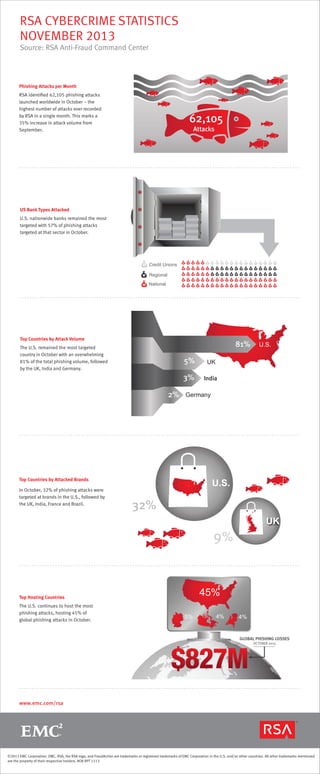
RSA Cybercrime Statistics : November 2013
•
1 like•1,150 views
E
EMCSource: RSA Anti-Fraud Command Center Read more on http://www.slideshare.net/emcacademics/wwwemccom-collateral-fraudreportrsaonlinefraudreport1113
Report
Share
Report
Share
Download to read offline
Recommended
Skeptics in the Church of Data: Getting Evangelical

Presented by Cage Data's Aaron Aldrich, DevOps Consultant and Evangelist.
Access the full presentation recordings for GalaxZ17 here: http://ow.ly/WyBu30cakk0
How secure is your company's information?

Do your employees know their responsibilities when it comes to your company's information security? Education is key when helping employees understand the risks that we all too often ignore. Take a look and find out how you can improve your security to keep your information from being at risk.
Creating a Global Bodyguard Network 

This presentation was given at the Unsummit in St. Paul, MN on June 18, 2011. It profiles the rise of a business from website idea to industry gem to global social powerhouse
DevSecOps - a 2 year journey of success & failure!

I've spent over 2 years at Skyscanner 'doing security stuff'. There have been lots of successes, but also some failure - here's a whistle-stop run-down!
What I learned from protecting over 1 million crypto traders and investors fr...

A few simple tips on how to avoid phishing scams.
Building a Highly Secure S3 Bucket

Amazon S3 probably gets a lot of use at your company—the object storage service was one of the first cloud services offered by AWS way back in 2006. Its ease of use, reliability, and scalability have proven incredibly popular over the years.
But S3 security isn’t so simple—it’s easy to get wrong and think you got it right. Recent high-profile cloud-based data breaches that involved S3 cannot be chalked up to simple customer mistakes. Rather, advanced cloud misconfiguration attacks exploit S3 buckets that otherwise appear to be configured securely.
In this talk, Fugue CTO Josh Stella will dig into the complex layers of S3 security to help you think critically about security for your unique AWS use cases. You’ll understand how other AWS services such as IAM and EC2 can create S3 vulnerabilities you may not be seeing—and how malicious actors exploit them.
Recommended
Skeptics in the Church of Data: Getting Evangelical

Presented by Cage Data's Aaron Aldrich, DevOps Consultant and Evangelist.
Access the full presentation recordings for GalaxZ17 here: http://ow.ly/WyBu30cakk0
How secure is your company's information?

Do your employees know their responsibilities when it comes to your company's information security? Education is key when helping employees understand the risks that we all too often ignore. Take a look and find out how you can improve your security to keep your information from being at risk.
Creating a Global Bodyguard Network 

This presentation was given at the Unsummit in St. Paul, MN on June 18, 2011. It profiles the rise of a business from website idea to industry gem to global social powerhouse
DevSecOps - a 2 year journey of success & failure!

I've spent over 2 years at Skyscanner 'doing security stuff'. There have been lots of successes, but also some failure - here's a whistle-stop run-down!
What I learned from protecting over 1 million crypto traders and investors fr...

