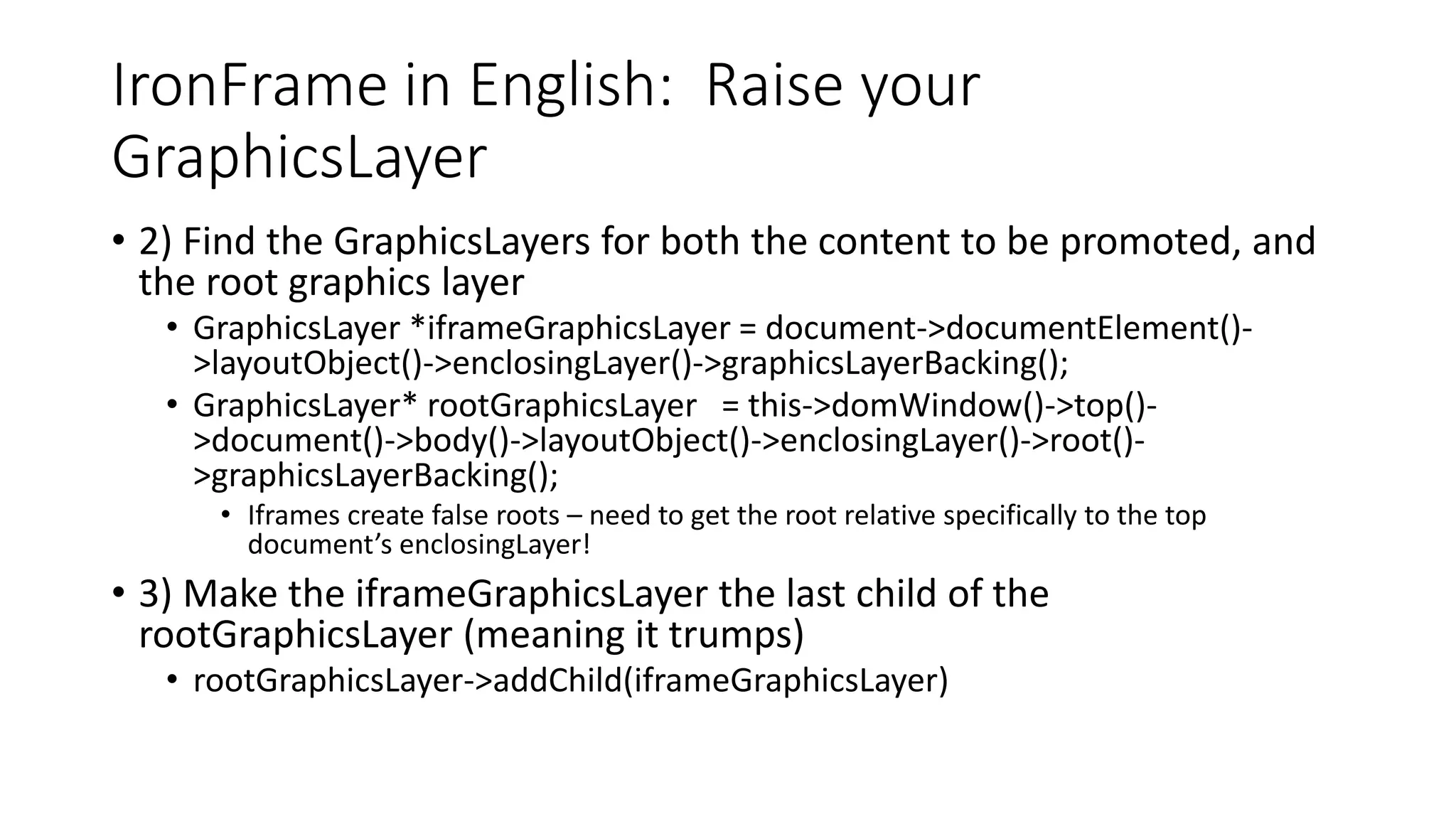
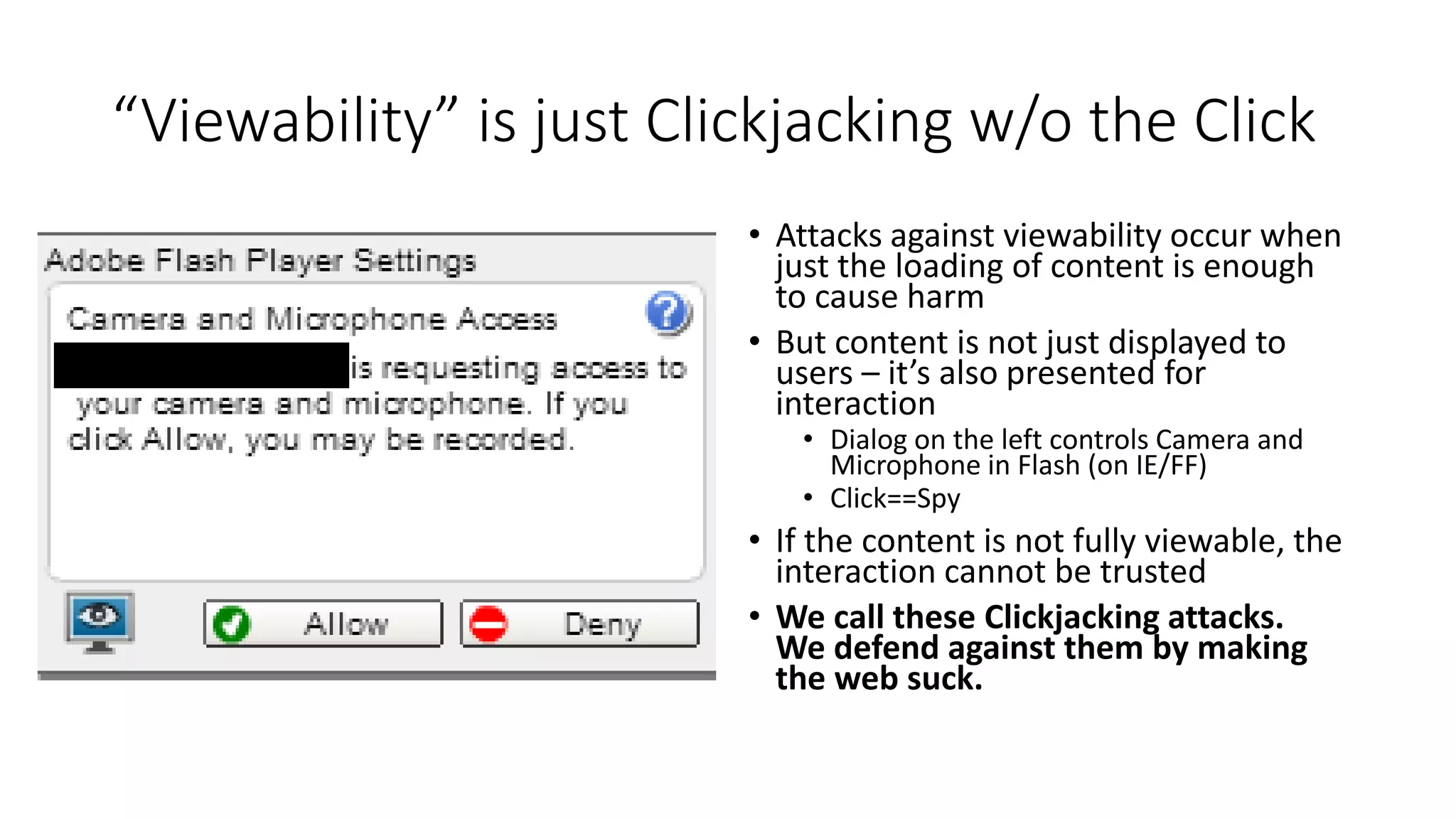
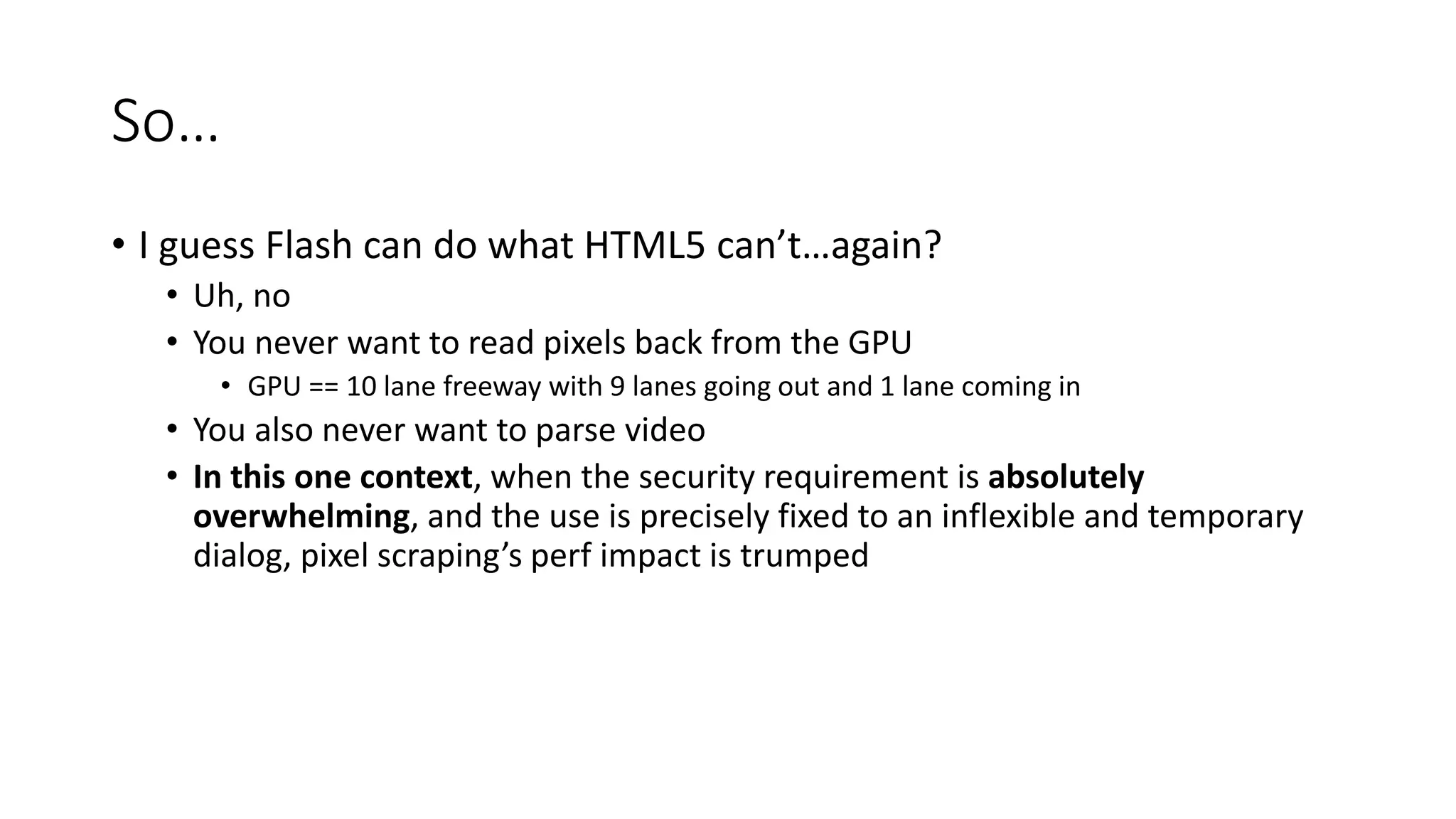
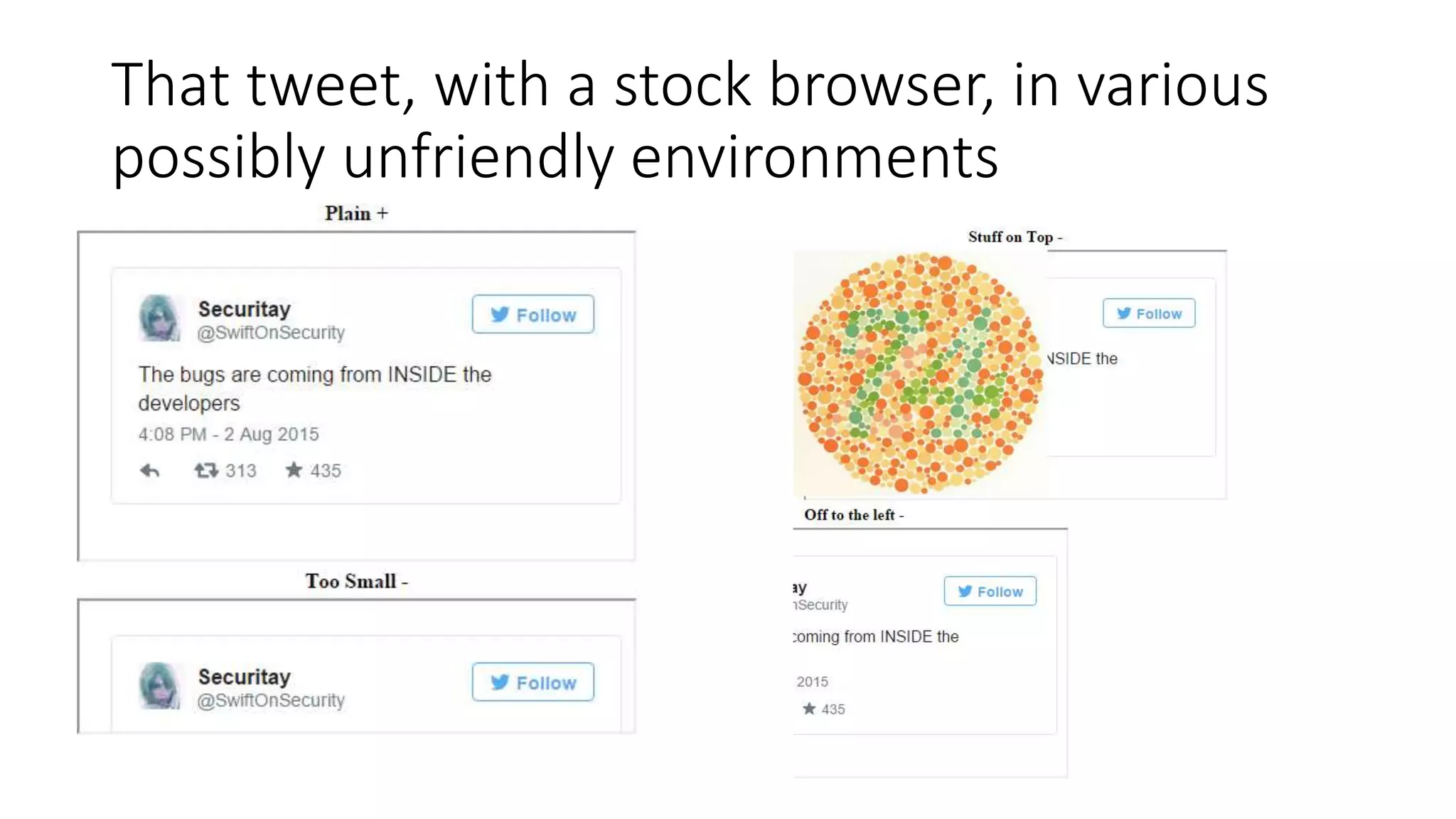
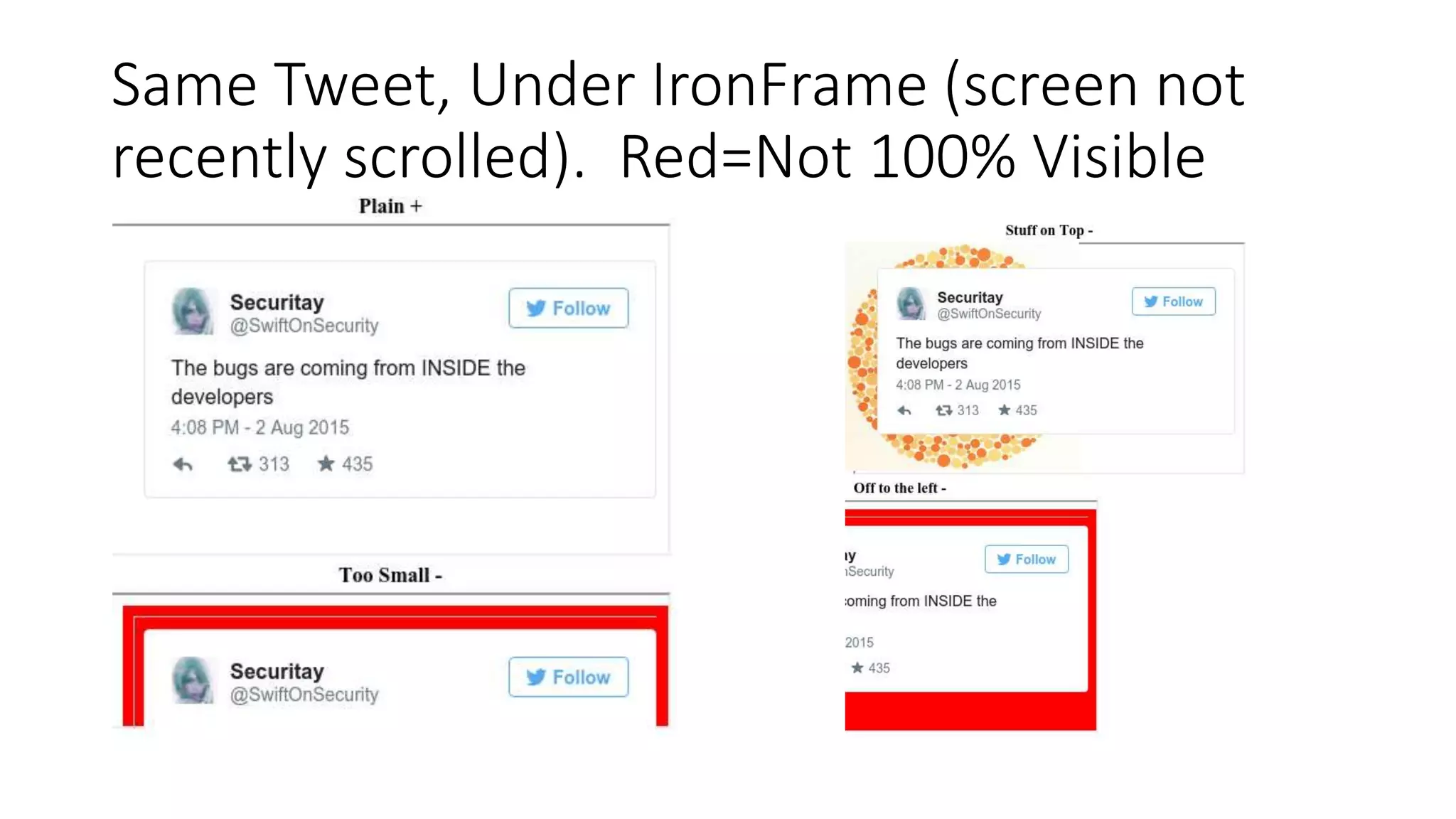
