Infocom 2013-2-state-markov
•
0 likes•838 views
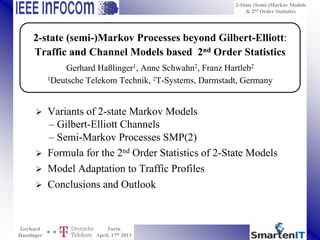
This document discusses 2-state Markov models and their use in modeling traffic variability and channel error profiles. It presents formulations for the second order statistics of 2-state Gilbert-Elliott channels, Markov processes, and semi-Markov processes. Measurement data from various traffic types is fitted using these models to demonstrate how a 2-state semi-Markov process with 6 parameters provides the best fit for the measured variability over time scales from 1ms to 10s. More complex models like the Gilbert-Elliott and self-similar processes have less flexibility with only one parameter for fitting second order statistics.
Report
Share
Report
Share
Download to read offline
Recommended
Process RTK Data Based On Kalman Filtering Algorithm

With the development of satellite positioning technology, there is a strong need for high accuracy
position information. Currently the most widely used high-precision positioning technology is RTK(Real-Time
Kinematic).RTK technology is the key to using carrier phase measurements. It takes advantage of the base
stations and monitor stations observed error of spatial correlation, except monitor stations observed by means of
differential most of the errors in the data, in order to achieve high accuracy positioning.[3]Based on Kalman
filtering algorithm to handle the noise of RTK data and selecting appropriate models to further improve the
accuracy of the data. This paper will explore the use of Kalman filtering method of RTK data processing, which
reduces random noise interference, thus improving the accuracy of GNSS deformation monitoring data.[1]
JGrass-Newage snow component

This documentation teaches how to run the snow component of JGrass-NewAge
JGrass-NewAge rain-snow separation

This documentation teaches how to run the rain-snow separation component of JGrass-NewAge
B.sc cs-ii-u-2.1-overview of register transfer, micro operations and basic co...

overview of register transfer, micro operations and basic computer organization and design
Real-time or full-precision CRS imaging using a cloud computing portal: multi...

Real-time or full-precision CRS imaging using a cloud computing portal: multi...CRS4 Research Center in Sardinia
CRS4, May 2015overview of register transfer, micro operations and basic computer organizati...

overview of register transfer, micro operations and basic computer organization and design
Analysing OpenStreetMap Data with QGIS

Presentation to UK QGIS South East User Group, 2nd April 2014 at Imperial College London
Recommended
Process RTK Data Based On Kalman Filtering Algorithm

With the development of satellite positioning technology, there is a strong need for high accuracy
position information. Currently the most widely used high-precision positioning technology is RTK(Real-Time
Kinematic).RTK technology is the key to using carrier phase measurements. It takes advantage of the base
stations and monitor stations observed error of spatial correlation, except monitor stations observed by means of
differential most of the errors in the data, in order to achieve high accuracy positioning.[3]Based on Kalman
filtering algorithm to handle the noise of RTK data and selecting appropriate models to further improve the
accuracy of the data. This paper will explore the use of Kalman filtering method of RTK data processing, which
reduces random noise interference, thus improving the accuracy of GNSS deformation monitoring data.[1]
JGrass-Newage snow component

This documentation teaches how to run the snow component of JGrass-NewAge
JGrass-NewAge rain-snow separation

This documentation teaches how to run the rain-snow separation component of JGrass-NewAge
B.sc cs-ii-u-2.1-overview of register transfer, micro operations and basic co...

overview of register transfer, micro operations and basic computer organization and design
Real-time or full-precision CRS imaging using a cloud computing portal: multi...

Real-time or full-precision CRS imaging using a cloud computing portal: multi...CRS4 Research Center in Sardinia
CRS4, May 2015overview of register transfer, micro operations and basic computer organizati...

overview of register transfer, micro operations and basic computer organization and design
Analysing OpenStreetMap Data with QGIS

Presentation to UK QGIS South East User Group, 2nd April 2014 at Imperial College London
JGrass-NewAge probabilities forward component 

This documentation teaches how to run the probabilities forward component of JGrass-NewAge
Jgrass-Newage net radiation component 

This documentation teaches how to run the net radiation component of JGrass-NewAge
Concurrent Ternary Galois-based Computation using Nano-apex Multiplexing Nibs...

