Embed presentation
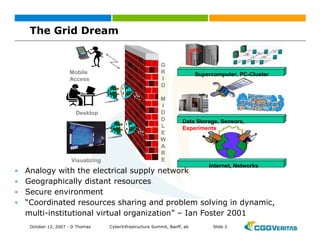
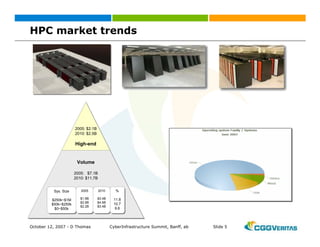
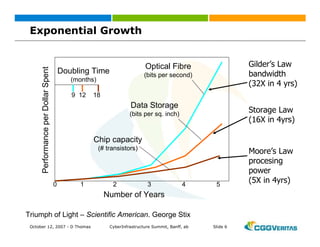
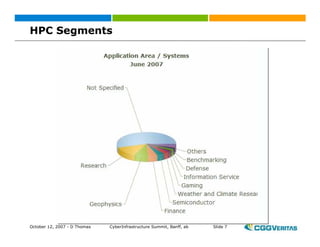
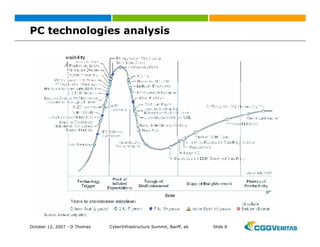
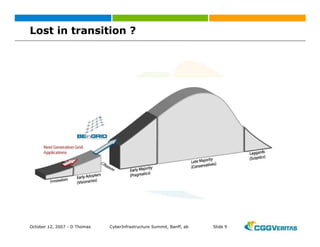
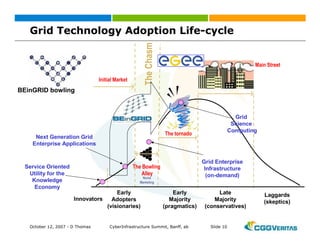
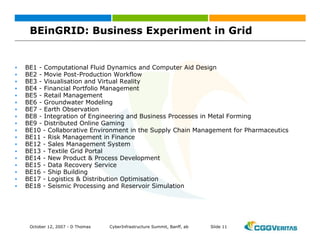
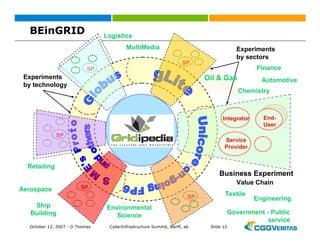

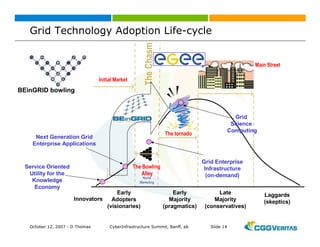

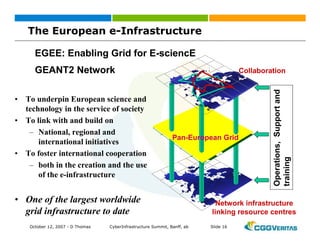
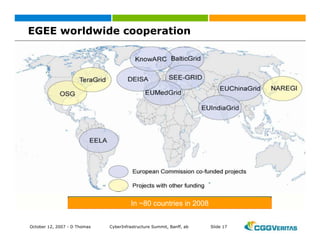
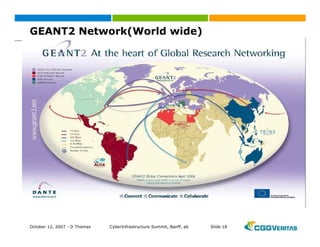
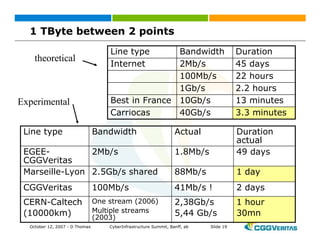
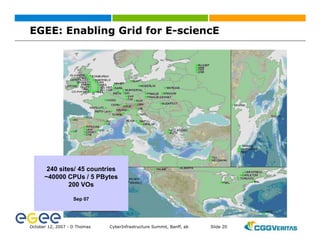
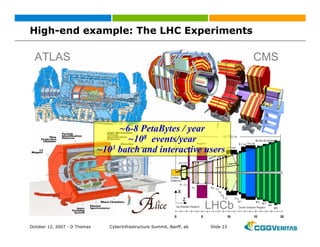
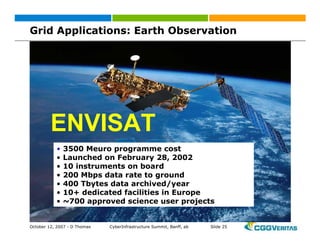
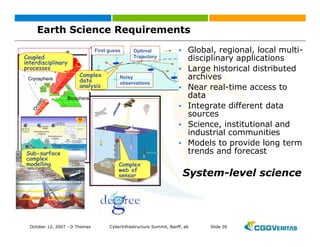
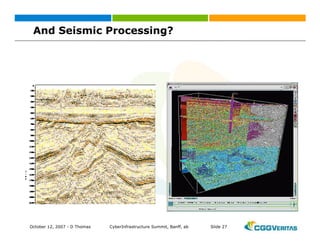


