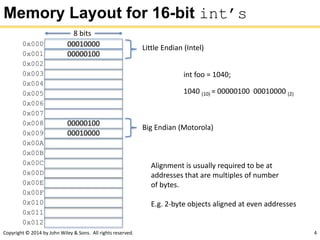
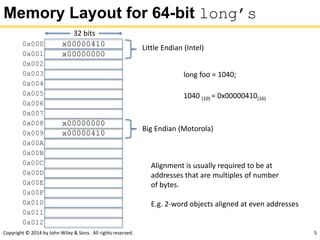
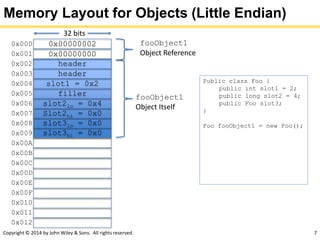
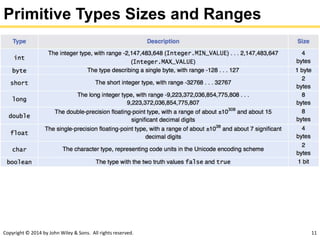
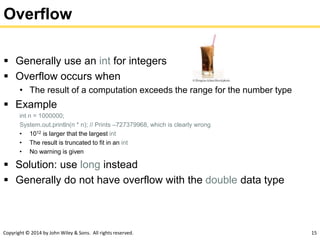
This document contains a chapter about fundamental data types in Java. It discusses integer and floating-point numbers, limitations of numeric types including overflow and rounding errors, proper use of constants, and string manipulation. The chapter aims to explain memory layout for different data types, number systems, and causes of errors when performing arithmetic operations in Java.
![Copyright © 2014 by John Wiley & Sons. All rights reserved. 28
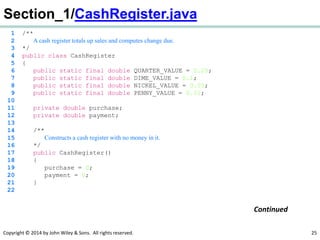
Section_1/CashRegisterTester.java
1 /**
2 This class tests the CashRegister class.
3 */
4 public class CashRegisterTester
5 {
6 public static void main(String[] args)
7 {
8 CashRegister register = new CashRegister();
9
10 register.recordPurchase(0.75);
11 register.recordPurchase(1.50);
12 register.receivePayment(2, 0, 5, 0, 0);
13 System.out.print("Change: ");
14 System.out.println(register.giveChange());
15 System.out.println("Expected: 0.25");
16
17 register.recordPurchase(2.25);
18 register.recordPurchase(19.25);
19 register.receivePayment(23, 2, 0, 0, 0);
20 System.out.print("Change: ");
21 System.out.println(register.giveChange());
22 System.out.println("Expected: 2.0");
23 }
24 }
Program Run:
Change: 0.25
Expected: 0.25
Change: 2.0
Expected: 2.0](https://image.slidesharecdn.com/icom4015-lecture3-f17-170914195307/85/Icom4015-lecture3-f17-28-320.jpg)

![Copyright © 2014 by John Wiley & Sons. All rights reserved. 64
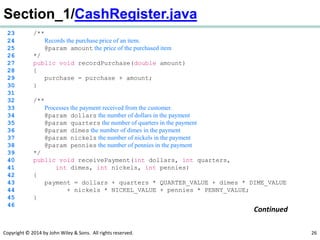
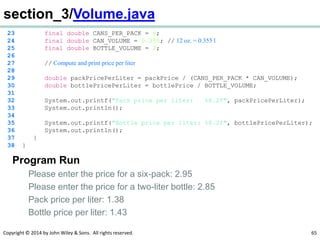
section_3/Volume.java
1 import java.util.Scanner;
2
3 /**
4 This program prints the price per liter for a six-pack of cans and
5 a two-liter bottle.
6 */
7 public class Volume
8 {
9 public static void main(String[] args)
10 {
11 // Read price per pack
12
13 Scanner in = new Scanner(System.in);
14
15 System.out.print("Please enter the price for a six-pack: ");
16 double packPrice = in.nextDouble();
17
18 // Read price per bottle
19
20 System.out.print("Please enter the price for a two-liter bottle: ");
21 double bottlePrice = in.nextDouble();
22
Continued](https://image.slidesharecdn.com/icom4015-lecture3-f17-170914195307/85/Icom4015-lecture3-f17-64-320.jpg)


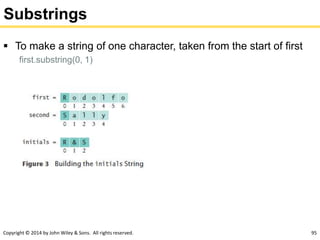
![Copyright © 2014 by John Wiley & Sons. All rights reserved. 96
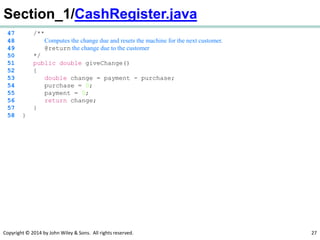
section_5/Initials.java
1 import java.util.Scanner;
2
3 /**
4 This program prints a pair of initials.
5 */
6 public class Initials
7 {
8 public static void main(String[] args)
9 {
10 Scanner in = new Scanner(System.in);
11
12 // Get the names of the couple
13
14 System.out.print("Enter your first name: ");
15 String first = in.next();
16 System.out.print("Enter your significant other's first name: ");
17 String second = in.next();
18
19 // Compute and display the inscription
20
21 String initials = first.substring(0, 1)
22 + "&" + second.substring(0, 1);
23 System.out.println(initials);
24 }
25 } Continued](https://image.slidesharecdn.com/icom4015-lecture3-f17-170914195307/85/Icom4015-lecture3-f17-96-320.jpg)