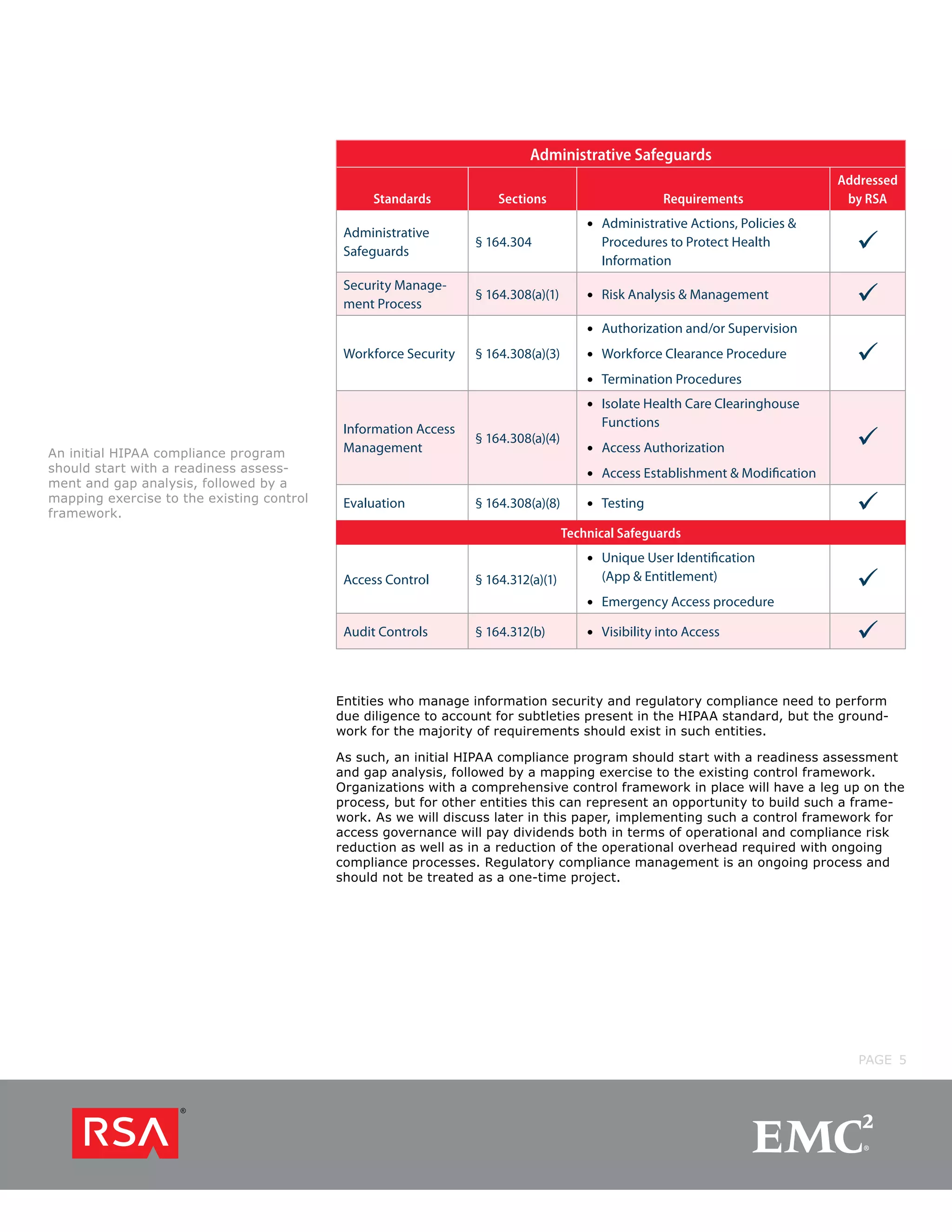
The passage discusses how the HITECH Act updated and strengthened the privacy and security requirements of the Health Insurance Portability and Accountability Act (HIPAA). It made HIPAA compliance more important and challenging for covered entities by extending requirements to business associates, increasing penalties, and requiring stricter auditing and breach notification. To comply with HIPAA, organizations need to implement an access governance framework that provides a unified view of user access across systems and enables dynamic access management, audit capabilities, and prevention of inappropriate access. The increased focus on compliance under HITECH presents an opportunity for organizations to improve access risk management and security.