Novel realizations of concurrent computations utilizing three-dimensional lattice networks and their corresponding carbon-based field emission controlled switching is introduced in this article. The formalistic ternary nano-based implementation utilizes recent findings in field emission and nano applications which include carbon-based nanotubes and nanotips for three-valued lattice computing via field-emission methods. The presented work implements multi-valued Galois functions by utilizing concurrent nano-based lattice systems, which use two-to-one controlled switching via carbon-based field emission devices by using nano-apex carbon fibers and carbon nanotubes that were presented in the first part of the article. The introduced computational extension utilizing many-to-one carbon field-emission devices will be further utilized in implementing congestion-free architectures within the third part of the article. The emerging nano-based technologies form important directions in low-power compact-size regular lattice realizations, in which carbon-based devices switch less-costly and more-reliably using much less power than silicon-based devices. Applications include low-power design of VLSI circuits for signal processing and control of autonomous robots.
JGrass-Newage clearness index

This documentation teaches how to run the clearness index component of JGrass-Newage
The Many Uses of FME at PNM

PNM's GIS department has been using FME Desktop (Workbench) since 2002, when they hired Safe to create some workspaces for a major gas data conversion project. The PNM employee who worked with Safe realized FME's potential and started spreading the word. Today, in 2016, several GIS professionals at the company employ FME, using it for various ends. These include data conversion, extracts, reports, analyses, data quality and improvement, and error checking. This presentation will provide a brief overview of the many ways we use FME at PNM, exploring a couple of projects in greater detail. Presented by Aaron Allen and Rene Carrillo from PNM.
Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...

Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...CRS4 Research Center in Sardinia
Viene presentato e discusso (in inglese) in dettaglio l'utilizzo della piattaforma EIAGRID/SmartGEO in due casi studio significativi per le applicazioni geotecniche e ambientali. Al termine, l'utente interessato dovrebbe essere in grado di utilizzare in modo autonomo la piattaforma attraverso il portale SmartGEO.Closed loop Control of grid Integrated High Frequency Linked Active Bridge Co...

Closed-loop Control of grid Integrated High-Frequency Linked Active Bridge Converter for multiple PV modules interfacing
Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...

Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...CRS4 Research Center in Sardinia
The presentation discusses a new method for imaging seismic data that was recently implemented on the SmartGeo cloud computing portal (https://smartgeo.crs4.it/enginframe/eiagrid/eiagrid.xml). The method is particularly suited for near-surface applications such as geotechnical engineering or environmental studies. It is shown that instead of limiting the stacking velocity analysis to single Common-Midpoint-Gathers, groups of neighboring Common-Midpoint-Gathers gathers are considered to identify entire reflection surfaces in the data. As a result the extracted kinematic properties of the subsurface, e.g. wave-propagation velocities, are more reliable and the final data stacking leads to a more detailed subsurface image even in case of noisy prestack data and laterally strongly variable velocities. In the second part of the presentation, the successful application of the proposed method is discussed in a case study based on a ultra-shallow seismic SH-wave data set recorded close to Teulada, Sardinia, Italy.JGrass-NewAge water budget 

This documentation teaches how to run the water budget component of JGrass-NewAge
JGrass-NewAge LongWave radiation Balance

This documentation teaches how to run the LWRB component of JGrass-NewAge
A Novel Route Optimized Cluster Based Routing Protocol for Pollution Controll...

https://irjet.net/archives/V4/i7/IRJET-V4I7401.pdf
JGrass-NewAge ET component

This documentation teaches how to run the evapotranspiration component of JGrass-NewAge
JGrass-Newage SWRB

This documentation teaches how to run the ShortWave Radiation Balance Component of JGrass-NewAge
The GRASS GIS software (with QGIS) - GIS Seminar

Introduction to GRASS and QGIS for newbies, 6 hours course with practical examples based on GRASS 6 and QGIS
32-bit unsigned multiplier by using CSLA & CLAA

In this project 31 % area delay product reduction is possible with the use of the CSLA based 32 bit unsigned parallel multiplier than CLAA based 32 bit unsigned parallel multiplier
More Related Content
What's hot
JGrass-NewAge probabilities forward component 

This documentation teaches how to run the probabilities forward component of JGrass-NewAge
Jgrass-Newage net radiation component 

This documentation teaches how to run the net radiation component of JGrass-NewAge
Concurrent Ternary Galois-based Computation using Nano-apex Multiplexing Nibs...

