Hipaa it risk analysis and risk analysis
•
0 likes•279 views
The Compliancy Group is your complete HIPAA Compliance Solution. Try The Guard now to find out how easy HIPAA can be. Solve Omnibus, Meaningful Use, HITECH.
Report
Share
Report
Share
Download to read offline
Recommended
HIPAA eBOOK: Avoid Common HIPAA Violations 

The top 3 HIPAA violations could be happening under your watch.
1. Inadequate Tracking of Media
2. Inadequate Security
3. Inadequate Policies
If you deal with ePHI, you must comply. Find out how to remain compliant with our tips.
Hipaa for business associates simple

Presentation designed to explain Business Associates the basics of HIPAA and real-life examples of cases that failed to implement and follow HIPAA requirements on a timely basis.
Redspin Webinar Business Associate Risk

Webinar on how healthcare organizations can manage business associate IT security risk.
Redspin & Phyllis and Associates Webinar- HIPAA,HITECH,Meaninful Use,IT Security

Slides from our 1/20/2011 webinar - HIPAA & HITECH Requirements, Compliance, Meaningful Use, and IT security assessments...we know it’s confusing!
Let’s focus on what you need to know!
An Overview of the Major Compliance Requirements

In this blog, we will explore some of the US government’s compliance standards that are helpful for many federal, state and local agencies while procuring technology and related services.
HIPAA Security Audits in 2012-What to Expect. Are You Ready?

Within the 2009 American Recovery and Reinvestment Act (ARRA) was a legislative gem, the HITECH Act. HITECH provided a much needed “shot in the arm” (no pun intended) for the vanguard of healthcare technology advocates (including industry leaders, academics, economists, politicians, and concerned citizens), who had been promoting the necessity of modernizing the U.S. healthcare system for years.
Recommended
HIPAA eBOOK: Avoid Common HIPAA Violations 

The top 3 HIPAA violations could be happening under your watch.
1. Inadequate Tracking of Media
2. Inadequate Security
3. Inadequate Policies
If you deal with ePHI, you must comply. Find out how to remain compliant with our tips.
Hipaa for business associates simple

Presentation designed to explain Business Associates the basics of HIPAA and real-life examples of cases that failed to implement and follow HIPAA requirements on a timely basis.
Redspin Webinar Business Associate Risk

Webinar on how healthcare organizations can manage business associate IT security risk.
Redspin & Phyllis and Associates Webinar- HIPAA,HITECH,Meaninful Use,IT Security

Slides from our 1/20/2011 webinar - HIPAA & HITECH Requirements, Compliance, Meaningful Use, and IT security assessments...we know it’s confusing!
Let’s focus on what you need to know!
An Overview of the Major Compliance Requirements

In this blog, we will explore some of the US government’s compliance standards that are helpful for many federal, state and local agencies while procuring technology and related services.
HIPAA Security Audits in 2012-What to Expect. Are You Ready?

Within the 2009 American Recovery and Reinvestment Act (ARRA) was a legislative gem, the HITECH Act. HITECH provided a much needed “shot in the arm” (no pun intended) for the vanguard of healthcare technology advocates (including industry leaders, academics, economists, politicians, and concerned citizens), who had been promoting the necessity of modernizing the U.S. healthcare system for years.
The Summary Guide to Compliance with the Kenya Data Protection Law 

The Data Protection Act 2019, was enacted on November 8th, 2019, ushering a new era of accountability and responsibility with regard to processing of personal data and information. Naturally, there has been a resurrection of the chatter around data protection in increasingly data-driven social and economic settings. The question on everyone’s mind being what does this mean for me?
The Evolution of Data Privacy: 3 things you didn’t know

The European Union’s proposed General Data Protection Regulation (GDPR) has left even the most informed confused. This new regulation has been designed to update the current directive which was drafted in a time that was in technology terms, prehistoric. It’s time to evolve.
Keeping Your Business HIPAA-Compliant

We explain what your business needs to know about the HIPAA Omnibus Rule and share tips for evaluating secure cloud backup solutions that can facilitate compliance with regulatory requirements.
Cybersecurity & Data Challenges