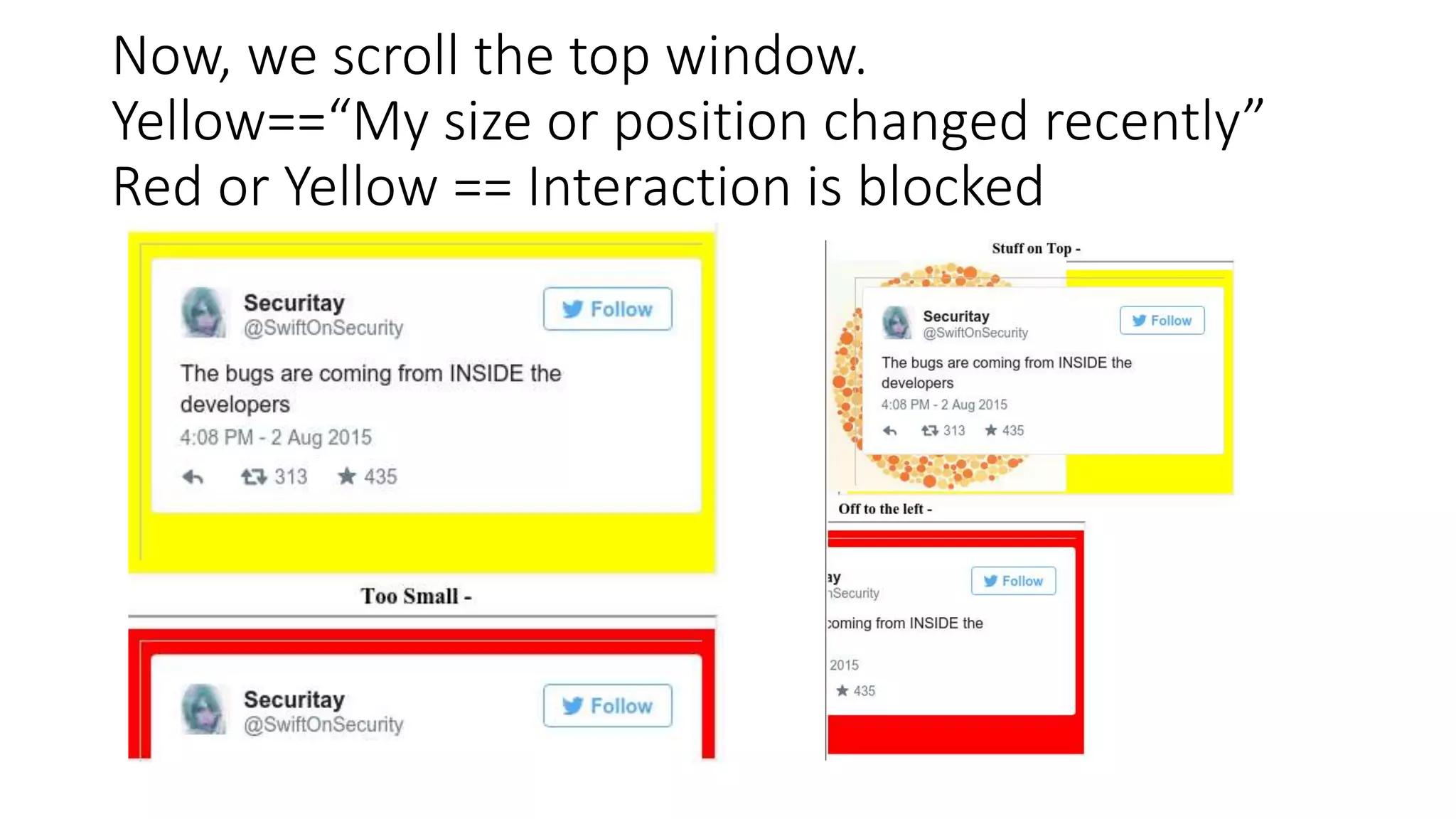
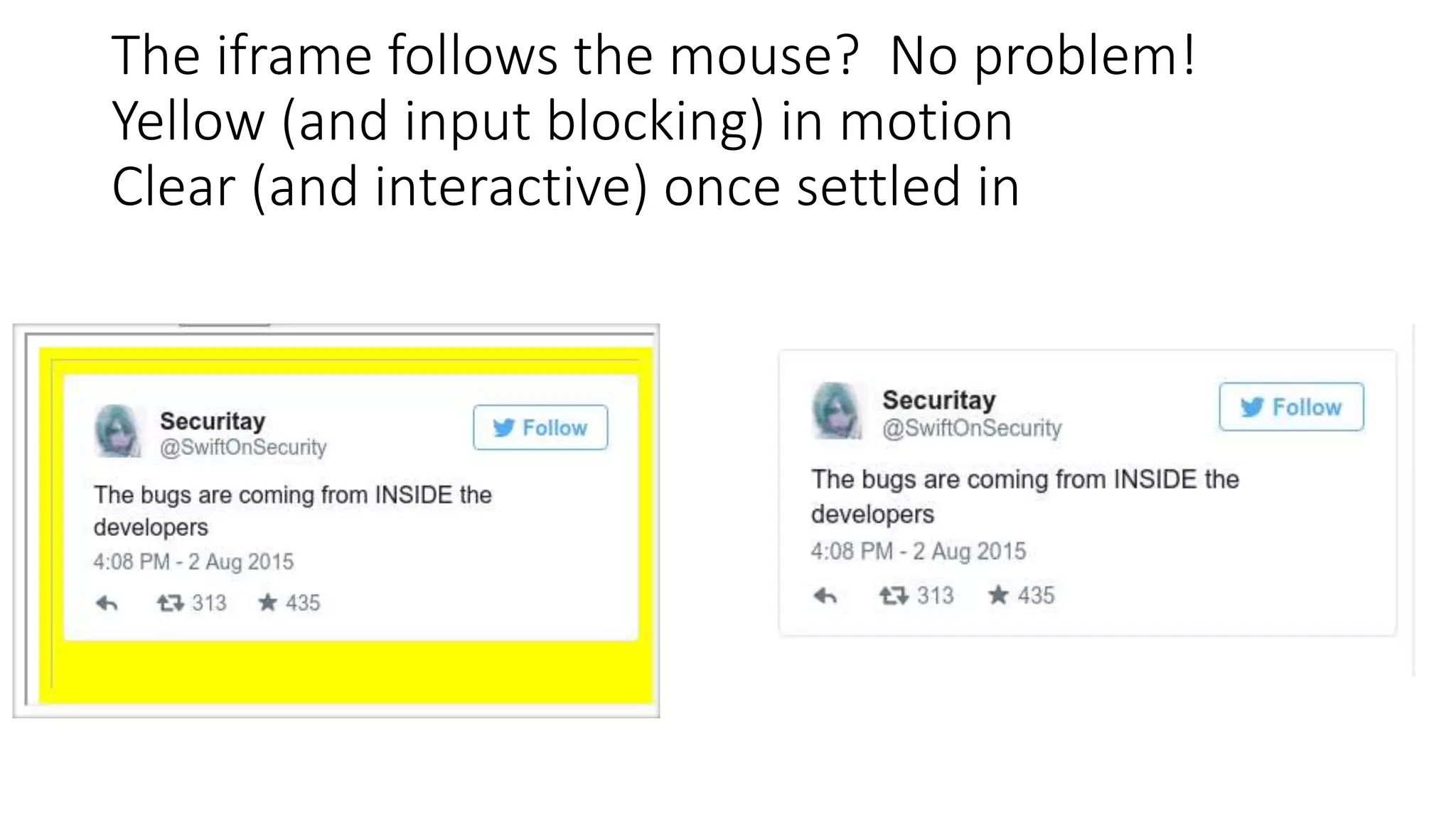
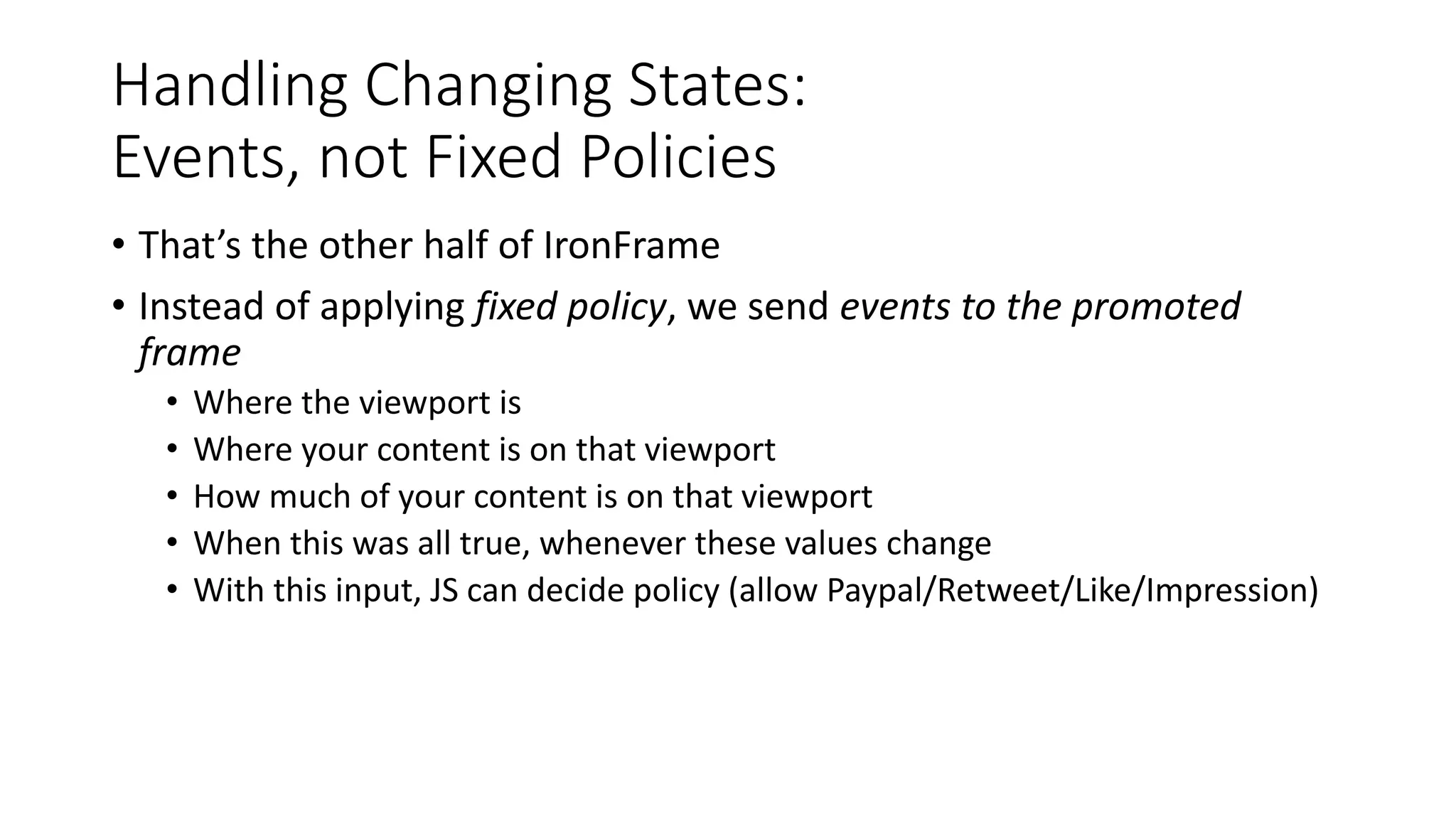
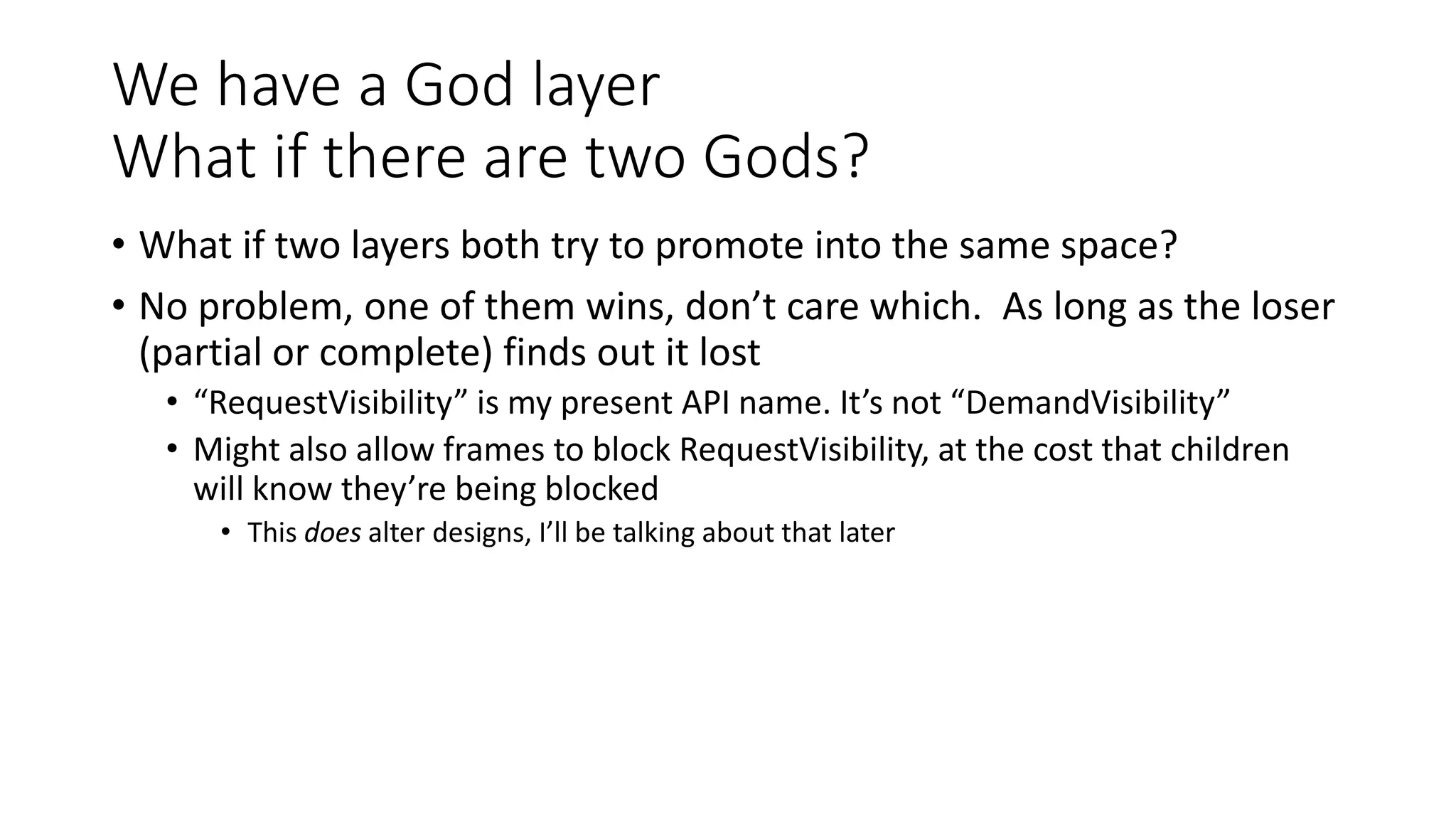
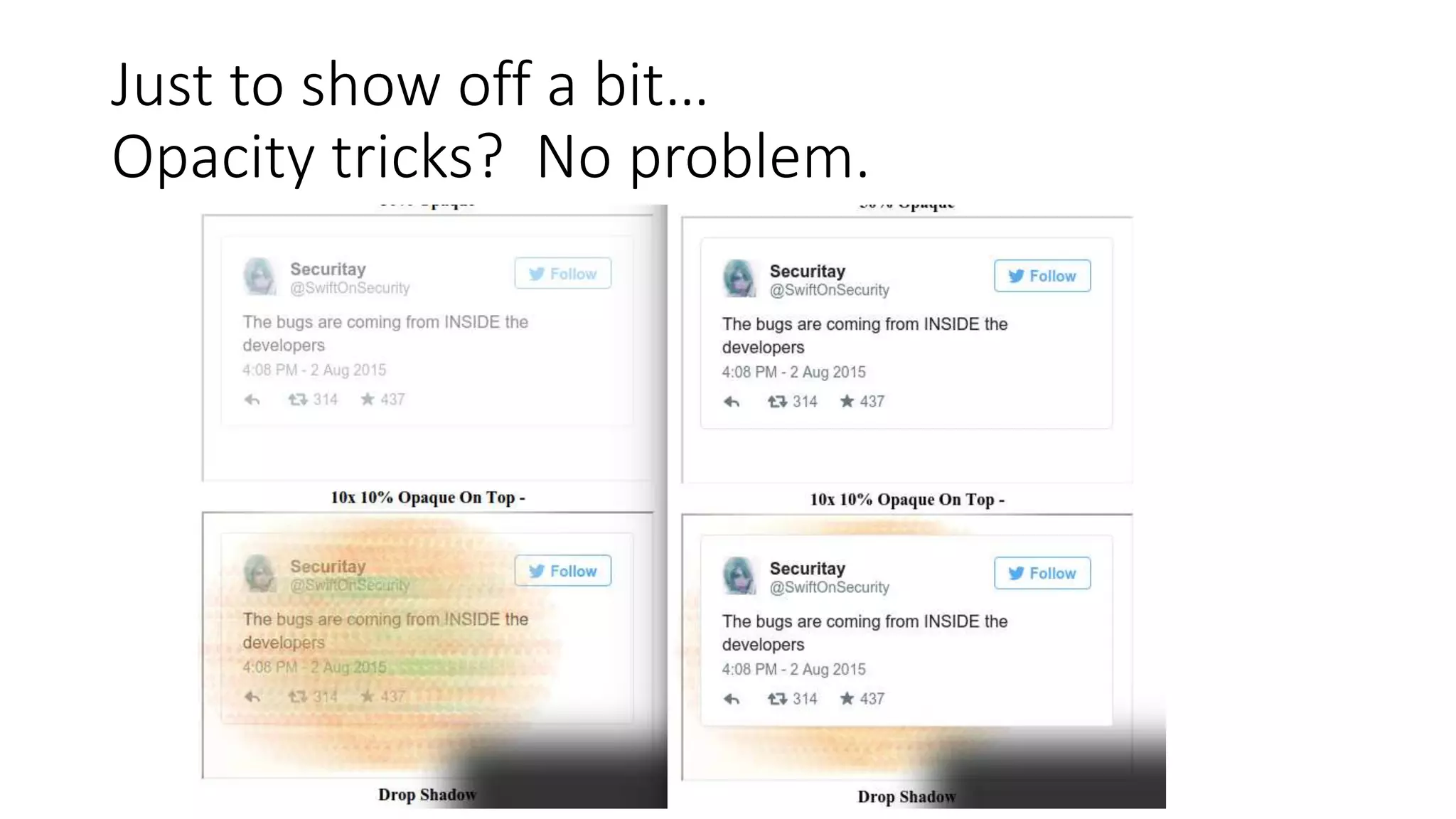
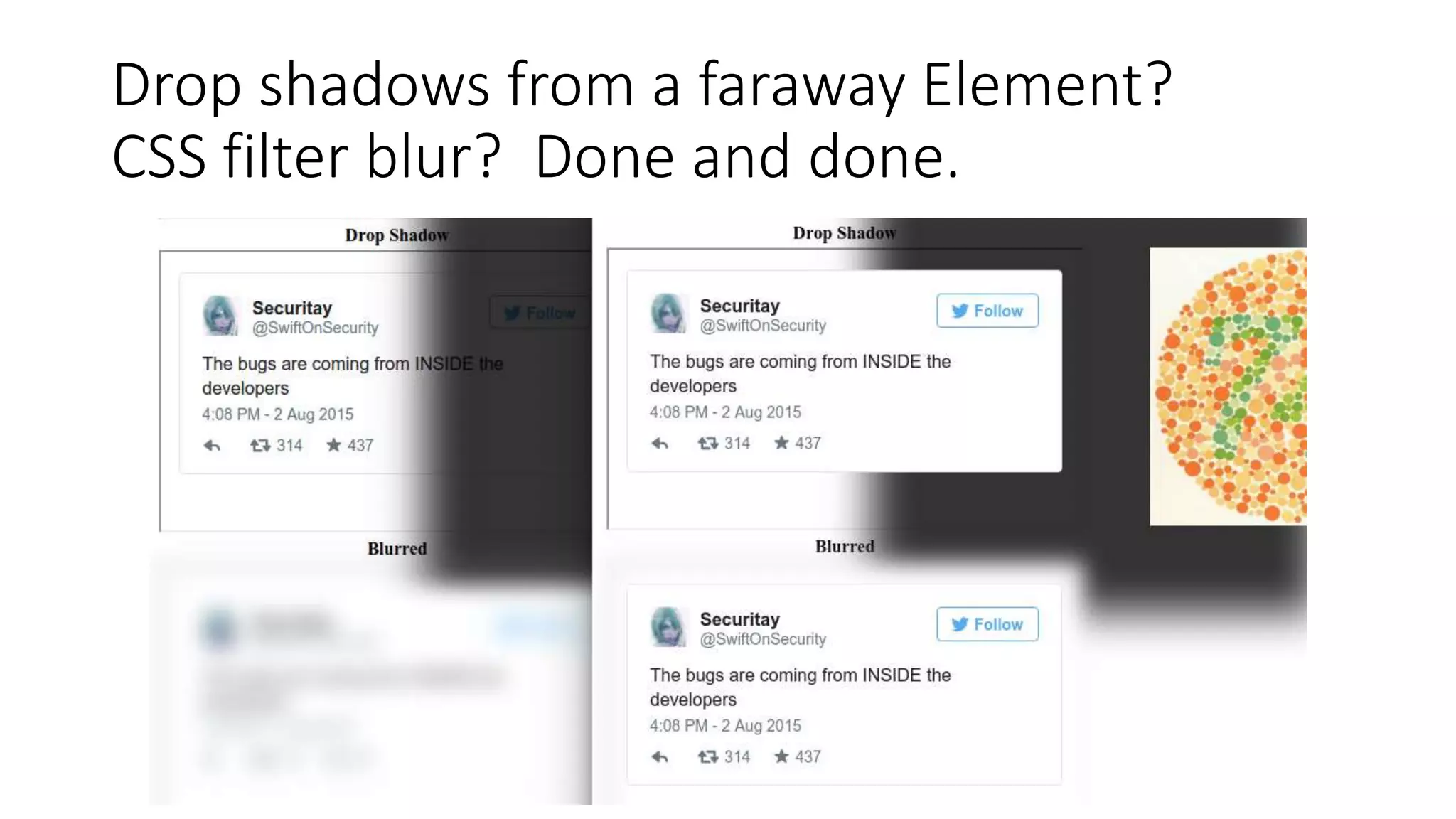