Novel realizations of concurrent computations utilizing three-dimensional lattice networks and their corresponding carbon-based field emission controlled switching is introduced in this article. The formalistic ternary nano-based implementation utilizes recent findings in field emission and nano applications which include carbon-based nanotubes and nanotips for three-valued lattice computing via field-emission methods. The presented work implements multi-valued Galois functions by utilizing concurrent nano-based lattice systems, which use two-to-one controlled switching via carbon-based field emission devices by using nano-apex carbon fibers and carbon nanotubes that were presented in the first part of the article. The introduced computational extension utilizing many-to-one carbon field-emission devices will be further utilized in implementing congestion-free architectures within the third part of the article. The emerging nano-based technologies form important directions in low-power compact-size regular lattice realizations, in which carbon-based devices switch less-costly and more-reliably using much less power than silicon-based devices. Applications include low-power design of VLSI circuits for signal processing and control of autonomous robots.
JGrass-Newage clearness index

This documentation teaches how to run the clearness index component of JGrass-Newage
The Many Uses of FME at PNM

PNM's GIS department has been using FME Desktop (Workbench) since 2002, when they hired Safe to create some workspaces for a major gas data conversion project. The PNM employee who worked with Safe realized FME's potential and started spreading the word. Today, in 2016, several GIS professionals at the company employ FME, using it for various ends. These include data conversion, extracts, reports, analyses, data quality and improvement, and error checking. This presentation will provide a brief overview of the many ways we use FME at PNM, exploring a couple of projects in greater detail. Presented by Aaron Allen and Rene Carrillo from PNM.
Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...

Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...CRS4 Research Center in Sardinia
Viene presentato e discusso (in inglese) in dettaglio l'utilizzo della piattaforma EIAGRID/SmartGEO in due casi studio significativi per le applicazioni geotecniche e ambientali. Al termine, l'utente interessato dovrebbe essere in grado di utilizzare in modo autonomo la piattaforma attraverso il portale SmartGEO.Closed loop Control of grid Integrated High Frequency Linked Active Bridge Co...

Closed-loop Control of grid Integrated High-Frequency Linked Active Bridge Converter for multiple PV modules interfacing
Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...

Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...CRS4 Research Center in Sardinia
The presentation discusses a new method for imaging seismic data that was recently implemented on the SmartGeo cloud computing portal (https://smartgeo.crs4.it/enginframe/eiagrid/eiagrid.xml). The method is particularly suited for near-surface applications such as geotechnical engineering or environmental studies. It is shown that instead of limiting the stacking velocity analysis to single Common-Midpoint-Gathers, groups of neighboring Common-Midpoint-Gathers gathers are considered to identify entire reflection surfaces in the data. As a result the extracted kinematic properties of the subsurface, e.g. wave-propagation velocities, are more reliable and the final data stacking leads to a more detailed subsurface image even in case of noisy prestack data and laterally strongly variable velocities. In the second part of the presentation, the successful application of the proposed method is discussed in a case study based on a ultra-shallow seismic SH-wave data set recorded close to Teulada, Sardinia, Italy.JGrass-NewAge water budget 

This documentation teaches how to run the water budget component of JGrass-NewAge
JGrass-NewAge LongWave radiation Balance

This documentation teaches how to run the LWRB component of JGrass-NewAge
A Novel Route Optimized Cluster Based Routing Protocol for Pollution Controll...

https://irjet.net/archives/V4/i7/IRJET-V4I7401.pdf
JGrass-NewAge ET component

This documentation teaches how to run the evapotranspiration component of JGrass-NewAge
JGrass-Newage SWRB

This documentation teaches how to run the ShortWave Radiation Balance Component of JGrass-NewAge
The GRASS GIS software (with QGIS) - GIS Seminar

Introduction to GRASS and QGIS for newbies, 6 hours course with practical examples based on GRASS 6 and QGIS
32-bit unsigned multiplier by using CSLA & CLAA

In this project 31 % area delay product reduction is possible with the use of the CSLA based 32 bit unsigned parallel multiplier than CLAA based 32 bit unsigned parallel multiplier
What's hot (20)
Concurrent Ternary Galois-based Computation using Nano-apex Multiplexing Nibs...

