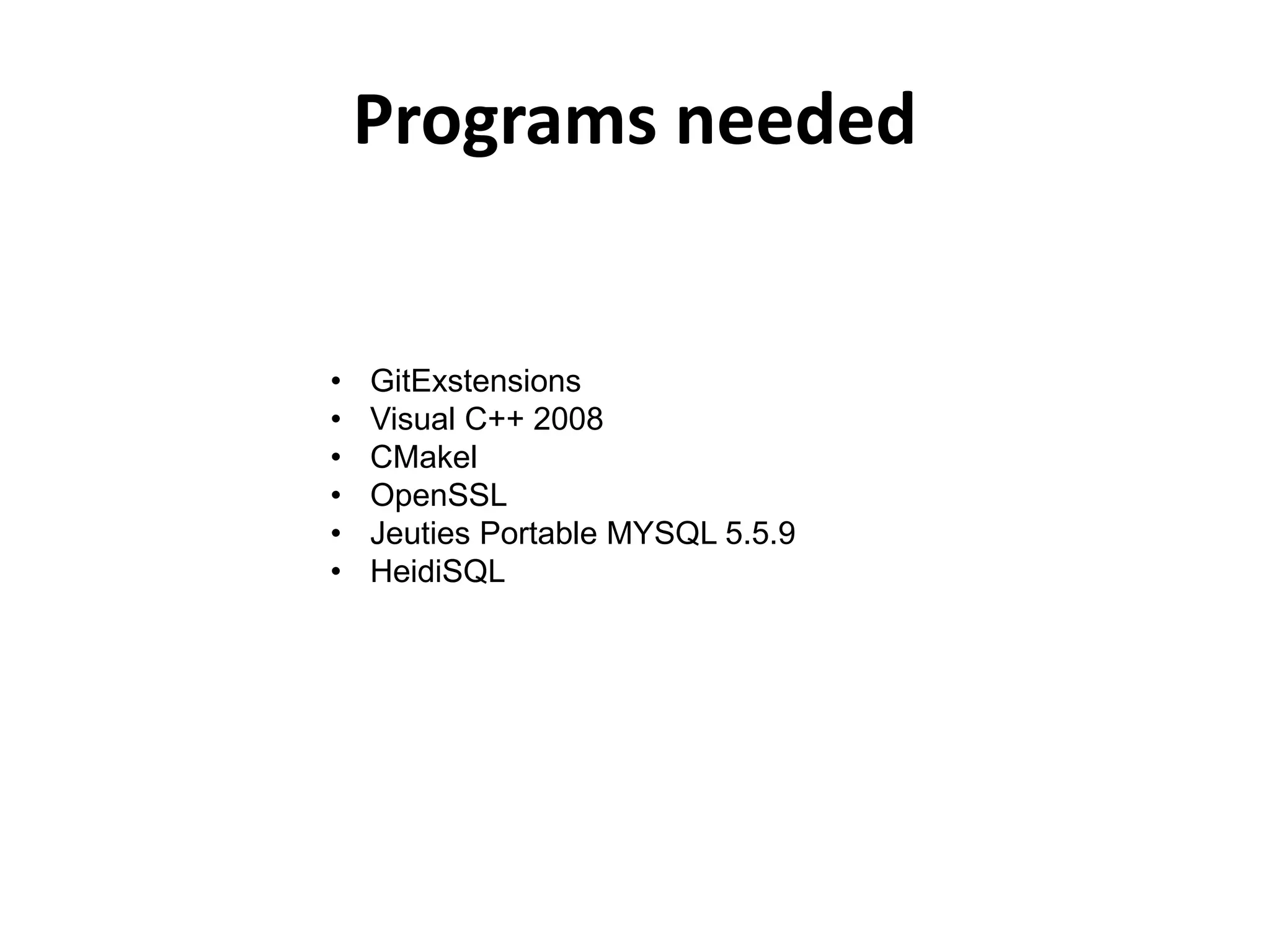
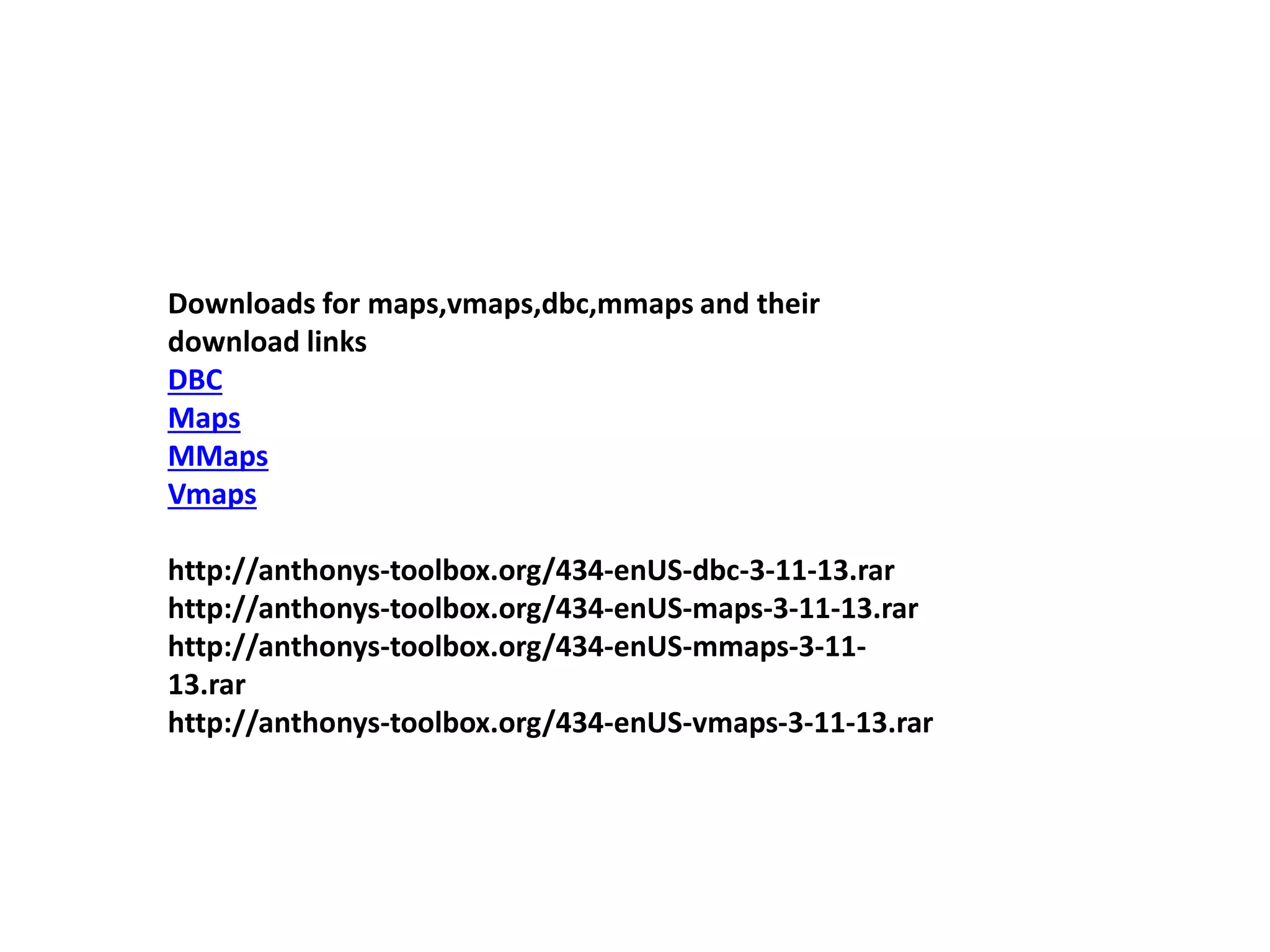