Workshop at Simulation for Digital Health - London South Bank University
Assessing Your Hosting Environment for HIPAA Compliance

When you’re striving to be HIPAA compliant, the idea of third-party hosting can be daunting. Learn the key elements to consider when assessing your hosting environment for HIPAA compliance.
Solution Brief: Helping prepare for risk & compliance challenges for GDPR

Solution Brief: Helping prepare for risk & compliance challenges for GDPRIceberg Networks Corporation
Many aspects of GDPR compliance can be achieved through leveraging established data security and compliance management best practices. Four key focus areas to focus on include Risk Assessment, Breach Response, Data Governance, and Compliance Program Management. This paper explore each of these areas.Is Ukraine safe for software development outsourcing? 

Many companies that are looking for a software development outsourcing company in Ukraine wonder if the destination is safe in terms of politics, economy, business climate, and information security.
We’ve completed the guide that covers all these aspects and will hopefully help you make well-weighed conclusions.
Hipaa checklist for healthcare software

What are the significant aspects of software development in the healthcare industry? In healthcare software, it should ensure HIPAA IT compliance.
Complete Guide to General Data Protection Regulation (GDPR)

European government in 2016 adopted General Data Protection Regulation (GDPR) and was
put into effect on May 25, 2018, replacing the 1995’s Data Protection Directive to protect the
personal information of EU citizens. GDPR aims to govern personal data processing and ensure
processing is fair and lawful. It is also designed to emphasize the fundamental right to privacy.
Avoid the Audit Trap

Infographic describing the rising number of FINRA and SEC disciplinary actions and fines. It also informs customers about how EAI Information Systems can help companies be compliant and survive audits.
The HIPAA Security Rule: Yes, It's Your Problem

An overview of the HIPAA Security Rule for office managers, receptionists, doctors, physicians, and IT professionals. Need to get HIPAA compliant?
Learn more here: www.securitymetrics.com/sm/pub/hipaa/overview
Don't Let Cybersecurity Trip You Up

Infographic outlining regulations organizations should be aware of from the FDIC and FINRA and measures for cybersecurity compliance.
HIPAA Basic Healthcare Guide

This guide to designed to help private doctors and small clinics understand the HIPPA regulation and get them ready for an audit. The guide contains several checklists that will guide them step by step to make sure everything is done to create and secure and EMR network
DOL Fiduciary Rule Infographic

As the new DOL rule approaches, make sure your business is prepared. EAI has the technology today that you'll need to stay compliant tomorrow.
3 Steps to Automate Compliance for Healthcare Organizations

In this webinar, AvePoint's Chief Compliance & Risk Officer Dana Simberkoff and AvePoint's Director of Risk Management & Compliance Marc Dreyfus shared the playbook to jumpstart your comprehensive, automated program to mitigate the risk of data loss, privacy, and security breaches using AvePoint Compliance Guardian’s “Say it, do it, prove it” approach. To watch the webinar, please visit: http://www.avepoint.com/resources/videos/
You and HIPAA - Get the Facts

The HIPAA Security Rule - An overview and preview for 2014, from Summit Security Group. Summit Security Group is a business partner to Resource One, managed IT services provider for over 15 years to small and mid-sized businesses in the Portland Metro and Southwest Washington area.
Complying with HIPAA Security Rule

