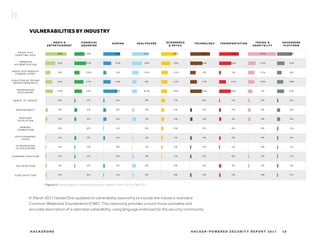
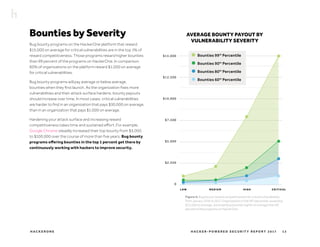
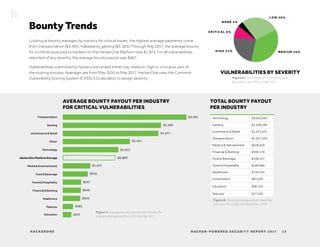
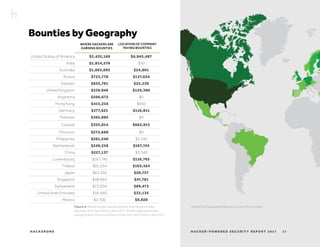
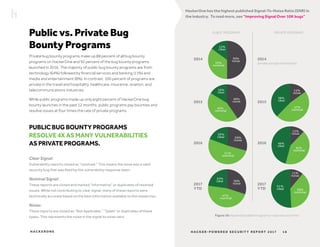
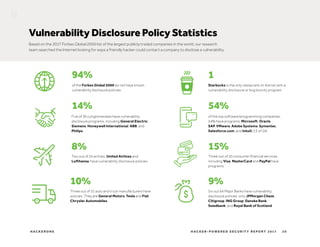
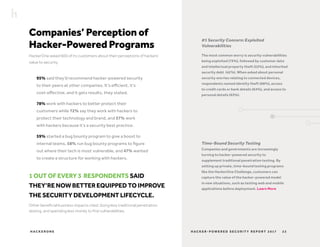
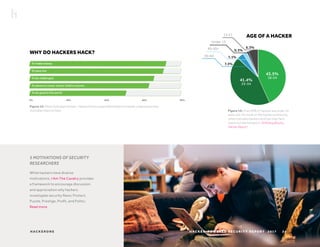
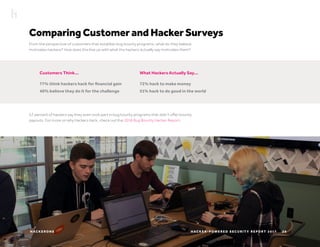
The 2017 Hacker-Powered Security Report highlights the growing adoption of bug bounty programs across various industries, with 41% of new programs initiated outside of technology sectors. Despite the increase in bug bounty participation, 94% of Fortune 2000 companies lack vulnerability disclosure policies, and the report emphasizes the need for improved security practices amidst rising cyber threats. The average bounty paid for critical vulnerabilities has seen a significant increase, reflecting a competitive landscape to attract skilled hackers.