Concurrent Ternary Galois-based Computation using Nano-apex Multiplexing Nibs...
Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...

Near Surface Geoscience Conference 2014, Athens - Real-time or full‐precisi...
Closed loop Control of grid Integrated High Frequency Linked Active Bridge Co...

Closed loop Control of grid Integrated High Frequency Linked Active Bridge Co...
Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...

Near Surface Geoscience Conference 2015, Turin - A Spatial Velocity Analysis ...
A Novel Route Optimized Cluster Based Routing Protocol for Pollution Controll...

A Novel Route Optimized Cluster Based Routing Protocol for Pollution Controll...
NNPDF3.0: Next generation parton distributions for the LHC Run II

NNPDF3.0: Next generation parton distributions for the LHC Run II
Viewers also liked
Búsquedas del estado de la técnica 

Búsquedas del estado de la técnica
«Evitando reinventar la rueda»
(Linked) Open (Data) (Science)

Az előadás az első Budapest Open Knowledge meetup-on hangzott el 2014-ben.
FSA freshmen presentation 2012 

This is a summary of the presentation to the freshmen of 2012 at SZIE-ÁOTK by the FSA.
Chordspeller 2.0

Simple chart showing common chords found in piano, guitar and vocal music. The main page uses note names (like C-E-G-Bb) instead of notes. Also provides scale note formula (e.g. a major triad is "1 3 5") and common notation (e.g. "Dm7 = D major 7th") for all chords.
The (NEW!) second page presents standard treble clef notation for the 204 chords listed on page 1. Printed as double-sided, this chart can be as useful to those who read music as it is to those who do not.
204 chords explicitly listed, with formulae to create another 225 - all on one 8.5"x11" page! (Print page 2 and get treble clef notation for 204 chords.) Covers triads, sixths, sevenths, ninths and more!
(Created with open source tools: Open Office Writer for page 1 and Musescore for page 2.)
Moodle tips and tricks

Presentation from the IATEFL Poland conference, Bydgoszcz, 17-19.09.2010 - a selection of moodle tips and tricks, ranging from beginner to quite advanced moodle knowledge level.
Худшее в практике интранета

Перевод презентации "10 Worst practices for Intranets". Ее автор - Sam Marshall, директор ClearBox Consulting (UK). Речь идет о таких проблемах, как сложности поиска информации в интранете, отсутствие поддержки рабочих процессов и общения между сотрудниками, неуправляемое разрастание сайтов, преобладание "промо"- подхода в подаче информации, конфликт интересов разных поколений и др. Перевод публикую с согласия автора.
Læring i bevægelse på EUD

Skulle fremlægge for ledelsen, hvad forskningen siger om læring i bevægelse. Alle unge på EUD skal bevæge sig 30 min. hver dag.
Viewers also liked (20)
Similar to Infocom 2013-2-state-markov
International Journal of Computational Engineering Research(IJCER)

International Journal of Computational Engineering Research (IJCER) is dedicated to protecting personal information and will make every reasonable effort to handle collected information appropriately. All information collected, as well as related requests, will be handled as carefully and efficiently as possible in accordance with IJCER standards for integrity and objectivity.
Aw4102359364

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
Analysis of low pdp using SPST in bilateral filter

A FPGA Implementation of a bilateral filter for image processing is given which does spatial averaging without smoothing edges. Kernel based processing is possible, which means that processing of the entire filter window at one pixel clock cycle. It is also supported by the arrangement of the input data into groups and applied a single clock cycle for a group of pixels. Based on these features, a technique called Spurious Power Suppression Technique (SPST) is implemented in Bilateral Filter to minimize Power Delay Product (PDP). SPST can also dramatically reduce the power by turn off its MSP (Most significant bit) without compromising the computational results to achieve the target parameters. Furthermore, an Original Glitch Diminishing technique is proposed to filter out useless switching power by asserting signals after the data transient period. The SPST can be expanded to a Fine-grain scheme in which the combinational circuits are divided into more than two parts. In Bilateral Filter a kernel of different size can be implemented using SPST which achieve good performance.
Data Quality Analysis of Different Receivers Based on Static Base Station