What is HIPAA?
HIPAA: Health Insurance Portability and Accountability Act
It was passed by Congress in 1996
It includes requirements for:
Transfer and continuation of health insurance coverage for millions of American workers and their families when they change or lose their jobs
Reducing healthcare fraud and waste
The protection and confidential handling of protected health information
HIPAA Security Rule
Establishes national standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity.
Requires appropriate safeguards to ensure the confidentiality, integrity, and security of electronic protected health information.
Safeguards include:
Administrative
Physical
Technical
Administrative Safeguards
HIPAA security rule requires covered entities to implement the following administrative safeguards:
Security Management Process
Security Personnel
Information Access Management
Workforce Training
Evaluation
Physical Safeguards
The security rule requires covered entities to implement physical safeguards such as:
Facility Access and Control
Access can be restricted through use of access cards, biometric scanners, keys, pass codes and so on
Workstation and Device Security
Develop and implement policies for workstation and device security
Implement unique password/user ids for each user
Proper user logs and records should be maintained
Technical Safeguards
The security rule requires a covered entity to implement technical safeguards such as:
Access Controls
Audit Controls
Integrity Controls
Transmission Security
Want to learn more about HIPAA, HIPAA Privacy and Security Rule, its requirements and best practices to comply with them? ComplianceOnline webinars and seminars are a great training resource. Check out the following links:
How to examine security policies, practices, and risk issues to comply with HIPAA
How to use social media and texting without breaking HIPAA rules
How to Conduct risk analysis to comply with HIPAA
HIPAA/HITECH Assessment for Healthcare Business Associates
How to comply with HIPAA Omnibus Rule
Understanding new rules and responsibilities of Privacy Officer under HIPAA
HIPAA Security and Breach Rule Compliance
For more details Visit us at:http://www.complianceonline.com/the-new-hipaa-audit-program-focus-webinar-training-703180-prdw?channel=ppt-slideshare
An Overview of HIPAA Laws and Regulations.pdf

Seasia has several years of experience offering HIPAA-compliant IT services for the healthcare industry.
More Related Content
What's hot
The Summary Guide to Compliance with the Kenya Data Protection Law 

The Data Protection Act 2019, was enacted on November 8th, 2019, ushering a new era of accountability and responsibility with regard to processing of personal data and information. Naturally, there has been a resurrection of the chatter around data protection in increasingly data-driven social and economic settings. The question on everyone’s mind being what does this mean for me?
The Evolution of Data Privacy: 3 things you didn’t know

The European Union’s proposed General Data Protection Regulation (GDPR) has left even the most informed confused. This new regulation has been designed to update the current directive which was drafted in a time that was in technology terms, prehistoric. It’s time to evolve.
Keeping Your Business HIPAA-Compliant

We explain what your business needs to know about the HIPAA Omnibus Rule and share tips for evaluating secure cloud backup solutions that can facilitate compliance with regulatory requirements.
Cybersecurity & Data Challenges

Workshop at Simulation for Digital Health - London South Bank University
Assessing Your Hosting Environment for HIPAA Compliance

When you’re striving to be HIPAA compliant, the idea of third-party hosting can be daunting. Learn the key elements to consider when assessing your hosting environment for HIPAA compliance.
Solution Brief: Helping prepare for risk & compliance challenges for GDPR

Solution Brief: Helping prepare for risk & compliance challenges for GDPRIceberg Networks Corporation
Many aspects of GDPR compliance can be achieved through leveraging established data security and compliance management best practices. Four key focus areas to focus on include Risk Assessment, Breach Response, Data Governance, and Compliance Program Management. This paper explore each of these areas.Is Ukraine safe for software development outsourcing? 

Many companies that are looking for a software development outsourcing company in Ukraine wonder if the destination is safe in terms of politics, economy, business climate, and information security.
We’ve completed the guide that covers all these aspects and will hopefully help you make well-weighed conclusions.
Hipaa checklist for healthcare software

What are the significant aspects of software development in the healthcare industry? In healthcare software, it should ensure HIPAA IT compliance.
Complete Guide to General Data Protection Regulation (GDPR)

European government in 2016 adopted General Data Protection Regulation (GDPR) and was
put into effect on May 25, 2018, replacing the 1995’s Data Protection Directive to protect the
personal information of EU citizens. GDPR aims to govern personal data processing and ensure
processing is fair and lawful. It is also designed to emphasize the fundamental right to privacy.
Avoid the Audit Trap

Infographic describing the rising number of FINRA and SEC disciplinary actions and fines. It also informs customers about how EAI Information Systems can help companies be compliant and survive audits.
The HIPAA Security Rule: Yes, It's Your Problem

An overview of the HIPAA Security Rule for office managers, receptionists, doctors, physicians, and IT professionals. Need to get HIPAA compliant?
Learn more here: www.securitymetrics.com/sm/pub/hipaa/overview
Don't Let Cybersecurity Trip You Up