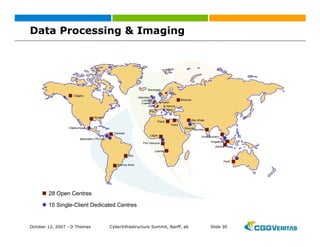
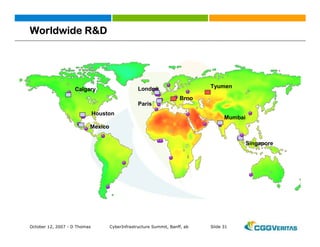
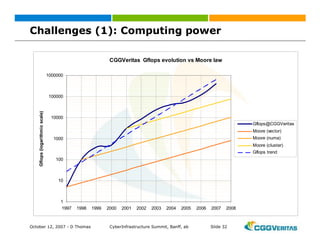
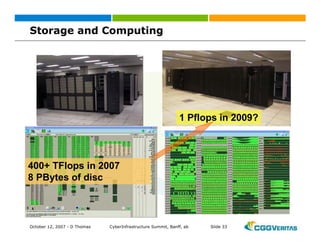

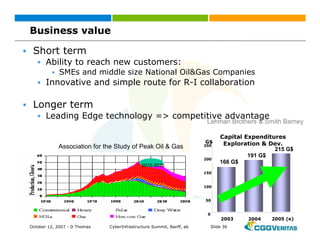

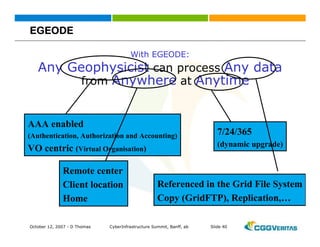
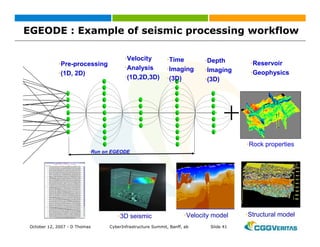

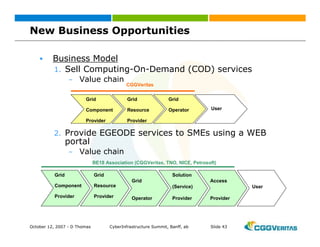
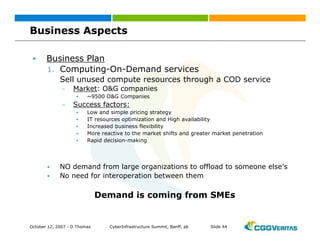