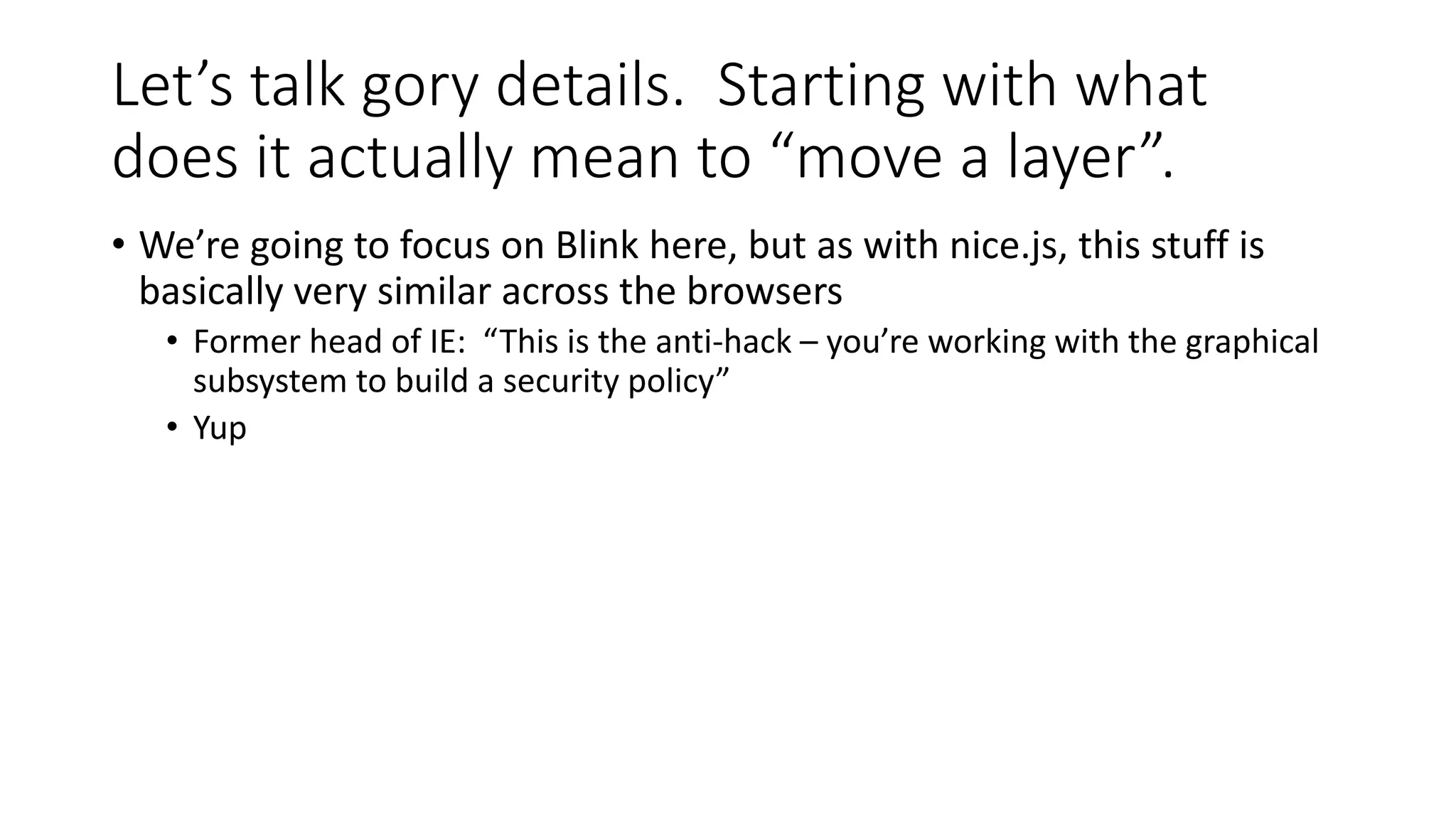
Dan Kaminsky discusses the challenges of web security, particularly focusing on the limitations of the same origin policy and malvertising. He introduces various concepts such as 'nice.js' for monitoring browser performance and 'ironframe' for enhancing security against clickjacking. His insights underscore the need for a balance between user experience and security measures in web architectures.

