Embed presentation
Download as PDF, PPTX
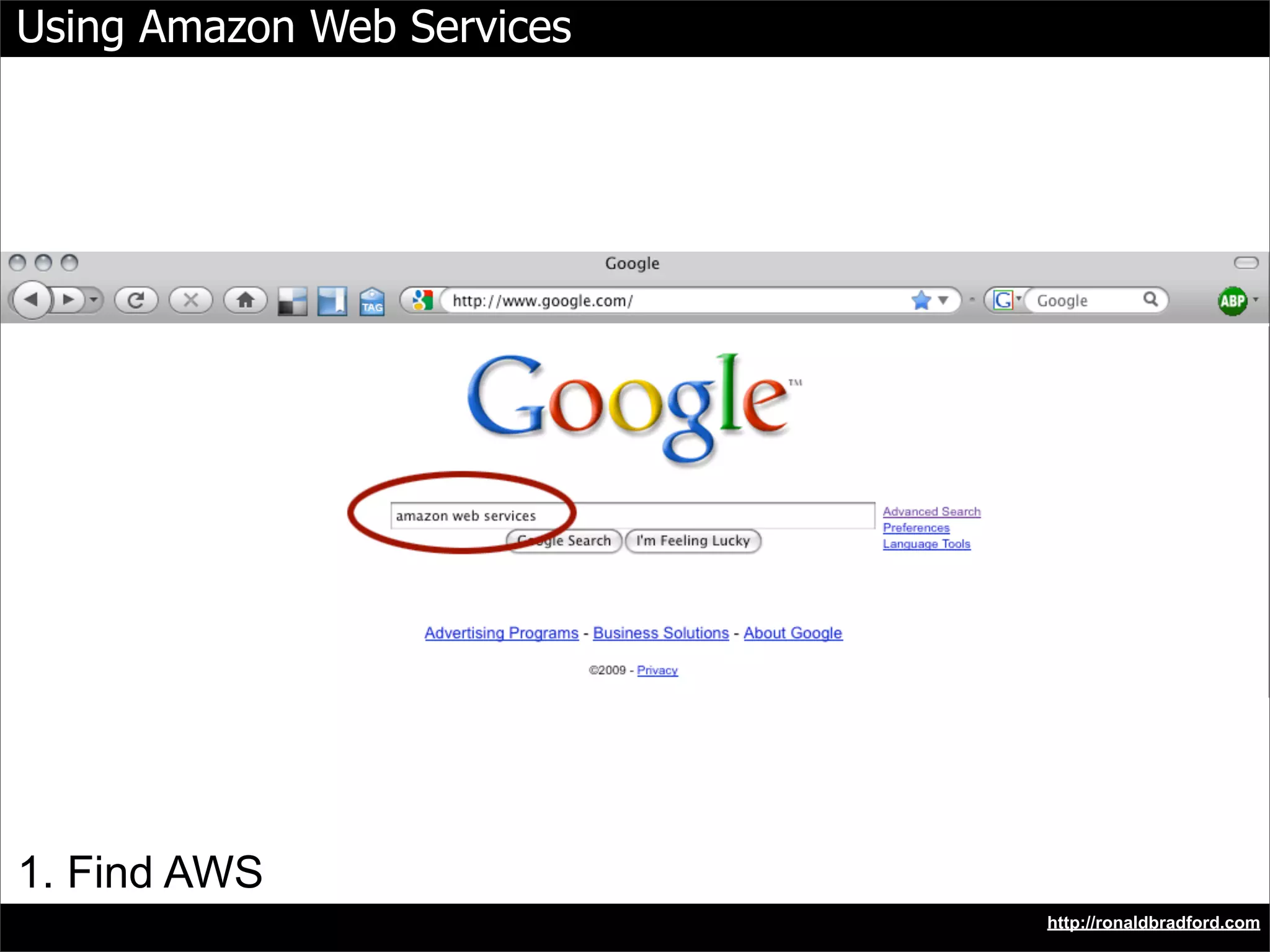
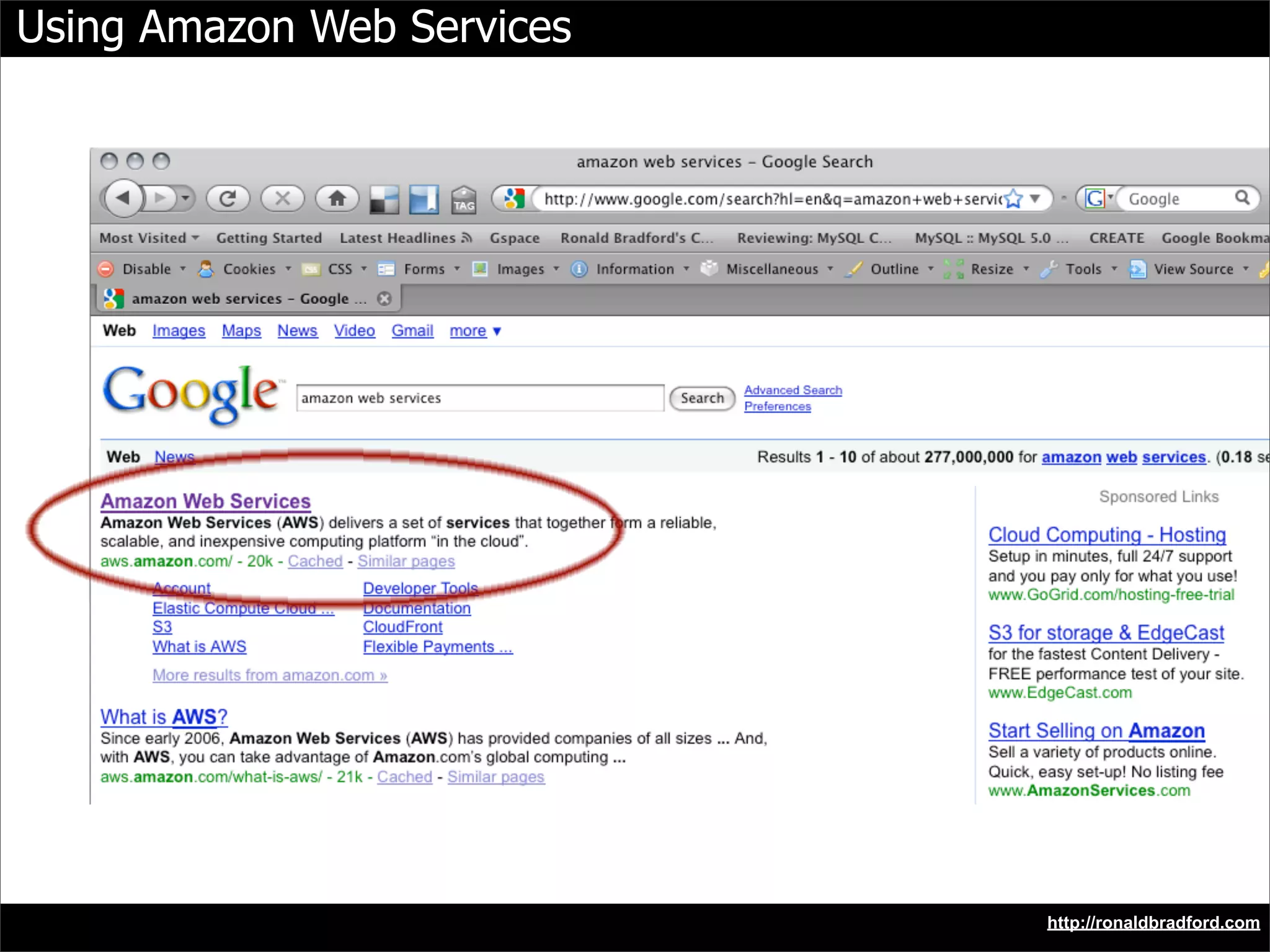
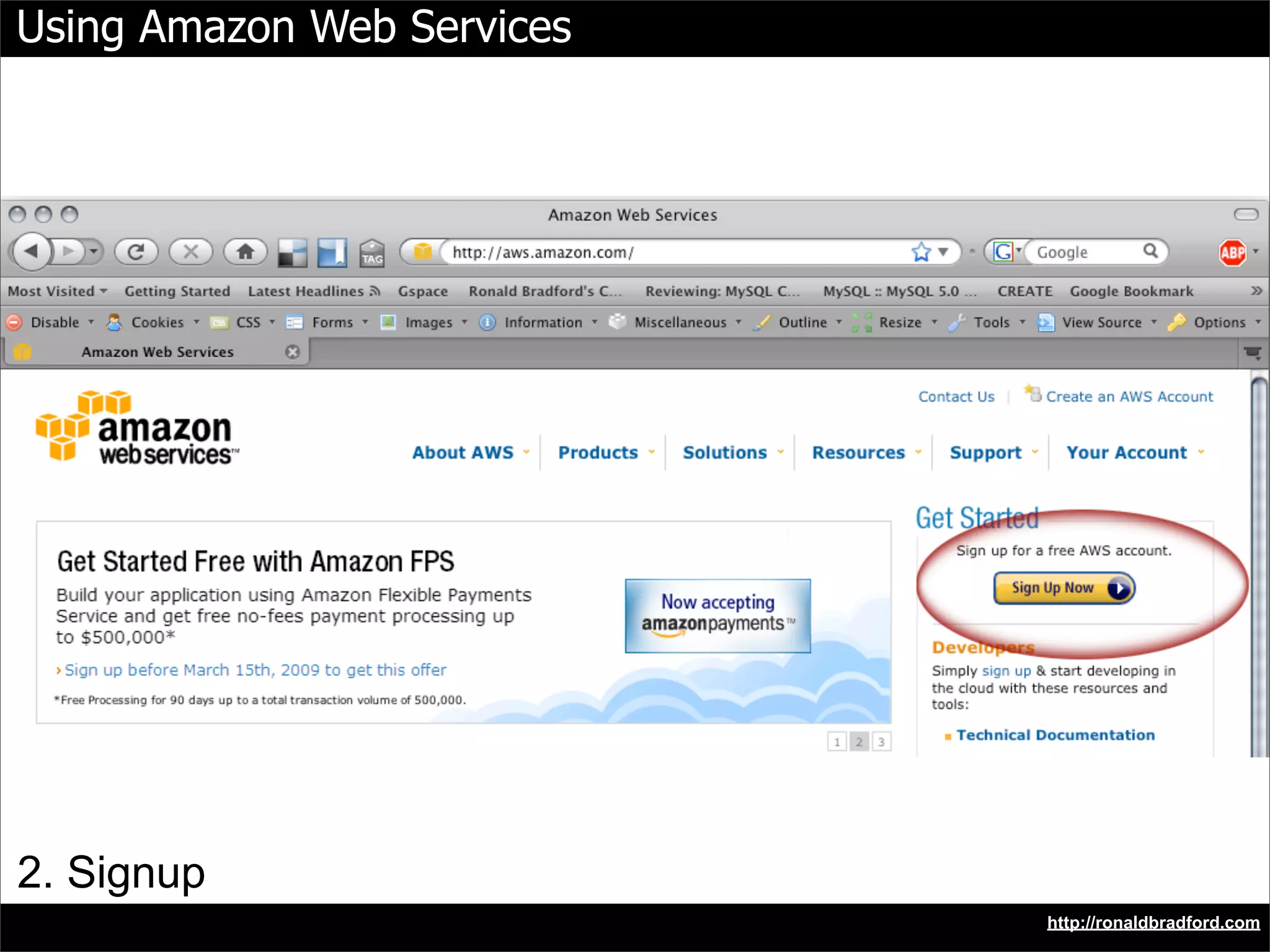
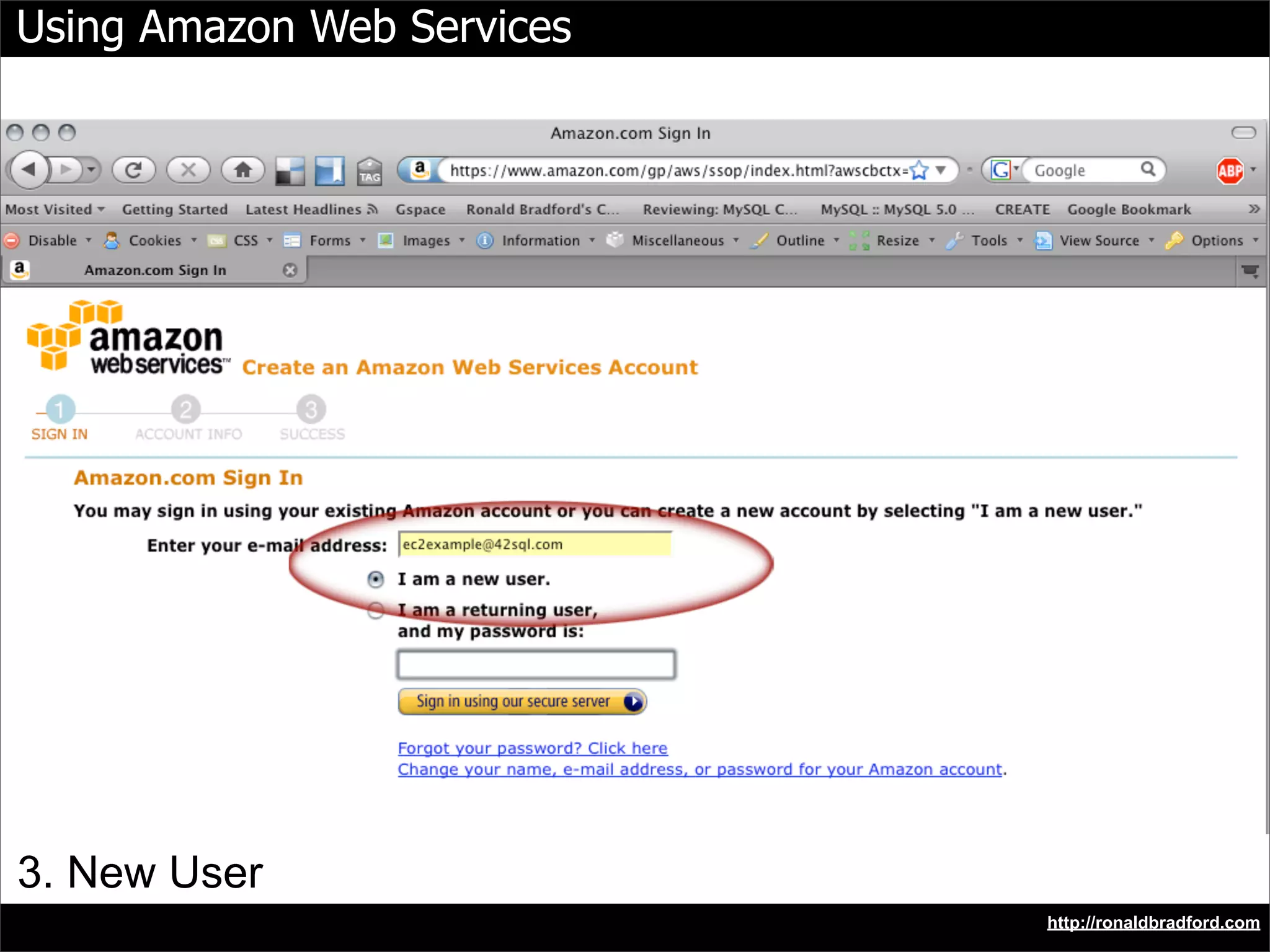
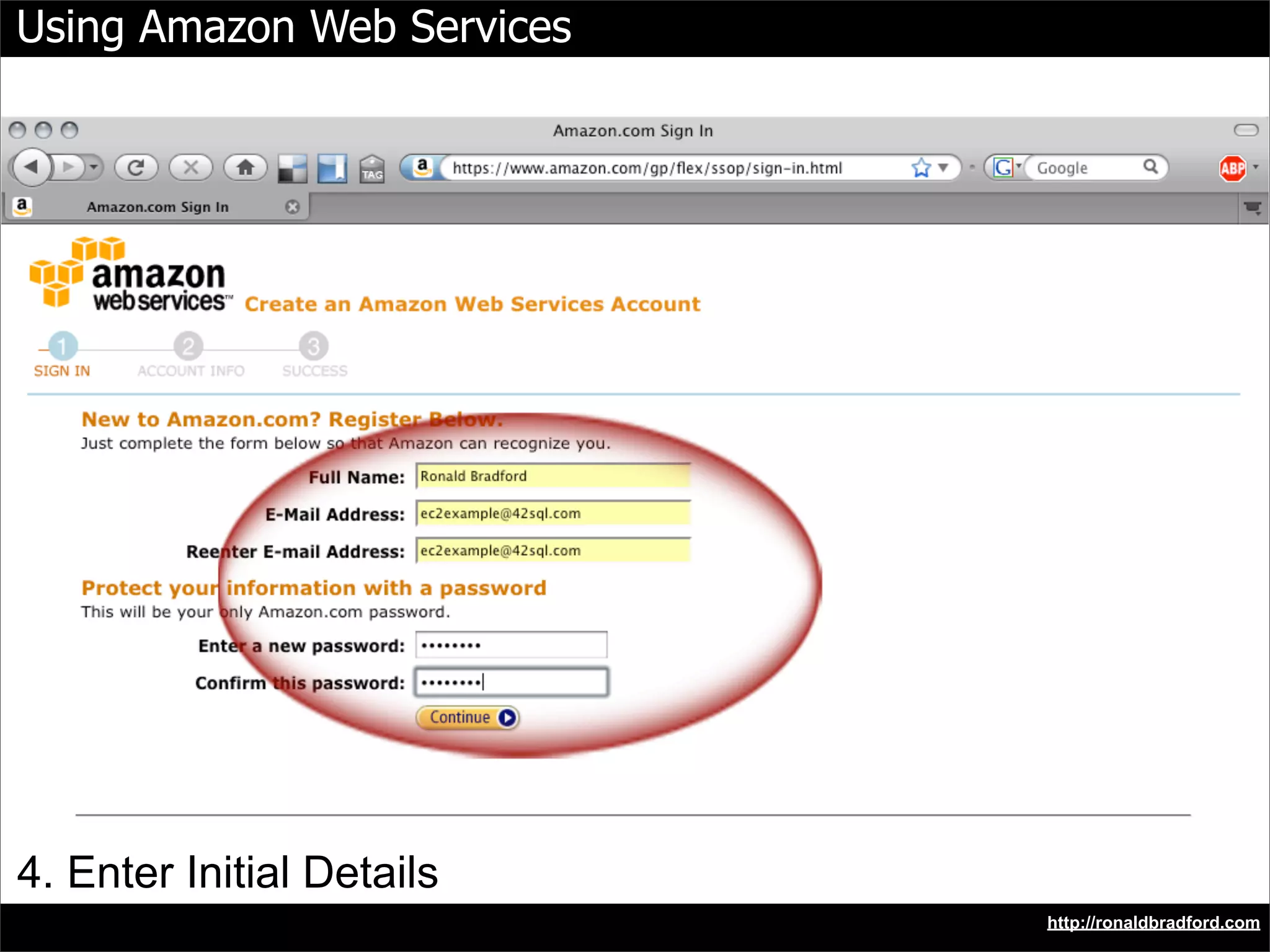
