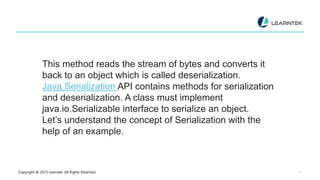
The document explains Java serialization, which converts an object's state into a byte stream for storage or transport, allowing it to be later deserialized back into an object. It details types of data streams in Java, including byte, data, character, and object streams, and highlights the use of the java.io.Serializable interface for serialization. The document includes code examples illustrating the serialization and deserialization process, including handling of transient fields that should not be serialized.







![Copyright @ 2015 Learntek. All Rights Reserved. 12
package com.serialization;
import java.io.IOException;
public class SerializationImplDemo {
public static void main(String args[]) {
DataObject dataObject = new DataObject();
dataObject.setClient(“Yolanda”);
dataObject.setStore(“Programming store”);
dataObject.setId(“hhhhh”);
dataObject.setPasswordKeys(“$MyG0tt!!”);
try {
SerializationDemoExample.serialize(“file.txt”, dataObject);
DataObject object = (DataObject)
SerializationDemoExample.deSerialize(“file.txt”);
System.out.println(object.toString());
} catch (IOException exp) {
exp.printStackTrace();
} catch (ClassNotFoundException exp) {
exp.printStackTrace();
}
}
}](https://image.slidesharecdn.com/gulshanserializationinjava-240511021254-02054c66/85/Gulshan-serialization-inJava-PPT-ex-pptx-12-320.jpg)