A few simple tips on how to avoid phishing scams.
Building a Highly Secure S3 Bucket

Amazon S3 probably gets a lot of use at your company—the object storage service was one of the first cloud services offered by AWS way back in 2006. Its ease of use, reliability, and scalability have proven incredibly popular over the years.
But S3 security isn’t so simple—it’s easy to get wrong and think you got it right. Recent high-profile cloud-based data breaches that involved S3 cannot be chalked up to simple customer mistakes. Rather, advanced cloud misconfiguration attacks exploit S3 buckets that otherwise appear to be configured securely.
In this talk, Fugue CTO Josh Stella will dig into the complex layers of S3 security to help you think critically about security for your unique AWS use cases. You’ll understand how other AWS services such as IAM and EC2 can create S3 vulnerabilities you may not be seeing—and how malicious actors exploit them.
RSA Laboratories' Frequently Asked Questions About Today's Cryptography, Vers...

RSA Laboratories’ Frequently Asked Questions about Today's Cryptography was first published in 1992 and has been one of the most popular sections of RSA’s Web site. The latest revision, version 4.1 from the year 2000, still remains a valuable introduction to the field. Its content, however, no longer represents the state of the art.
The Industrial Internet@Work

The Industrial Internet is bringing about a profound transformation to global industry, by connecting more intelligent machines, advanced analytics, and people at work. This deeper meshing of the digital world with the world of machines has the potential to bring enormous economic benefits. We have estimated that this new wave of innovation could boost global GDP by as much as $10-15 trillion over the next 20 years, through accelerated productivity growth.
Discussions of the Industrial Internet tend to focus on the machines and the data, but people at work are an equally essential element of this revolution. In fact, it is exactly by changing the way people work that the Industrial Internet will deliver its benefts in terms of greater effciency, lower costs, and ultimately more and better jobs and rising living standards. Just as the Internet has fundamentally changed the ease with which we access information and interact with each other in our everyday lives, so the Industrial Internet will transform the way in which we can leverage information and collaborate in the workplace.
A Digital Eurovision for European Union

A Digital Eurovision for the European Union – the next step for European Public Service Broadcasting without frontiers. Why and how we must increase the availability of public service broadcasting to the widest Pan-European use.
This paper aims to initiate a discussion in Europe about the future of mass media in relation to the possibilities that can be achieved through technological development and policy innovation to stimulate the rise of a Pan-European identity across the European Union. By classifying current affairs reporting (news, current affairs and documentaries) produced by/for public service broadcasters (PSB) to fall within the definition of Open Government Data, European policy makers will unlock access to a wealth of European PSB content for European citizens, journalists and new start-ups to access, interact with, aggregate and disseminate. Such policy innovation not only comes with the already acknowledged economic benefits associated with open data and data-driven innovation; it also helps stimulate the creation of a strong Pan-European identity through increased Pan-European access to national stories, news and identity projections.
Mit2 092 f09_lec23

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
PyCon PL 2014 executable api

How do you keep your REST API documented? Online description? Or maybe a spreadsheet/doc? Think about how does your consumer discover it. Poor one is pasting URLs to curl or POSTman, right? And he’s mad as hell, as documentation is out of sync with code as soon as it’s written. Not to mention submitting bugs looks like an email ping-pong. It’s not 2010 any more, you know? Let’s jump into cool tools that will improve your consumers’ life and save you some time.
RSA Monthly Online Fraud Report -- October 2013

The RSA Monthly Online Fraud Report tracks phishing and cybercrime trends globally.
Read more
More Related Content
Viewers also liked
RSA Laboratories' Frequently Asked Questions About Today's Cryptography, Vers...

