, denial-of-service attacks, and phishing are major security threats. Defenses include antivirus software, encryption, secure connections, and multi-factor authentication.