ht-f02-inside-the-world-of-java-applets_final
•
0 likes•318 views
1. JAR attacks are complex and use obfuscation and reflection to evade static analysis, posing challenges for detection. 2. Executing JAR files within sandbox environments requires correct input parameters, an active internet connection, and the appropriate Java version, which sandboxes still struggle with. 3. An effective detection model requires multi-vector and multi-flow analysis to correlate static, dynamic, and network behaviors and detect sophisticated unknown JAR attacks.
Report
Share
Report
Share
Download to read offline
Recommended
Agile Network India | DevSecOps - The What and the Why | Ritesh Shregill

Agile Network India | DevSecOps - The What and the Why by Ritesh Shregill
Security Testing ModernApps_v1.0

In the recent years, the traditional application monolith has broken down into a hefty chunk of micro-services thereby increasing the attack surface. We will look at how this increases the entry points into the complex modern day application ecosystem. The modern security tester needs various skills to pen-test such apps including the understanding of containers to successfully break or defend such applications.
When we tie this with the fast paced devOps life cycles for applications and explore the challenges when scaling security for such applications across the organization.
Hence, this webinar discusses traditional and relatively newer methods of Pen-testing web applications. Thereby illustrating how the changing business requirements and Agile life cycles for applications affect Security testing for modern applications.
Key Takeaways:
- what do the traditional Pen testing/Security testing Techniques entail?
- How is the landscape for Applications changing and how it affects security testing?
- What are the key essentials for testing modern applications?
- what can be done to scaling Security Assessments(Testing) for Modern & Agile life cycles?
Présentation kaspersky threat intelligence services

Dans le cadre de la 8ème edition des Cyber Security Days 2018, organisée par l'agence nationale de la sécurité informatique, notre partenaire Kaspersky North Africa a présenté son module "Kaspersky Threat intelligence".
Dev week cloud world conf2021

Talk to executives in IT divisions of large enterprises about security and invariably the conversation will hover around
DevSecOps pipeline.
Is DevSecOps the only thing you need to do for security in your IT division or is there more?
What impact does bringing in secure culture in an engineering context mean?
What handshake is needed between the IT function and the security / risk function for large enterprises?
How does this impact roles and responsibilities of a developer?
This talk is an attempt to answer questions such as these using a real world examples of transformations seen in Fortune 100 companies.
Owasp A9 USING KNOWN VULNERABLE COMPONENTS IT 6873 presentation

OWASP A9 USING KNOWN VULNERABLE COMPONENTS ITEC6873
Standards and methodology for application security assessment 

Based on the research results, it can be concluded that the ISO / IEC 27034 standard regulates that vulnerability testing should be carried out, but it is not specified how and what should be tested for vulnerabilities, but how and what is not described. NIST and NIAP both refer to OWASP MASVS and contain controls by which the mobile application is tested, mainly focusing on vulnerabilities that relate to vulnerabilities in data storage and authorization. This is confirmed by statistics provided by Digital Security. The most recognized is MASVS. One of the parts of MASVS describes what, how and how to test.
It should be noted that all standards rather weakly assess vulnerabilities that relate to interaction with the API. As can be seen from the tests described in Section 2.2, the most critical vulnerabilities are vulnerabilities that are associated with interaction with the application server.
Recommended
Agile Network India | DevSecOps - The What and the Why | Ritesh Shregill

Agile Network India | DevSecOps - The What and the Why by Ritesh Shregill
Security Testing ModernApps_v1.0

In the recent years, the traditional application monolith has broken down into a hefty chunk of micro-services thereby increasing the attack surface. We will look at how this increases the entry points into the complex modern day application ecosystem. The modern security tester needs various skills to pen-test such apps including the understanding of containers to successfully break or defend such applications.
When we tie this with the fast paced devOps life cycles for applications and explore the challenges when scaling security for such applications across the organization.
Hence, this webinar discusses traditional and relatively newer methods of Pen-testing web applications. Thereby illustrating how the changing business requirements and Agile life cycles for applications affect Security testing for modern applications.
Key Takeaways:
- what do the traditional Pen testing/Security testing Techniques entail?
- How is the landscape for Applications changing and how it affects security testing?
- What are the key essentials for testing modern applications?
- what can be done to scaling Security Assessments(Testing) for Modern & Agile life cycles?
Présentation kaspersky threat intelligence services