RSA Laboratories’ Frequently Asked Questions about Today's Cryptography was first published in 1992 and has been one of the most popular sections of RSA’s Web site. The latest revision, version 4.1 from the year 2000, still remains a valuable introduction to the field. Its content, however, no longer represents the state of the art.
The Industrial Internet@Work

The Industrial Internet is bringing about a profound transformation to global industry, by connecting more intelligent machines, advanced analytics, and people at work. This deeper meshing of the digital world with the world of machines has the potential to bring enormous economic benefits. We have estimated that this new wave of innovation could boost global GDP by as much as $10-15 trillion over the next 20 years, through accelerated productivity growth.
Discussions of the Industrial Internet tend to focus on the machines and the data, but people at work are an equally essential element of this revolution. In fact, it is exactly by changing the way people work that the Industrial Internet will deliver its benefts in terms of greater effciency, lower costs, and ultimately more and better jobs and rising living standards. Just as the Internet has fundamentally changed the ease with which we access information and interact with each other in our everyday lives, so the Industrial Internet will transform the way in which we can leverage information and collaborate in the workplace.
A Digital Eurovision for European Union

A Digital Eurovision for the European Union – the next step for European Public Service Broadcasting without frontiers. Why and how we must increase the availability of public service broadcasting to the widest Pan-European use.
This paper aims to initiate a discussion in Europe about the future of mass media in relation to the possibilities that can be achieved through technological development and policy innovation to stimulate the rise of a Pan-European identity across the European Union. By classifying current affairs reporting (news, current affairs and documentaries) produced by/for public service broadcasters (PSB) to fall within the definition of Open Government Data, European policy makers will unlock access to a wealth of European PSB content for European citizens, journalists and new start-ups to access, interact with, aggregate and disseminate. Such policy innovation not only comes with the already acknowledged economic benefits associated with open data and data-driven innovation; it also helps stimulate the creation of a strong Pan-European identity through increased Pan-European access to national stories, news and identity projections.
Mit2 092 f09_lec23

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
PyCon PL 2014 executable api

How do you keep your REST API documented? Online description? Or maybe a spreadsheet/doc? Think about how does your consumer discover it. Poor one is pasting URLs to curl or POSTman, right? And he’s mad as hell, as documentation is out of sync with code as soon as it’s written. Not to mention submitting bugs looks like an email ping-pong. It’s not 2010 any more, you know? Let’s jump into cool tools that will improve your consumers’ life and save you some time.
Viewers also liked (20)
RSA Laboratories' Frequently Asked Questions About Today's Cryptography, Vers...

RSA Laboratories' Frequently Asked Questions About Today's Cryptography, Vers...
What must a leader bear in mind when attempting to change workplace culture

What must a leader bear in mind when attempting to change workplace culture
Similar to RSA Cybercrime Statistics : November 2013
RSA Monthly Online Fraud Report -- October 2013

The RSA Monthly Online Fraud Report tracks phishing and cybercrime trends globally.
Read more
Symantec Cyber Security Intelligence Report

As reported in the ISTR Volume 19, 2013 saw a 500 percent increase in ransomware in the latter part of the year. Overall ransomware levels remained high through March 2014, and then slowly started to decline, in part due to the disruption of the GameOver Zeus botnet back in late May.
In contrast, crypto-style ransomware has seen a 700 percent-plus increase. These file-encrypting versions of ransomware began the year comprising 1.2 percent of all ransomware detec¬tions, but now make up 31 percent at the end of August. One variant known as Trojan.Cryptodefense began to appear in large numbers in early June. By the end of July, it made up 77 percent of all crypto-style ransomware for the year to date. This follows predictions in the ISTR saying this type of malware would become more common in 2014.
Over 31.5 million identities were reported exposed in August, from 12 incidents. The jump in exposed identities is due to a large breach in South Korea, comprising 27 million identities. In the last 12 months 53 percent of data breaches were caused by hacking and 21 percent were accidentally made public.
The average number of spear-phishing emails blocked each day for August was 20, compared with 54 in July and 88 in June. This is below the year-to-date average of 86, which is slightly higher than the daily average of 84 for all if 2013.
The most frequently used malicious file types in these email-based targeted attacks were .exe and .doc file types, with .exe attachments coming out on top this month at 31.8 percent. 29 percent of spear phishing emails were sent to Manufacturing, returning it to the top of the industries targeted.
One in 1,587 emails was identified as a phishing attempt, compared with one in 1,298 for July and one in 496 in June. While at first glance this looks like a big drop, it is not indica¬tive of a wider trend just yet, resulting in only a 0.01 percentage point decrease in the overall phishing rate.
We hope that you enjoy this month’s report and feel free to contact us with any comments or feedback.
Symantec Intelligence Report - Oct 2015