ABSTRACT: With the global navigation and positioning system technology in various industries more and more widely used. As a result, higher requirements are made for the performance of GNSS receiver and the quality of receiving data. The quality of the received data is analyzed and compared to the receivers produced by different manufacturers. By comparison, The processing ability and data quality of different receivers for GNSS signals are analyzed. Data is collected for two different receiver from production M300Pro of ComNav and SPS 855 of Trimble. The quality analysis and discussion were carried out by using TEQC and CRU software respectively. The results show that the data quality of the two receivers conforms to the detection experience value, and is analyzed and compared by data quality. The two quality analysis software has Respective advantages. Combining different observation factors analysis that is important for the stable operation of the system and improving the positioning accuracy.
Real time traffic management - challenges and solutions

Presentation from NORTHMOST - a new biannual series of meetings on the topic of mathematical modelling in transport.
Hosted at its.leeds.ac.uk, NORTHMOST 01 focussed on academic research, to encourage networking and collaboration between academics interested in the methodological development of mathematical modelling applied to transport.
The focus of the meetings will alternate; NORTHMOST 02 - planned for Spring 2017 - will be led by practitioners who are modelling experts. Practitioners will give presentations, with academic researchers in the audience. In addition to giving a forum for expert practitioners to meet and share best practice, a key aim of the series is to close the gap between research and practice, establishing a feedback loop to communicate the needs of practitioners to those working in university research.
Updated-Traffic Simulation of Construction zone for Baranagar -.pptx

Microsimulation and traffic diversion Plan
PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001

PREDICTING THE TIME OF OBLIVIOUS PROGRAMS
The BSP model can be extended with a zero cost synchronization mechanism, which can be used when the number of messages due to receives is known. This mechanism, usually known as "oblivious synchronization" implies that different processors can be in different supersteps at the same time. An unwanted consequence of these software improvements is a loss of accuracy in prediction. This paper proposes an extension of the BSP complexity model to deal with oblivious barriers and shows its accuracy.
PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001

PREDICTING THE TIME OF OBLIVIOUS PROGRAMS
The BSP model can be extended with a zero cost synchronization mechanism, which can be used when the number of messages due to receives is known. This mechanism, usually known as "oblivious synchronization" implies that different processors can be in different supersteps at the same time. An unwanted consequence of these software improvements is a loss of accuracy in prediction. This paper proposes an extension of the BSP complexity model to deal with oblivious barriers and shows its accuracy.
Similar to Infocom 2013-2-state-markov (20)
International Journal of Computational Engineering Research(IJCER)

International Journal of Computational Engineering Research(IJCER)
International Journal of Computational Engineering Research(IJCER)

International Journal of Computational Engineering Research(IJCER)
Holistic Analysis and Optimization of Heterogeneous Fault-Tolerant Embedded S...

Holistic Analysis and Optimization of Heterogeneous Fault-Tolerant Embedded S...
07 image filtering of colored noise based on kalman filter

07 image filtering of colored noise based on kalman filter
Analysis of low pdp using SPST in bilateral filter

Analysis of low pdp using SPST in bilateral filter
Data Quality Analysis of Different Receivers Based on Static Base Station

Data Quality Analysis of Different Receivers Based on Static Base Station
Real time traffic management - challenges and solutions

Real time traffic management - challenges and solutions
Updated-Traffic Simulation of Construction zone for Baranagar -.pptx

Updated-Traffic Simulation of Construction zone for Baranagar -.pptx
PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001

PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001
PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001

PREDICTING THE TIME OF OBLIVIOUS PROGRAMS. Euromicro 2001
More from SmartenIT
Assessing Effect Sizes of Influence Factors Towards a QoE Model for HTTP Adap...