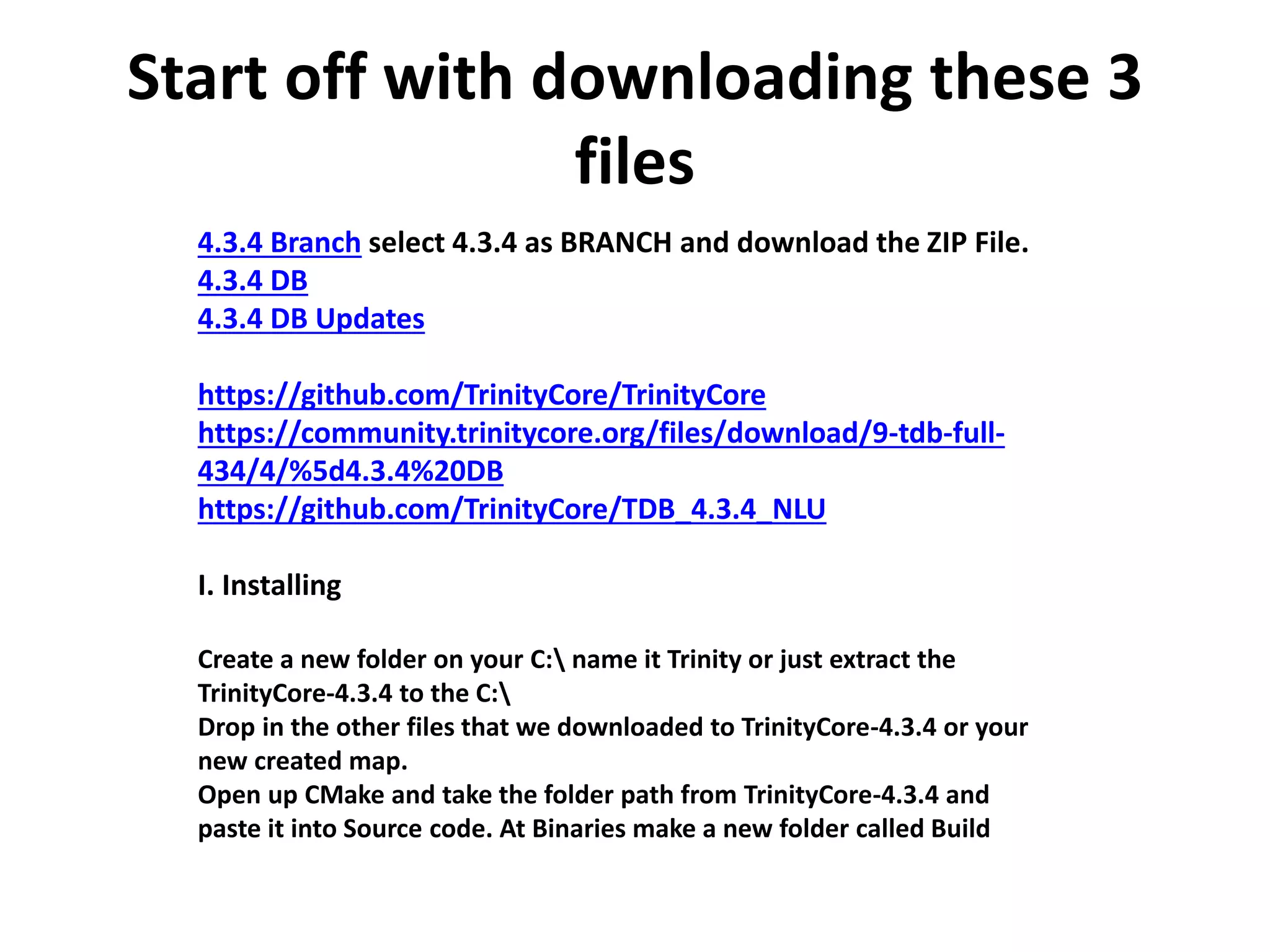
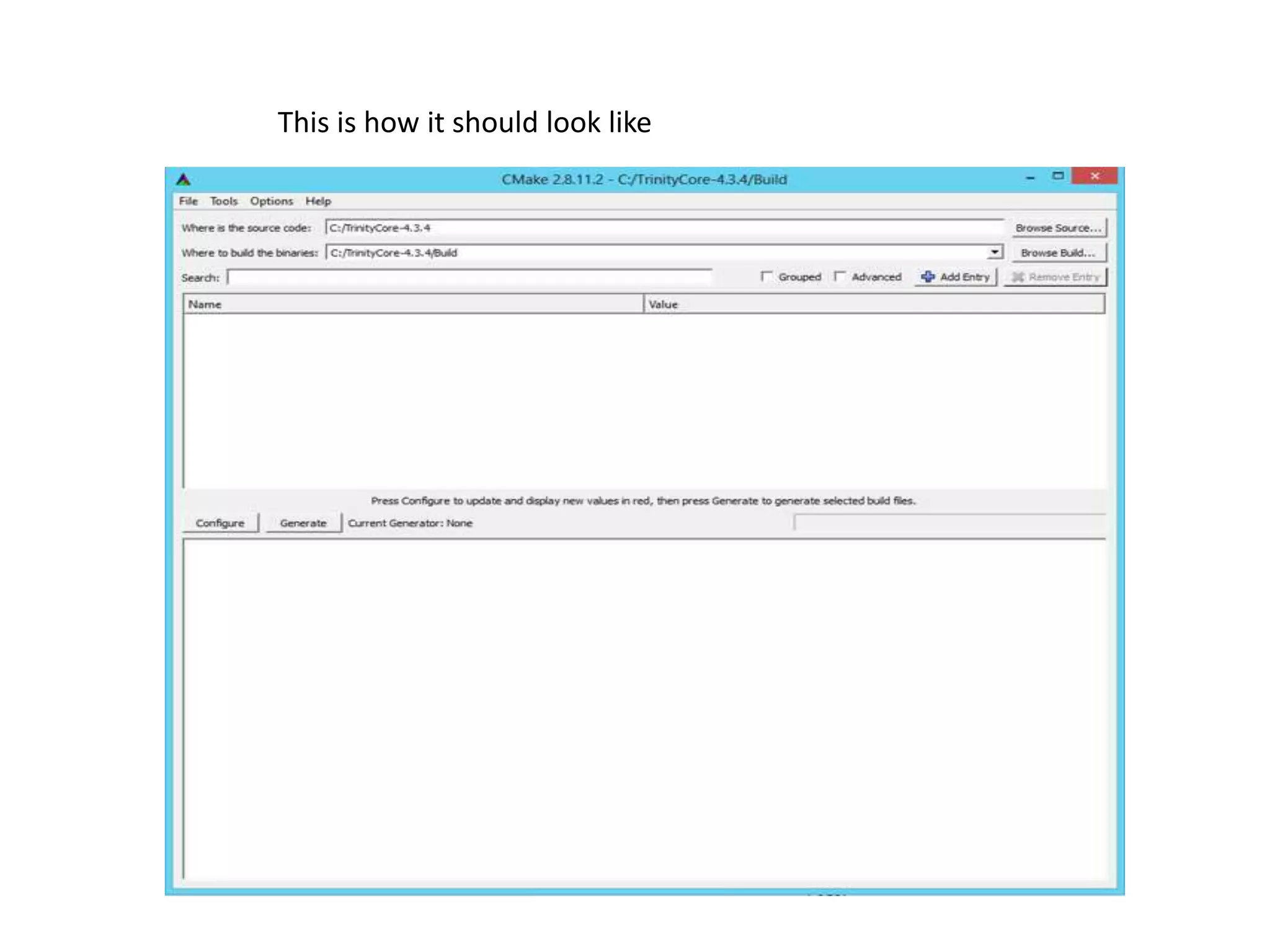
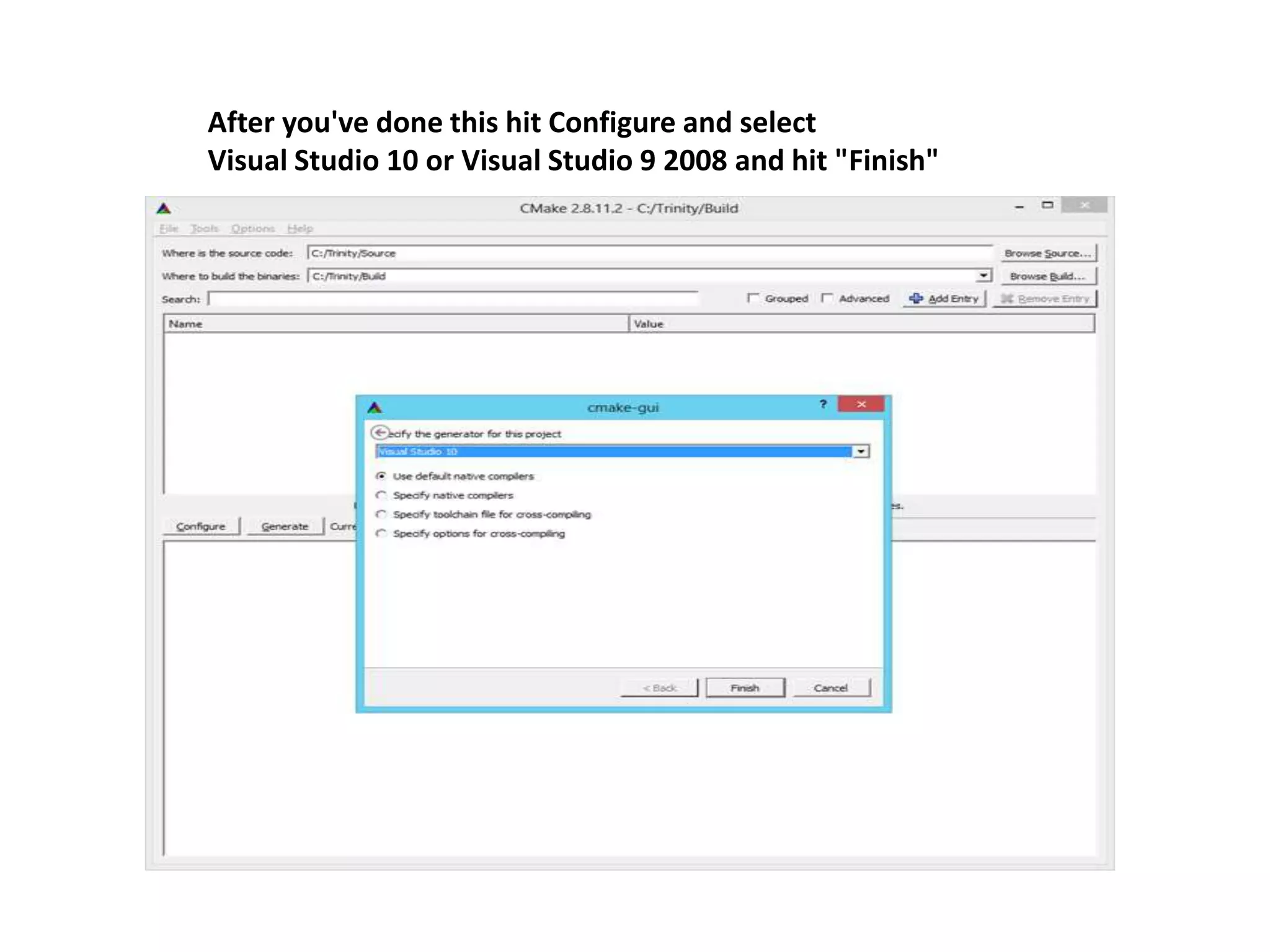