Explore this PDF to know Symantec intelligence report for OCT 2015 from Symantec Global Intelligence Network.
Enjoy this report and feel free to contact us with any comments or feedback.
Important points you have to note down from this report:
- The number of new malware
- Spam have been increasing over the last few month
- Finance, Insurance, & Real Estate sector was the most targeted sector in OCT month
Symantec Intelligence Report September 2014

Symantec Intelligence aims to provide the latest analysis of cyber security threats, trends, and insights concerning malware, spam, and other potentially harmful business risks.
The average number of spear-phishing attacks rose to 53 per day in September, after a 12-month low in August. Spear phishing activity has returned to levels seen earlier in the summer, but is still down from the 12-month average of 85 attacks per day.
The .doc file type was the most common attachment type used in spear-phishing attacks, making up more than 52.9 percent of all attachments in September. At 4.8 percent, last month’s top attachment, .exe file types, dropped to fourth.
There were only four publically disclosed data breaches that took place within the month September, resulting in the exposure of 2.5 million identities. However, there were 14 additional data breaches reported in September that took place earlier in the year. The largest data breach reported in September actually took place in April, and resulted in the exposure of 56 million identities.
Ransomware continues to decline as 2014 progresses. However, crypto-style ransomware remains high, making up 38 percent of all ransomware detected in September.
There were 600 vulnerabilities disclosed in the month of September, the highest number so far in 2014 and second highest in last 12 months.
One in 2,041 emails was identified as a phishing attempt, compared with one in 1,587 for August. While at first glance this looks like a big drop, it results in only a 0.01 percentage point decrease in the overall phishing rate.
Symantec Intelligence Report - July 2014

Welcome to the July edition of the Symantec Intelligence report. Symantec Intelligence aims to provide the latest analysis of cyber security threats, trends, and insights concerning malware, spam, and other potentially harmful business risks. Symantec has established the most comprehensive source of Internet threat data in the world through the Symantec Global Intelligence Network, which is made up of more than 41.5 million attack sensors and records thousands of events per second. This network monitors threat activity in over 157 countries and territories through a combination of Symantec products and services such as Symantec DeepSight Threat Management System, Symantec Managed Security Services, Norton consumer products, and other third-party data sources.
The average number of spear-phishing attacks per day has dropped back to a similar level seen in May. The .doc file type continues to be the most common attachment type used in spear-phishing attacks, followed by .exe files. Organizations with 2500+ employees were the most likely to be targeted, which non-traditional services, such as Business, Amusement, and Repair-related services, lead the Top-Ten Industries targeted, followed by Manufacturing.
The largest data breach reported in July resulted in the exposure of 900,000 identities. Hackers continue to be responsible for 49 % of data breaches over the last 12 months, most often exposing real names, government ID numbers, such as Social Security numbers, and home addresses in the data breaches. W32.Sality and W32.Ramnit variants continue to dominate the top-ten malware list. The most common OSX threat seen was OSX.RSPlug.A, making up 38 % of all OSX malware found on OSX Endpoints.
There were 575 vulnerabilities disclosed during the month of July, though no zero-day vulnerabilities discovered. Internet Explorer has reported the most browser vulnerabilities in the last 12 months, while Oracle’s Java reported the most plug-in vulnerabilities over the same time period.
There were four Android malware families discovered in July. Of the mobile threats discovered in the last 12 months, 24 % steal information from the device and 22 % track the device’s user. In terms of social networking scams, 63 % were fake offerings and 27 % were manually shared scams.
Finally, the phishing rate was down in July, at one in 1,299 emails, down from one in 496 emails in June. The global spam rate was 63.7 % for the month of July, one out of every 351 emails contained a virus, and of the email traffic in the month of July, 7.9 % contained a malicious URL. We hope that you enjoy this month’s report and feel free to contact us with any comments or feedback.
Symantec Intelligence Report November 2014

