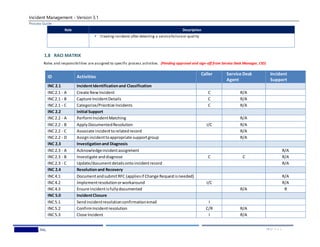
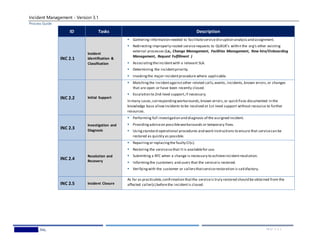
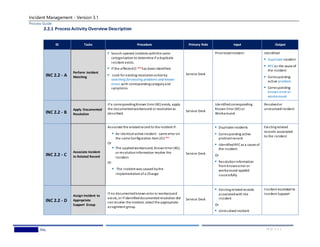
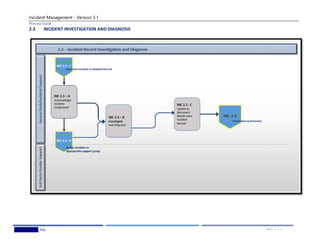
This document provides guidelines for Wedgewood Inc.'s incident management process. It describes the process goals as restoring normal service operation quickly and minimizing business impact from incidents. Key activities are identified as incident identification and classification, initial support, investigation and diagnosis, resolution and recovery, and closure. Roles and responsibilities are defined for various positions along with metrics for monitoring process performance.














![Incident Management - Version 3.1
Process Guide
Wedgewood,Inc. 26 | P A G E
APPENDIX B: INCIDENT CATEGORIZATIONS
Incidentcategorization is commonly used to drive assignmentin the incidentmanagement process as well as establish trends (incidenttypes/frequencies) for use in
problem management, supplier management and other ITSM activities.
This method of categorization requires the creator of the incident to manually select the category and subcategory from predefined lists.
It is possibleto automatically categorizeand assign the incidentbased on the Configuration Item (or CI) that is identified in the incidentrecord. With this technique,
the incidentmanagement process inherits thesamecategorization schema as CIs maintained through the configuration management process and the category of an
incidentis automatically determined once the affected CI is identified in the incidentrecord. This technique ensures more accurateand consistentcategorization of
incidents and supports a CI-centric approach to IT service management.].
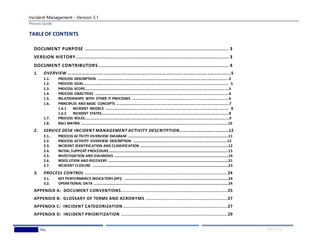
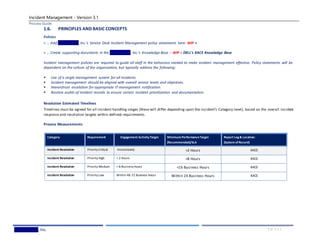
APPENDIX C: INCIDENT PRIORITIZATIONS
Incidentprioritization typically drives thetimescales associated with the handlingof the incidentand the targeted time to resolution.There are a couple of
methods that can be used to determine priority.
ITIL recommends that PRIORITY be considered a dependent on impactand urgency, where:
IMPACT is the effect that an incidenthas on business.
URGENCY is the extent to which the incident's resolution can bear delay.
PRIORITY is generated from urgency and impactaccordingto the followingtable
UrgencyHigh UrgencyMedium UrgencyLow
Impact High Priority 1 Priority 2 Priority 3
Impact Medium Priority 2 Priority 3 Priority 4
Impact Low Priority 3 Priority 4 Priority 5
** It is possible to automatically establish the priority of the incident based on the Configuration Item (or CI) that is identified in the incidentrecord. With this technique,
the business criticality value of the CI is used to determine the priority of the incident. This ensures a more accurate and consistent prioritization of incidents, as the
determination of impact and urgency can be a subjective call.](https://image.slidesharecdn.com/bf8e8b02-2227-4ddb-bb73-e0495b03ca3c-161011055941/85/Incident-Mgmt-Process-Guideand-Standards-26-320.jpg)