Tobias Hoßfeld, Michael Seufert, Christian Sieber, Thomas Zinner
Assessing Effect Sizes of Influence Factors Towards a QoE Model for HTTP Adaptive Streaming.
6th International Workshop on Quality of Multimedia Experience (QoMEX), Singapore, September 2014.
Abstract:
HTTP Adaptive Streaming (HAS) is employed by more and more video streaming services in the Internet. It allows to adapt the downloaded video quality to the current network conditions, and thus, avoids stalling (i.e., playback interruptions) to the greatest possible extend. The adaptation of video streams is done by switching between different quality representation levels, which influences the user perceived quality of the video stream. In this work, the influence of several adaptation parameters, namely, switch amplitude (i.e., quality level difference), switching frequency, and recency effects, on Quality of Experience (QoE) is investigated. Therefore, crowdsourcing experiments were conducted in order to collect subjective ratings for different adaptation-related test conditions. The results of these subjective studies indicate the influence of the adaptation parameters, and based on these findings a simplified QoE model for HAS is presented, which only relies on the switch amplitude and the playback time of each layer.
An Automatic and On-demand MNO Selection Mechanism

A manual selection of the Mobile Network Operator (MNO) to be used on a mobile device is possible through the respective user interface. Furthermore, mobile devices can be adjusted to select automatically the MNO based on the strongest signal strength, among the list of those MNOs the Subscriber Identity Module (SIM) card is allowed to be registered with. However, so far in modern mobile operating systems, such as Android and iOS, there is no available method in the public developer’s Application Programming Interface (API), which allows for an automatic and on-demand selection of the MNO by third- party applications. Recently, various research approaches assume the existence of an automatic and on-demand MNO selection mechanism to achieve different goals, such as breaking the termination rates monopoly (AbaCUS) or minimizing the non-ionizing radiation of mobile/wearable devices. The interest of such a mechanism has been raised three years ago by the Android developers community. Thus, this work here presents an automatic and on-demand MNO selection mechanism, that has been designed and implemented on the Android platform. For evaluation purposes the energy and end-to-end (e2e) time consumption while switching among MNOs using this mechanism is evaluated and as an applied example the data consumption of AbaCUS signaling messages is measured.
Gamification Framework for Personalized Surveys on Relationships in Online So...

Michael Seufert, Karl Lorey, Matthias Hirth, Tobias Hoßfeld
Gamification Framework for Personalized Surveys on Relationships in Online Social Networks.
1st International Workshop on Crowdsourcing and Gamification in the Cloud (CGCloud), Dresden, Germany, December 2013.
Abstract:
The estimation of psychological properties of relationships (e.g., popularity, influence, or trust) only from objective data in online social networks (OSNs) is a rather vague approach. A subjective assessment produces more accurate results, but it requires very complex and cumbersome surveys. The key contribution of this paper is a framework for personalized surveys on relationships in OSNs which follows a gamification approach. A game was developed and integrated into Facebook as an app, which makes it possible to obtain subjective ratings of users' relationships and objective data about the users, their interactions, and their social network. The combination of both subjective and objective data facilitates a deeper understanding of the psychological properties of relationships in OSNs, and lays the foundations for future research of subjective aspects within OSNs.
Socially-aware Traffic Management (Workshop Sozioinformatik)

Talk on "Socially-aware Traffic Management" given by Michael Seufert (http://www3.informatik.uni-wuerzburg.de/staff/michael.seufert/) at the workshop Sozioinformatik 2013 (http://www.sozioinformatik2013.de/, organized by Katharina Anna Zweig; held in conjunction with Jahrestagung der Gesellschaft für Informatik (INFORMATIK 2013)). The workshop addressed questions evolving around the interplay between social and technical systems, and bridged the gap from social sciences to computer sciences. The workshop talks gave an overview on different aspects of interactions between humans and IT-systems, and highlighted the need for a combination of social sciences and computer science in this field. The workshop showed that it is possible and sometimes necessary to integrate social studies into the design and application of IT-systems. This applies to SmartenIT especially in the context of socially-aware traffic management.
Michael Seufert, George Darzanos, Valentin Burger, Ioanna Papafili, Tobias Hoßfeld
Socially-Aware Traffic Management.
Workshop Sozioinformatik 2013, Koblenz, Germany, September 2013.
Abstract:
Socially-aware traffic management exploits social signals to optimize traffic management in the Internet in terms of traffic load, energy consumption, or end-user satisfaction. Several use cases can benefit from socially-aware traffic management and the performance of overlay applications can be enhanced. In the talk we show interdisciplinary efforts between communication networks and social network analysis. Specifically, we give an overview on existing use cases and solutions, but also raise discussions at the workshop on additional benefits from the integration of social information into traffic management.
More from SmartenIT (13)
Assessing Effect Sizes of Influence Factors Towards a QoE Model for HTTP Adap...