There was a significant jump in emails containing malicious URLs during the month of November, where 41 percent of emailborne malware contained a link to a malicious or compromised website. The last time we saw this level of activity was back in August of 2013. Since then, URL malware had been present in 3 to 16 percent of malicious emails each month, until this recent surge.
We have reason to believe that the Cutwail botnet is responsible for some of this increase. However, this botnet only makes up 3.7 percent of total botnet activity tracked in November. Kelihos and Gamut appear to be in the number one and two positions, comprising 19.2 and 18.8 percent respectively.
The topics in the campaigns we’ve seen so far include fake telecom billing notices, as well as fax and voicemail spam, and government levied fines. The URLs in the first two campaigns appear to be downloaders that will install further malware on a compromised computer, while the third campaign leads to fake captcha sites hosting crypto-ransomware.
Ransomware as a whole continues to decline as the year progresses. However, the amount of crypto-ransomware seen continues to comprise a larger portion of this type of malware. This particularly aggressive form of ransomware made up 38 percent of all ransomware in the month of November.
Phishing Report Gennaio 2010

I risultati del Report mensile sul Phishing condotto da Symantec e aggiornato a gennaio 2010
Symantec Intelligence Report - June 2014

The largest data breach reported in June resulted in the exposure up 1.3 million identities. This seems like a small number when compared to the 145 million exposed in the largest breach of May. However, while reported in June, this breach also took place during the month of May. This brings the total number of identities exposed in May to over 147 million, which is the second-worst month for data breaches in the last 12 months.
There was an average of 88 spear-phishing attacks per day in June. This appears to be a return of spear-phishing levels seen in the months of March and April, after the average per day dropped in May.
A relatively new OSX threat by the name of OSX.Stealbit.B topped our list of OSX malware, responsible for 25.7 percent of OSX threat found on OSX systems. This threat looks for specific bitcoin-related software on OSX computers and will attempt to modify the programs in order to steal bitcoins.
The number of Android variants per family reached the lowest levels seen in the last twelve months. While there was not a significant change in the number of families discovered in June, this may indicate that attackers have had more success with their current set of threats, reducing their need to create multiple variants.
June was a quiet month for vulnerabilities, where (only) 438 were reported—tying the lowest number reported in the last 12 months. There were no zero day vulnerabilities disclosed during the month.
Highlights from June 2014 Intelligence Report
Key Findings
There was an average of 88 spear-phishing attacks per day in June.
The number of Android variants per family reached the lowest levels seen in the last twelve months, at 18 variants per family.
The largest data breach reported in June took place in May, and resulted in the exposure of 1.3 million identities.
Symantec Intelligence Report - October 2014

The number of spear phishing attacks per day continues to trend downward over the last twelve months, coming in at 45 per day in October. Of the attachments used in such email-based attacks, the .doc attachment type comprised 62.5 percent and .exe attachments made up 14.4 percent. Of the industries attacked, the category of Finance, Insurance, and Real Estate received 28 percent of all spear phishing attempts in the month of October, followed by Manufacturing at 17 percent.
The largest data breach that was disclosed in October took place back in July. This breach had previously been reported; however, we learned this month that the breach resulted in the exposure of identities within 76 million households, plus information on an additional seven million small businesses.
In the Mac threat landscape, OSX.Okaz was the most frequently encountered OSX risk seen on OSX endpoints, making up 28.8 percent of OSX risks. OSX.Okaz is an adware program that may modify browser homepage and search settings.
Finally, ransomware as a whole continues to decline as the year progresses. However, the amount of crypto-style ransomware seen continues to increase. This particularly aggressive form of ransomware made up 55 percent of all ransomware in the month of October.
Security/Compliance - Advanced Threat Detection and Compliance