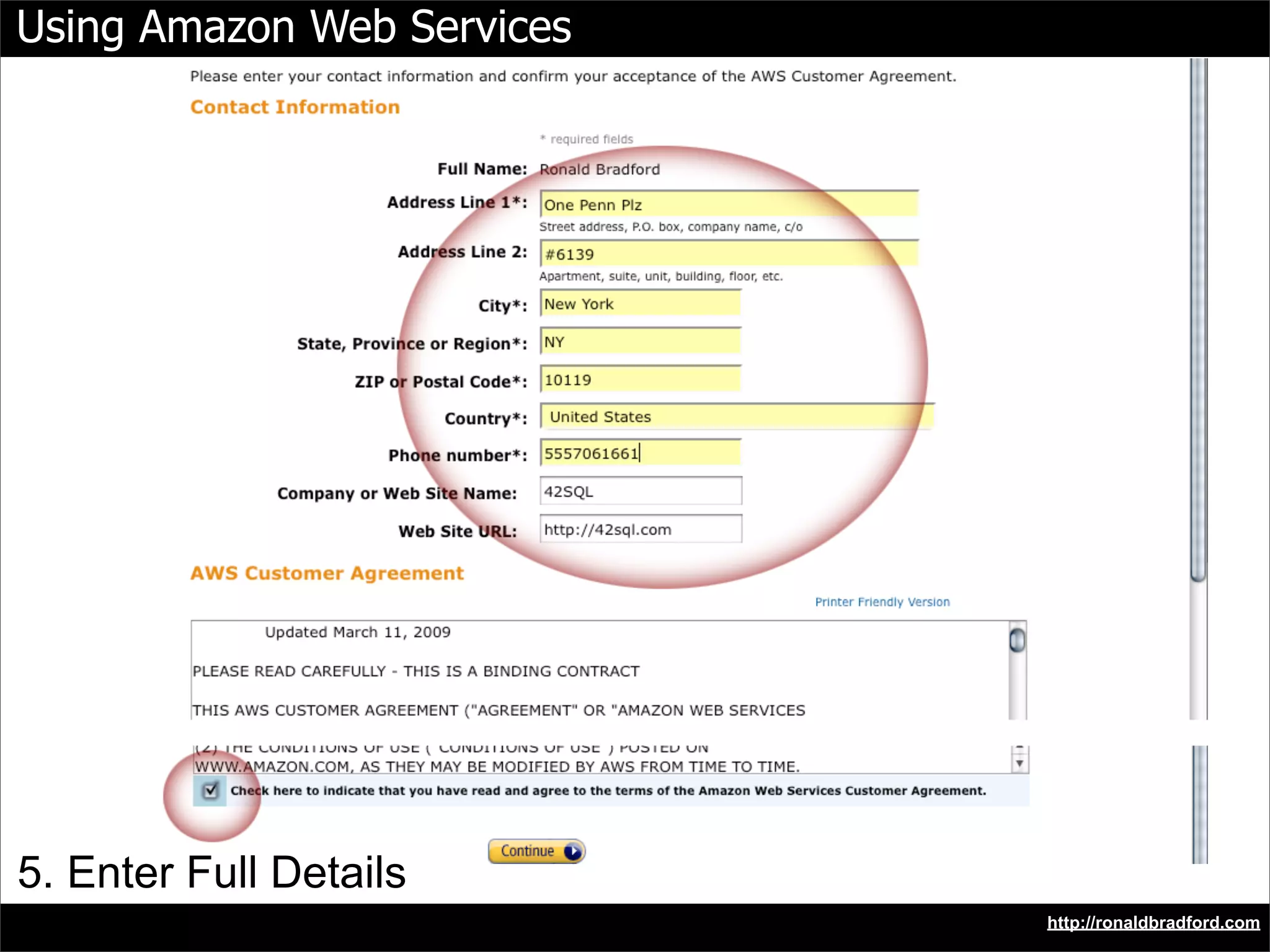
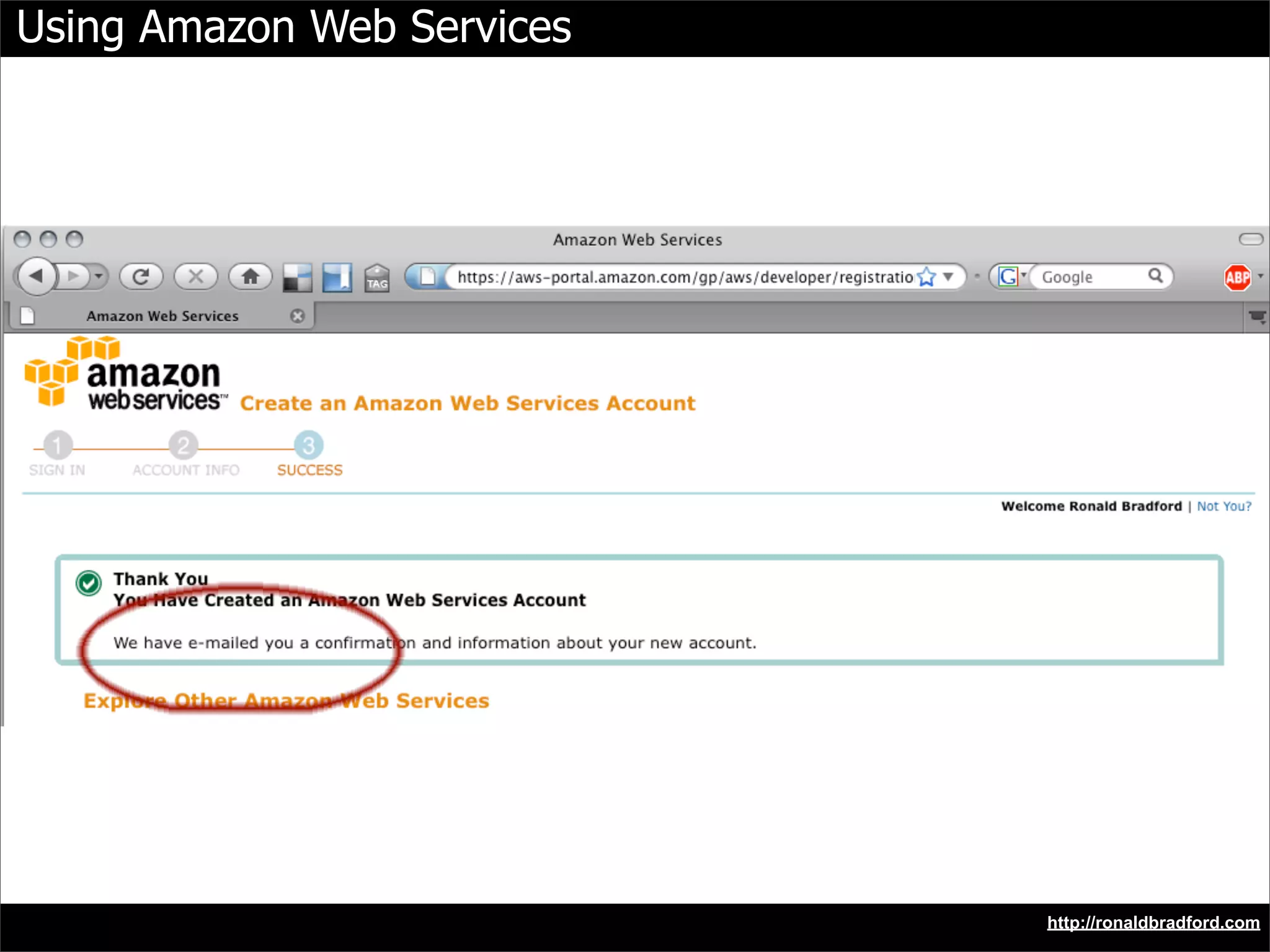
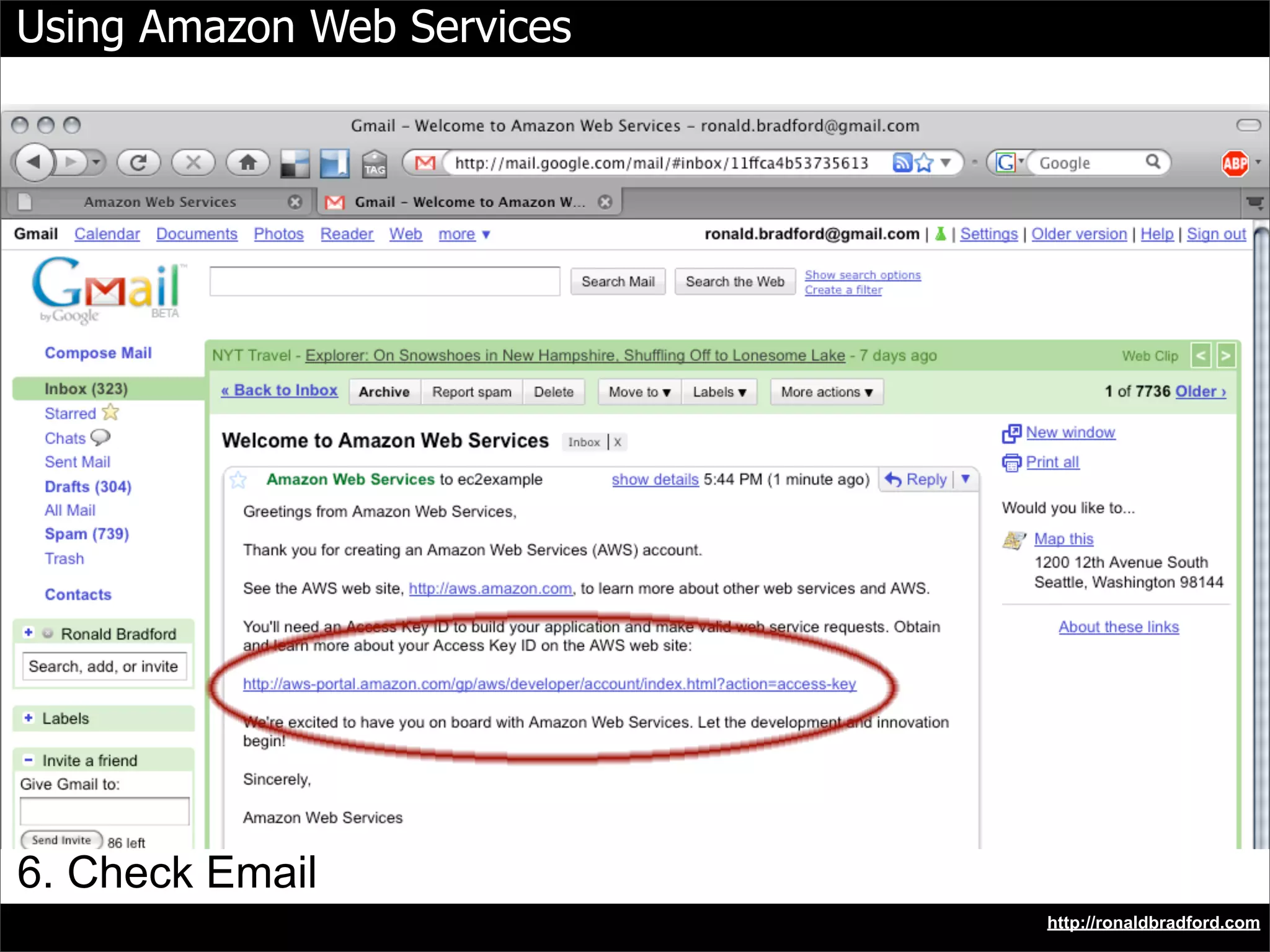
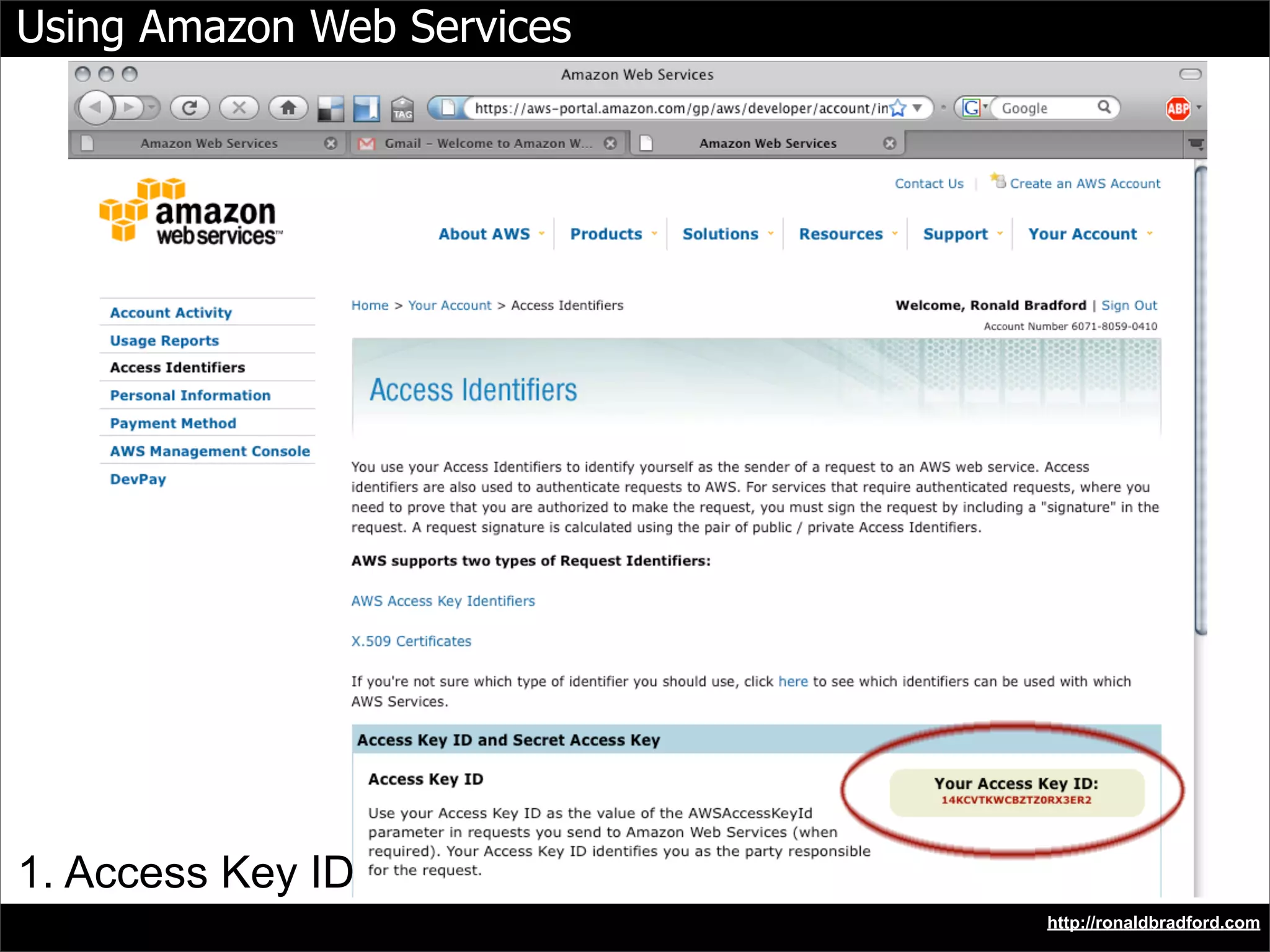
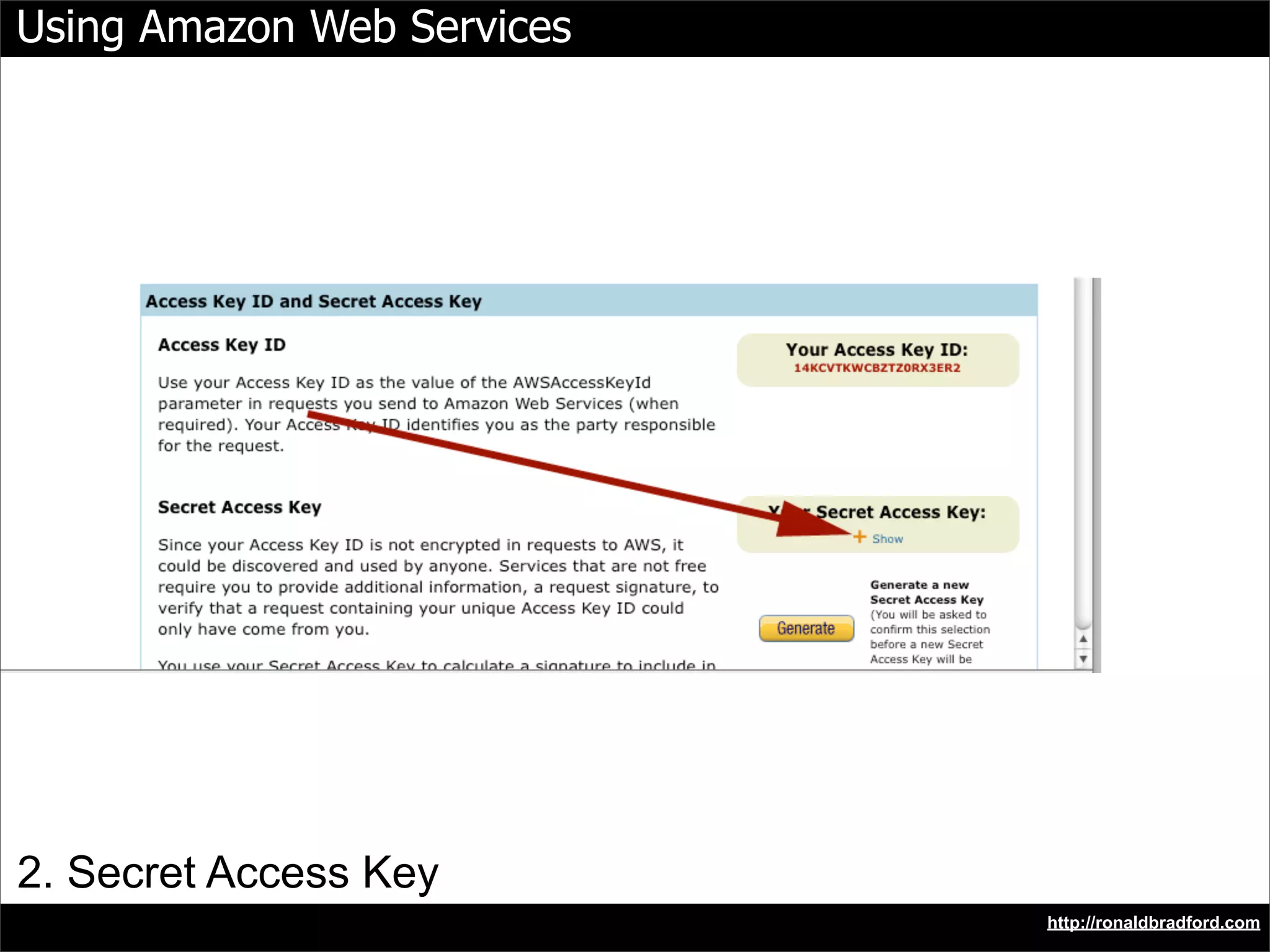