Infographic outlining regulations organizations should be aware of from the FDIC and FINRA and measures for cybersecurity compliance.
HIPAA Basic Healthcare Guide

This guide to designed to help private doctors and small clinics understand the HIPPA regulation and get them ready for an audit. The guide contains several checklists that will guide them step by step to make sure everything is done to create and secure and EMR network
DOL Fiduciary Rule Infographic

As the new DOL rule approaches, make sure your business is prepared. EAI has the technology today that you'll need to stay compliant tomorrow.
3 Steps to Automate Compliance for Healthcare Organizations

In this webinar, AvePoint's Chief Compliance & Risk Officer Dana Simberkoff and AvePoint's Director of Risk Management & Compliance Marc Dreyfus shared the playbook to jumpstart your comprehensive, automated program to mitigate the risk of data loss, privacy, and security breaches using AvePoint Compliance Guardian’s “Say it, do it, prove it” approach. To watch the webinar, please visit: http://www.avepoint.com/resources/videos/
You and HIPAA - Get the Facts

The HIPAA Security Rule - An overview and preview for 2014, from Summit Security Group. Summit Security Group is a business partner to Resource One, managed IT services provider for over 15 years to small and mid-sized businesses in the Portland Metro and Southwest Washington area.
Complying with HIPAA Security Rule

What is HIPAA?
HIPAA: Health Insurance Portability and Accountability Act
It was passed by Congress in 1996
It includes requirements for:
Transfer and continuation of health insurance coverage for millions of American workers and their families when they change or lose their jobs
Reducing healthcare fraud and waste
The protection and confidential handling of protected health information
HIPAA Security Rule
Establishes national standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity.
Requires appropriate safeguards to ensure the confidentiality, integrity, and security of electronic protected health information.
Safeguards include:
Administrative
Physical
Technical
Administrative Safeguards
HIPAA security rule requires covered entities to implement the following administrative safeguards:
Security Management Process
Security Personnel
Information Access Management
Workforce Training
Evaluation
Physical Safeguards
The security rule requires covered entities to implement physical safeguards such as:
Facility Access and Control
Access can be restricted through use of access cards, biometric scanners, keys, pass codes and so on
Workstation and Device Security
Develop and implement policies for workstation and device security
Implement unique password/user ids for each user
Proper user logs and records should be maintained
Technical Safeguards
The security rule requires a covered entity to implement technical safeguards such as:
Access Controls
Audit Controls
Integrity Controls
Transmission Security
Want to learn more about HIPAA, HIPAA Privacy and Security Rule, its requirements and best practices to comply with them? ComplianceOnline webinars and seminars are a great training resource. Check out the following links:
How to examine security policies, practices, and risk issues to comply with HIPAA
How to use social media and texting without breaking HIPAA rules
How to Conduct risk analysis to comply with HIPAA
HIPAA/HITECH Assessment for Healthcare Business Associates
How to comply with HIPAA Omnibus Rule
Understanding new rules and responsibilities of Privacy Officer under HIPAA
HIPAA Security and Breach Rule Compliance
For more details Visit us at:http://www.complianceonline.com/the-new-hipaa-audit-program-focus-webinar-training-703180-prdw?channel=ppt-slideshare
What's hot (20)
The Summary Guide to Compliance with the Kenya Data Protection Law 

The Summary Guide to Compliance with the Kenya Data Protection Law
The Evolution of Data Privacy: 3 things you didn’t know

The Evolution of Data Privacy: 3 things you didn’t know
Assessing Your Hosting Environment for HIPAA Compliance

Assessing Your Hosting Environment for HIPAA Compliance
Solution Brief: Helping prepare for risk & compliance challenges for GDPR

Solution Brief: Helping prepare for risk & compliance challenges for GDPR
Is Ukraine safe for software development outsourcing? 

