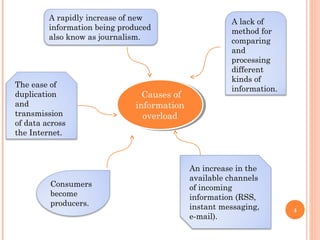
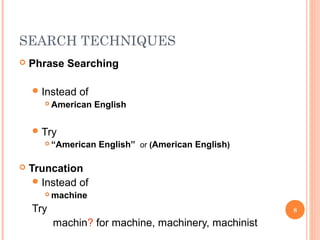
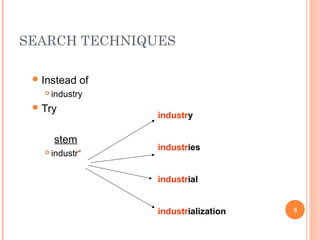
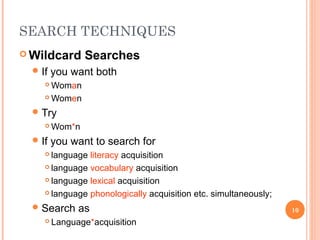
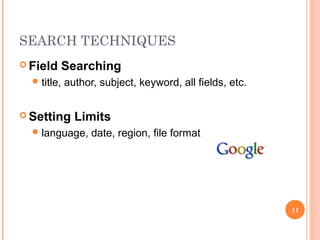
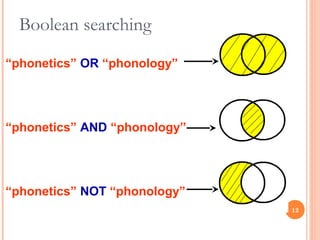
Information overload is the struggle to comprehend issues and make decisions due to excessive information input, often exacerbated by the rapid increase of new information and inadequate processing methods. Many workers report decreased productivity as they struggle to manage and prioritize information effectively. The document also outlines effective online search techniques such as phrase searching, truncation, and boolean searching to better navigate the information landscape.