Dans le cadre de la 8ème edition des Cyber Security Days 2018, organisée par l'agence nationale de la sécurité informatique, notre partenaire Kaspersky North Africa a présenté son module "Kaspersky Threat intelligence".
Dev week cloud world conf2021

Talk to executives in IT divisions of large enterprises about security and invariably the conversation will hover around
DevSecOps pipeline.
Is DevSecOps the only thing you need to do for security in your IT division or is there more?
What impact does bringing in secure culture in an engineering context mean?
What handshake is needed between the IT function and the security / risk function for large enterprises?
How does this impact roles and responsibilities of a developer?
This talk is an attempt to answer questions such as these using a real world examples of transformations seen in Fortune 100 companies.
Owasp A9 USING KNOWN VULNERABLE COMPONENTS IT 6873 presentation

OWASP A9 USING KNOWN VULNERABLE COMPONENTS ITEC6873
Standards and methodology for application security assessment 

Based on the research results, it can be concluded that the ISO / IEC 27034 standard regulates that vulnerability testing should be carried out, but it is not specified how and what should be tested for vulnerabilities, but how and what is not described. NIST and NIAP both refer to OWASP MASVS and contain controls by which the mobile application is tested, mainly focusing on vulnerabilities that relate to vulnerabilities in data storage and authorization. This is confirmed by statistics provided by Digital Security. The most recognized is MASVS. One of the parts of MASVS describes what, how and how to test.
It should be noted that all standards rather weakly assess vulnerabilities that relate to interaction with the API. As can be seen from the tests described in Section 2.2, the most critical vulnerabilities are vulnerabilities that are associated with interaction with the application server.
Popular Approaches to Preventing Code Injection Attacks are Dangerously Wrong

Presentation by John Matthew Holt, Founder and CTO, Waratek at OWASP AppSec USA 2017
Machine Learning in Malware Detection

When dealing with over 300 hundred thousand of malware samples every day, we had to deploy the state-of-the-art techniques to combat cyberthreats. And among them - machine learning algorithms.
In this whitepaper, we start from describing the basic approaches and proceed to explaining the key applications of machine learning algorithms to automated malware detection. Learn more about how Kaspersky Lab protects businesses like yours => https://kas.pr/8dxv
Secure Code review - Veracode SaaS Platform - Saudi Green Method

Veracode provides the world’s leading Application Risk Management Platform. Veracode's patented and proven cloud-based capabilities allow customers to govern and mitigate software security risk across a single application or an enterprise portfolio with unmatched simplicity. Veracode was founded with one simple mission in mind: to make it simple and cost-effective for organizations to accurately identify and manage application security risk.
Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...

Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...Microsoft Tech Community
Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, and Azure
7 Reasons Your Applications are Attractive to Adversaries

Presentation from 18 November 2014.
Software applications need to be delivered faster and across more platforms than ever. To build high quality software in short order, we’ve seen a dramatic shift from source code to component-based development, with open source and third party components providing the innovation and efficiency that developers need.
Unfortunately, our dependence on components is growing faster than our ability to secure them. These shared components are not top-of-mind when considering application risk. Worse yet, components are increasingly the preferred attack surface in today’s applications.
The combination of growing component usage, coupled with lack of security, requires us to urgently re-evaluate traditional application security approaches and identify practical next steps for closing this security gap.
So what’s the “neglected 90%,” why is it attractive to your adversaries and what can you do about it? Plenty. Here are 7 key points, for starters.
http://bit.ly/AHC_USAF
Pentesting Your Own Wireless Networks, June 2011 Issue

Pentesting Your Own Wireless Networks, June 2011 Issue
The Web AppSec How-To: The Defender's Toolbox

Web application security has made headline news in the past few years. In this article, we review the various Web application security tools and highlight important decision factors to help you choose the application security technology best suited for your environment.
Understanding & Addressing OWASP’s Newest Top Ten Threat: Using Components wi...

