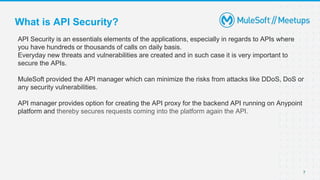
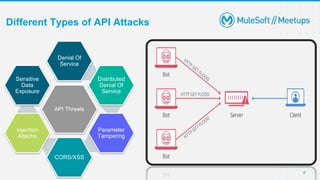
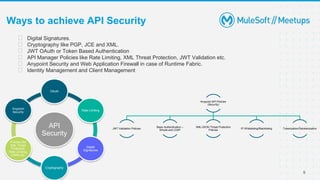
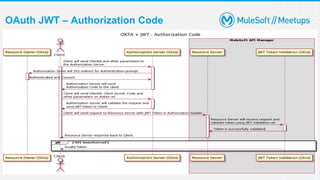
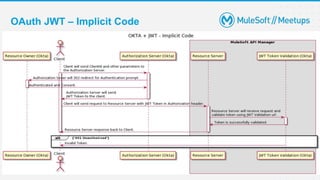
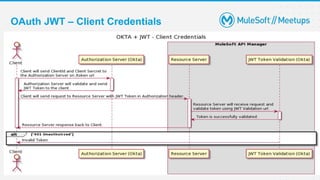
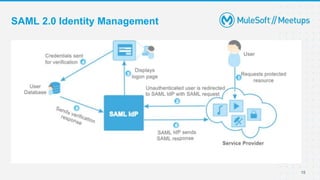
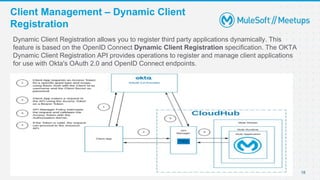
The document details a Mulesoft meetup discussing identity and client management, specifically focusing on API security, identity management protocols like SAML and OpenID Connect, and client management through dynamic client registration. Key points include the importance of API security in preventing various types of attacks and how Mulesoft's API manager aids in securing APIs. The session also featured live demonstrations and quizzes on these topics.
![[8th May 2021]
[Coimbatore] MuleSoft Meetup Group
Identity and Client Management With MuleSoft](https://image.slidesharecdn.com/slidesharecoimbatoreidentityclientmanagement-210508092842/85/Identity-and-Client-Management-using-OpenID-Connect-and-SAML-1-320.jpg)