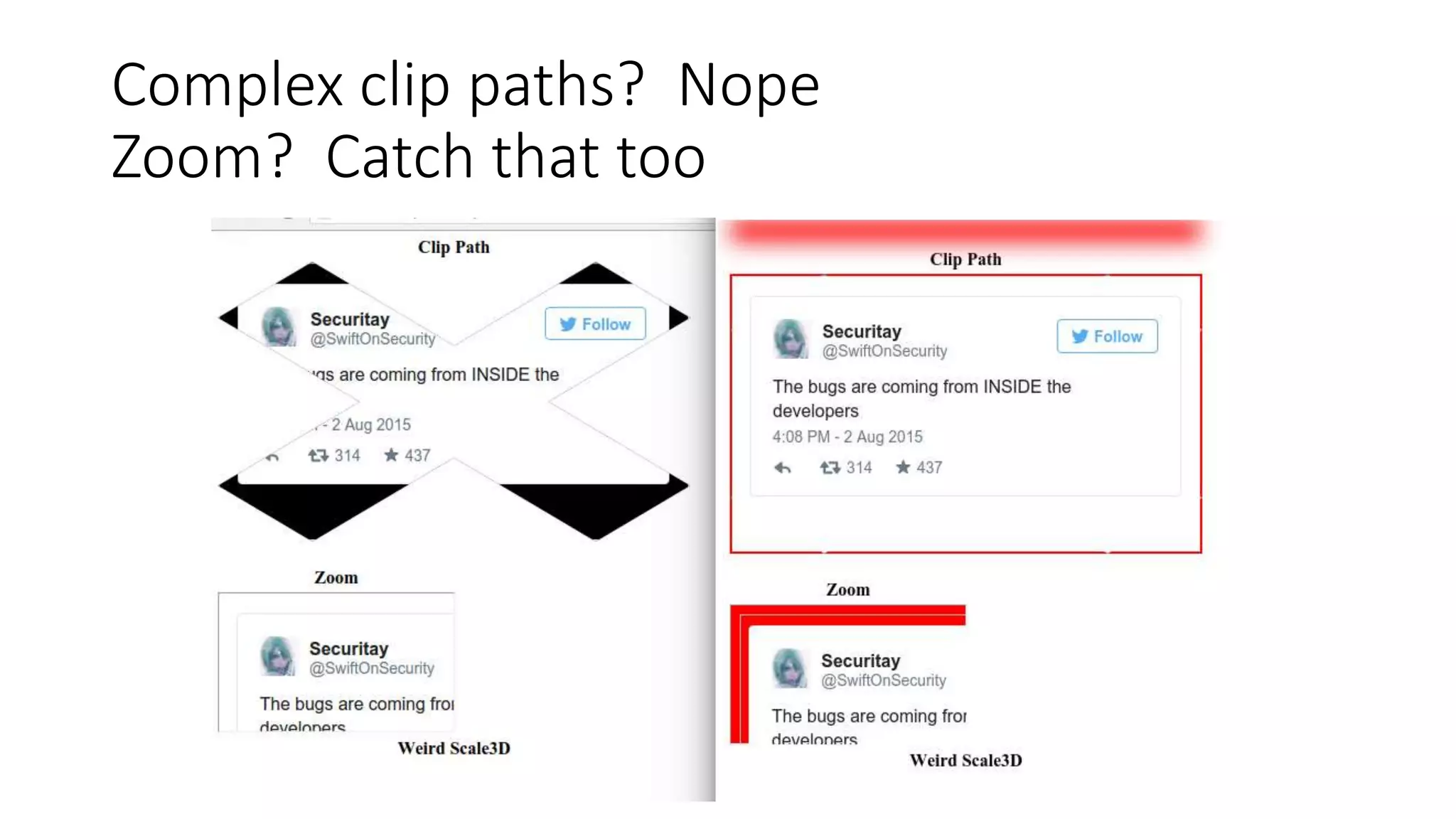
![How it works
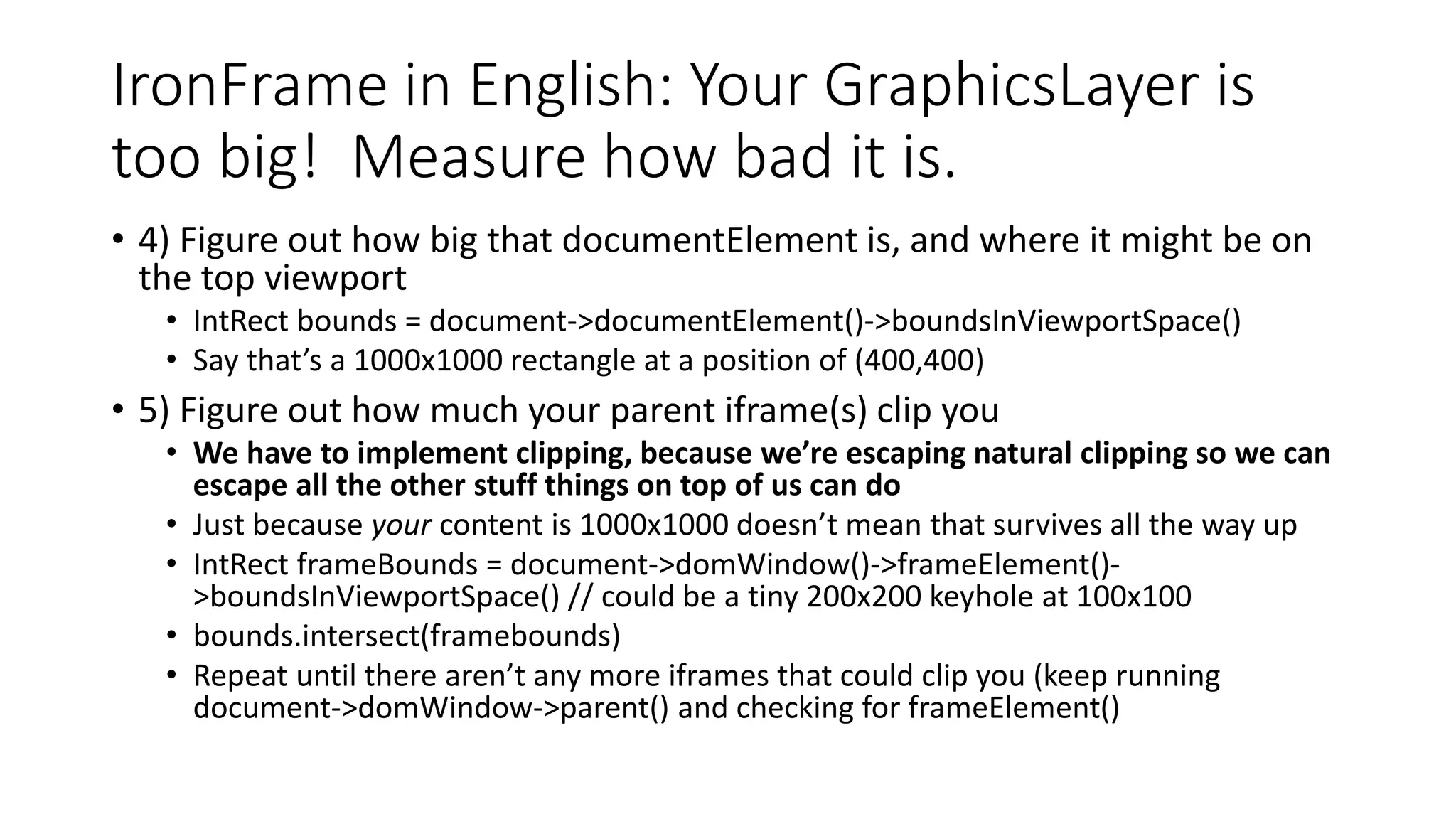
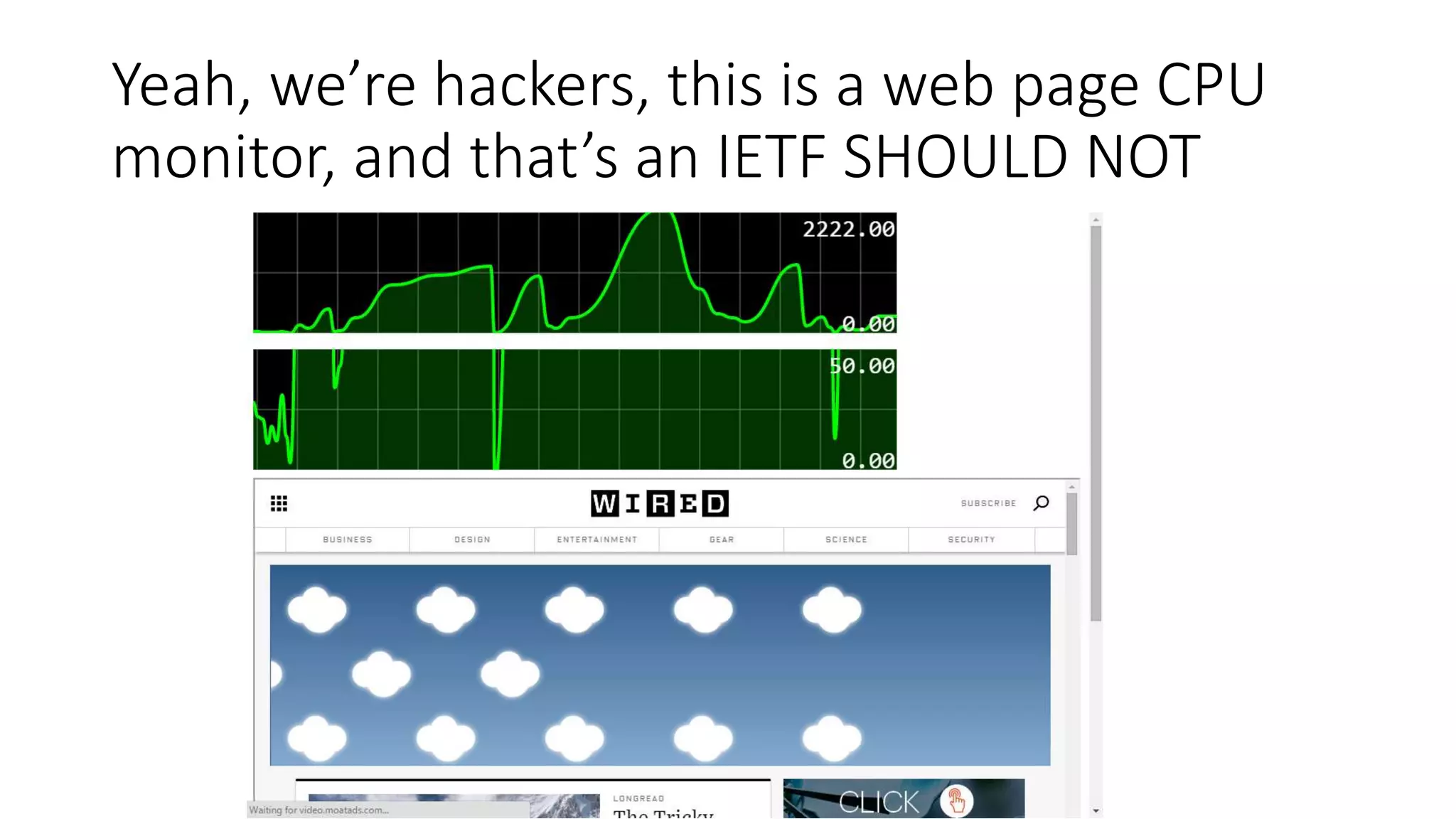
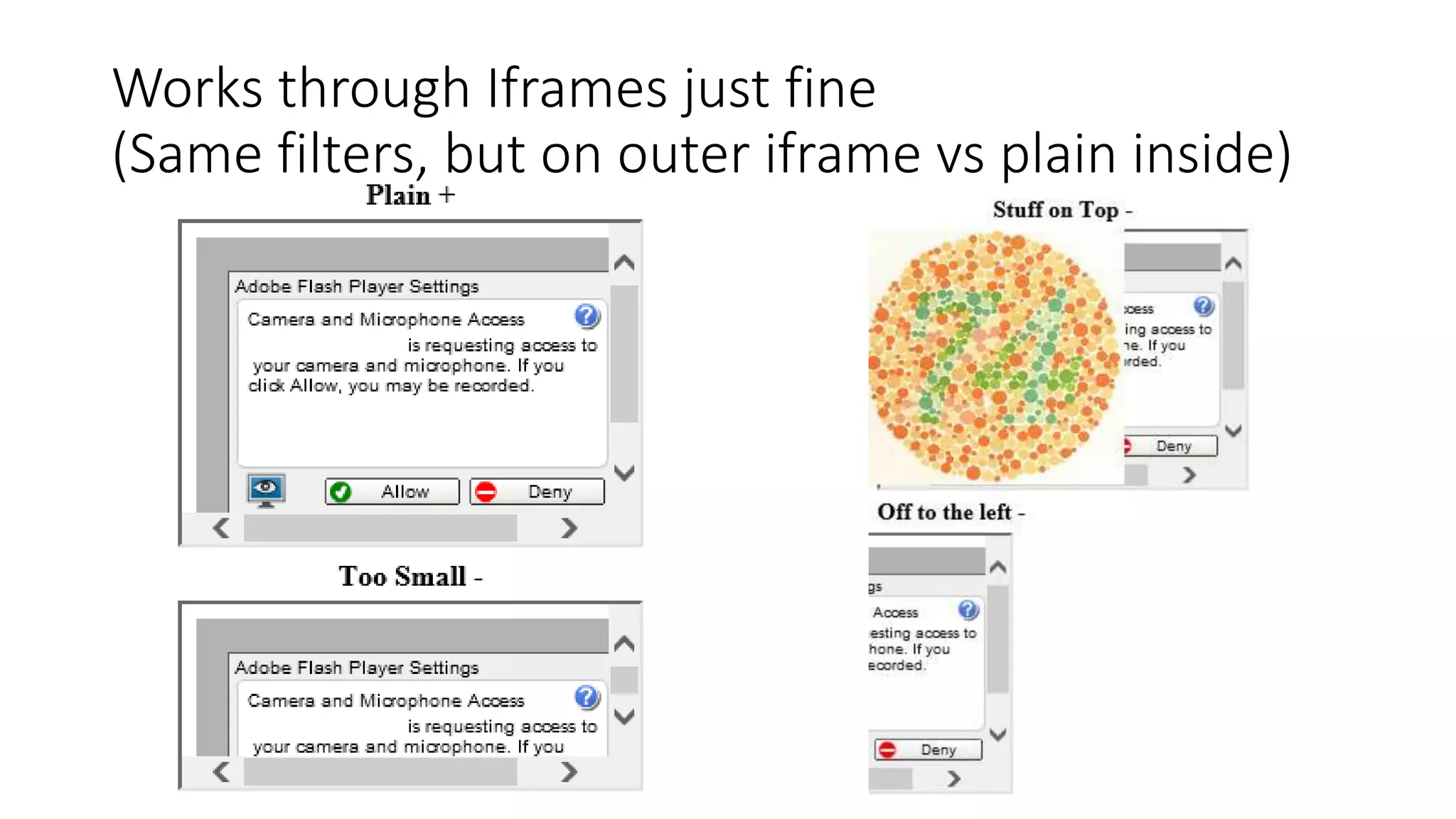
• nice.js (simplified)
• setInterval(
function(){
var now = Date.now();
console.log(now-window.prev-250);
window.prev=now;
}, 250
)
• “Try to do something every 250ms. Then tell me how much we miss that mark.”
• [0,1,1,0] == Idle
• [20,30,20,20] == Somewhat busy
[1000,2000,1000,5000] == Oh dear
• (Can also implement with setTimeout, requestAnimationFrame, and setImmediate,
yielding slightly different results)](https://image.slidesharecdn.com/defcon2015-150809012813-lva1-app6891/75/I-Want-These-Bugs-Off-My-Internet-12-2048.jpg)