In 2013, the Open Web Application Security Project (OWASP) was updated to include “A9: using components with known vulnerabilities.” This paper explains this new threat with practical ideas for reducing risk from open source components which now comprise 80% of an average application.
Crafting Super-Powered Risk Assessments by Digital Defense Inc & Veracode

http://www.ddifrontline.com
Digital Defense Inc (DDI) and Veracode present the "Crafting Super-Powered Risk Assessments" webinar and slides. The presentation covers security assessments, application security, and how to manage risk.
Secure coding presentation Oct 3 2020

Secure Coding, What you need to know as a developer, SAST, DAST, DevOps, OWASP, Application Security
Application Security Guide for Beginners 

This beginner’s guide to application security focuses on the main concepts and keywords used in the Application Security domain. From a secure software development lifecycle (SDLC) to the top threats facing applications and their impacts, this guide covers it all!
This guide is divided into the following categories:
-Code DevelopmentMethodologies
-Code
-Application SecuritySolutions
-Common threats and their impacts
Secure Coding for Java - An Introduction

Ce talk est une introduction au Secure Coding pour Java. Il s'efforcera de présenter via différents exemples les bonnes pratiques permettant de développer de manière pragmatique une application java sécurisée. Nous aborderons aussi bien des pratiques fonctionnelles que des morceaux de codes java à erreurs et leur correctifs.
We explain the security flaw that's freaking out the internet

Security geniuses say it's one of the most exceedingly awful PC weaknesses they've at any point seen.
The Duqu 2.0: Technical Details

Earlier this year, during a security sweep, Kaspersky Lab detected a cyber intrusion affecting several of its internal systems. Following this finding, we launched a large-scale investigation, which led to the discovery of a new malware platform from one of the most skilled, mysterious and
powerful groups in the APT world – Duqu. The Duqu threat actor went dark in 2012 and was believed to have stopped working on this project - until now. Our technical analysis
indicates the new round of attacks include an updated version of the infamous 2011 Duqu malware, sometimes referred to as the step-brother of Stuxnet. We named this
new malware and its associated platform “Duqu 2.0”.
Victims of Duqu 2.0 have been found in several places, including western countries, the Middle East and Asia. The actor appears to compromise both final and utilitarian targets, which allow them to improve their cyber capabilities. Most notably, some of the new 2014-2015 infections are linked to the P5+1 events and venues related to the negotiations with Iran about a nuclear deal. The threat actor behind Duqu appears to have launched attacks at the venues for some of these high level talks.
In addition to the P5+1 events, the Duqu 2.0 group has launched a similar attack in relation to the 70th anniversary event of the liberation of Auschwitz-Birkenau.
In the case of Kaspersky Lab, the attack took advantage of a zero-day (CVE-2015-2360) in the WindowsKernel, patched by Microsoft on June 9 2015 and possibly up to two other, currently patched vulnerabilities, which were zeroday at that time.
Infrastructure as (Secure) Code

Software-defined networking is the latest technology in a move to abstract a variety of data center resources. As more and more of the data center is defined in code, some unique security challenges come to the fore.
In this session, we'll explore both sides of the security challenge. What types of controls and implementations are required to define security as part of your infrastructure code? What challenges does maintaining an infrastructure codebase present?
You'll learn not only how to integrate security into your infrastructure code but also how to properly and securely manage that codebase.
Application Security Management with ThreadFix

How to efficiently identify and remediate critical vulnerabilities in SAP and other Business Applications.
Vulnerabilities in individual applications harbor enormous risks for companies because they can be exploited by hackers to gain access to the corporate network and critical IT infrastructure such as SAP systems. An effective approach to application security management therefore must take the entire application portfolio of a company into consideration. It must evaluate critical vulnerabilities uniform and must be capable to track their remediation, regardless of the programming language or the development environment used.
This approach is facilitated by ThreadFix, an open source software offered by Denim Group. In our webinar APPLICATION SECURITY MANAGEMENT we show you:
- How you can scan your SAP and other business applications automatically for critical vulnerabilities
- How you can easily track the remediation of vulnerabilities with ThreadFix
- How you can accomplish important security and quality milestones more easily in your projects
More Related Content
What's hot
Popular Approaches to Preventing Code Injection Attacks are Dangerously Wrong

Presentation by John Matthew Holt, Founder and CTO, Waratek at OWASP AppSec USA 2017
Machine Learning in Malware Detection

When dealing with over 300 hundred thousand of malware samples every day, we had to deploy the state-of-the-art techniques to combat cyberthreats. And among them - machine learning algorithms.
In this whitepaper, we start from describing the basic approaches and proceed to explaining the key applications of machine learning algorithms to automated malware detection. Learn more about how Kaspersky Lab protects businesses like yours => https://kas.pr/8dxv
Secure Code review - Veracode SaaS Platform - Saudi Green Method

Veracode provides the world’s leading Application Risk Management Platform. Veracode's patented and proven cloud-based capabilities allow customers to govern and mitigate software security risk across a single application or an enterprise portfolio with unmatched simplicity. Veracode was founded with one simple mission in mind: to make it simple and cost-effective for organizations to accurately identify and manage application security risk.
Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...

Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...Microsoft Tech Community
Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, and Azure
7 Reasons Your Applications are Attractive to Adversaries

Presentation from 18 November 2014.
Software applications need to be delivered faster and across more platforms than ever. To build high quality software in short order, we’ve seen a dramatic shift from source code to component-based development, with open source and third party components providing the innovation and efficiency that developers need.
Unfortunately, our dependence on components is growing faster than our ability to secure them. These shared components are not top-of-mind when considering application risk. Worse yet, components are increasingly the preferred attack surface in today’s applications.
The combination of growing component usage, coupled with lack of security, requires us to urgently re-evaluate traditional application security approaches and identify practical next steps for closing this security gap.
So what’s the “neglected 90%,” why is it attractive to your adversaries and what can you do about it? Plenty. Here are 7 key points, for starters.
http://bit.ly/AHC_USAF
Pentesting Your Own Wireless Networks, June 2011 Issue

Pentesting Your Own Wireless Networks, June 2011 Issue
The Web AppSec How-To: The Defender's Toolbox

Web application security has made headline news in the past few years. In this article, we review the various Web application security tools and highlight important decision factors to help you choose the application security technology best suited for your environment.
Understanding & Addressing OWASP’s Newest Top Ten Threat: Using Components wi...

In 2013, the Open Web Application Security Project (OWASP) was updated to include “A9: using components with known vulnerabilities.” This paper explains this new threat with practical ideas for reducing risk from open source components which now comprise 80% of an average application.
Crafting Super-Powered Risk Assessments by Digital Defense Inc & Veracode

http://www.ddifrontline.com
Digital Defense Inc (DDI) and Veracode present the "Crafting Super-Powered Risk Assessments" webinar and slides. The presentation covers security assessments, application security, and how to manage risk.
Secure coding presentation Oct 3 2020

Secure Coding, What you need to know as a developer, SAST, DAST, DevOps, OWASP, Application Security
Application Security Guide for Beginners 

This beginner’s guide to application security focuses on the main concepts and keywords used in the Application Security domain. From a secure software development lifecycle (SDLC) to the top threats facing applications and their impacts, this guide covers it all!
This guide is divided into the following categories:
-Code DevelopmentMethodologies
-Code
-Application SecuritySolutions
-Common threats and their impacts
Secure Coding for Java - An Introduction

Ce talk est une introduction au Secure Coding pour Java. Il s'efforcera de présenter via différents exemples les bonnes pratiques permettant de développer de manière pragmatique une application java sécurisée. Nous aborderons aussi bien des pratiques fonctionnelles que des morceaux de codes java à erreurs et leur correctifs.
We explain the security flaw that's freaking out the internet

Security geniuses say it's one of the most exceedingly awful PC weaknesses they've at any point seen.
The Duqu 2.0: Technical Details

Earlier this year, during a security sweep, Kaspersky Lab detected a cyber intrusion affecting several of its internal systems. Following this finding, we launched a large-scale investigation, which led to the discovery of a new malware platform from one of the most skilled, mysterious and
powerful groups in the APT world – Duqu. The Duqu threat actor went dark in 2012 and was believed to have stopped working on this project - until now. Our technical analysis
indicates the new round of attacks include an updated version of the infamous 2011 Duqu malware, sometimes referred to as the step-brother of Stuxnet. We named this
new malware and its associated platform “Duqu 2.0”.
Victims of Duqu 2.0 have been found in several places, including western countries, the Middle East and Asia. The actor appears to compromise both final and utilitarian targets, which allow them to improve their cyber capabilities. Most notably, some of the new 2014-2015 infections are linked to the P5+1 events and venues related to the negotiations with Iran about a nuclear deal. The threat actor behind Duqu appears to have launched attacks at the venues for some of these high level talks.
In addition to the P5+1 events, the Duqu 2.0 group has launched a similar attack in relation to the 70th anniversary event of the liberation of Auschwitz-Birkenau.
In the case of Kaspersky Lab, the attack took advantage of a zero-day (CVE-2015-2360) in the WindowsKernel, patched by Microsoft on June 9 2015 and possibly up to two other, currently patched vulnerabilities, which were zeroday at that time.
Infrastructure as (Secure) Code