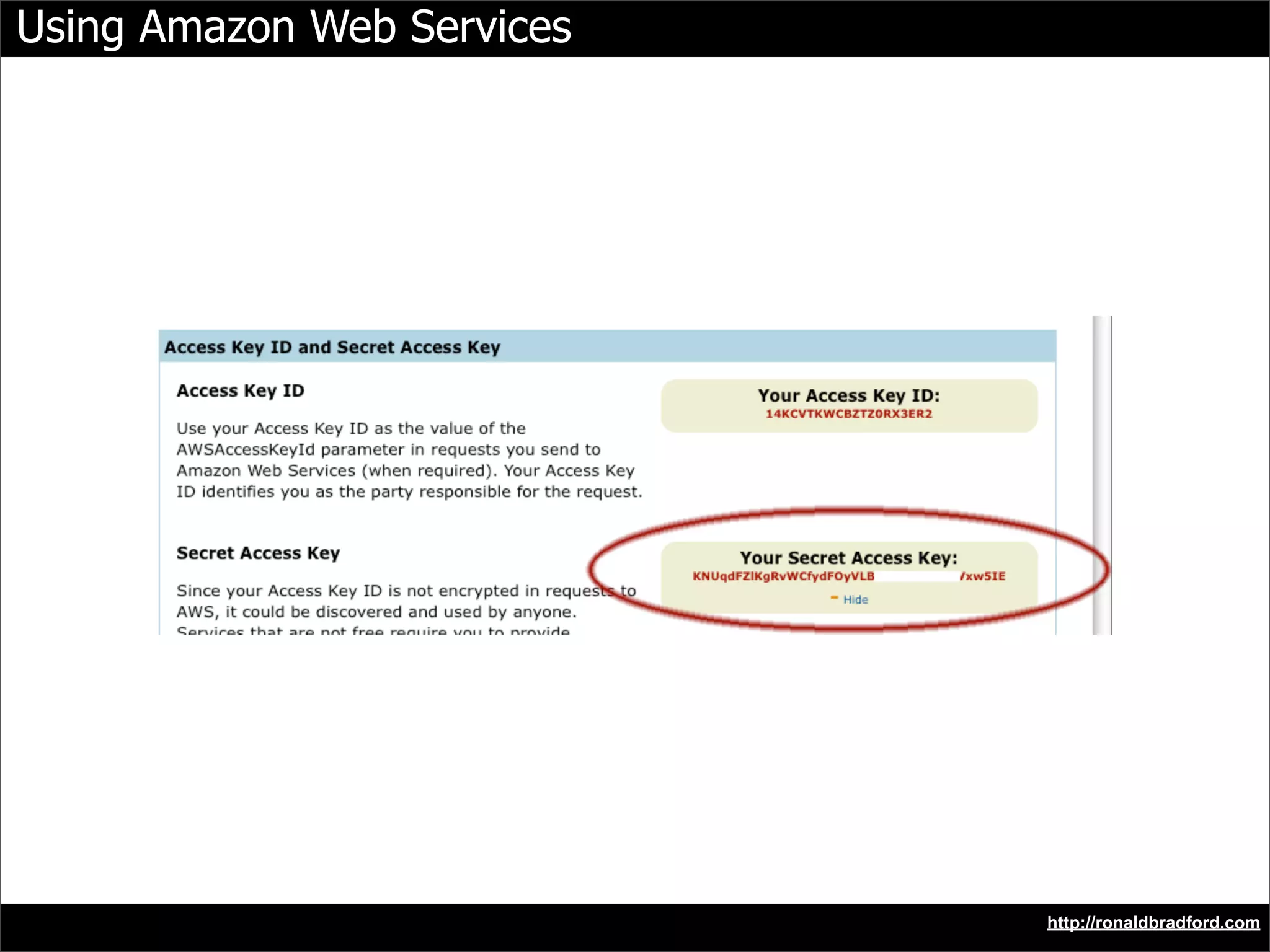
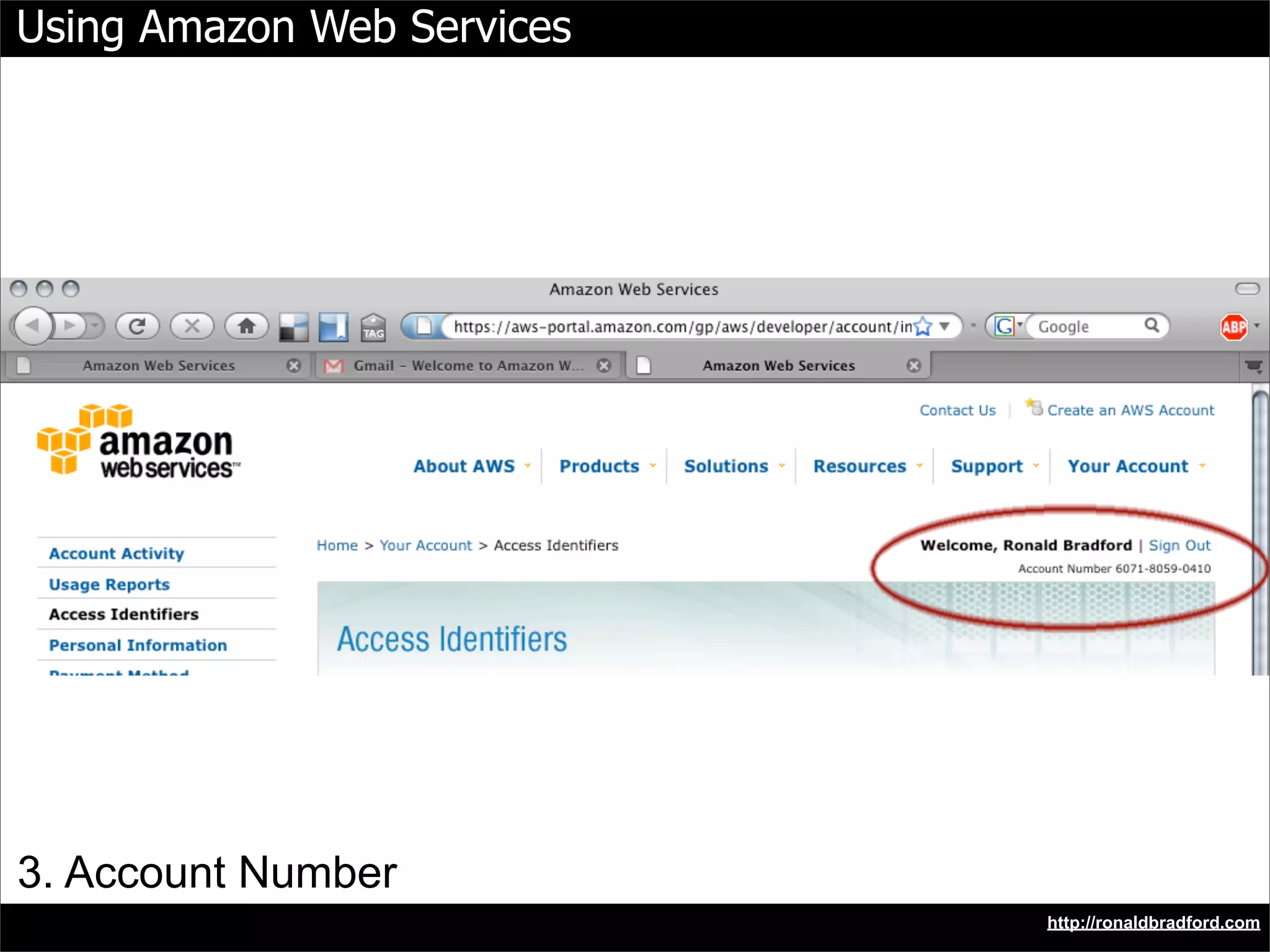
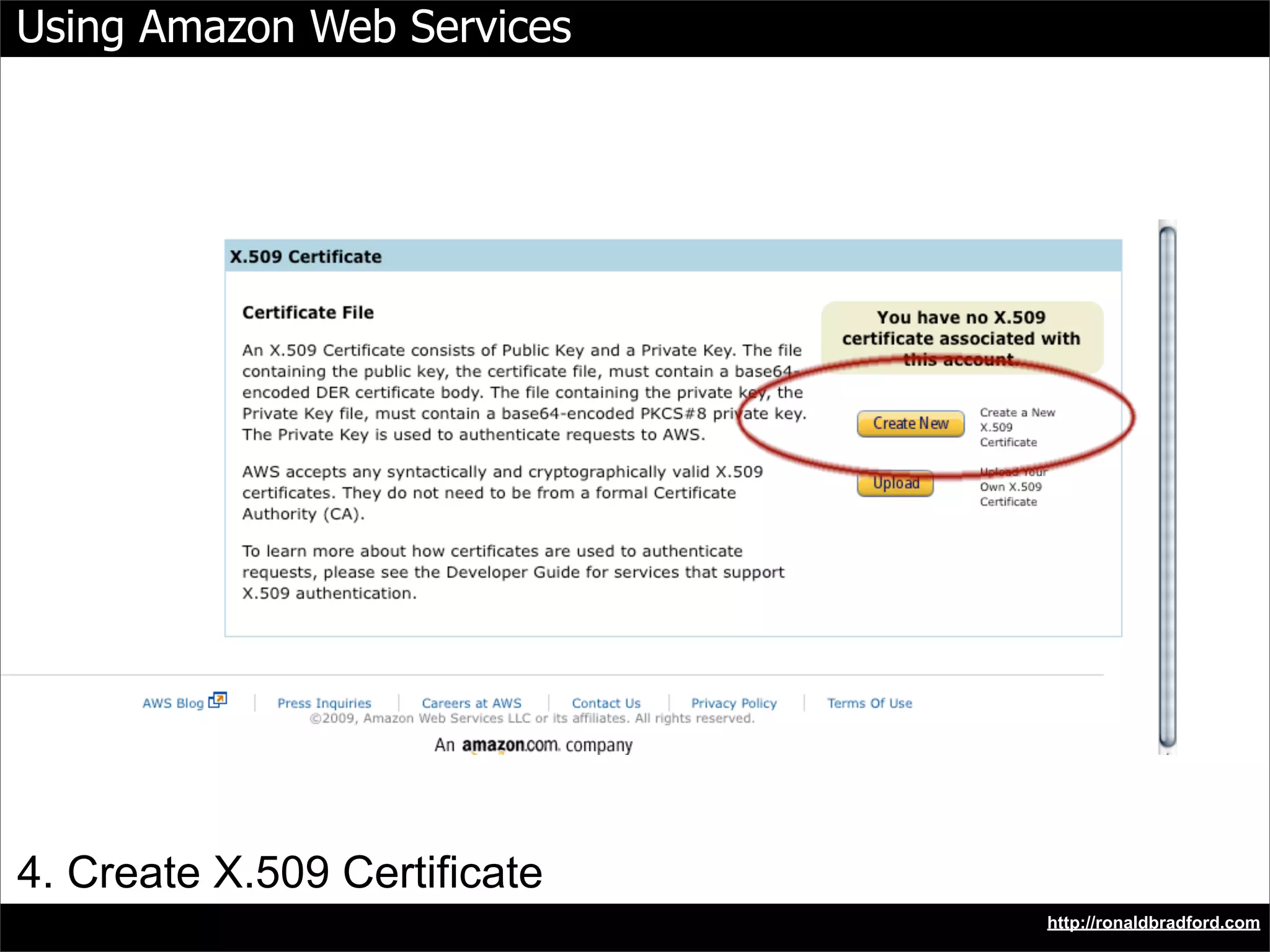
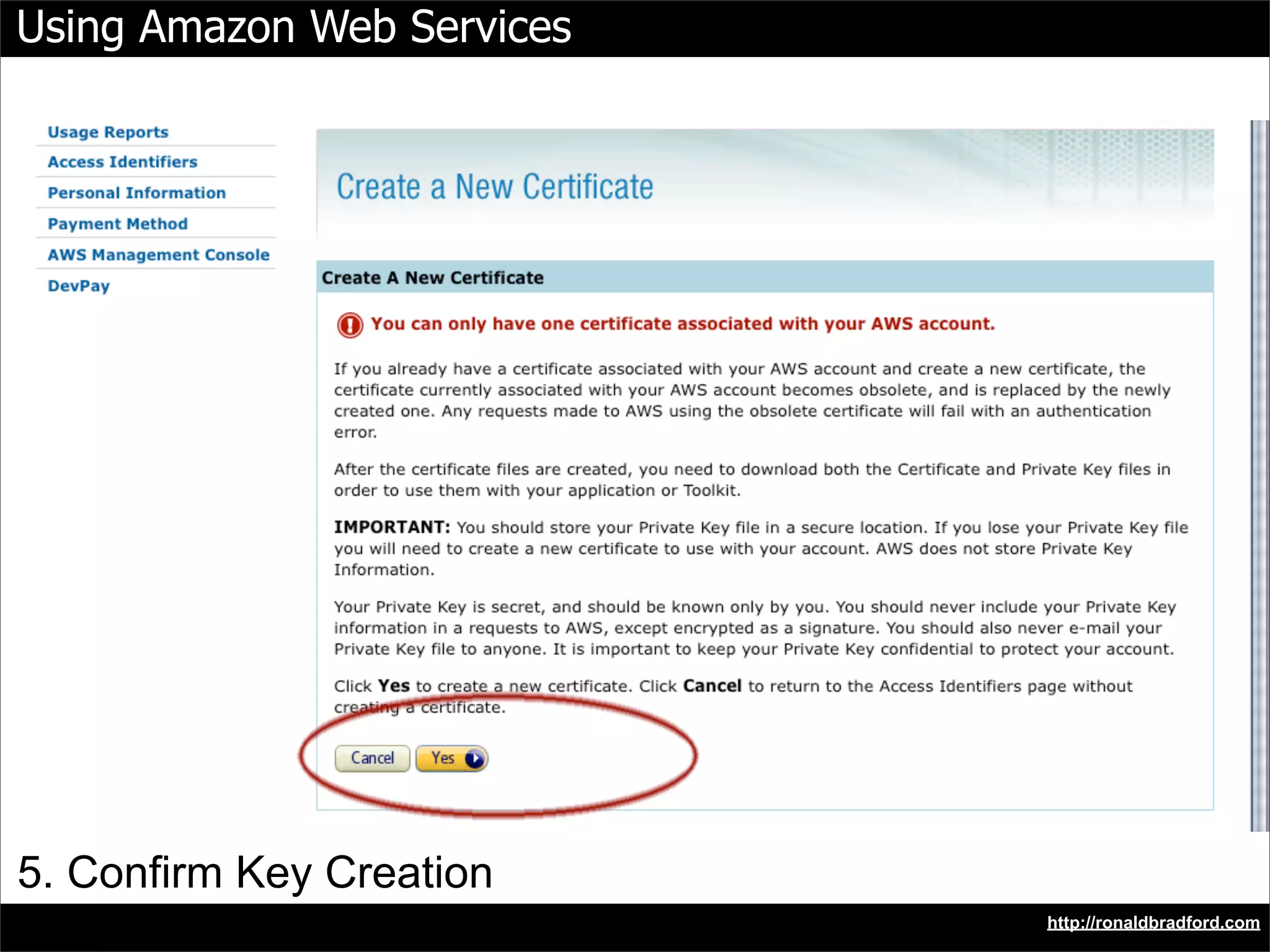
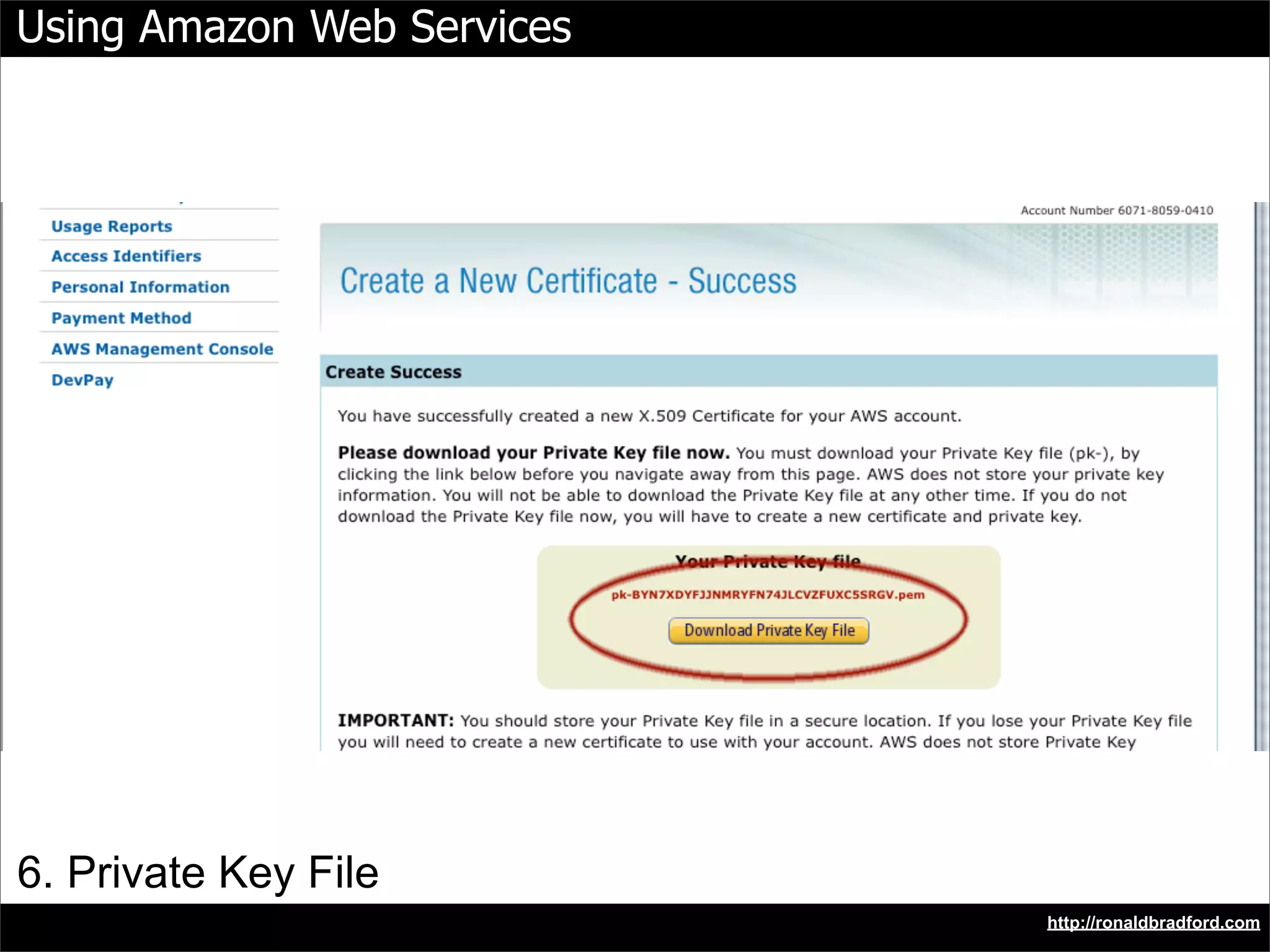
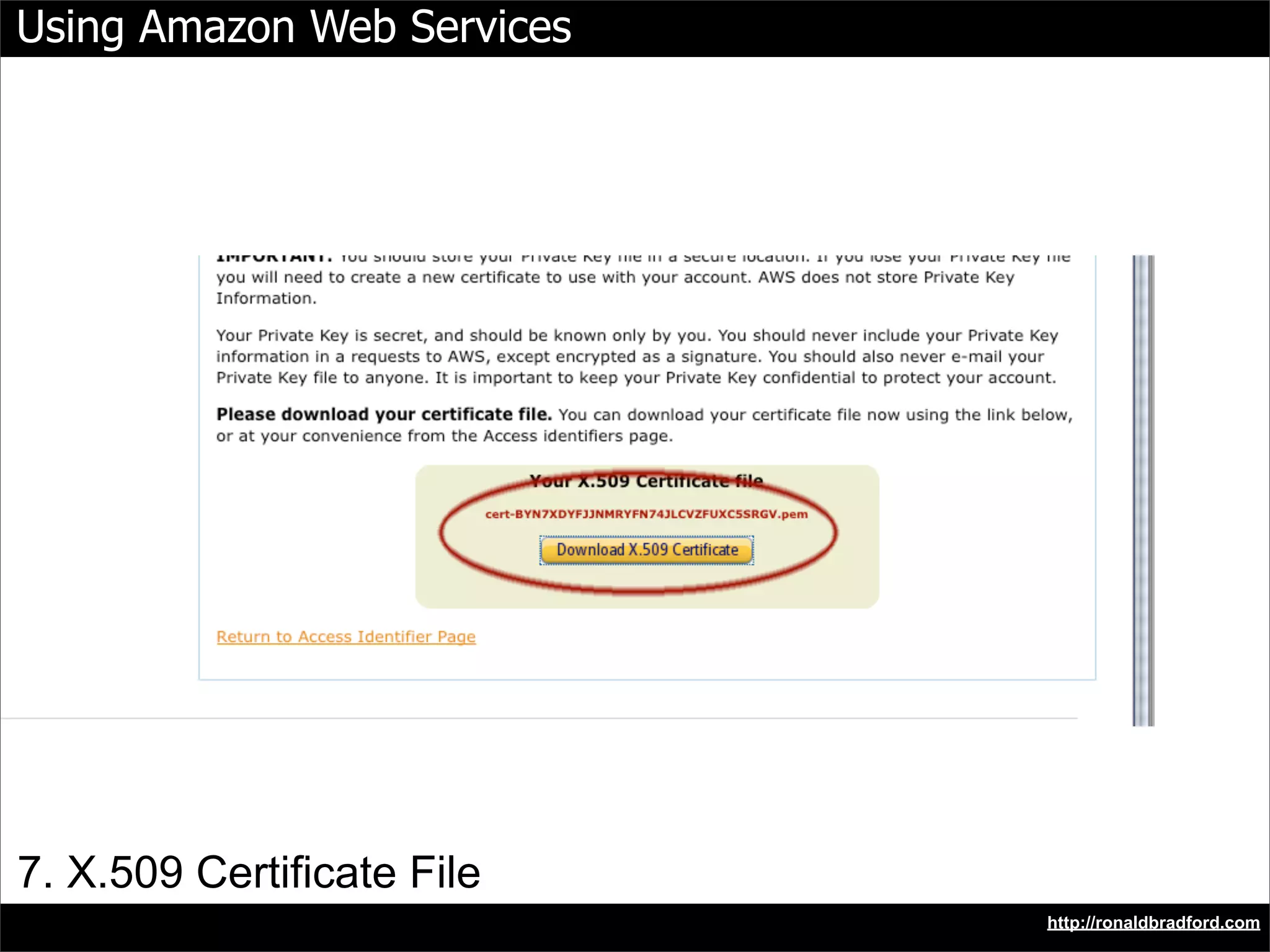