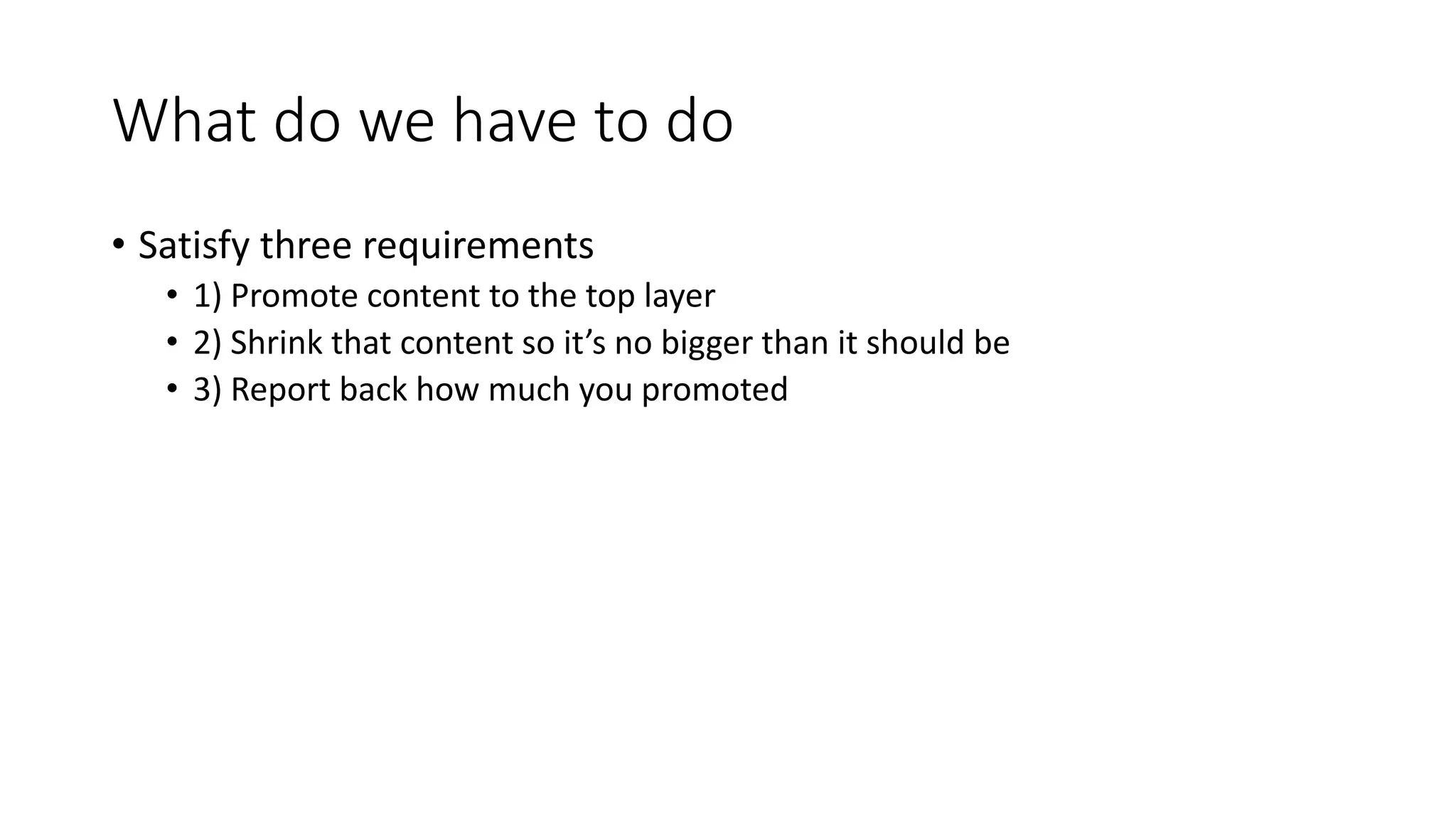
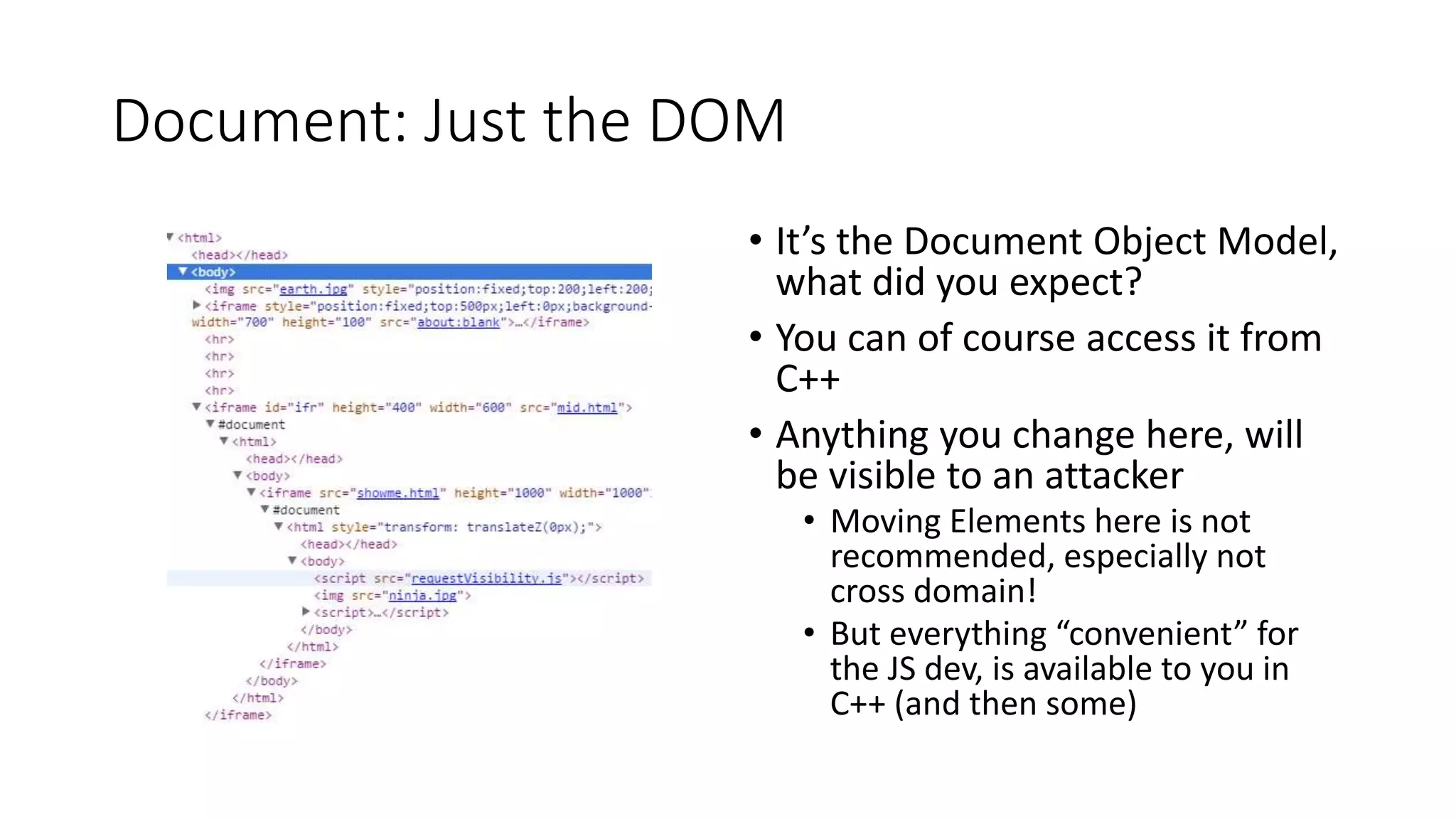
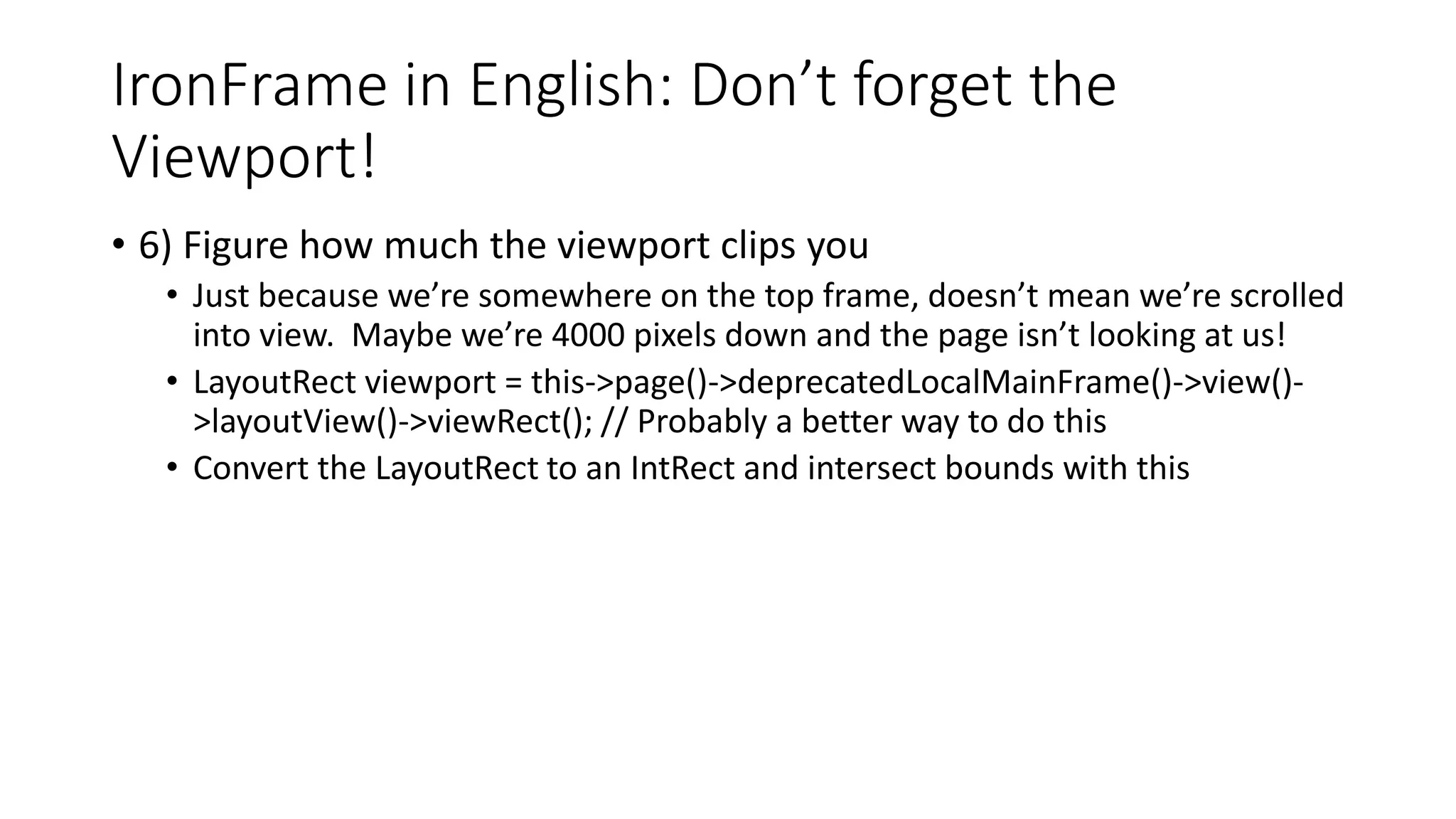
![LayoutObject: A fast OM that still knows what
sort of elements it contains
internals.elementLayoutTreeAsText(
imgdoc.documentElement)
• layer at (0,0) size 784x762
• LayoutBlockFlow {HTML} at
(0,0) size 784x762
• LayoutBlockFlow {BODY} at
(8,8) size 768x746
• LayoutImage {IMG} at (0,0)
size 0x0
internals.elementLayoutTreeAsText(
iframedoc.documentElement)
• layer at (0,0) size 784x762
• LayoutBlockFlow {HTML} at (0,0) size 784x762