Software-defined networking is the latest technology in a move to abstract a variety of data center resources. As more and more of the data center is defined in code, some unique security challenges come to the fore.
In this session, we'll explore both sides of the security challenge. What types of controls and implementations are required to define security as part of your infrastructure code? What challenges does maintaining an infrastructure codebase present?
You'll learn not only how to integrate security into your infrastructure code but also how to properly and securely manage that codebase.
Application Security Management with ThreadFix

How to efficiently identify and remediate critical vulnerabilities in SAP and other Business Applications.
Vulnerabilities in individual applications harbor enormous risks for companies because they can be exploited by hackers to gain access to the corporate network and critical IT infrastructure such as SAP systems. An effective approach to application security management therefore must take the entire application portfolio of a company into consideration. It must evaluate critical vulnerabilities uniform and must be capable to track their remediation, regardless of the programming language or the development environment used.
This approach is facilitated by ThreadFix, an open source software offered by Denim Group. In our webinar APPLICATION SECURITY MANAGEMENT we show you:
- How you can scan your SAP and other business applications automatically for critical vulnerabilities
- How you can easily track the remediation of vulnerabilities with ThreadFix
- How you can accomplish important security and quality milestones more easily in your projects
What's hot (20)
Popular Approaches to Preventing Code Injection Attacks are Dangerously Wrong

Popular Approaches to Preventing Code Injection Attacks are Dangerously Wrong
Secure Code review - Veracode SaaS Platform - Saudi Green Method

Secure Code review - Veracode SaaS Platform - Saudi Green Method
Advanced red teaming all your badges are belong to us

Advanced red teaming all your badges are belong to us
Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...

Find Security Flaws with AI using Microsoft Security Risk Detection, VSTS, an...
7 Reasons Your Applications are Attractive to Adversaries

7 Reasons Your Applications are Attractive to Adversaries
Pentesting Your Own Wireless Networks, June 2011 Issue

Pentesting Your Own Wireless Networks, June 2011 Issue
Security precognition chaos engineering in incident response

Security precognition chaos engineering in incident response
Understanding & Addressing OWASP’s Newest Top Ten Threat: Using Components wi...

Understanding & Addressing OWASP’s Newest Top Ten Threat: Using Components wi...
Crafting Super-Powered Risk Assessments by Digital Defense Inc & Veracode

Crafting Super-Powered Risk Assessments by Digital Defense Inc & Veracode
We explain the security flaw that's freaking out the internet

We explain the security flaw that's freaking out the internet
Viewers also liked
Applied and clinical anatomy of lower limb

everything you need to know about clinical anatomy of lower limb
Viewers also liked (9)
Similar to ht-f02-inside-the-world-of-java-applets_final
Effectiveness of AV in Detecting Web Application Backdoors

Effectiveness of AV in Detecting Web Application Backdoors by Rahul Sasi @ null Mumbai Meet in January, 2011
IRJET- Bug Hunting using Web Application Penetration Testing Techniques.

https://www.irjet.net/archives/V6/i3/IRJET-V6I31385.pdf
Orchestrating Software Defined Networks To Disrupt The Apt Kill Chain

Orchestrating Software Defined Networks To Disrupt The Apt Kill Chain
Owasp masvs spain 17

Mediante el pentest de aplicaciones móviles, es posible identificar los diferentes tipos de errores que comenten en el desarrollo y pueden poner en riesgo datos del usuario final. Se explica cómo aplicando técnicas de ingeniería inversa y hooking se puede manipular las funcionalidades de la aplicación y probar los niveles de seguridad.
Java: A Secure Programming Language for Today's Market

In the software development sector, Java has become one of the most well-liked and commonly used programming languages. Along with being adaptable and cross-platform compatible, Java is recognized for having strong security measures.
Serverless - minimizing the attack surface

Slides from my talk at ServerlessConf NYC 2017.
The talk will cover the various aspects of reducing the attack surface on serverless applications with an emphasis on maintaining least privileged access. I’ll cover the possible ways for attackers to leverage an overly permissive application and what might be the impacts of such attempts. In the talk, I’ll present a demo of an open source tool which can help you maintain least privileged roles and policies for your Lambda functions and reduce the overall attack surface on your serverless application.
Devoid Web Application From SQL Injection Attack

