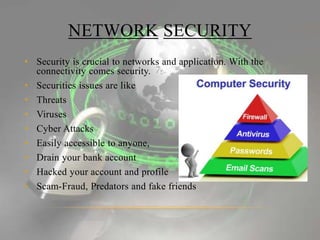
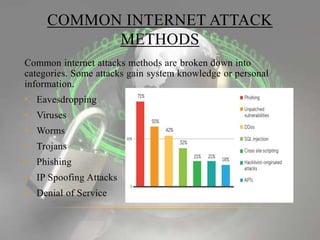
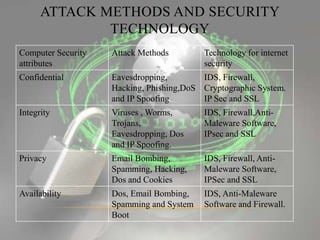
The document discusses the increasing importance of network security in the context of global internet connectivity and the various threats that arise, including eavesdropping, viruses, phishing, and denial of service attacks. It outlines security technologies such as firewalls, intrusion detection systems, and Secure Socket Layer (SSL) that are crucial to mitigate these threats. The conclusion emphasizes the growing focus on network security as the internet continues to expand.