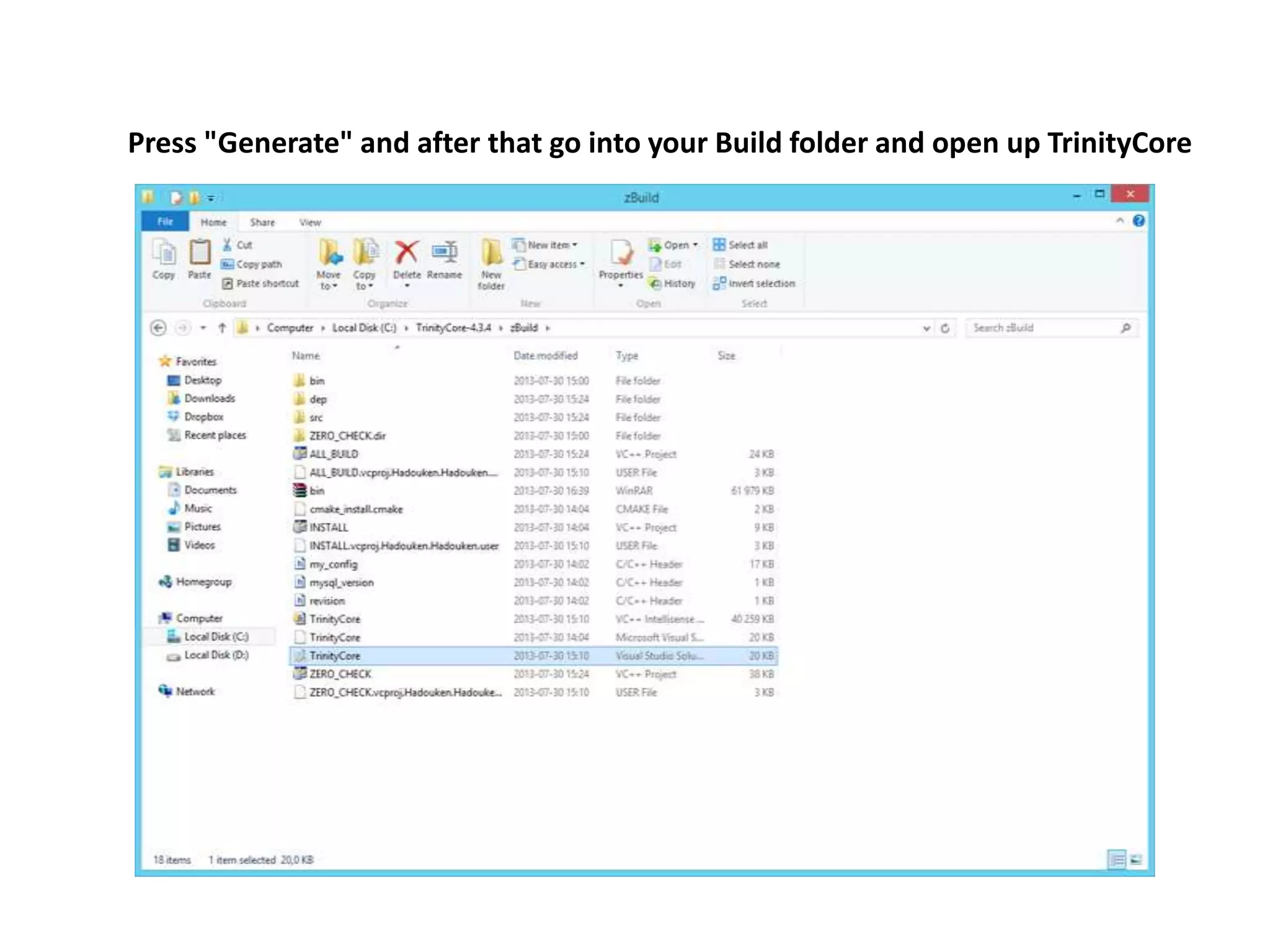
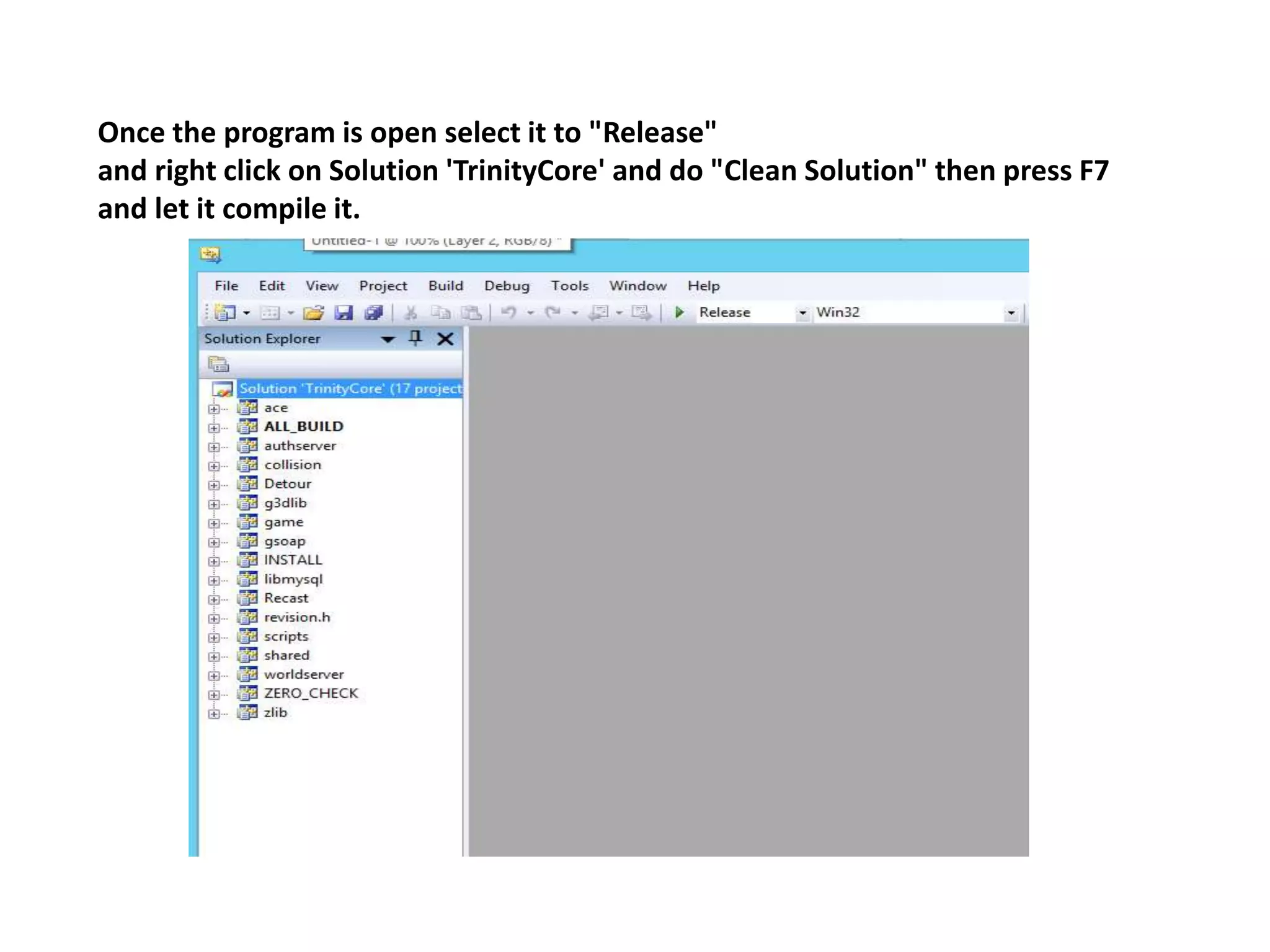