ABSTRACT: The entire field of web based application is controlled by the internet. In every region, World Wide Web is hugely necessary. So, network assurance is badly assuring job for us. Several kind of attacker or application programmer is attempting to split the immunity of information and destroy the instruction composed in the database. The SQL Injection Attack is very large safety measure risk in that present day. The indicated attacks allow to attacker’ s unlimited access from the database or still authority of database those determine web based application. That manages conscious and secret records and put the injurious SQL query put to modify the expected function. Many database reviewer and theorist give distinct concept to avoid regarding SQL Injection Attack. But no one of the concept is completely adaptable to. This research introduces a latest framework to protecting web based application from the SQL Injection Attack. Introduced framework i.e. present in this research is based on two techniques known as SQM (SQL Query Monitor) and Sanitization Application. That is the two ways filter program which analyses the user query and generate a separate key for user before it is sent to the application server. Several aspects of SQL Injection Attack are also discussed in that research.
Sania: Syntactic and Semantic Analysis for Automated Testing against SQL Inje...

With the recent rapid increase in interactive web applications that employ back-end database services, an SQL injection attack has become one of the most serious security threats. The SQL injection attack allows an attacker to access the underlying database, execute arbitrary commands at intent, and receive a dynamically generated output, such as HTML web pages. In this paper, we present our technique, Sania, for detecting SQL injection vulnerabilities in web applications during the development and debugging phases. Sania intercepts the SQL queries between a web application and a database, and automatically generates elaborate attacks according to the syntax and semantics of the potentially vulnerable spots in the SQL queries. In addition, Sania compares the parse trees of the intended SQL query and those resulting after an attack to assess the safety of these spots. We evaluated our technique using real-world web applications and found that our solution is efficient in comparison with a popular web application vulnerabilities scanner. We also found vulnerability in a product that was just about to be released.
【HITCON FreeTalk 2021 - SolarWinds 供應鏈攻擊事件分析】

【HITCON FreeTalk 2021 - 近期供應鏈及勒索病毒事件剖析】
➠ Talk: SolarWinds 供應鏈攻擊事件分析
➠ Speaker: Fox-IT 研究員 Zywu, 台灣駭客協會理事 CK
➠ Video: https://fb.watch/4hg1RYiQWw/
AppSec California 2016 - Making Security Agile

Your security processes are just as good as its level of integration with SDLC. If your SDLC is agile, so should be security.
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Simon Wong and Chris Cram, Scalar security experts, discuss how Palo Alto Networks technology disrupts the entire malware kill chain. Attendees will also gain insight on flexible deployment options to better serve their mobile users, and how to get the most out of their Palo Alto Networks deployment.
Similar to ht-f02-inside-the-world-of-java-applets_final (20)
Effectiveness of AV in Detecting Web Application Backdoors

Effectiveness of AV in Detecting Web Application Backdoors
IRJET- Bug Hunting using Web Application Penetration Testing Techniques.

IRJET- Bug Hunting using Web Application Penetration Testing Techniques.
Orchestrating Software Defined Networks To Disrupt The Apt Kill Chain

Orchestrating Software Defined Networks To Disrupt The Apt Kill Chain
Java: A Secure Programming Language for Today's Market

Java: A Secure Programming Language for Today's Market
Sania: Syntactic and Semantic Analysis for Automated Testing against SQL Inje...