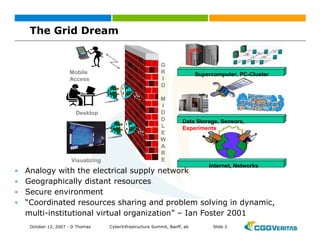
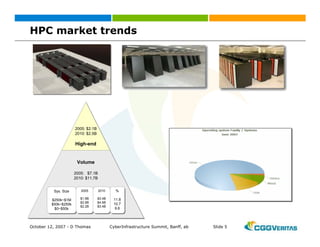
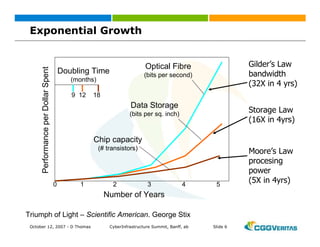
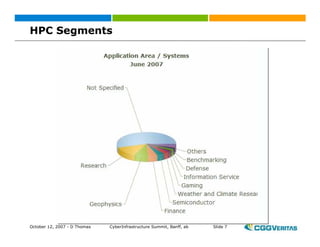
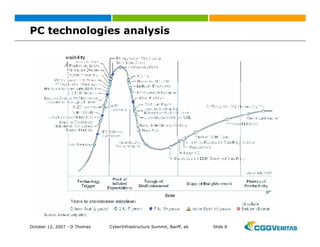
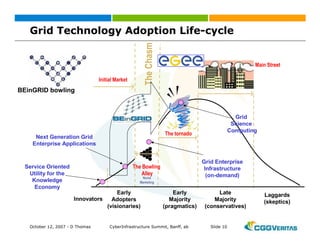
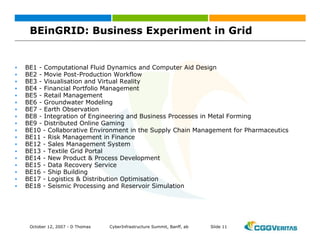
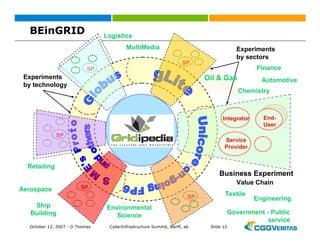
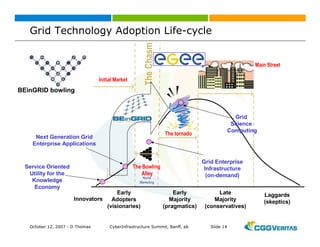
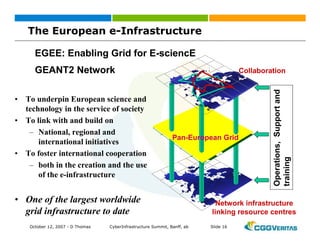
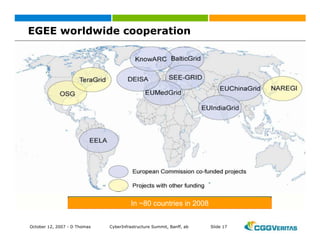
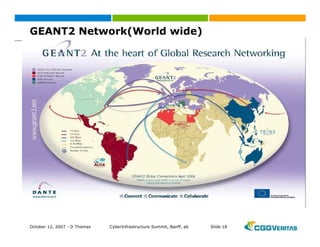
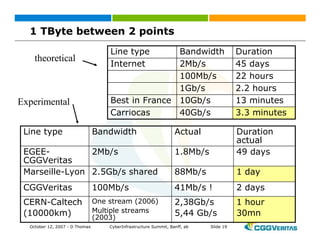
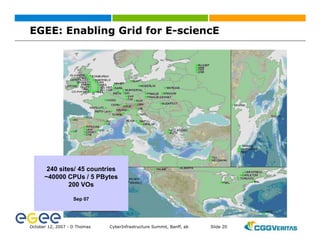
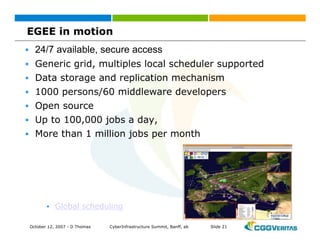
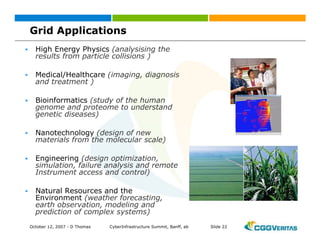
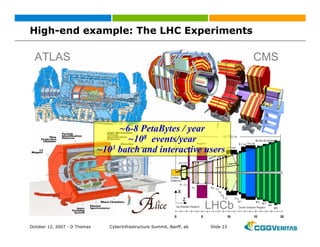
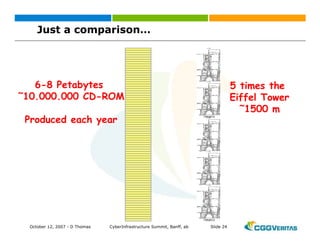
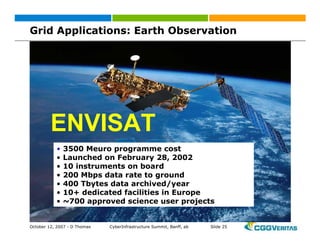
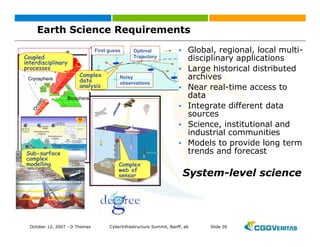
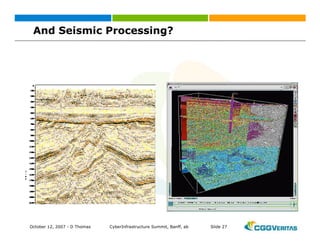
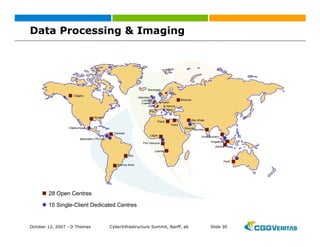
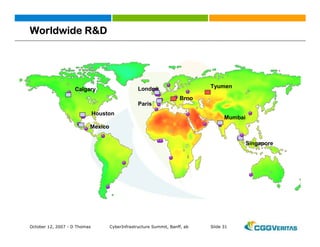
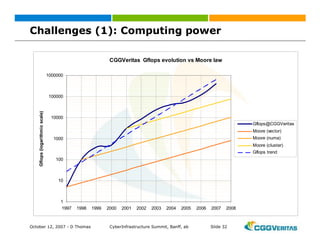