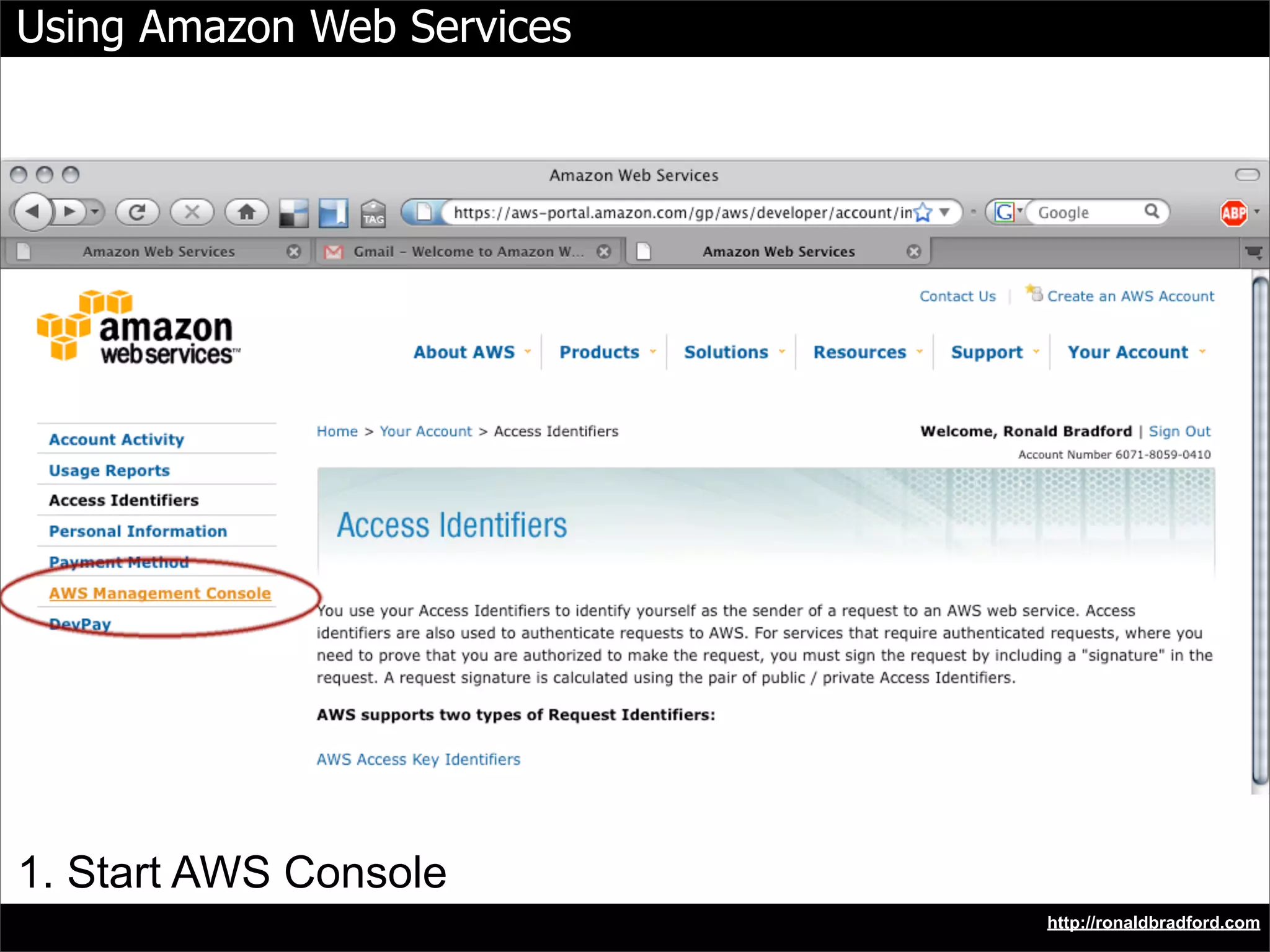
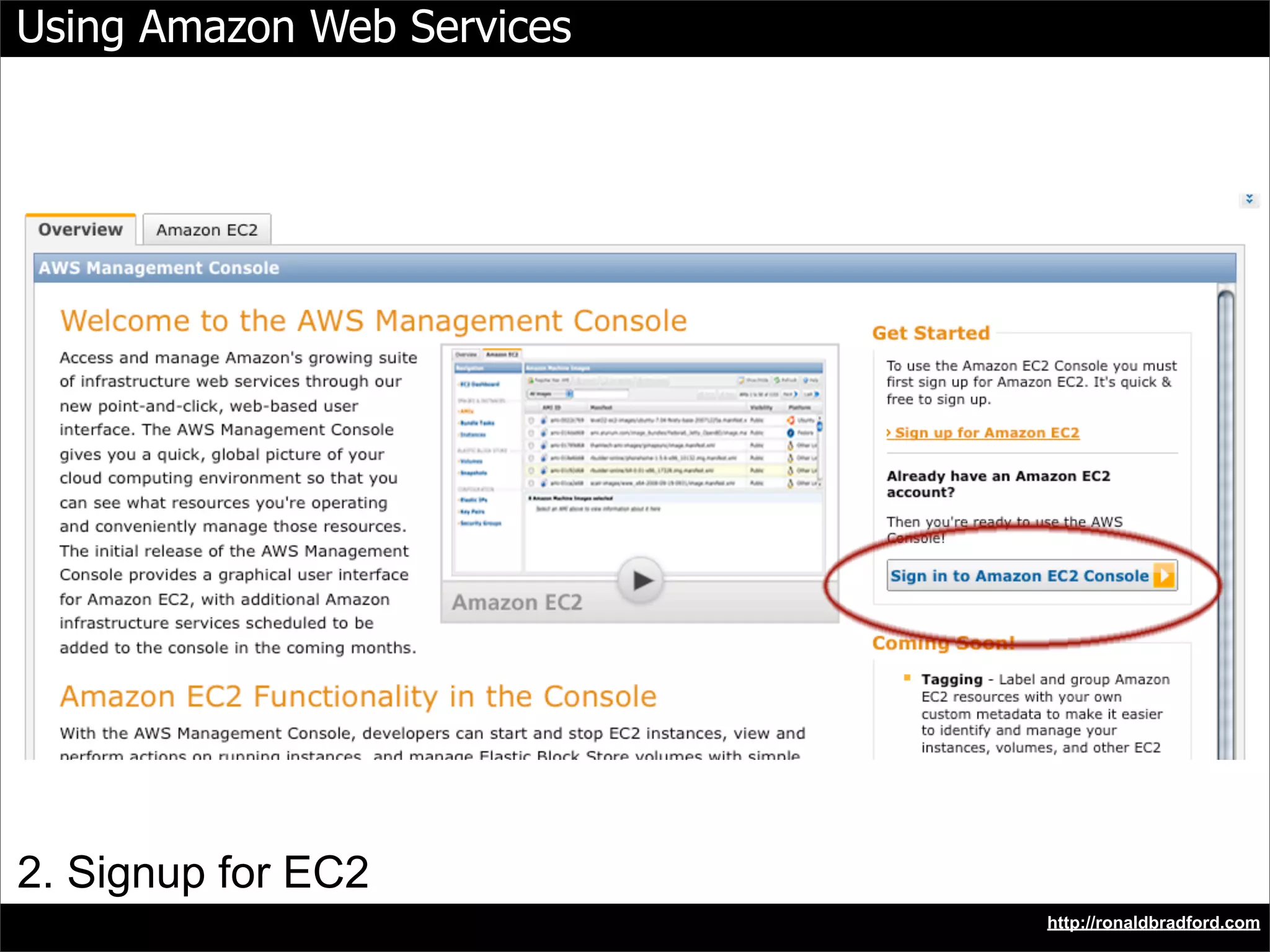
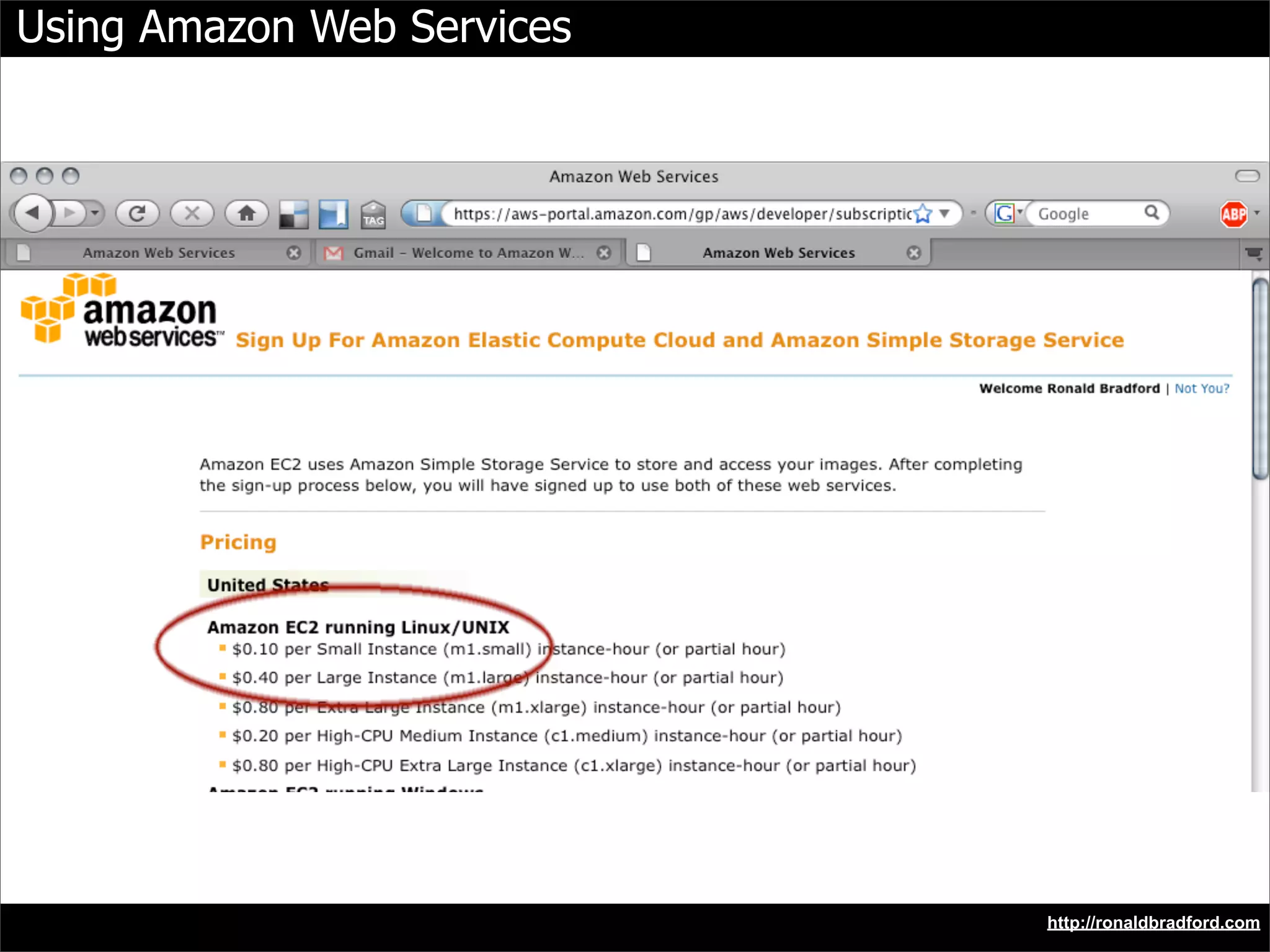
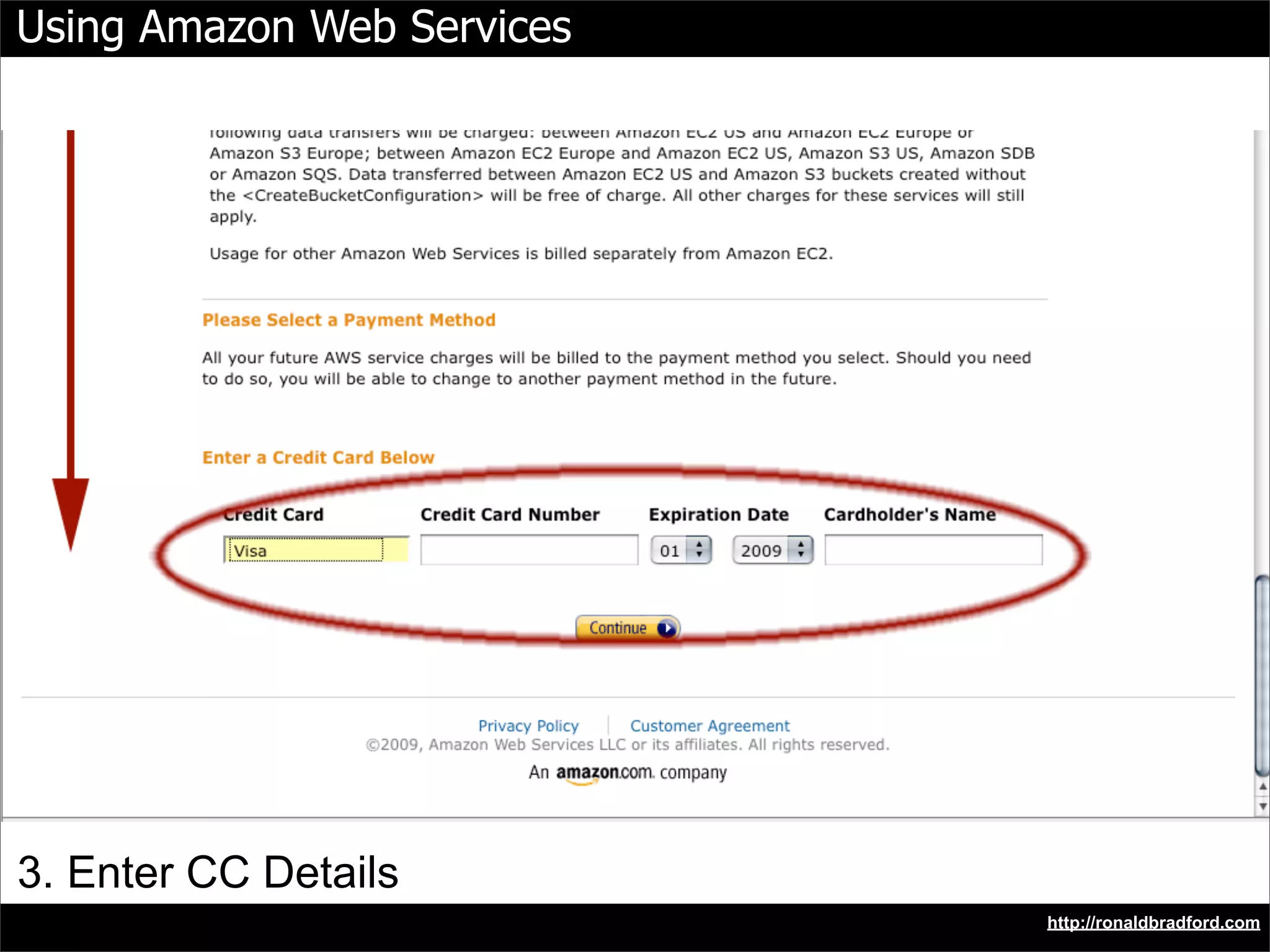
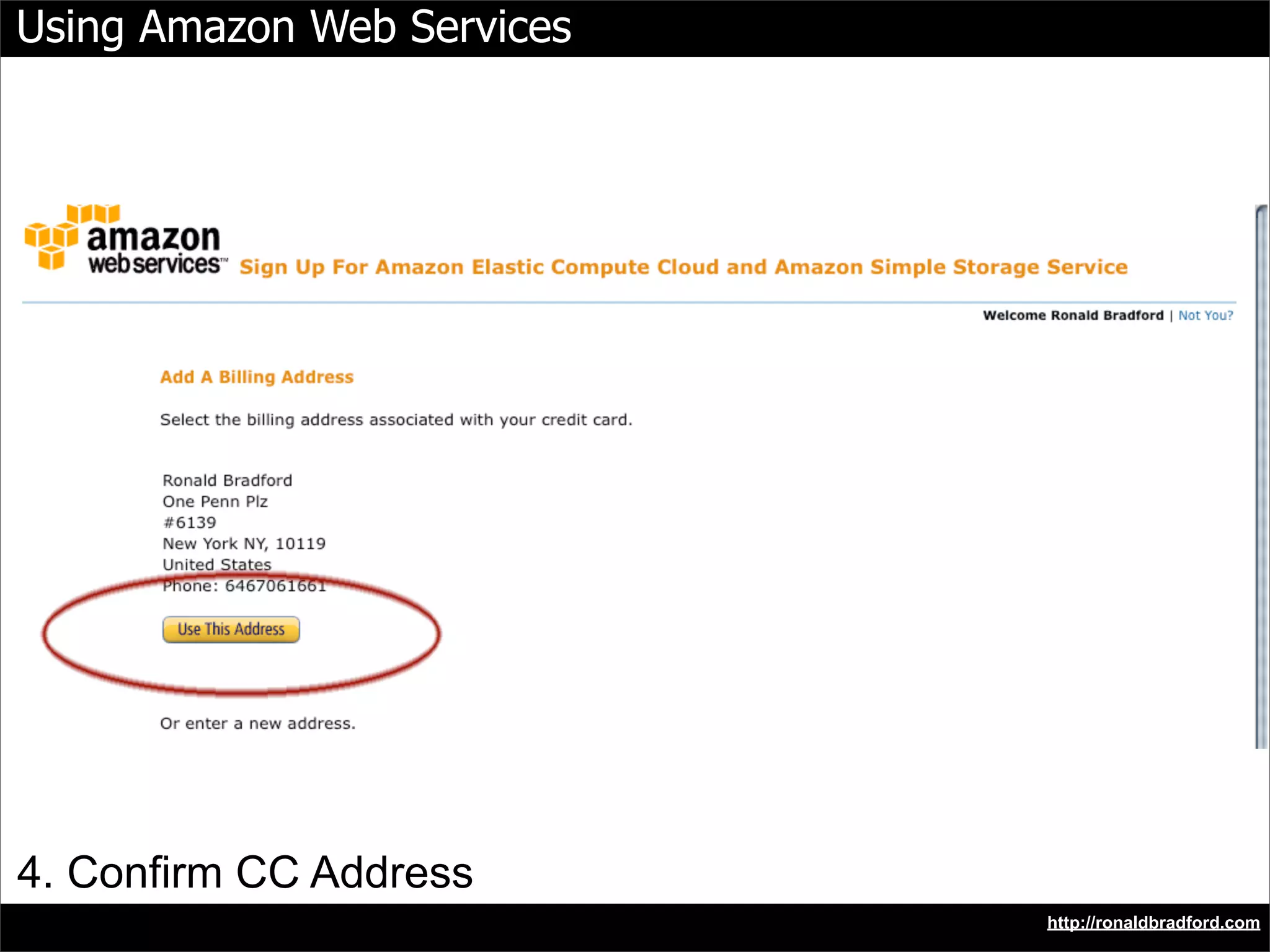
