The document provides an overview of the global cyber insurance market, including:
- The cyber insurance market is still in its infancy globally but has grown significantly in recent years, especially in the US where it is estimated to be worth $1.5 billion in 2015.
- The largest market is the US, driven by data breach legislation, high-profile cyber attacks increasing awareness, and demand from companies storing personal data.
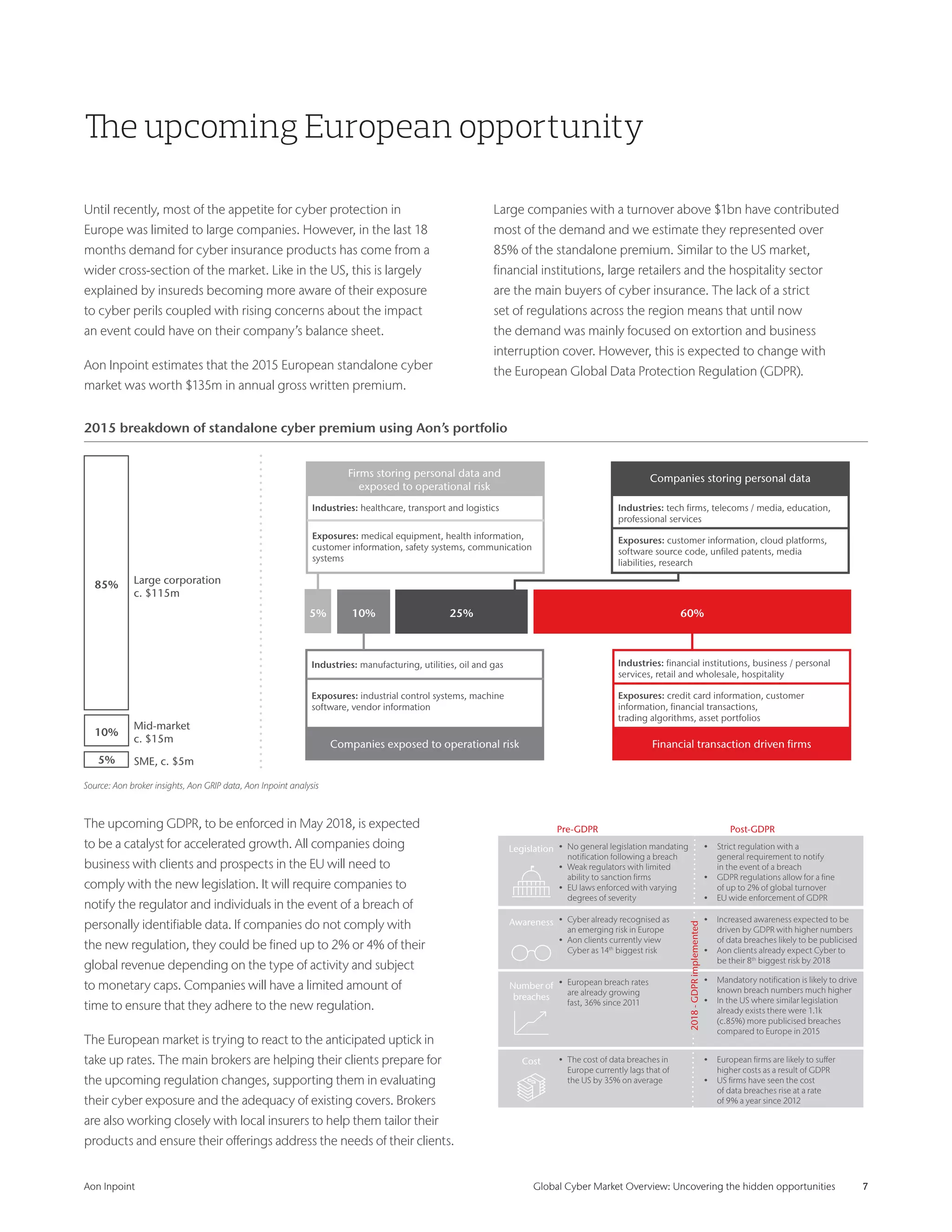
- The upcoming European GDPR regulation coming into effect in 2018 is expected to be a major driver for the growing but still relatively nascent European cyber insurance market.
- Various industries like retail, healthcare, and financial institutions are among the largest buyers of cyber insurance.