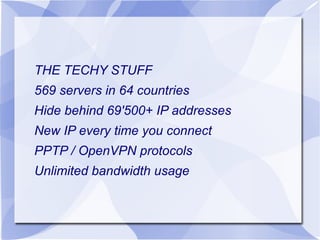
HideMyAss offers various online privacy services, including a free web proxy, VPN, and anonymous email, to protect users from identity theft and online surveillance. Their technology features over 569 servers in 64 countries and employs advanced encryption to secure internet connections. The platform provides tools to surf anonymously, secure file uploads, and hide online identities.