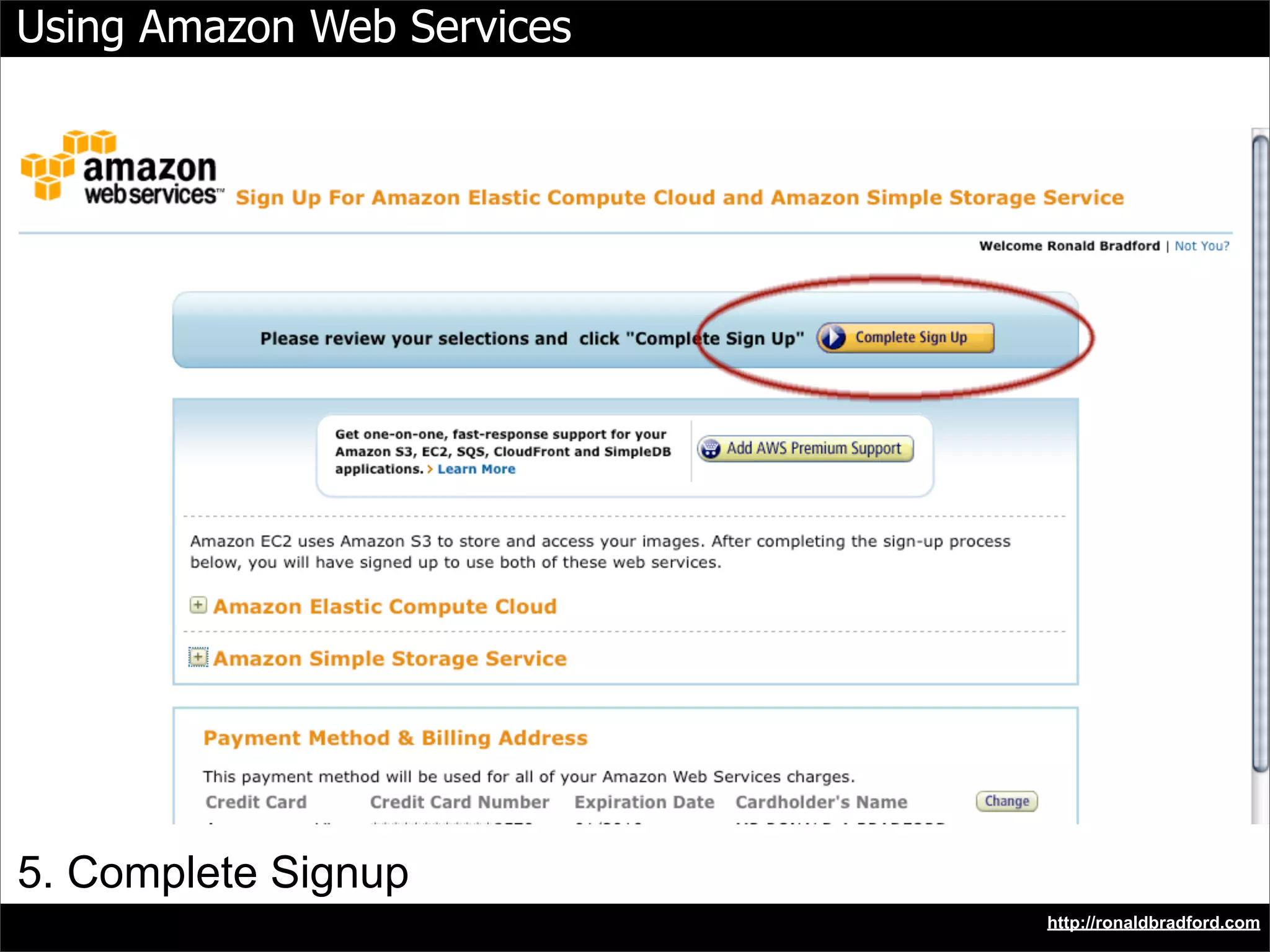
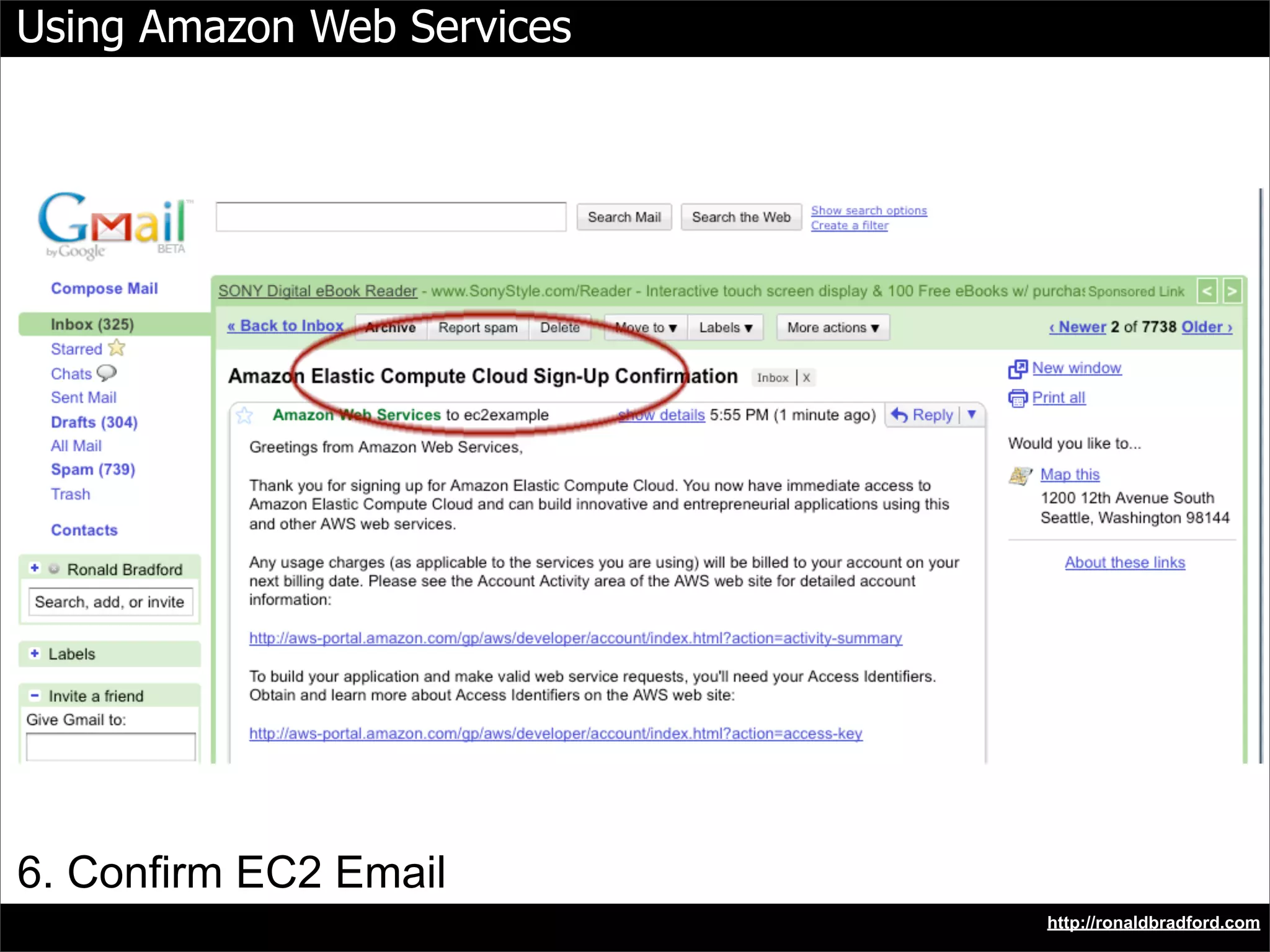
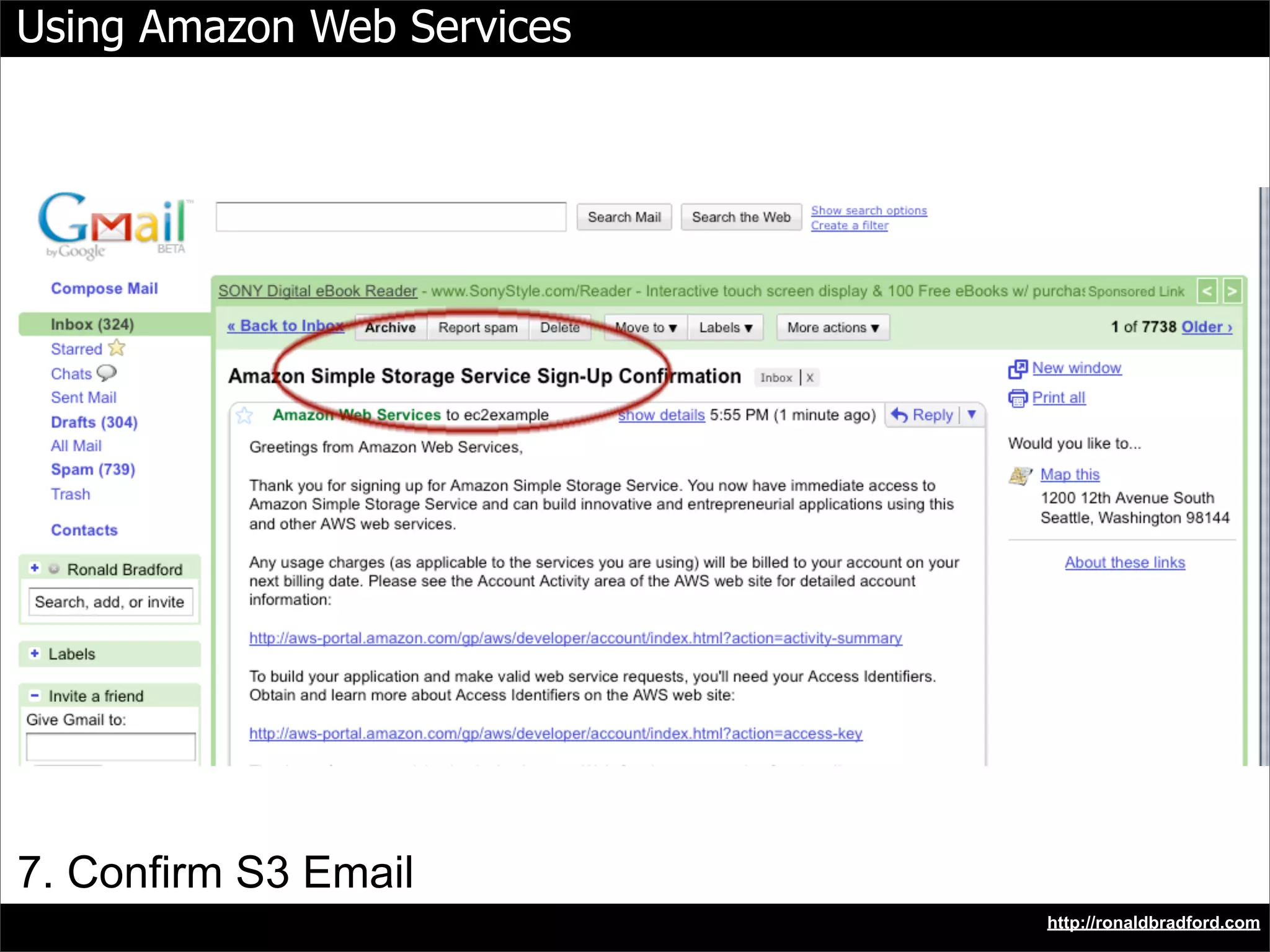

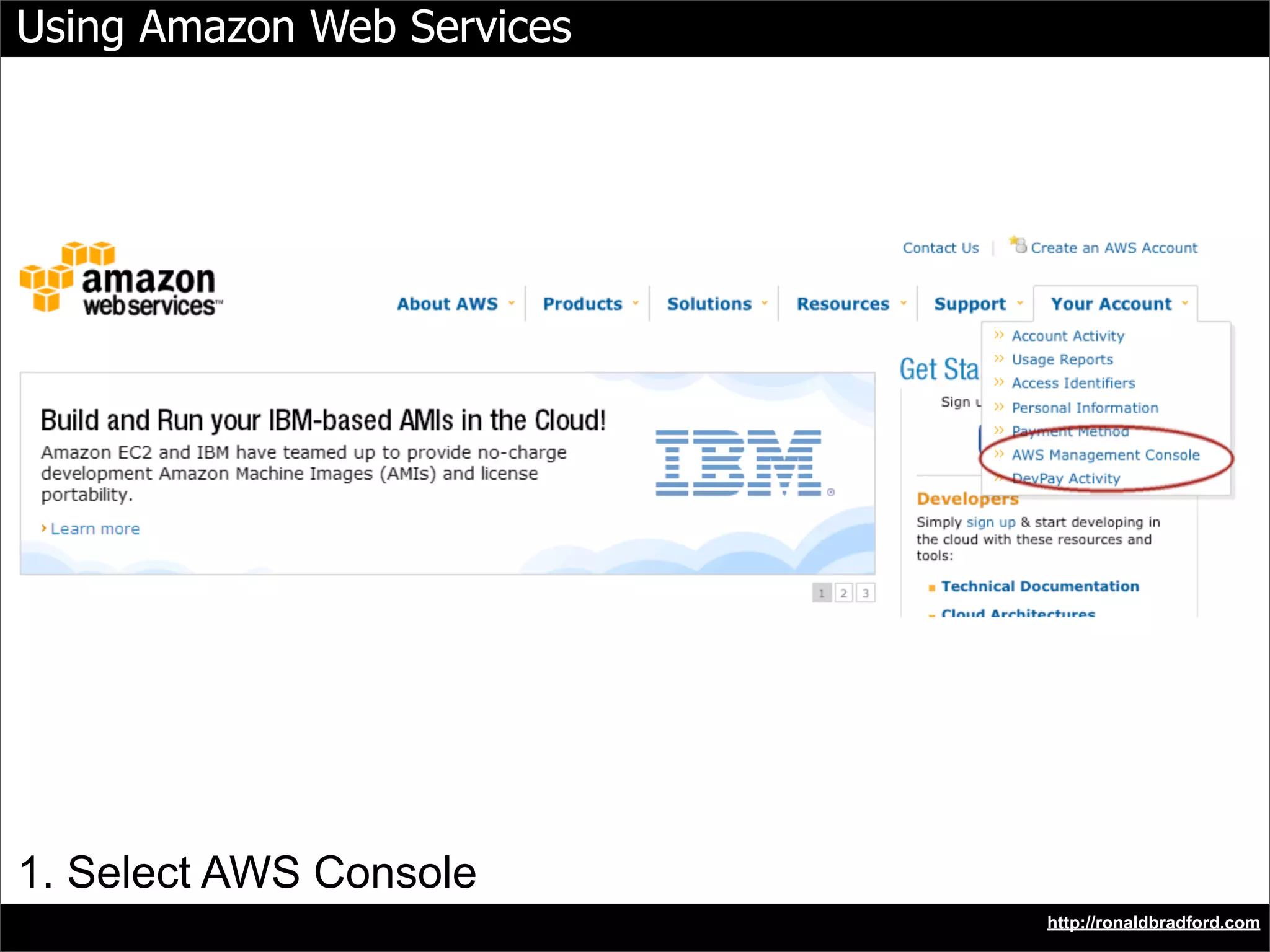
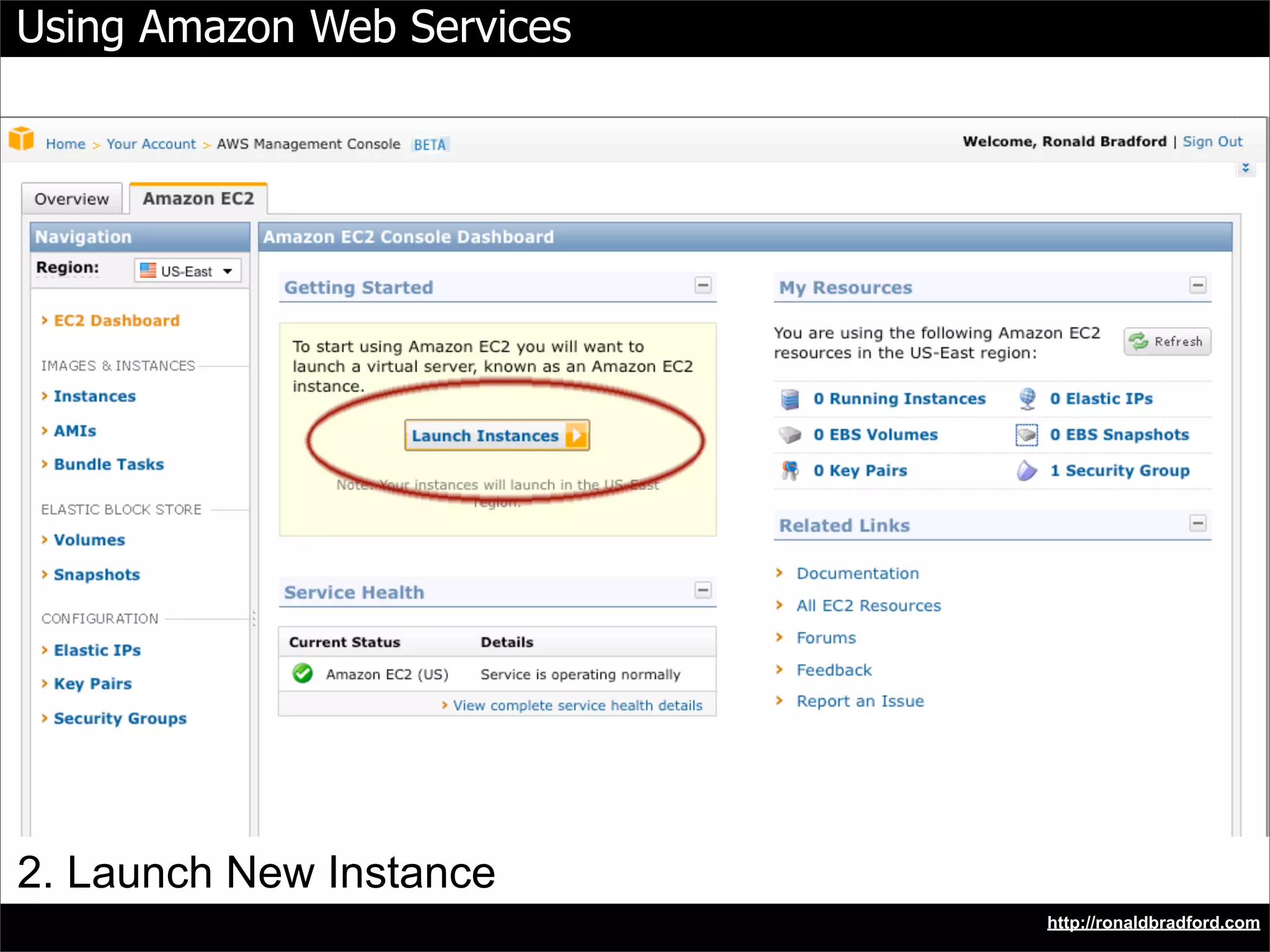