Assessing Effect Sizes of Influence Factors Towards a QoE Model for HTTP Adap...
A Deterministic QoE Formalization of User Satisfaction Demands (DQX)

A Deterministic QoE Formalization of User Satisfaction Demands (DQX)
Towards Evaluating Type of Service Related Quality-of-Experience on Mobile Ne...

Towards Evaluating Type of Service Related Quality-of-Experience on Mobile Ne...
An Automatic and On-demand MNO Selection Mechanism

An Automatic and On-demand MNO Selection Mechanism
Traffic Profiles and Management for Support of Community Networks

Traffic Profiles and Management for Support of Community Networks
Evaluation of Caching Strategies Based on Access Statistics on Past Requests

Evaluation of Caching Strategies Based on Access Statistics on Past Requests
Gamification Framework for Personalized Surveys on Relationships in Online So...

Gamification Framework for Personalized Surveys on Relationships in Online So...
Socially-aware Traffic Management (Workshop Sozioinformatik)

Socially-aware Traffic Management (Workshop Sozioinformatik)
Recently uploaded
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Recently uploaded (20)
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Infocom 2013-2-state-markov
- 1. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Variants of 2-state Markov Models – Gilbert-Elliott Channels – Semi-Markov Processes SMP(2) Formula for the 2nd Order Statistics of 2-State Models Model Adaptation to Traffic Profiles Conclusions and Outlook 2-state (semi-)Markov Processes beyond Gilbert-Elliott: Traffic and Channel Models based 2nd Order Statistics Gerhard Haßlinger1, Anne Schwahn2, Franz Hartleb2 1Deutsche Telekom Technik, 2T-Systems, Darmstadt, Germany
- 2. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Good State Bad State q Gilbert-Elliott channel: 4 parameters (p,q,hG,hB) 1 – p1 – q p Good State Bad State q, hGB 2-state Markov process with transition specific rates: 6 parameters (p,q,hGG,hGB,hBG,hBB) 1 – p hBB 1 – q hGG p, hBG State G q 2-state semi-Markov process for traffic rate distributions RG();RB()6 param. (p,q,G,G 2,B,B 2) in 2nd order statistics 1 – p1 – q p hG hB RG(); G;G 2 State B RB(); B;B 2 Good State Bad State q Gilbert-Elliott channel: 4 parameters (p,q,hG,hB) 1 – p1 – q p Good State Bad State q, hGB 2-state Markov process with transition specific rates: 6 parameters (p,q,hGG,hGB,hBG,hBB) 1 – p hBB 1 – q hGG p, hBG State G q 2-state semi-Markov process for traffic rate distributions RG();RB()6 param. (p,q,G,G 2,B,B 2) in 2nd order statistics 1 – p1 – q p hG hB RG(); G;G 2 State B RB(); B;B 2 2-State (semi-)Markov Processes
- 3. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Application spectrum of 2-state Markov models Traffic profiles, dimensioning for QoS/QoE demands - many papers on measurement of traffic profiles - many papers on queueing analysis with 2-(M-)state Markov input Error channel modeling - many papers on channel profiles (e.g., Rician fading, etc.) - some papers on error models for packets, data blocks of protocols - many papers on performance of error-detecting/correcting codes Application examples in other disciplines - in economics: for volatility in markets - in nuclear physics: for electron spin signals - in statistics of medicine: for estimation of misclassification - in documentation: for modeling of image degradation - analytical verification of simulations etc.
- 4. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Measured 2nd order statistics over several time scales = 1 10 100 1000 0,0 0,5 1,0 1,5 2,0 0,001 0,01 0,1 1 10 100 1000 Time Scale [s] StandardDeviation/MeanRate Twitter Facebook Uploaded VoIP YouTube Total Traffic = 1 10 100 1000 0,0 0,5 1,0 1,5 2,0 0,001 0,01 0,1 1 10 100 1000 Time Scale [s] StandardDeviation/MeanRate Twitter Facebook Uploaded VoIP YouTube Total Traffic