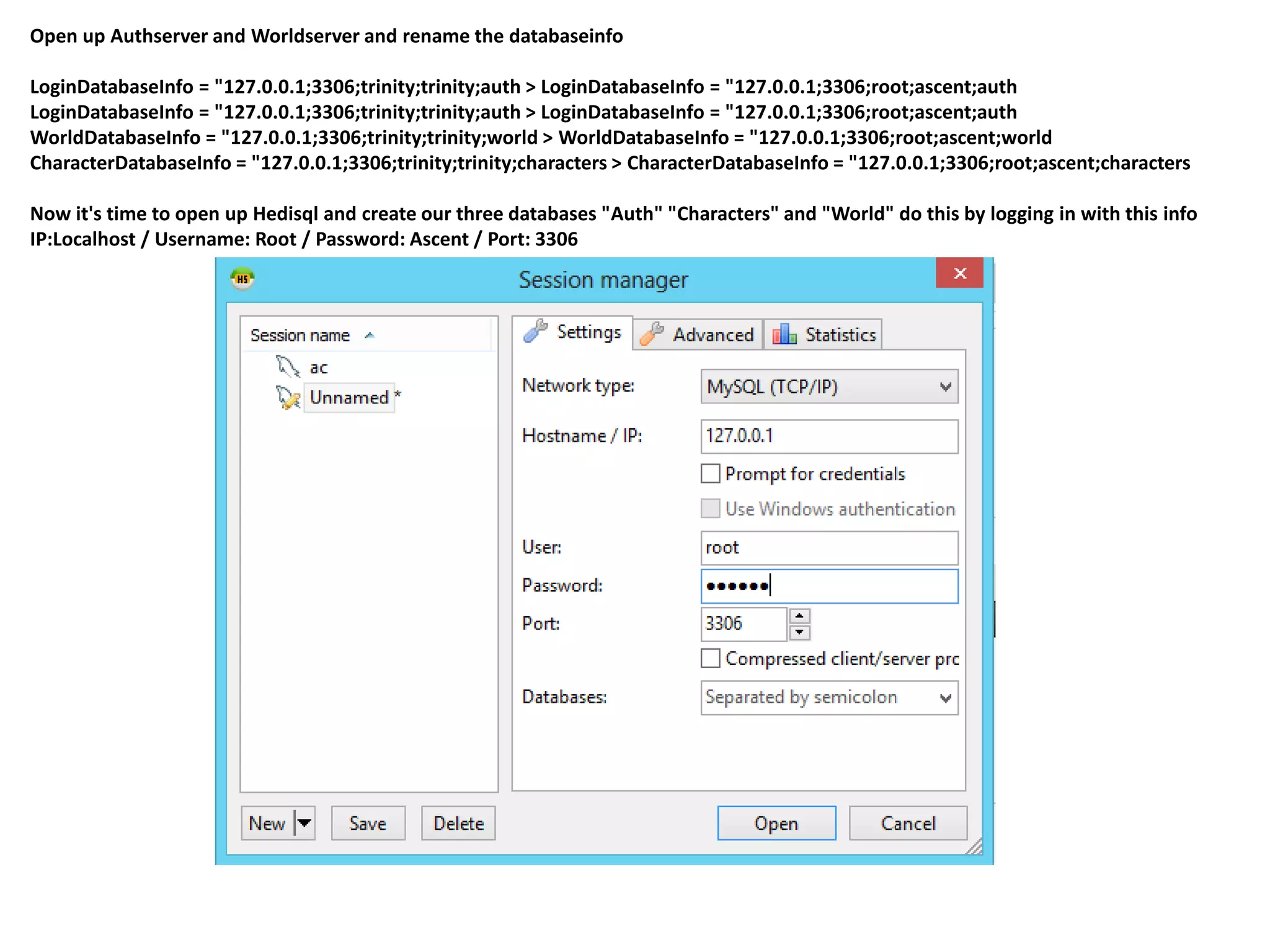
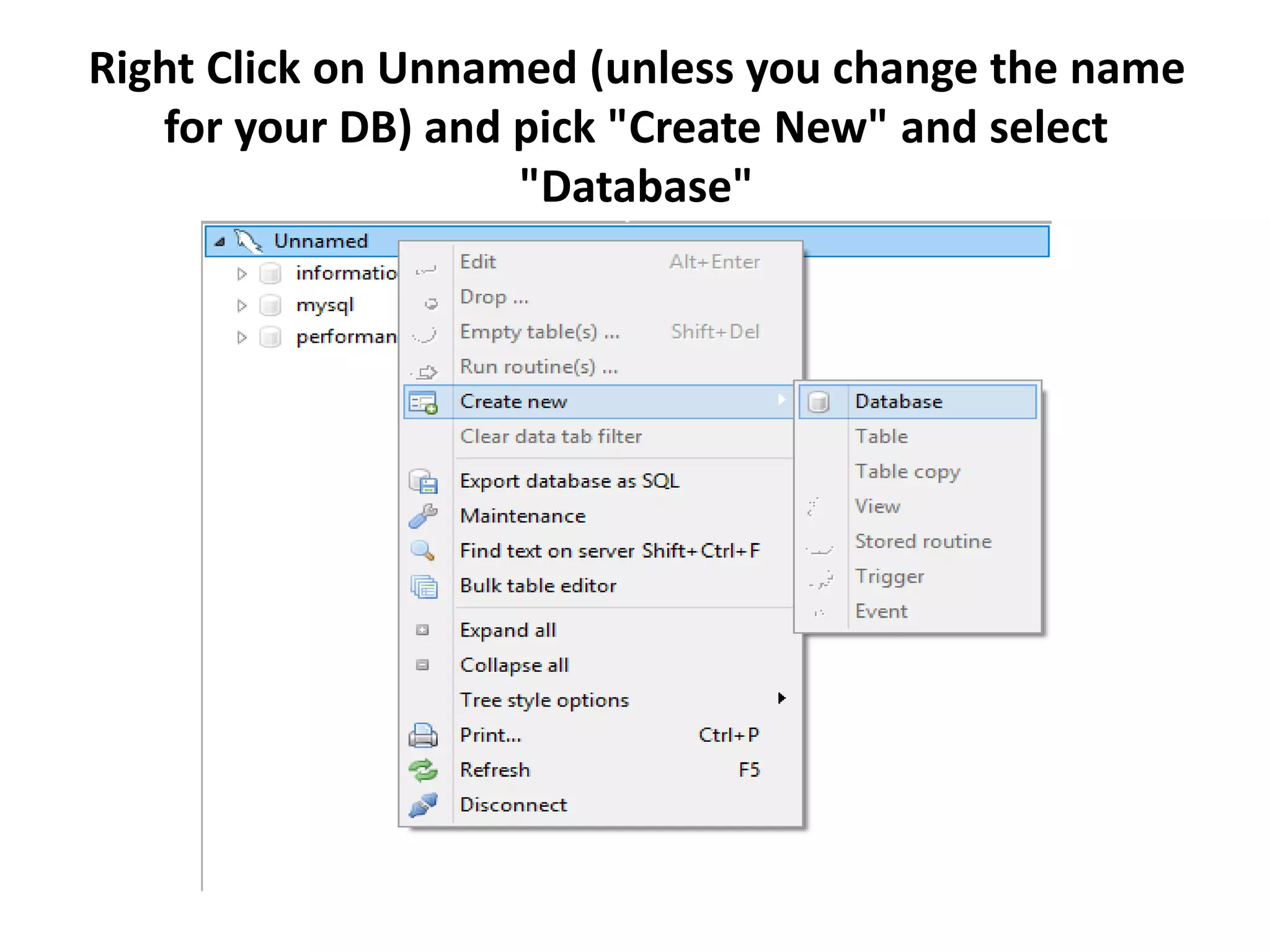