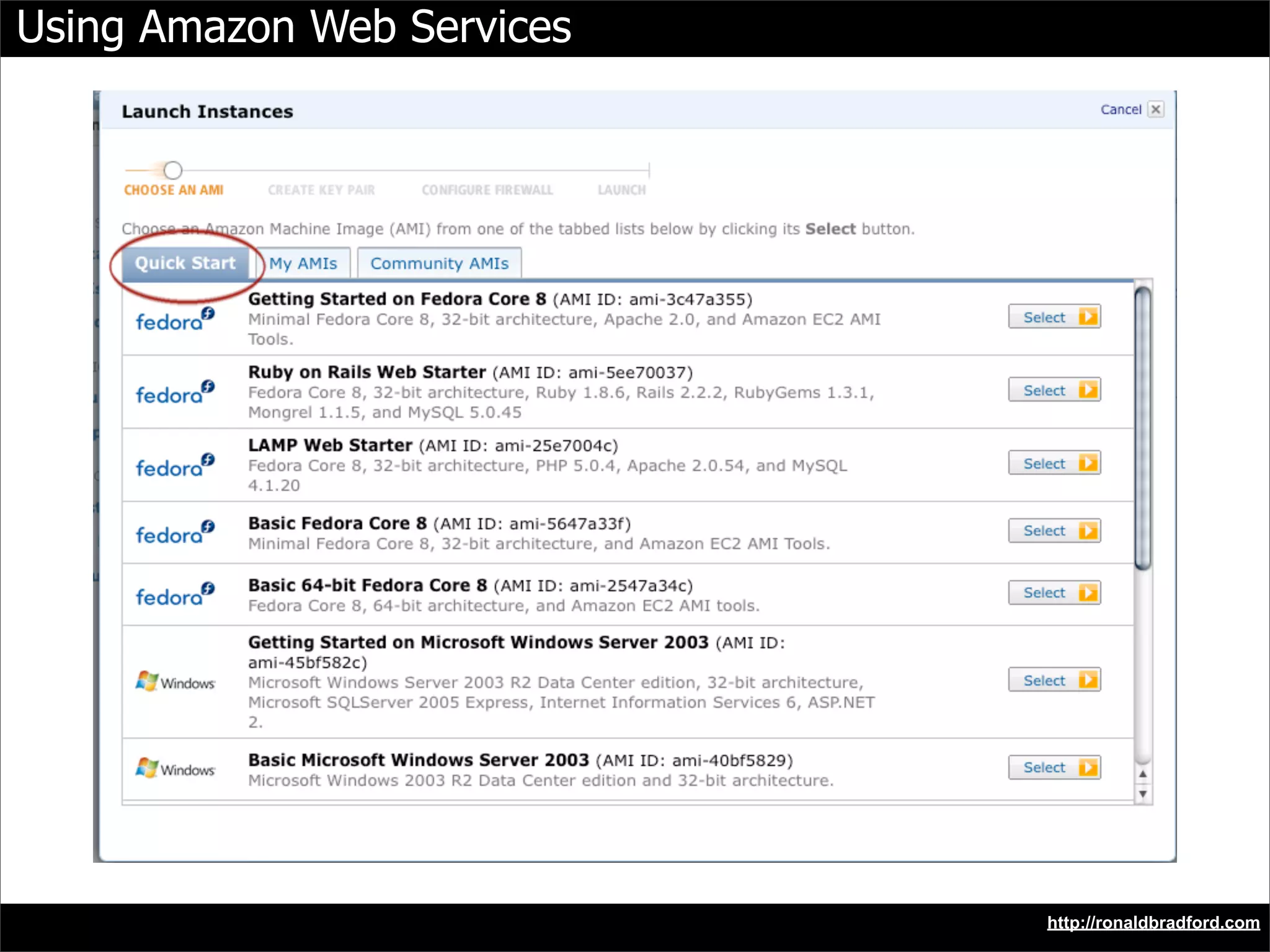
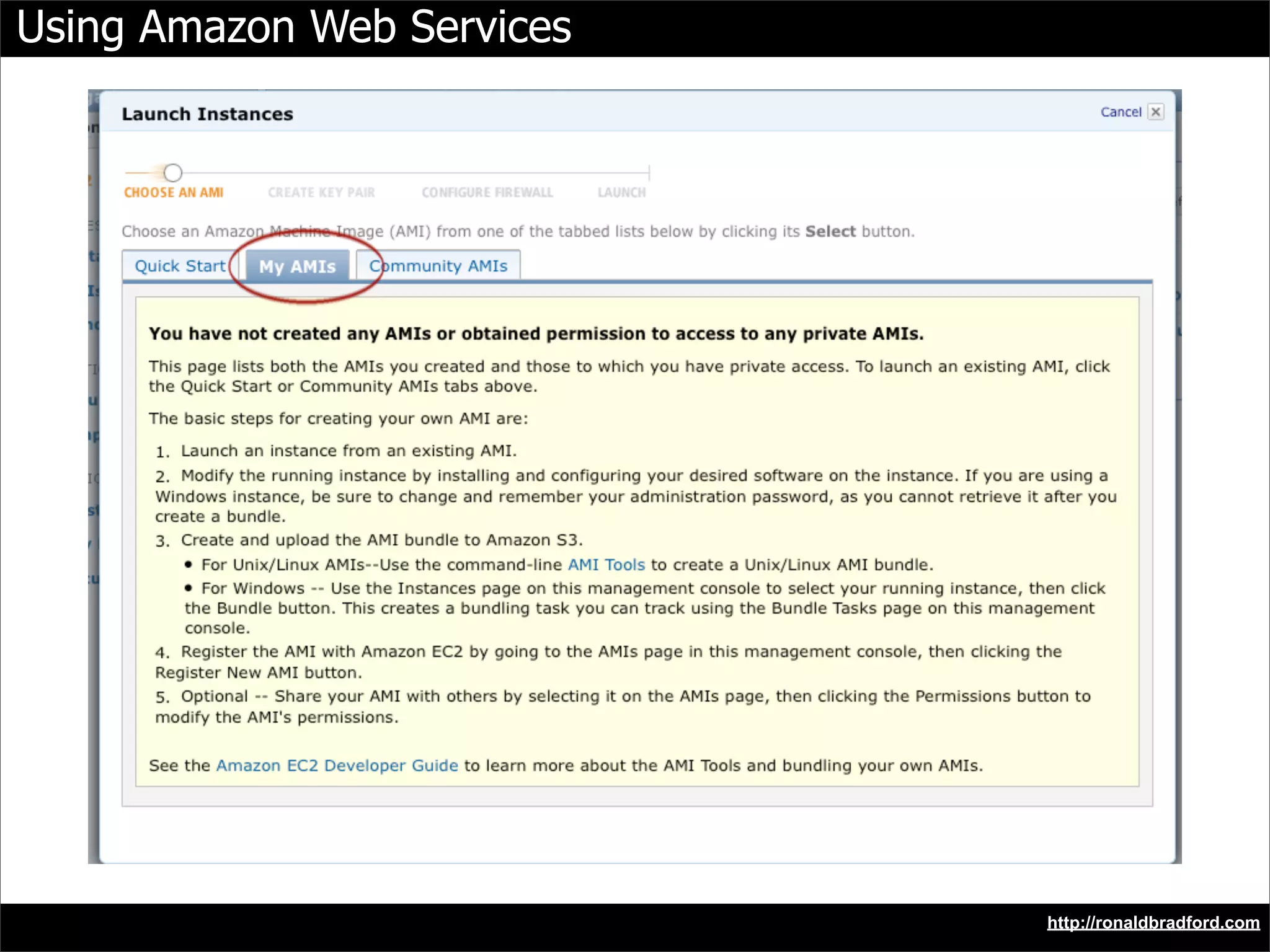
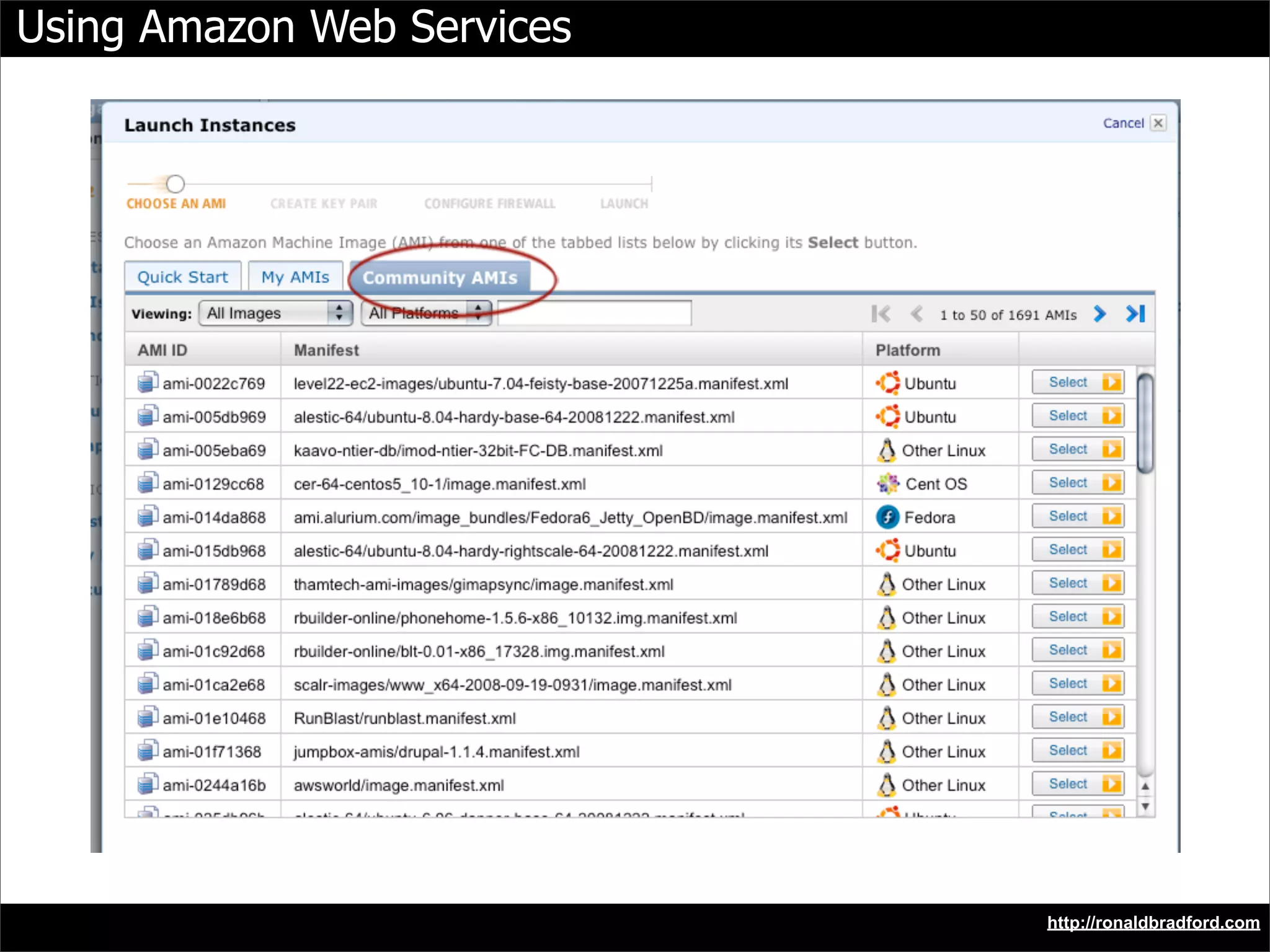
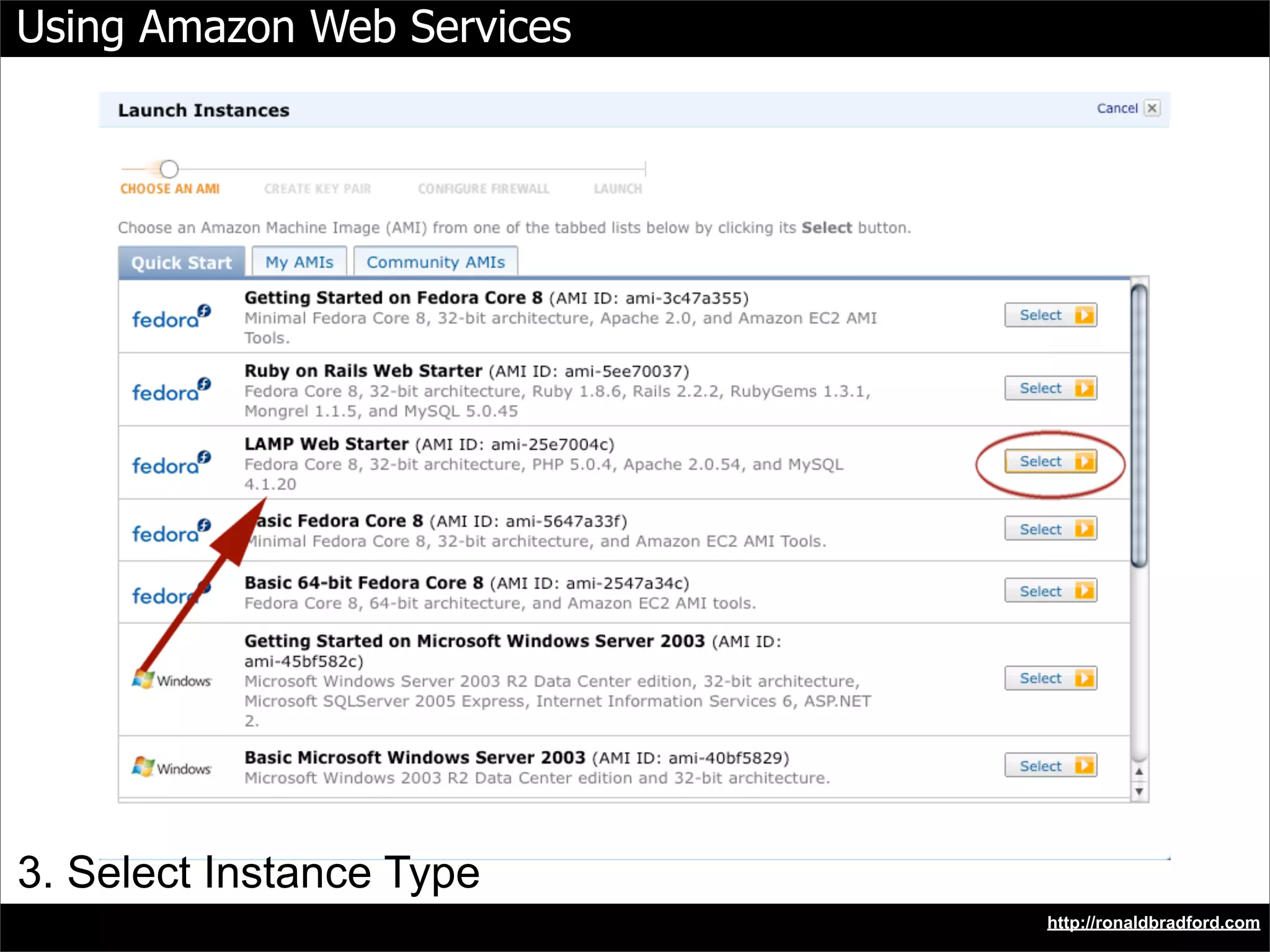
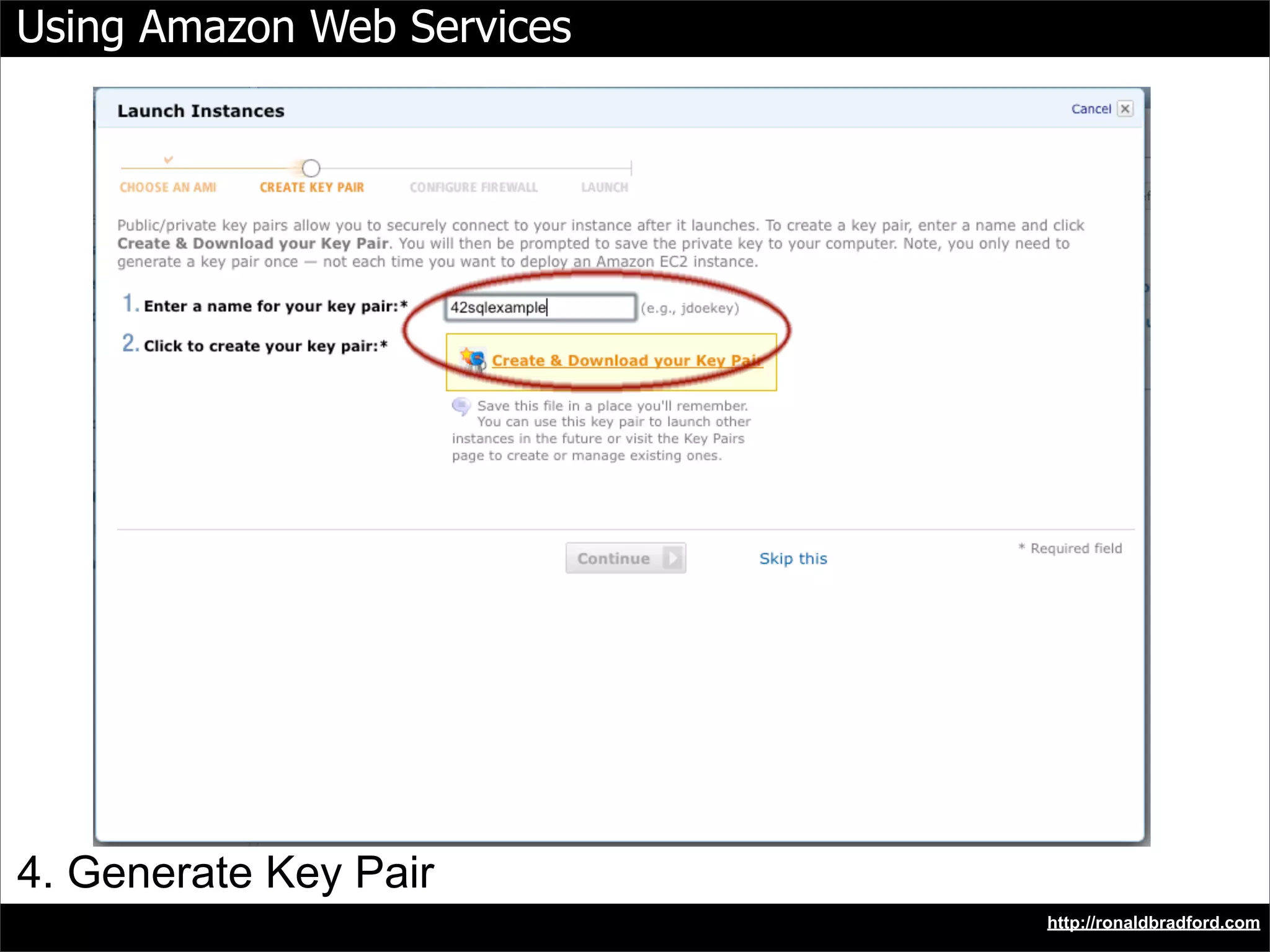
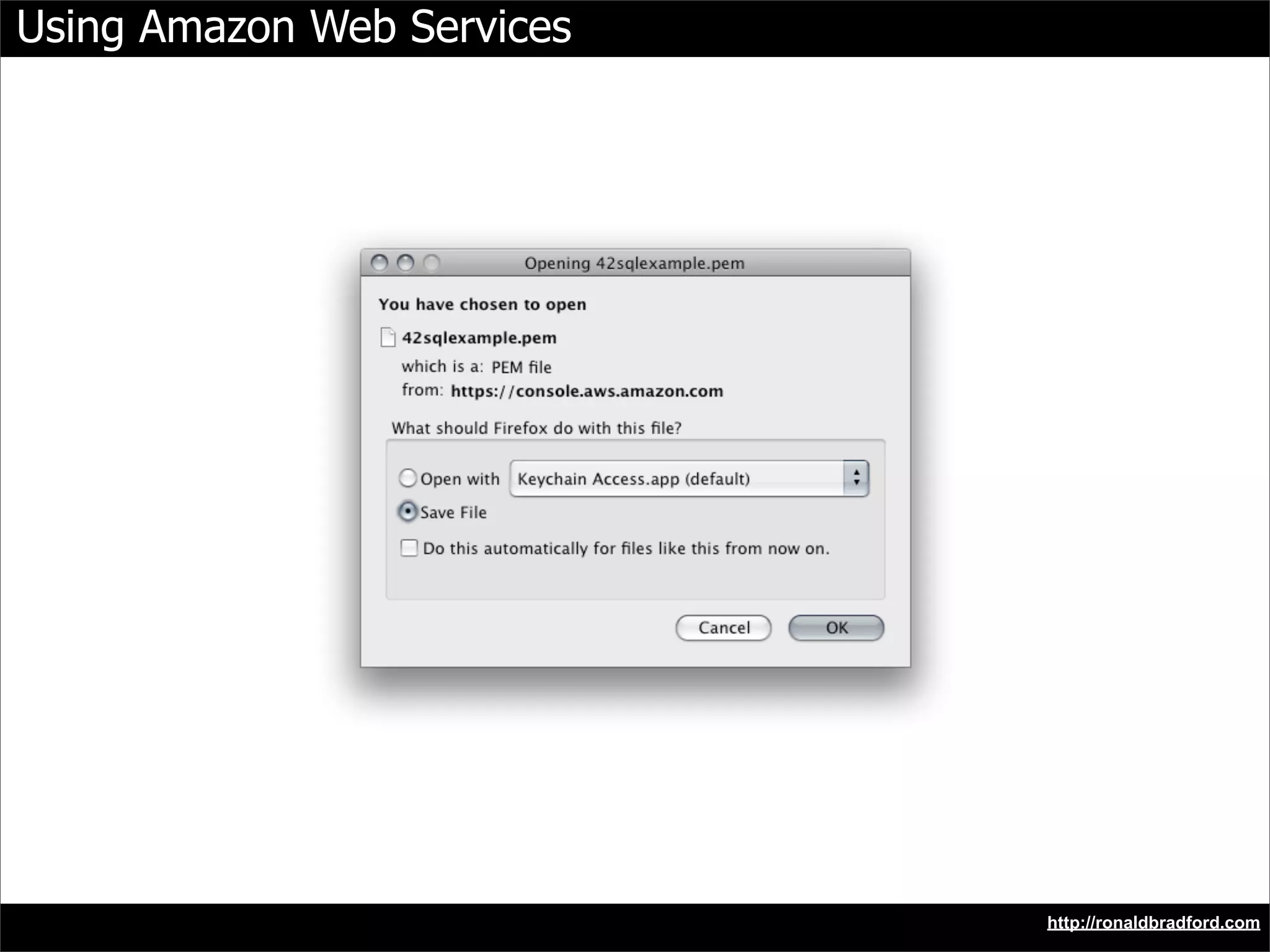