Sania: Syntactic and Semantic Analysis for Automated Testing against SQL Inje...
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.
ht-f02-inside-the-world-of-java-applets_final
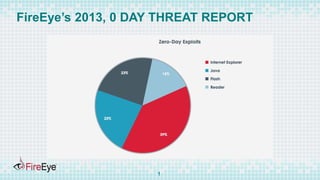
- 1. FireEye’s 2013, 0 DAY THREAT REPORT 1
- 2. PERENTAGE OF JAR ATTACKS AMONGST DRIVE BY DOWNLOAD 2
- 3. TARGETED ATTACKS CVE-2013-2465 used in strategic Web Compromise on an Embassy. Exploit was leveraged to disable security permissions, after which malicious executable was executed, which initiated call back and in the response base 64 embedded executable was served. 3
- 4. #RSAC SESSION ID: Abhishek Singh Varun Jain INTO THE WORLD OF JAVA APPLETS HT-F02 Malware Researcher FireEye Senior Staff Research Scientist Engineer FireEye
- 6. ATTACK FLOW Vulnerability Elevation of Privilege Security Manager Disabled Download and Execute the malware. 6
- 7. VULNERABILITIES Improper implementation of Java Runtime Environment awt_ImagingLib.c 7
- 8. VULNERABILITIES Type Confusion Ex: CVE-2011-3521/CVE-2012-0507 8
- 9. VULNERABILITIES Type Confusion Example: CVE 2012-0507 9
- 10. VULNERABILITIES Improper implementation of base classes Bug inside the base classes can be used to run privileged code from untrusted code. Eg CVE 2013-5076 10
- 11. DIVE INTO THE EXPLOITATION BYJAVA Live Demo 11
- 12. EXPLOITATION BASED UPON THE OPERATING SYSTEM 12
- 14. OBFUSCATION FLOW STEPS obfuscated string => decrypting function => parameter to the function 14
- 15. OBFUSCATION 15
- 16. #RSAC CHALLENGES FOR A FILE BASED SANDBOX.
- 17. HTML PAGE FOR EXECUTION 17
- 19. RIGHT ENVIRONMENT CVE-2012-0507 : Java SE 7 Update 2, 6 Update 30, 5.0 Update 33 19
- 21. Obfuscation Hide the Data , name of URL, file name Data Obfuscation : 21
- 22. METRICS TO DETERMINE OBFUSCATION N-gram, Entropy and Word Size N-gram checks for the probability of occurrence of certain sequence based upon the good and the bad sample set Entropy checks for the distribution of the used bytes codes Word Size checks if very long strings are used 22
- 24. FUNCTIONAL OBFUSCATION Hide the function Names By Using reflection API calls. Two Steps Process: a. Create the Obfuscated API calls. b. Use Reflection API to call at the runtime. 24
- 25. API’s FOR RETRIVING CLASS NAMES Class.forName() Object.getClass() Access to Fields, Methods, and Constructors of the Class a. getMethod() b. getField() 25
- 26. MALICIOUS INDICATORS: NAMES OF THE CLASS FILES. 26
- 27. N-GRAM ANALYSIS ON CLASS NAMES Accuracy ~ 90%. 27
- 28. #RSAC DESIGN ARCHITECTURE FOR A DETECTION MODEL
- 29. FEATURES IN A DETECTION MODEL Correlation between the static using probabilistic and Machine learning Algorithms, dynamic behavior and the network communication is a must . 29
- 30. FEATURES FOR A DETECTION MODEL Multi Flow Analysis of a network stream is must. 30
- 31. DESIGN ARCHITECTURE Multi Vector Multi Flow analysis providing correlation between the static dynamic and network behavior of a file. 31
- 32. SUMMARY JAR attacks are complex make use of obfuscation, reflection to prevent the static analysis which provides challenge to static scanning. Detonation of the JAR inside the file based sandboxes require the input parameters, live internet connection, right version which yet provided challenge to the file based sandbox. Multi Vector and Multi Flow analysis is must for detection of JAR. 32
- 33. SO WHAT SHOULD WE DO ? Ensure latest version java plugin is installed on client browser. Leverage and use the Java security policy built around certificate signing. Make an educated decision about use of Java Plugin. Detection solution at the Perimeter : Automated Analysis System leveraging correlation is must to detect and prevent sophisticated unknown jar applet attacks File based sandbox will fail to analyze the behavior of malicious jar. These are designed as a research tool. Static Scanning has limitations . 33
- 34. Q&A 34
- 35. REFERENCES Brewing up Trouble: Analyzing the four widely exploited Java Vulnerabilities. https://www.fireeye.com/content/dam/legacy/resources/pdfs/fireey e-java-vulnerabilities.pdf. A daily grind : Filtering Java Vulnerabilities. I https://www.fireeye.com/content/dam/legacy/resources/pdfs/fireeye -a-daily-grind-filtering-java-vulnerabilities.pdf 35
- 36. ACKNOWLEDGEMENTS We would like to express gratitude to Anirban Das and Ali Mesdaq, our colleagues at FireEye, for their help with NGRAM analysis. 36
- 37. Contact Information Varun Jain Email : varun.jain@fireeye.com Abhishek Singh: Email : abhishek.singh@fireeye.com 37