Is Ukraine safe for software development outsourcing?
Complete Guide to General Data Protection Regulation (GDPR)

Complete Guide to General Data Protection Regulation (GDPR)
3 Steps to Automate Compliance for Healthcare Organizations

3 Steps to Automate Compliance for Healthcare Organizations
Similar to Hipaa it risk analysis and risk analysis
An Overview of HIPAA Laws and Regulations.pdf

Seasia has several years of experience offering HIPAA-compliant IT services for the healthcare industry.
Meeting the Challenges of HIPAA Compliance, Phishing Attacks, and Mobile Secu...

Meeting the Challenges of HIPAA Compliance, Phishing Attacks, and Mobile Secu...Envision Technology Advisors
Healthcare organizations (HCOs) are facing three major IT security and compliance
challenges. First, IT regulations such as HIPAA are getting stricter and enforcement actions
are becoming more common and costly....The Importance of HIPAA Compliance in ensuring the Privacy and Security of PHI!

All the healthcare applications dealing with PHI data must comply with HIPAA rules and regulations as sensitive patient data is vulnerable to security threats and violations. HIPAA compliance ensures high security and privacy of sensitive healthcare patient data by enforcing measures such as access control, encryption, data disposal, data backup, automatic logging-off, auditing, etc.
HIPAA-Compliant App Development Guide for the Healthcare Industry.pdf

This is an article about HIPAA-compliant app development for the healthcare industry. It discusses the importance of HIPAA compliance and the risks of non-compliance. The article also outlines the steps involved in developing a HIPAA-compliant app. Some of the important points from this article are that HIPAA compliance is an ongoing process and that there is no certification required to build a HIPAA-secure app.
HIPAA HiTech Regulations: What Non-Medical Companies Need to Know

HIPAA HiTech regulations, since October 2013, have real teeth for Business Associates (BAs). If your company comes into contact with Personal Health Information (PHI) in the course of running your business then you must comply with these regulations. Many law firms and consulting firms are BAs You need to know and adhere to the HIPAA HiTECH regulations; or be subject to potentially heavy fines.
Cloud compliance test

If you have more questions about HIPAA cloud compliance requirements or how prancer can help your healthcare facility achieve and maintain compliance, contact us today to learn more.
The importance of hipaa compliance and training

Discuss the importance of complying to HIPAA. Learn new training techniques.
Application Developers Guide to HIPAA Compliance

Software developers building mobile health applications need to be HIPAA compliant if their application will be collecting and sharing protected health information. This free plain language guide gives developers everything they need to know about mobile health app development and HIPAA.
Not every mHealth app needs to be HIPAA compliant. Not sure whether your mHealth application needs to be HIPAA compliant or not? Read the guide to find out!
HIPAA-Compliant Healthcare App.pdf

What exactly is HIPPA Compliance, and why is it important in app development? Things to think about, and how to get your own app ,a comprehensive guide to follow Checkout the presentation to know more
CHAPTER3 Maintaining ComplianceMANY LAWS AND REGULATIONS.docx