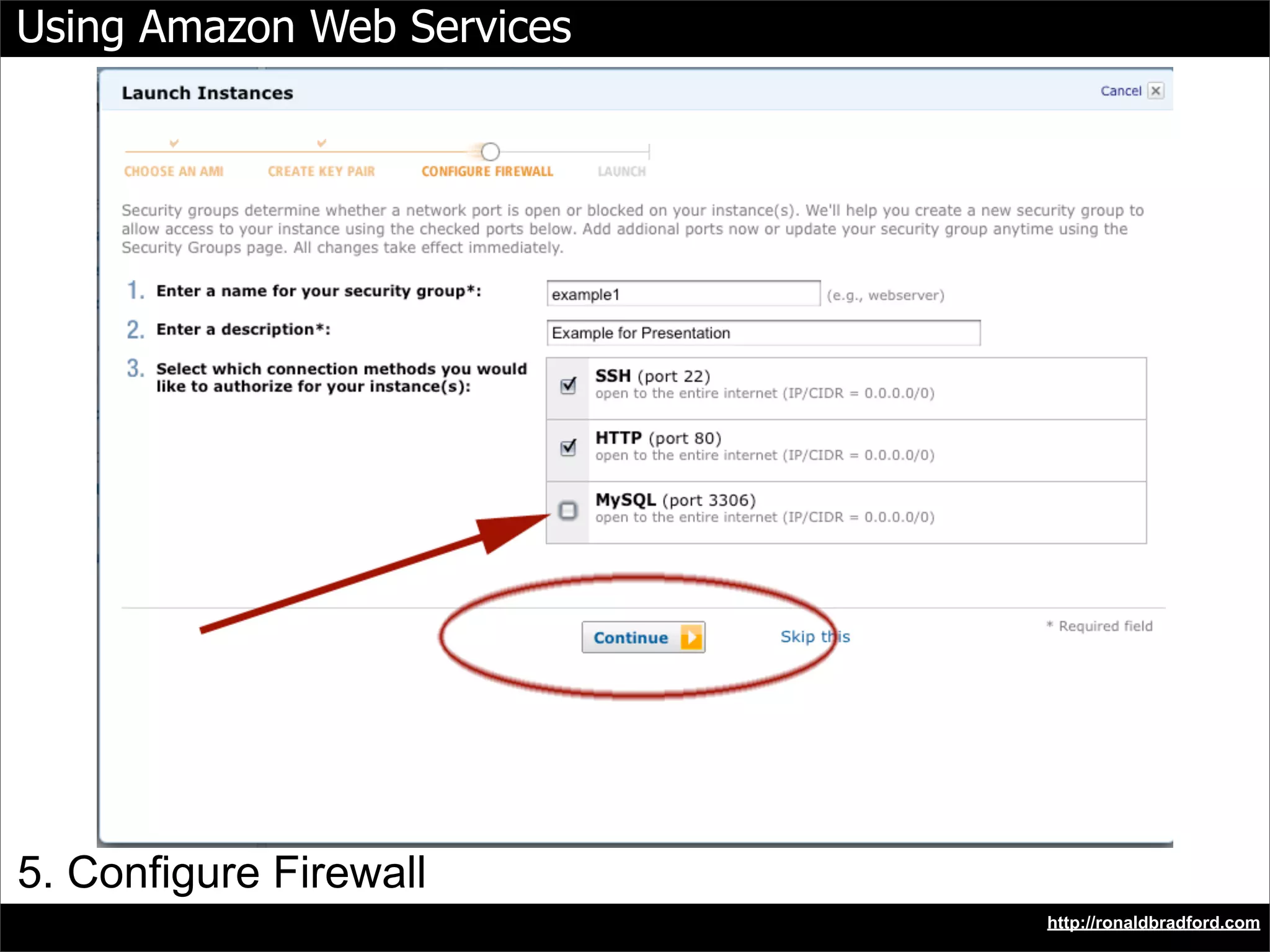
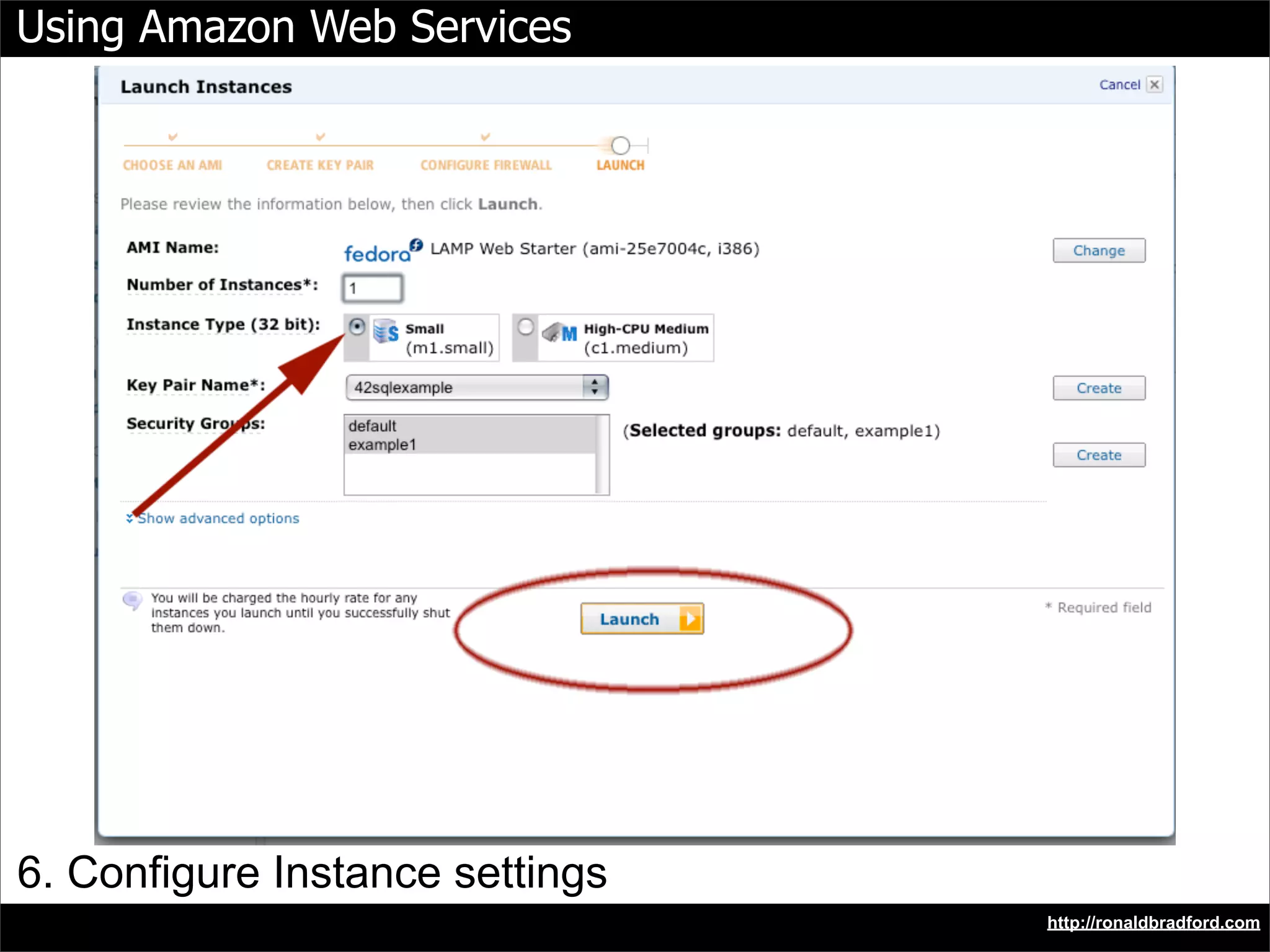
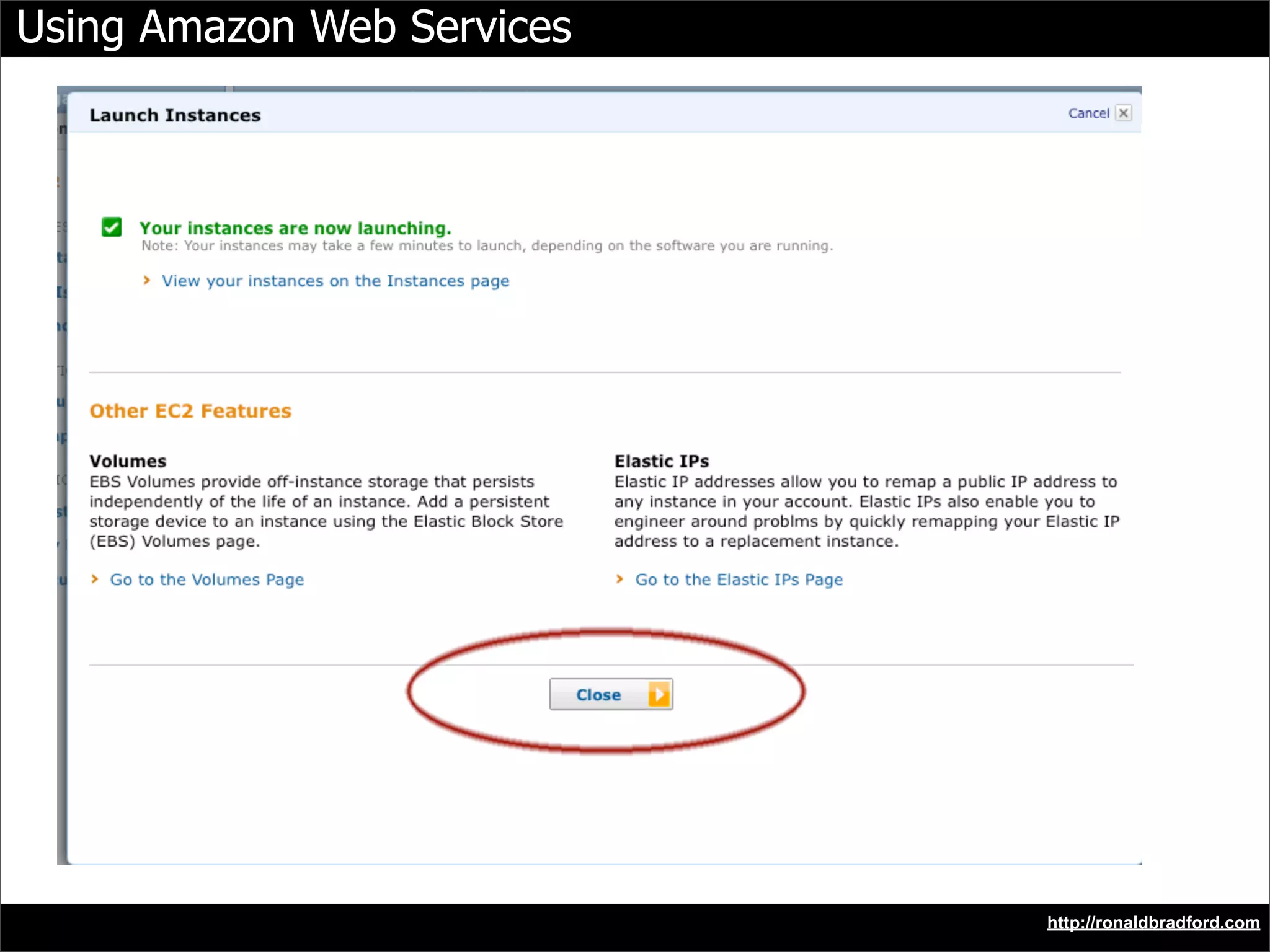
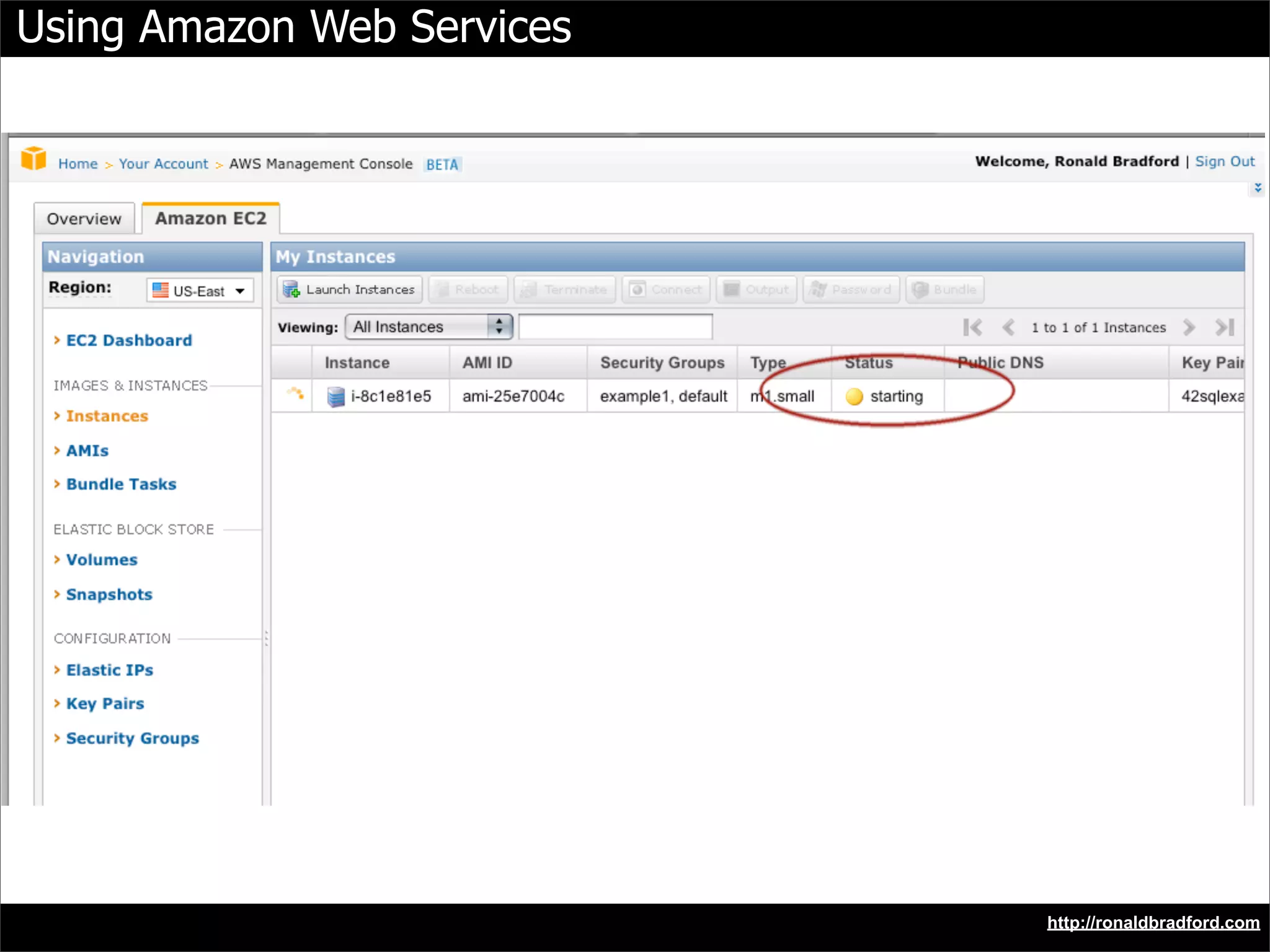
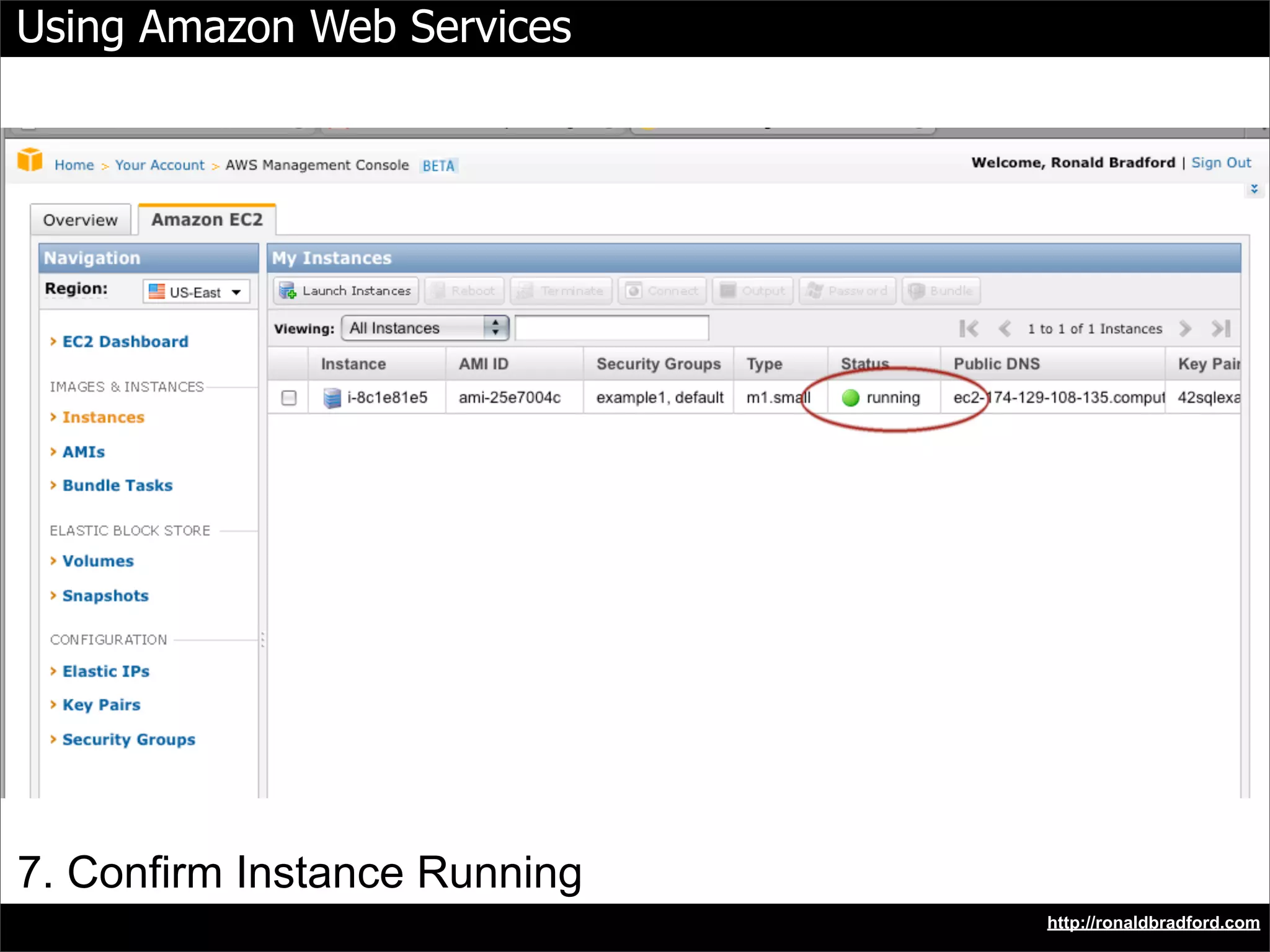