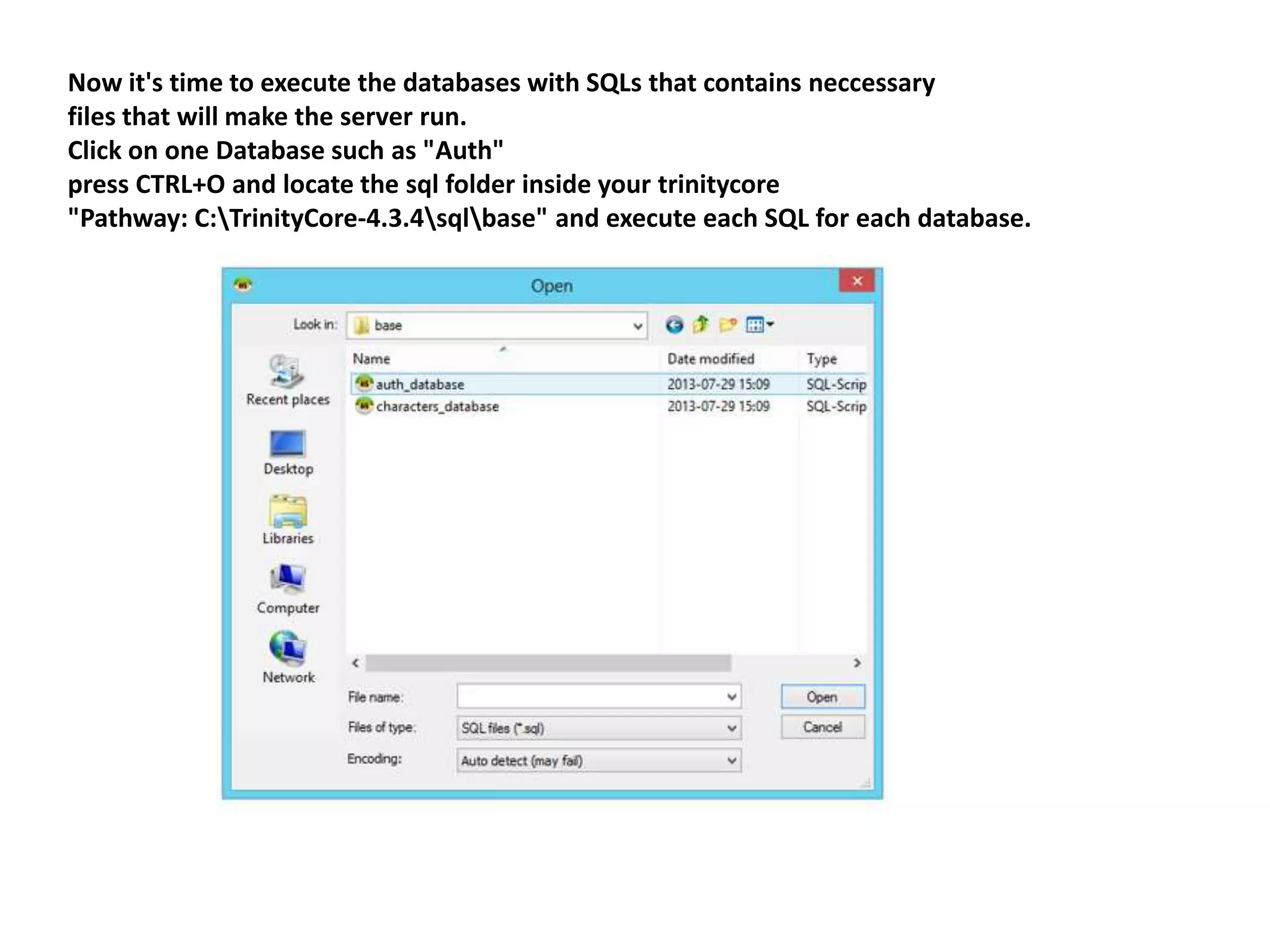
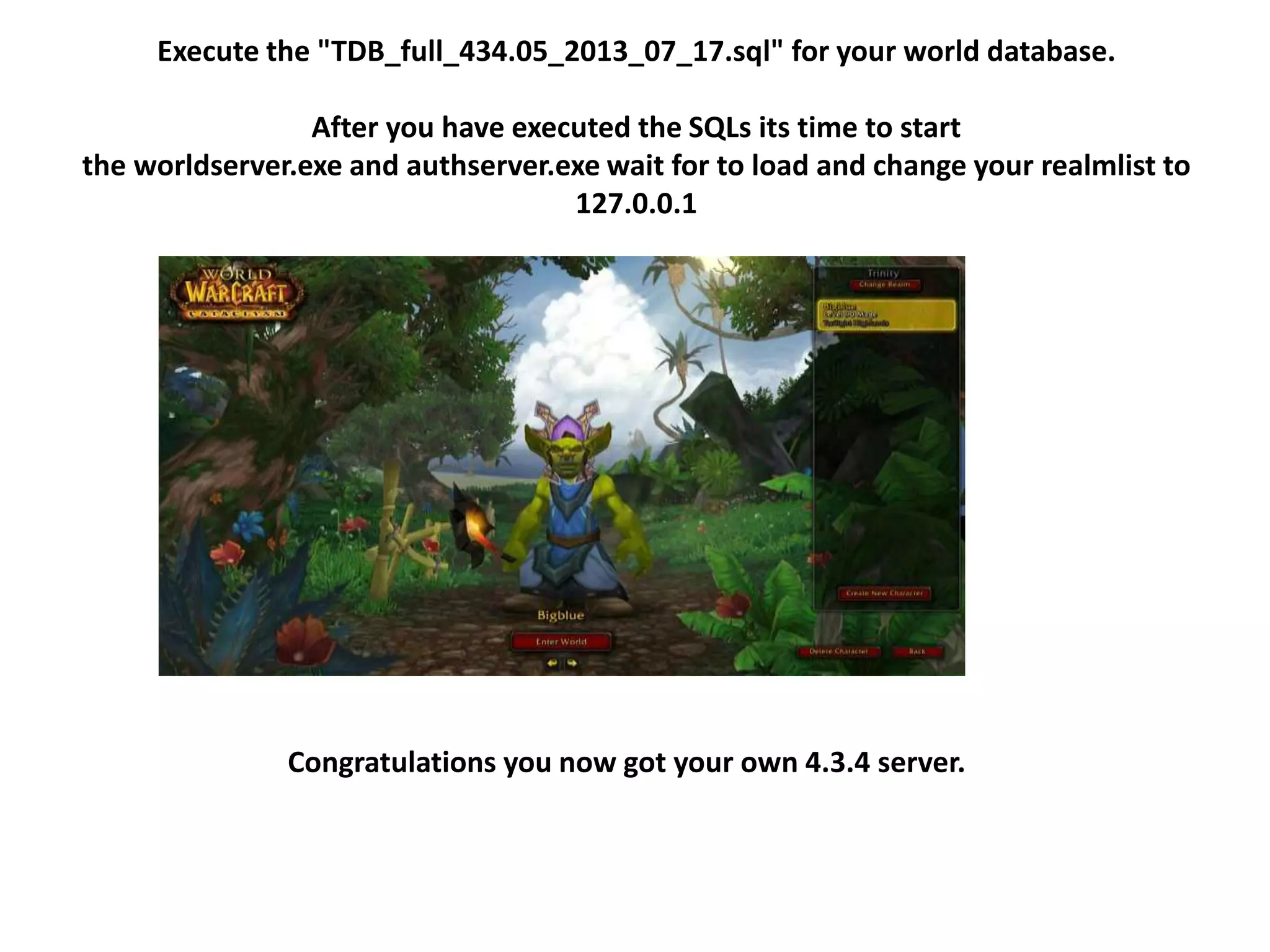
The document serves as a guide to compile a 4.3.4 Cataclysm server using TrinityCore. It details the required software, downloading necessary files, and installation steps including configuring databases and executing SQL files. Following the provided instructions allows users to set up their own 4.3.4 server successfully.