• LayoutBlockFlow {BODY} at (8,8) size 768x746
• layer at (8,8) size 304x154
• LayoutIFrame {IFRAME} at (0,0) size
304x154 [border: (2px inset
#EEEEEE)]
• layer at (0,0) size 300x150
• LayoutView at (0,0) size 300x150
• layer at (0,0) size 300x150
• LayoutBlockFlow {HTML} at (0,0) size 300x150
• LayoutBlockFlow {BODY} at (8,8) size 284x134](https://image.slidesharecdn.com/defcon2015-150809012813-lva1-app6891/75/I-Want-These-Bugs-Off-My-Internet-54-2048.jpg)
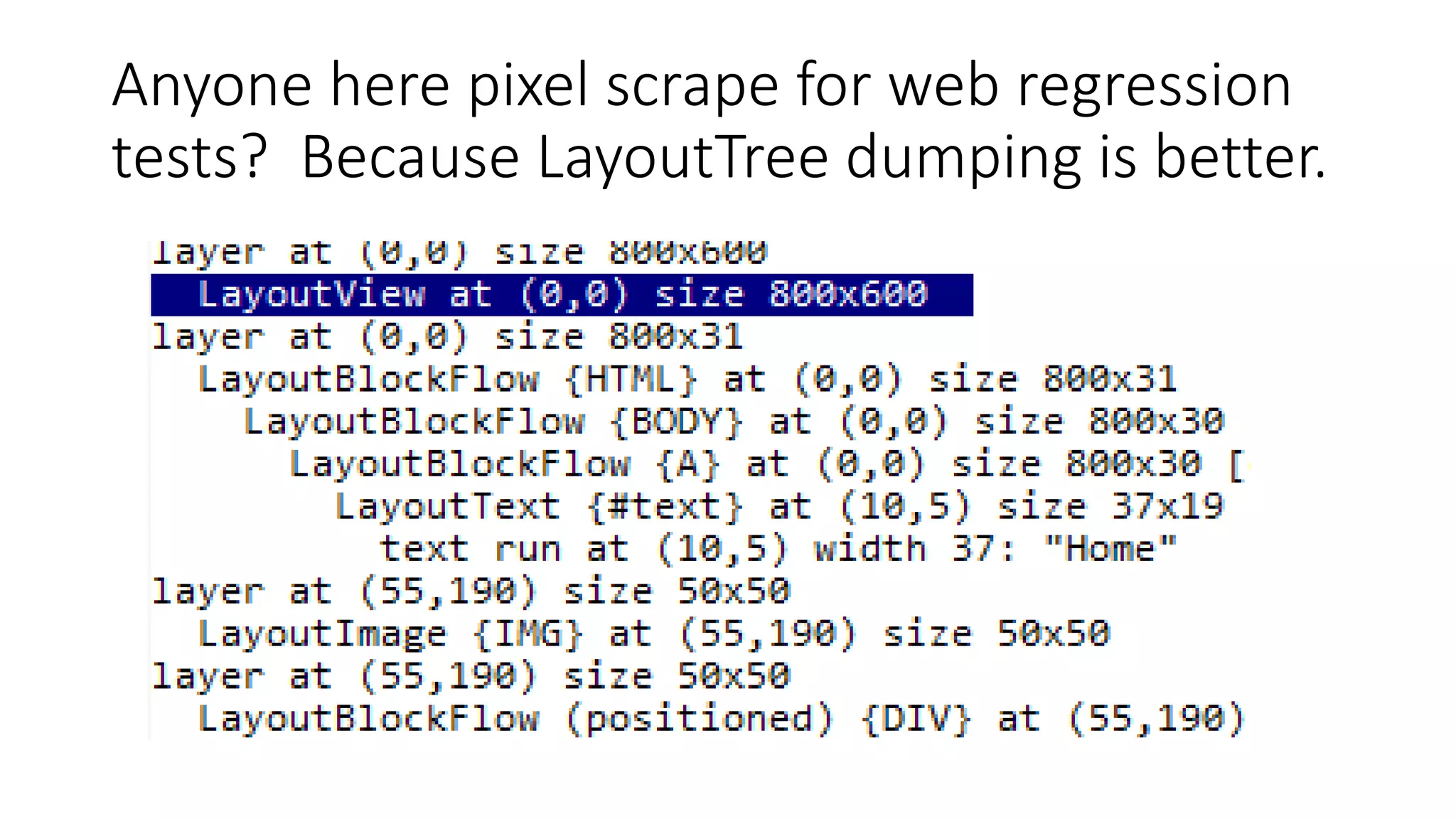
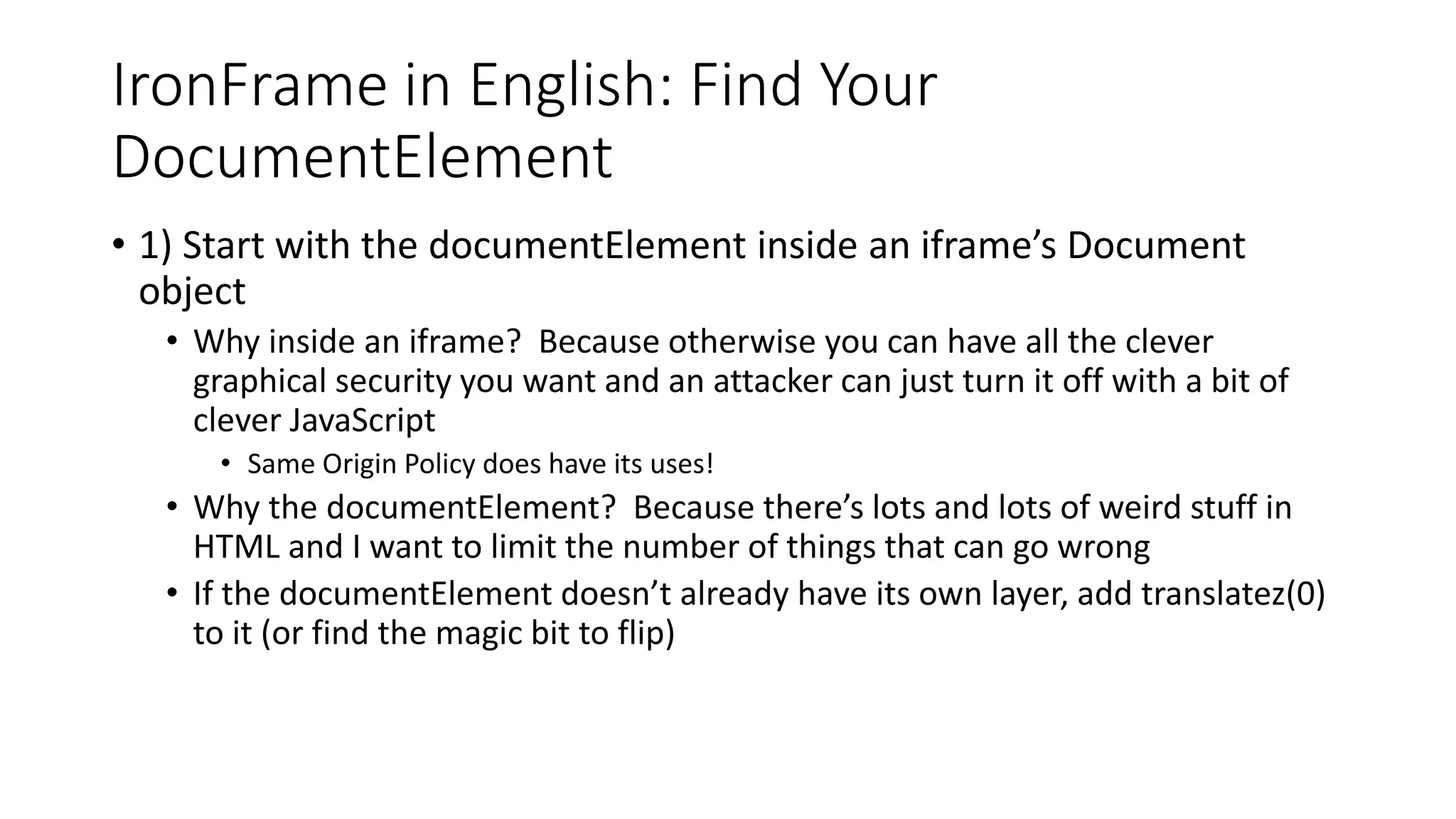
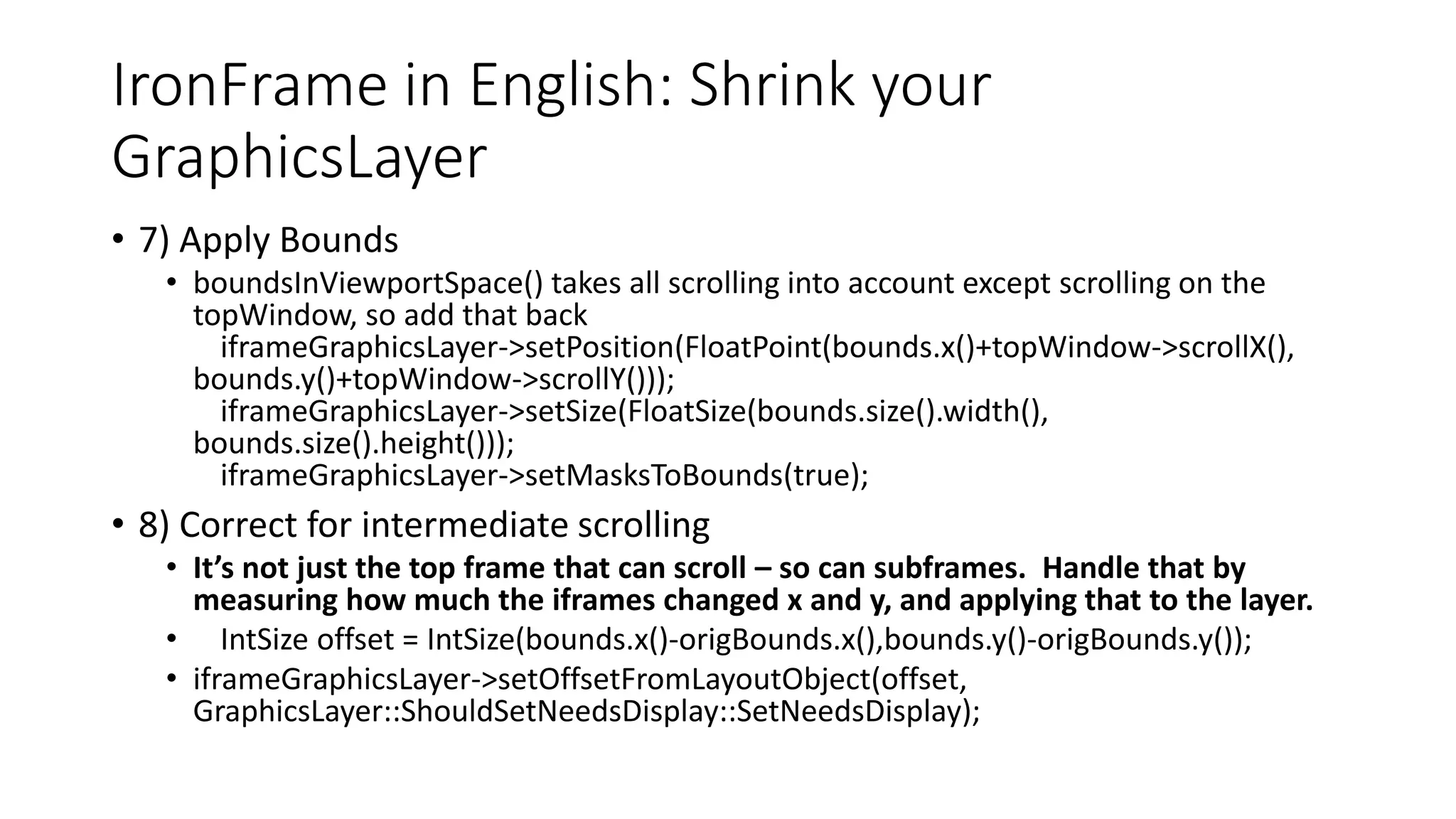
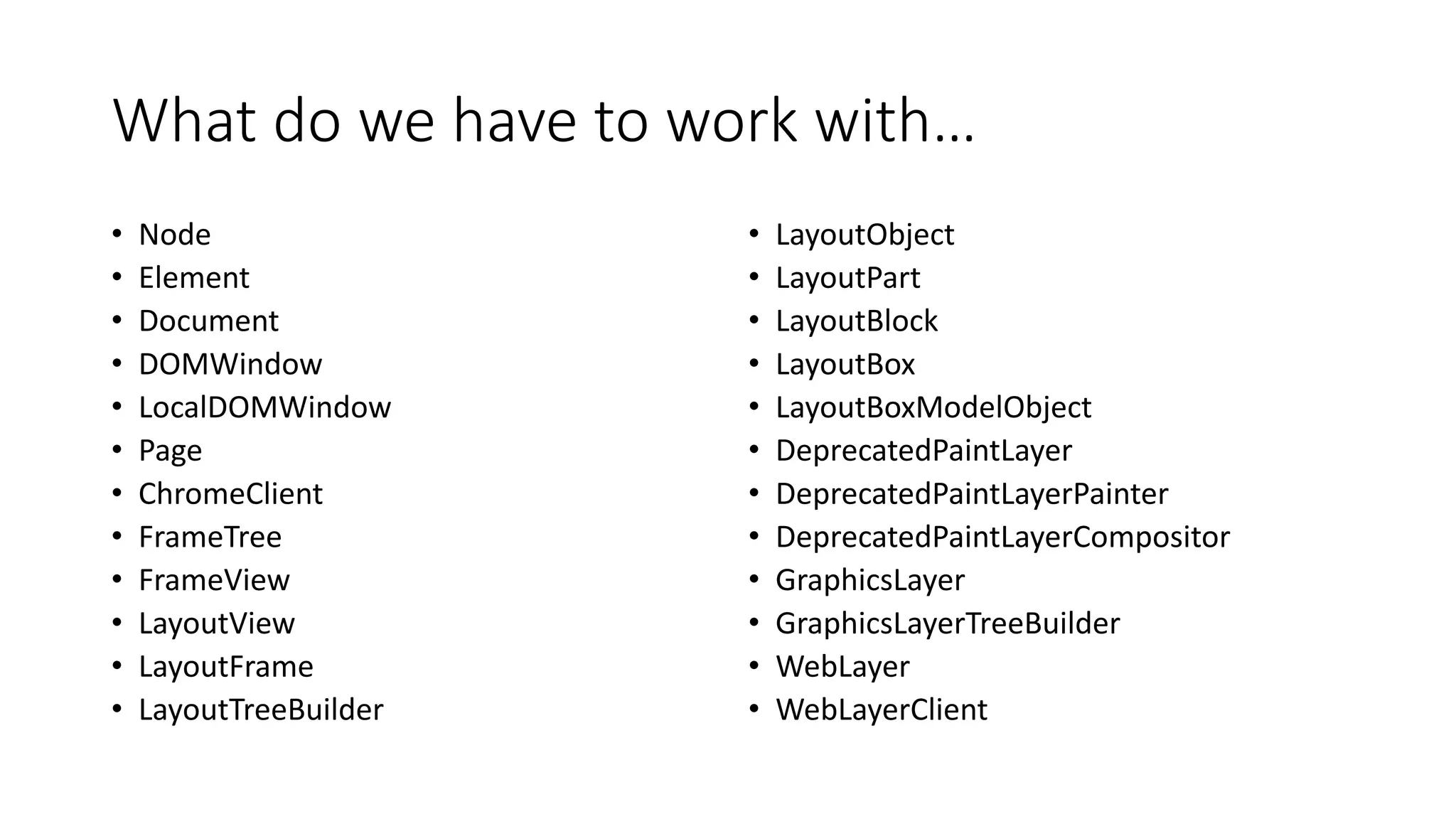
![DeprecatedPaintLayer / GraphicsLayer:
An OM that only knows surfaces to
paint/clip/scroll
internals.layerTreeAsText(document)
• {
• "bounds": [784, 762],
• "children": [
• {
• "bounds": [784, 762],
• "contentsOpaque": true,
• "drawsContent": true
• }
• ]
• }
Some notes
• Many LayoutObjects can
share the same
GraphicsLayer
• An object in the DOM can be
configured to ultimately
require a dedicated
GraphicsLayer
• document.documentElement.s
tyle.transform =
“translatez(0)”
• Well known optimization that
sometimes does good things](https://image.slidesharecdn.com/defcon2015-150809012813-lva1-app6891/75/I-Want-These-Bugs-Off-My-Internet-56-2048.jpg)