Trying to prioritize and roadmap effective cyber security investment—people and technology—without fully understanding the cyber threat landscape is like driving 70 MPH in the dark with the lights off while wearing sunglasses. Learn what trends and cyber threats CenturyLink sees globally and get ideas on how to shine a light on your corporation’s technical environment.
Rick Burger, Senior Solutions Architect, CenturyLink; Louie Hollmeyer, Moderator, ATC
Cyberattacks - Hurricane in Healthcare

Healthcare IT is talking about security only, question is WHY?
[Webinar Slides] The Simplest Route to Security and Compliance![[Webinar Slides] The Simplest Route to Security and Compliance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] The Simplest Route to Security and Compliance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Use these webinar slides to take a close look at some best practices for data privacy compliance, and assess how six large US-based multinational organizations are:
-Prioritizing GDPR compliance with other goals
-Assessing the risk posed by noncompliance
-Formalizing teams to address this and future mandates
-Revising data privacy models in a world where breaches continue to be the norm
Want to follow along with the webinar replay? Download it here for free: http://info.aiim.org/the-simplest-route-to-security-and-compliance
The Year in Phishing - RSA Fraud Report: January 2013

This monthly report, The Year in Phishing, highlights the latest fraud and phishing trends from RSA's Anti-Fraud Command Center.
Rising Menace of Phishing Attacks | Info Graphic | QPS

With 300,000 unique phishing attacks reported in the first half of 2017, organizations must evaluate prevention measures to mitigate the threat. As phishing becomes one of the frequently encountered fraud categories in businesses, QPS continues to be a sentinel for merchants and financial institutions in minimizing risks by implementing proactive fraud prevention measures.
Phishing Report Novembre 2009

I risultati del Report mensile sul Phishing condotto da Symantec aggiornato a novembre 2009
Similar to RSA Cybercrime Statistics : November 2013 (20)
The Executive's Guide to the 2016 Global Threat Intelligence Report

The Executive's Guide to the 2016 Global Threat Intelligence Report
Security/Compliance - Advanced Threat Detection and Compliance

Security/Compliance - Advanced Threat Detection and Compliance
[Webinar Slides] The Simplest Route to Security and Compliance![[Webinar Slides] The Simplest Route to Security and Compliance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] The Simplest Route to Security and Compliance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar Slides] The Simplest Route to Security and Compliance
The Year in Phishing - RSA Fraud Report: January 2013

The Year in Phishing - RSA Fraud Report: January 2013
Rising Menace of Phishing Attacks | Info Graphic | QPS

Rising Menace of Phishing Attacks | Info Graphic | QPS
More from EMC
INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD

CloudBoost is a cloud-enabling solution from EMC
Facilitates secure, automatic, efficient data transfer to private and public clouds for Long-Term Retention (LTR) of backups. Seamlessly extends existing data protection solutions to elastic, resilient, scale-out cloud storage
Cloud Foundry Summit Berlin Keynote 

Building a Cloud Foundry Dojo: A Model For Open Source Communities presented by Brian Gallagher, EMC Corporation
EMC GLOBAL DATA PROTECTION INDEX 

KEY FINDINGS & RESULTS FOR AMERICAS - GLOBALLY, ENTERPRISES ARE LOSING AS MUCH AS $1.7 TRILLION THROUGH DATA LOSS AND UNPLANNED DOWNTIME
Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO

With EMC XtremIO all-flash array, improve
1) your competitive agility with real-time analytics & development
2) your infrastructure agility with elastic provisioning for performance & capacity
3) your TCO with 50% lower capex and opex and double the storage lifecycle.
• Citrix & EMC XtremIO: Better Together
• XtremIO Design Fundamentals for VDI
• Citrix XenDesktop & XtremIO
-- Image Management & Storage
-- Demonstrations
-- XtremIO XenDesktop Integration
Citrix ready-webinar-xtremio

Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO
EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES 