- 5. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 )( )1(1 1 )1(2 1 2 2 qpN qp qp qp N N N Results for the 2nd order statistics 2. 2-state Markov with ;2222 H N N1. Self-similar traffic: Adaptation to traffic profile with mean rate and variance on smallest measurement time scale (1ms time slots): G, B are determined , only one parameter p+q remains free in the 2nd order statistics Remark: 2nd order statistics is equivalent to autocorrelation function 3 Parameters: , , H H: Hurst Parameter (0.5 < H < 1) 4 Parameters: p, q, G, B constant rate in each state:
- 6. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Results for the 2nd order statistics )( )1(1 1)( 11 2222 qpN qp qp qp N N N 3. Markov modulated Poisson process MMPP(2) (22): 4. Semi-Markov process SMP(2): ; )( )(2 ; )( )1(1 11 ][ )( 2 22 ][ GBBG BGBG N N qp EE qp EEpq qpN qp N .)1( ;)1( BGBBB GBGGG ppE qqE 4 Parameters: p, q, G, B (G 2=G 2, B 2=B 2); only one parameter p+q remains free in the 2nd order statistics 6 Parameters: p, q, G, B, G, B; or 10 param.: p, q, GG, GB, GB, BB, GG, GB, GB, BB 2 parameters , p+q remain free in the 2nd order statistics
- 7. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 SMP(2) Fitting of 2nd Order Statistics 0 5 10 15 20 25 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale StandardDeviation[Mb/s] 2-state SMP (p=5q=0.00001) 2-state SMP (p=5q=0.0005) 2-state SMP (p=5q=0.0028) 2-state SMP (p=5q=0.05) Measurement Result 2-sate SMP (p=5q=5/6) 1. Step of parameter fitting: p/q = 5 is const.; p+q is variable Monotonous increase of 2 8192 for p+q 0; match at p = 5q = 0.0028
- 8. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 SMP(2) Fitting of 2nd Order Statistics 2. Step of parameter fitting: p/q is variable; 2 8192 is kept constant; Monotonous decrease of N=0 13 2 2N; best match for p/q = 0.0013 0 50 100 150 200 250 300 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale Standarddeviation[Mb/s] SMP(2) with p/q = 0.405 (max.) SMP(2) with p/q = 0.1 SMP(2) with p/q = 0.04 Measurement Result SMP(2) with p/q = 0.013 SMP(2) with p/q = 0.00923 (min.)
- 9. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Fitting of the 2nd order statistics for YouTube traffic 0 40 80 120 160 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale Standarddeviation[Mb/s] Fixed Rate per State Self-Similar Process MMPP(2) Measurement Result SMP(2) All models are fitted to µ, 1 2 and 2 8192; A least mean square deviation criterion could be fitted in a 3. step, which isn´t monotonous optimization
- 10. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Fitting of the 2nd order statistics for Facebook traffic 0 5 10 15 20 25 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale StandardDeviation[Mb/s] Fixed Rate per State MMPP(2) Self-Similar Process Measurement Result SMP(2)
- 11. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Fitting of the 2nd order statistics for RapidShare traffic 0 5 10 15 20 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale Standarddeviation[Mb/s] Fixed Rate per State Self-Similar Process MMPP(2) Measurement Result SMP(2)
- 12. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Fitting of the 2nd order statistics for the total traffic MMPP(2) fitting curve is missing, since 1 2 < µ2 cannot be achieved 0 50 100 150 200 250 300 0.001s 0.004s 0.016s 0.064s 0.256s 1.024s 8.192s Time scale Standarddeviation[Mb/s] Fixed Rate per State Self-Similar Process Measurement Result SMP(2)
- 13. 2-State (Semi-)Markov Models & 2nd Order Statistics Gerhard Hasslinger Turin April, 17th 2013 Conclusions on 2-state traffic models Explicit formula for the 2nd order statistics of 2-state (semi-)Markov SMP(2) processes clearly reveals impact of parameters - More complex Eigenvalue solutions for N-state Markov SMP(2) model variants with 6 parameters provide a 2-dimensional adaptation space (p, q) fairly good fitting of measured traffic variability in times scales from 1ms to 10s Gilbert-Elliott, MMPP(2) and self-similar models have only one parameter for 2nd order adaptation only coarse fitting accuracy for measured traffic variability Traffic models of superposed or otherwise combined 2-state models have potential for improvement