CHAPTER
3 Maintaining Compliance
MANY LAWS AND REGULATIONS ARE IN PLACE regarding the protection of
information technology (IT) systems. Companies have a requirement to comply with the laws that
apply to them. The first step is to understand the laws. You’re not expected to be a lawyer, but you
should understand the basics of relevant laws.
Once you have an idea of which laws and regulations apply, you can then dig in deeper to
ensure your organization is in compliance. The cost of not complying can sometimes be
expensive. Fines can be in the hundreds of thousands of dollars. Some offenses can result in jail
time.
Chapter 3 Topics
This chapter covers the following topics and concepts:
• What U.S. compliance laws exist
• What some relevant regulations related to compliance are
• What organizational policies for compliance should be considered
• What standards and guidelines for compliance exist
Chapter 3 Goals
When you complete this chapter, you will be able to:
• Define compliance
• Describe the purpose of FISMA
• Identify the purpose and scope of HIPAA
• Describe GLBA and SOX, and the impact for IT
• Describe the purpose of FERPA
• Identify the purpose and scope of CIPA
• List some federal entities that control regulations related to IT
• Describe the purpose of PCI DSS
• Describe the contents of SP 800-30
• Describe the purpose of COBIT
• Describe the purpose of ISO and identify some relevant security standards
• Identify the purpose of ITIL
• Identify the purpose of CMMI
U.S. Compliance Laws
Many laws exist in the United States related to information technology (IT). Companies affected
by the laws are expected to comply with the laws. This is commonly referred to as compliance.
Many organizations have internal programs in place to ensure they remain in compliance with
relevant laws and regulations. These programs commonly use internal audits. They can also use
certification and accreditation programs. When compliance is mandated by law, external audits are
often done. These external audits provide third-party verification that the requirements are being
met.
An old legal saying is “ignorance is no excuse.” In other words, you can’t break the law and
then say “I didn’t know.” The same goes for laws that apply to any organization. It’s important for
any organization to know what the relevant laws and regulations are.
You aren’t expected to be an expert on any of these laws. However, as a manager or executive,
you should be aware of them. You can roll any of the relevant laws and regulations into a
compliance program for more detailed checks.
This section covers the following U.S. laws:
• Federal Information Security Management Act (FISMA) 2002
• Health Insurance Portability and Accountability Act (HIPAA) 1996
• Gramm-Leach-Bliley Act (GLBA) 1999
• Sarbanes-Oxley Act (SOX) 2002
• Family Educational Rights and Privacy Act (FERPA) 1974
• Children’s Internet Protection Act (CIPA) 2000
Federal Information ...
HIPAA Security 2019

The current healthcare system in the United States is heavily influenced by HIPAA Security. This translates into a need to understand technology and cybersecurity beyond the use of anti-malware applications. This presentation presents some of the basics Covered Entities and Business Associates must be aware of as it relates to HIPAA Security.
HIPAA Security Trends and Future Expectations

PYA Principal Barry Mathis, a former CIO, CTO, senior IT audit manager, and IT risk management consultant, presented at teh TSCPA Health Care Conference. His presentation, “HIPAA Security Trends and Future Expectations” will focuses on:
- Current HIPAA enforcement activities and future developments.
- Case studies that highlight the changing HIPAA landscape.
- Cyber threats that impact covered entities and business associates.
HIPAA Final Omnibus Rule Playbook

A step-by-step guide for helping healthcare organizations comply with HIPAA
Role-Based Access Governance and HIPAA Compliance: A Pragmatic Approach

This white paper discusses how some forward thinking organizations are using the passage of the HITECH Act as an opportunity to modernize how patient information is stored and accessed through electronic health records.
HIPAA Compliant Salesforce Health Cloud – Why Healthcare Organizations Must C...

With this fast paced world, healthcare consumers want their personalised information at a great speed. 71% of millennials want doctors to provide mobile applications for actively managing their health information which Salesforce health cloud does very well. Salesforce Health Cloud is fabricated to combine power and security of cloud with social and mobile technologies.
Let us first see what is HIPAA’s story and then move forward how Salesforce Health Cloud meet HIPAA guidelines.
Similar to Hipaa it risk analysis and risk analysis (20)
Meeting the Challenges of HIPAA Compliance, Phishing Attacks, and Mobile Secu...

Meeting the Challenges of HIPAA Compliance, Phishing Attacks, and Mobile Secu...
The Importance of HIPAA Compliance in ensuring the Privacy and Security of PHI!

The Importance of HIPAA Compliance in ensuring the Privacy and Security of PHI!
HIPAA-Compliant App Development Guide for the Healthcare Industry.pdf

HIPAA-Compliant App Development Guide for the Healthcare Industry.pdf
HIPAA HiTech Regulations: What Non-Medical Companies Need to Know

HIPAA HiTech Regulations: What Non-Medical Companies Need to Know
CHAPTER3 Maintaining ComplianceMANY LAWS AND REGULATIONS.docx

CHAPTER3 Maintaining ComplianceMANY LAWS AND REGULATIONS.docx
Role-Based Access Governance and HIPAA Compliance: A Pragmatic Approach

Role-Based Access Governance and HIPAA Compliance: A Pragmatic Approach
Overview Imagine you are the information security officer at a.docx

Overview Imagine you are the information security officer at a.docx
HIPAA Compliant Salesforce Health Cloud – Why Healthcare Organizations Must C...