Explore findings from the EMC Forum IT Study and learn how cloud computing, social, mobile, and big data megatrends are shaping IT as a business driver globally.
EMC with Mirantis Openstack

Reference architecture with MIRANTIS OPENSTACK PLATFORM.The changes that are going on in IT with disruptions from technology, business and culture and so IT to solve the issues has to change from moving from traditional models to broker provider model.
Force Cyber Criminals to Shop Elsewhere

Force Cyber Criminals to Shop Elsewhere
Learn the value of having an Identity Management and Governance solution and how retailers today are benefiting by strengthening their defenses and bolstering their Identity Management capabilities.
Pivotal : Moments in Container History 

Container-based technology has experienced a recent revival and is becoming adopted at an explosive rate. For those that are new to the conversation, containers offer a way to virtualize an operating system. This virtualization isolates processes, providing limited visibility and resource utilization to each, such that the processes appear to be running on separate machines. In short, allowing more applications to run on a single machine. Here is a brief timeline of key moments in container history.
Data Lake Protection - A Technical Review

This white paper provides an overview of EMC's data protection solutions for the data lake - an active repository to manage varied and complex Big Data workloads
Mobile E-commerce: Friend or Foe

This infographic highlights key stats and messages from the analyst report from J.Gold Associates that addresses the growing economic impact of mobile cybercrime and fraud.
Intelligence-Driven GRC for Security

This white paper describes how an intelligence-driven governance, risk management, and compliance (GRC) model can create an efficient, collaborative enterprise GRC strategy across IT, Finance, Operations, and Legal areas.
The Trust Paradox: Access Management and Trust in an Insecure Age

This white paper discusses the results of a CIO UK survey on a“Trust Paradox,” defined as employees and business partners being both the weakest link in an organization’s security as well as trusted agents in achieving the company’s goals.
Using EMC Symmetrix Storage in VMware vSphere Environments

This EMC Engineering TechBook describes how the VMware vSphere platform works with EMC Symmetrix storage systems and software technologies.
Using EMC VNX storage with VMware vSphereTechBook

This TechBook describes how VMware vSphere works with the EMC VNX family of storage systems.
More from EMC (20)
INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD

INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD
Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO

Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO
EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES 

EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES
The Trust Paradox: Access Management and Trust in an Insecure Age

The Trust Paradox: Access Management and Trust in an Insecure Age
Data Science and Big Data Analytics Book from EMC Education Services

Data Science and Big Data Analytics Book from EMC Education Services
Using EMC Symmetrix Storage in VMware vSphere Environments

Using EMC Symmetrix Storage in VMware vSphere Environments
Recently uploaded
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Recently uploaded (20)
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
RSA Cybercrime Statistics : November 2013
- 1. RSA CYBERCRIME STATISTICS NOVEMBER 2013 Source: RSA Anti-Fraud Command Center Phishing Attacks per Month RSA identified 62,105 phishing attacks launched worldwide in October – the highest number of attacks ever recorded by RSA in a single month. This marks a 35% increase in attack volume from September. 62,105 Attacks US Bank Types Attacked U.S. nationwide banks remained the most targeted with 57% of phishing attacks targeted at that sector in October. Credit Unions Regional National Top Countries by Attack Volume 81% The U.S. remained the most targeted country in October with an overwhelming 81% of the total phishing volume, followed by the UK, India and Germany. 5% 2% UK 3% India Germany Top Countries by Attacked Brands In October, 32% of phishing attacks were targeted at brands in the U.S., followed by the UK, India, France and Brazil. U.S. U.S. 32% UK 9% 45% Top Hosting Countries The U.S. continues to host the most phishing attacks, hosting 45% of global phishing attacks in October. 5% 4% 4% GLOBAL PHISHING LOSSES OCTOBER 2013 www.emc.com/rsa ©2013 EMC Corporation. EMC, RSA, the RSA logo, and FraudAction are trademarks or registered trademarks of EMC Corporation in the U.S. and/or other countries. All other trademarks mentioned are the property of their respective holders. NOV RPT 1113