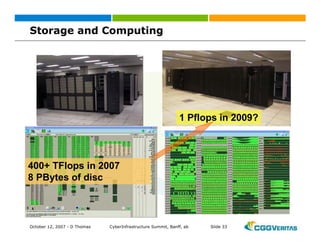
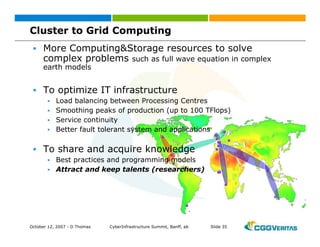
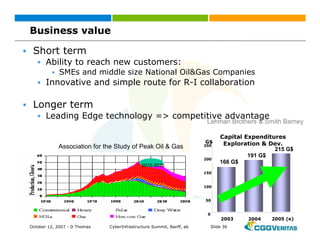
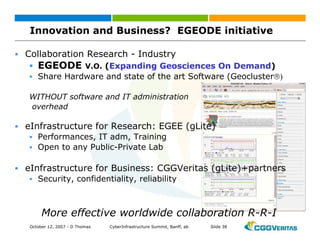
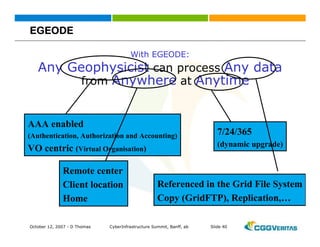
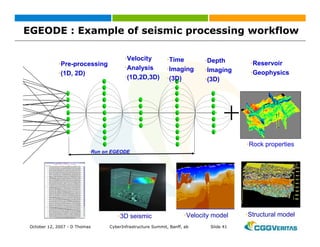
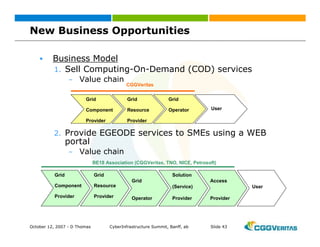
This document summarizes a presentation given by Dominique Thomas on opportunities for new business models using grid computing. Some key points discussed include: - Trends in high performance computing showing increasing demand for more computing power and data storage. - European projects like BEinGRID and EGEE that are developing grid infrastructure for e-science applications. - Challenges faced by CGGVeritas in seismic processing like needing more computing power and better management of large datasets and computing resources. - Potential benefits of adopting grid computing for CGGVeritas including better optimization of IT resources, ability to solve more complex problems, knowledge sharing, and new business opportunities.