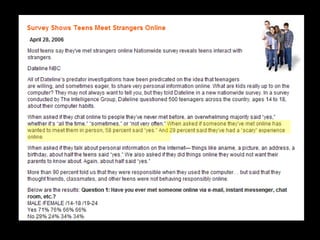
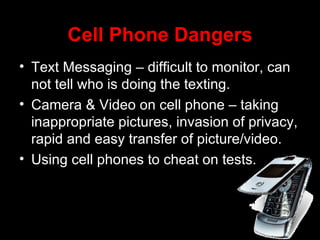
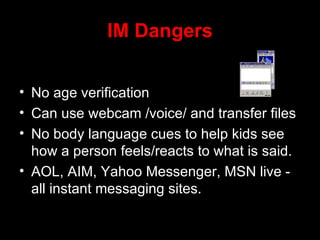
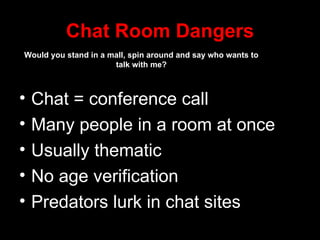
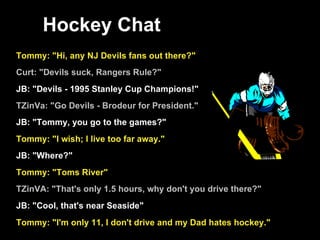
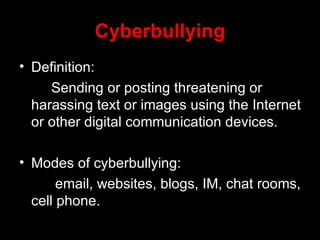
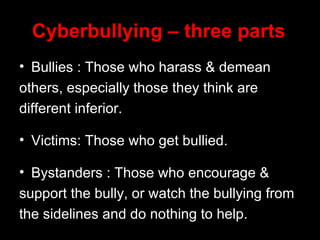
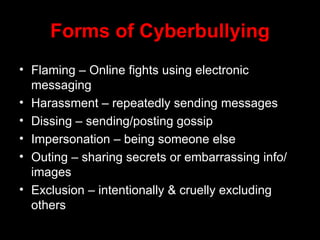
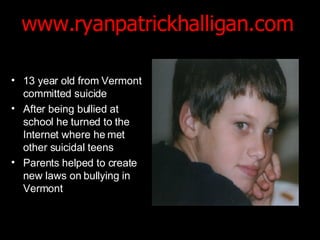
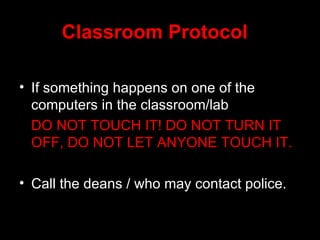
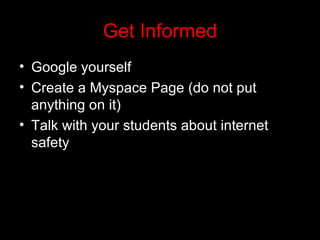
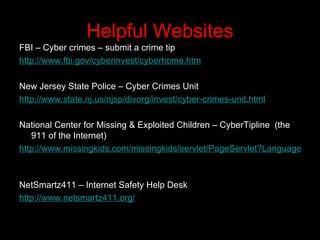
The document addresses various dangers students face online, including cyberbullying and interactions with predators on platforms like chat rooms and gaming consoles. It highlights the behavioral traits of online predators and the impact of cyberbullying on victims, emphasizing the need for better laws and proactive measures from parents and educators. Additionally, it provides resources for Internet safety and guidelines on how to handle incidents involving technology in educational settings.