HIPAA Compliant Salesforce Health Cloud – Why Healthcare Organizations Must C...
Recently uploaded
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Recently uploaded (20)
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
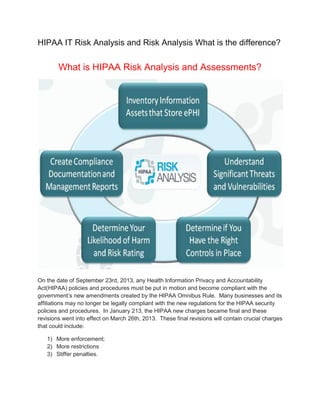
Hipaa it risk analysis and risk analysis
- 1. HIPAA IT Risk Analysis and Risk Analysis What is the difference? What is HIPAA Risk Analysis and Assessments? On the date of September 23rd, 2013, any Health Information Privacy and Accountability Act(HIPAA) policies and procedures must be put in motion and become compliant with the government’s new amendments created by the HIPAA Omnibus Rule. Many businesses and its affiliations may no longer be legally compliant with the new regulations for the HIPAA security policies and procedures. In January 213, the HIPAA new charges became final and these revisions went into effect on March 26th, 2013. These final revisions will contain crucial charges that could include: 1) More enforcement; 2) More restrictions 3) Stiffer penalties.
- 2. 1. Any business entity and its affiliations need to become compliant with these new HIPAA amendment rules and regulations. Some examples would be a health insurance company having to pay a huge fine of 1.7 million dollars, a large pharmacy having to pay a steep penalty of 1.44 million dollars or a large college university having to pay a whopping monetary fine of $400,000. Now the question now is if in fact your corporation can afford stiff penalties such as these examples. HIPAA policies and procedures surround the new HIPAA Omnibus Rule may cover over 200 security information topics that may be essential to a business and some examples are as follows: 1. Computer control access 2. Acceptable users and use of the computer 3. Developments for application software 4. Teams for direct emergency computer response systems 5. Viruses that could affect business computers 6. Planning contingency 7. Labeling and classifications of any data on a business computer 8. The destruction of any data 9. Digital signatures 10. Espionage from an economic standpoint 11. E-commerce 12. Mail sent electronically 13. Communications by any fax transmissions 14. Prevention of spam 15. LAN’s or Local Area Networks
- 3. Employers, officers, and any business directors of any business covered entity could also include criminal sanctions and liabilities. These sanctions may be up to $50,000 per incident and the individuals could also receive approximately 10 years in prison. Noncompliance with the HIPAA and HITECH rules is absolutely intolerable. There are hundreds of pages of information regarding these new regulations and amendments. The law is sometimes vague and very complicated but a corporation needs to make sure that their policies cover: 1) 2) 3) 4) Breach notification Sanction policies Business associate policies; and finally Confidential data policies and procedures. Any corporation needs to ensure that these four things are included in their new updated policies and procedures to become compliant with the revisions. The HIPAA and HITECH rules are very strong and powerful. Compliance with these rules is absolutely crucial to any business entity.
- 4. HIPAA Risk Assessment and hipaa Risk analysis are both standard processes for (IT) and information technology. These measures are crucial for a business entity trying to become compliant with efforts for these new revisions of these new security rules. Business entities always need to understand three terms in order to secure proper hipaa Risk analysis and the HIPAA Risk Assessments. The terms are "business risks", "business threats" and “and "business vulnerabilities". Some business steps to ensure proper hipaa Risk analysis and HIPAA Risk Assessment may include: 1. Data gathering 2. Security measures and its current risk assessment evaluations or implication 3. The level of business risk should be immediately determined 4. Security measures need to always be implemented into the business Business Address: The Compliancy Group LLC. 55 Broadway Unit 684 Greenlawn, NY 11740 Phone No:855 854 4722 Fax: 631.731.1643 Info@compliancygroup.com http://www.compliancy-group.com You Can follow us on Facebook | Linkedin | Twitter |