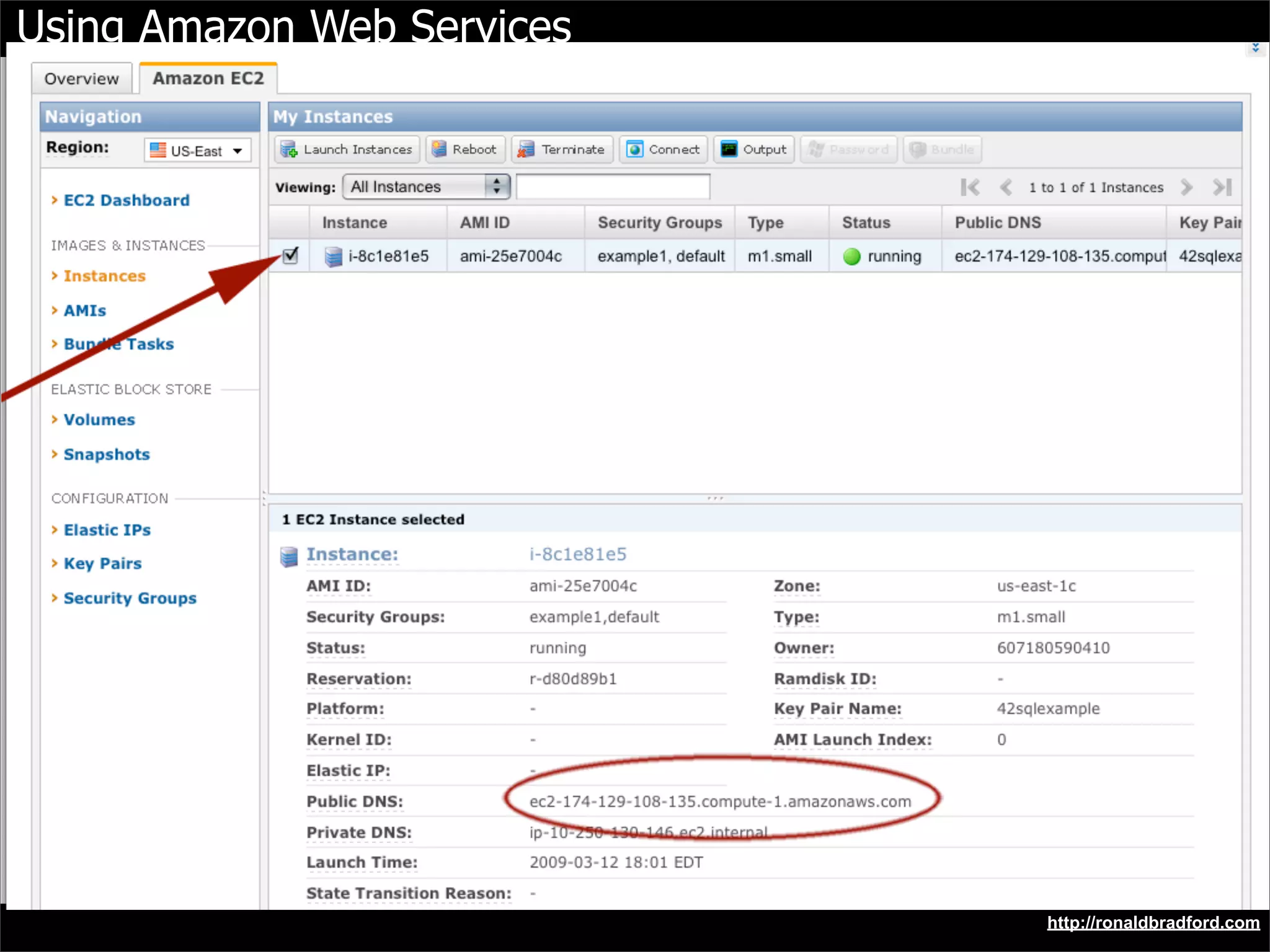
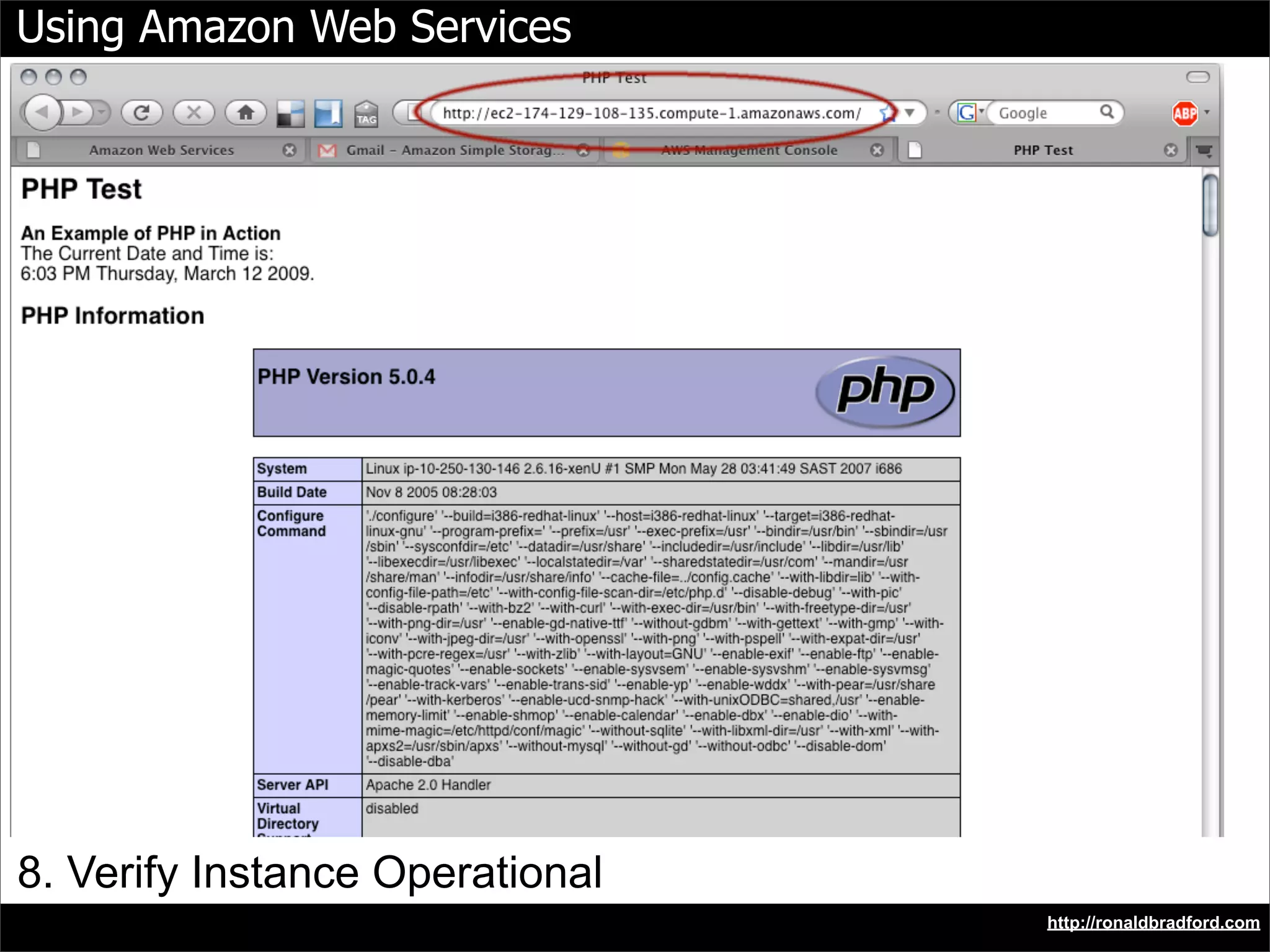
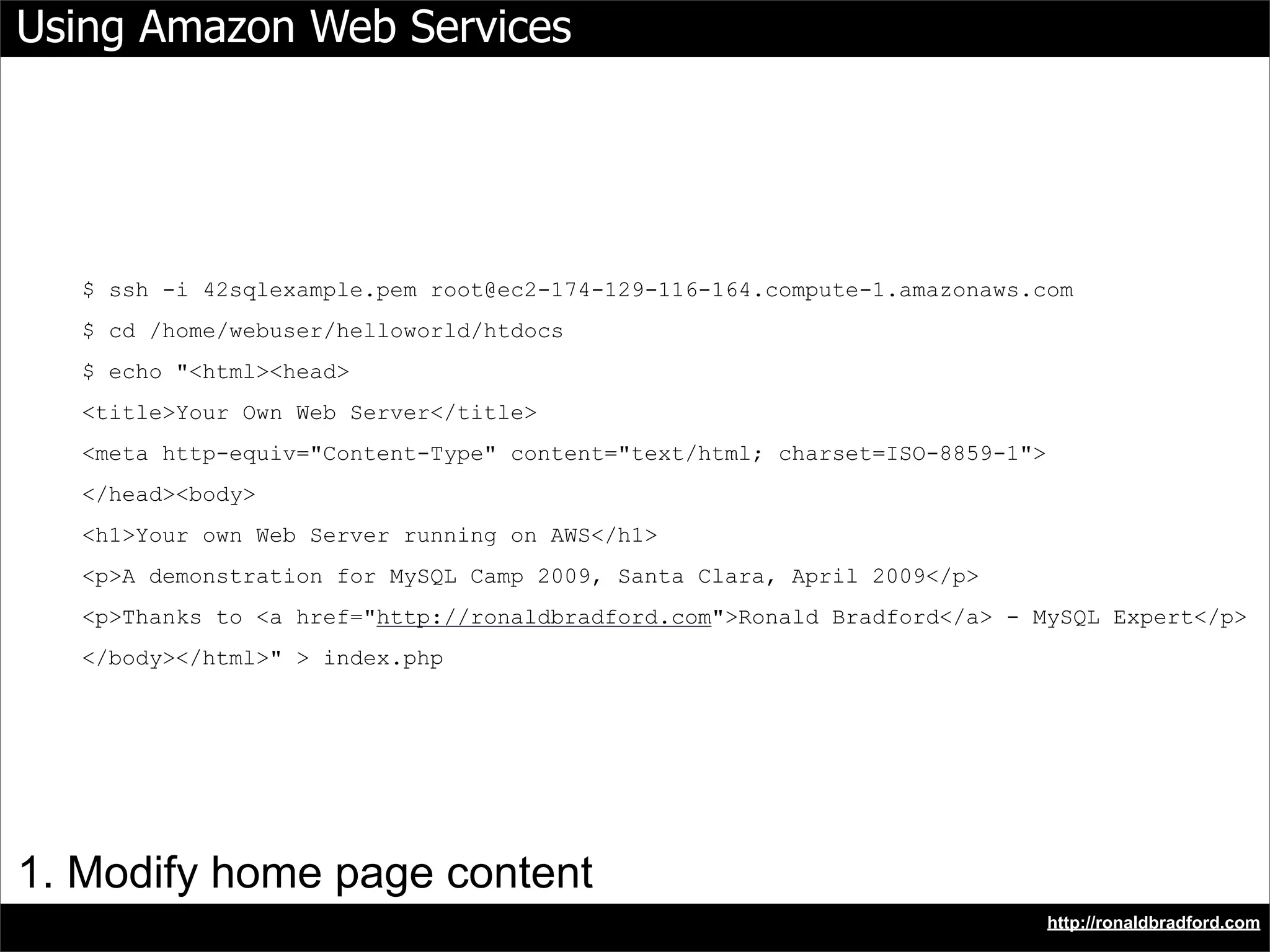
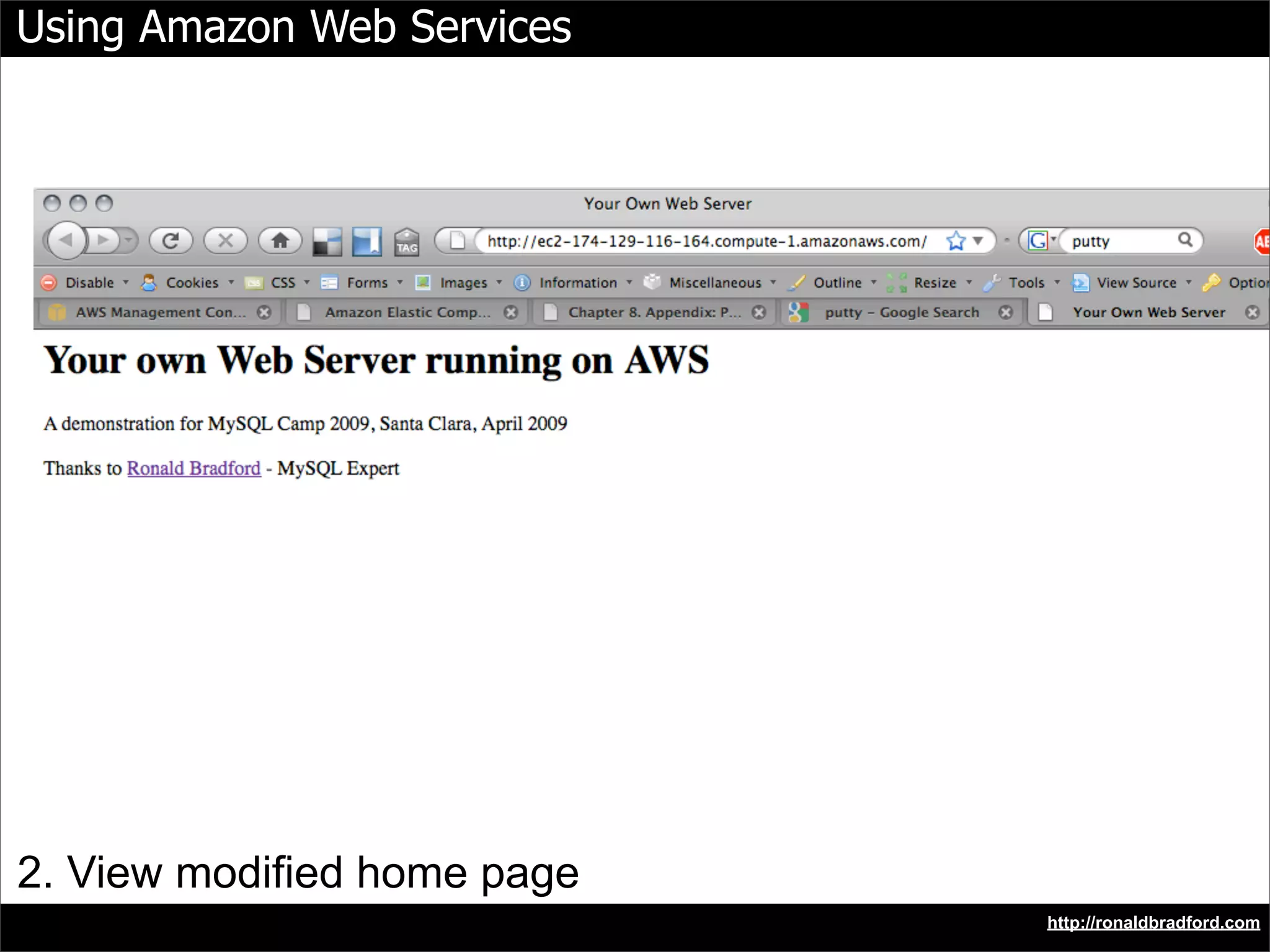
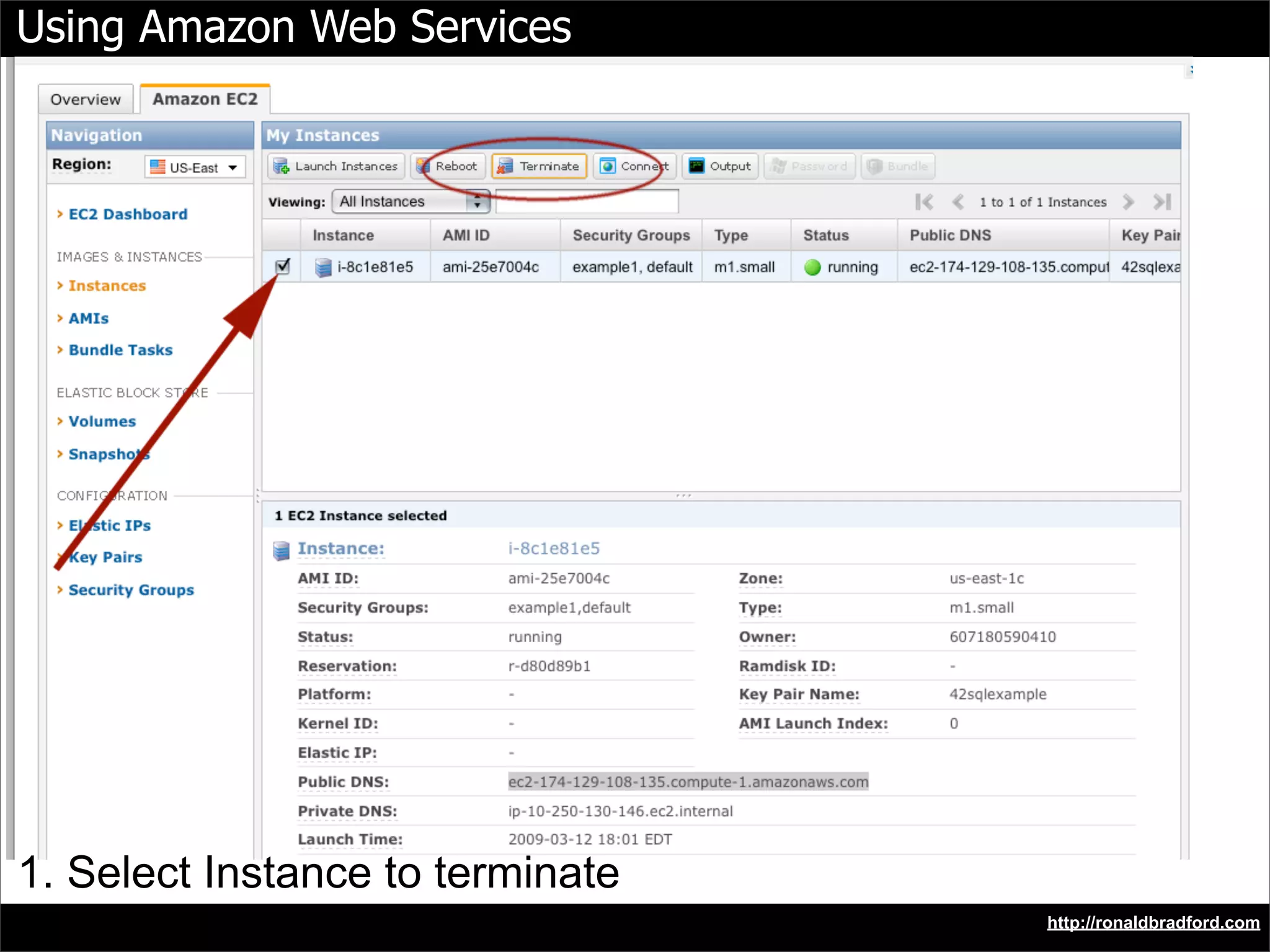
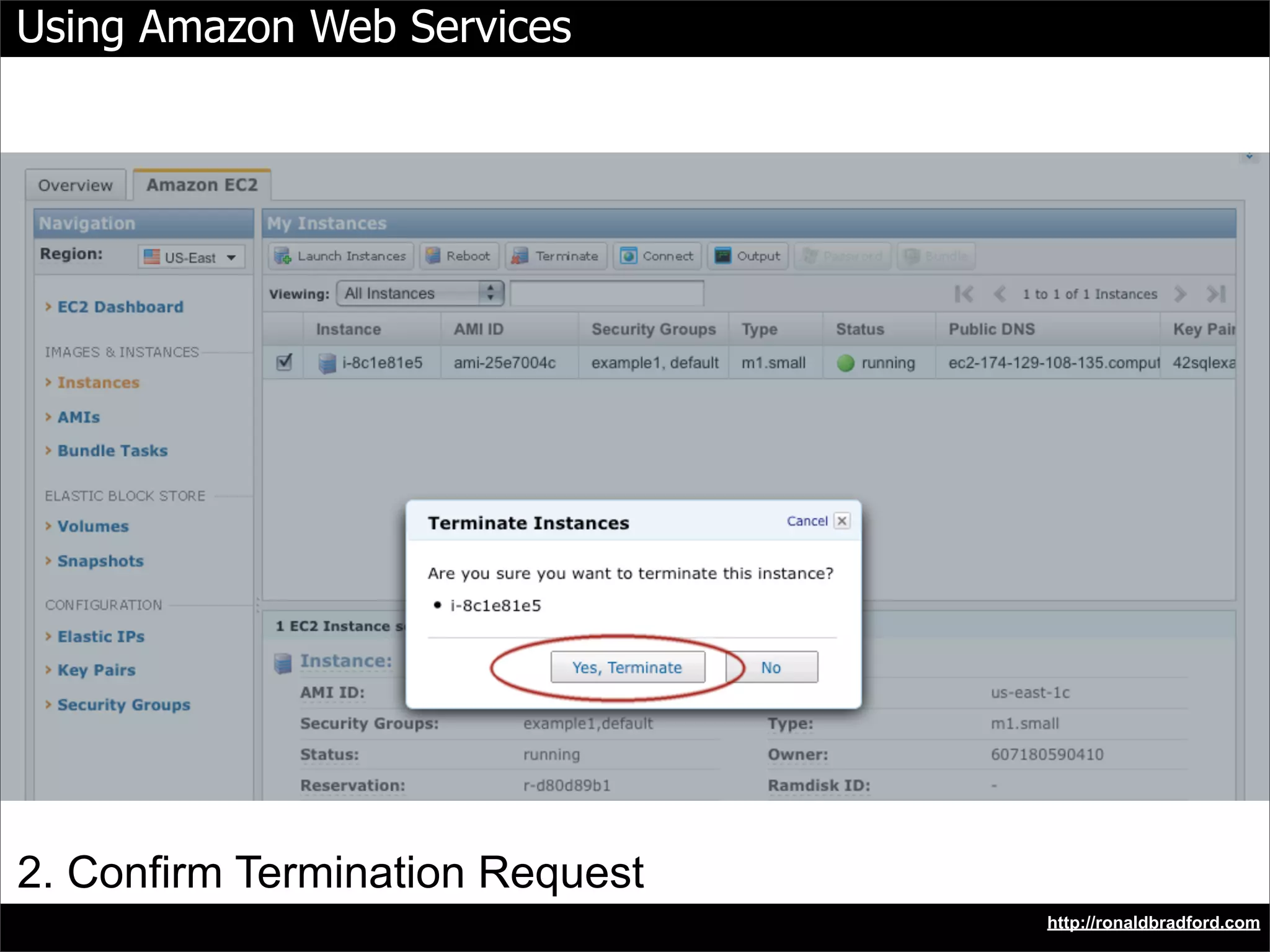
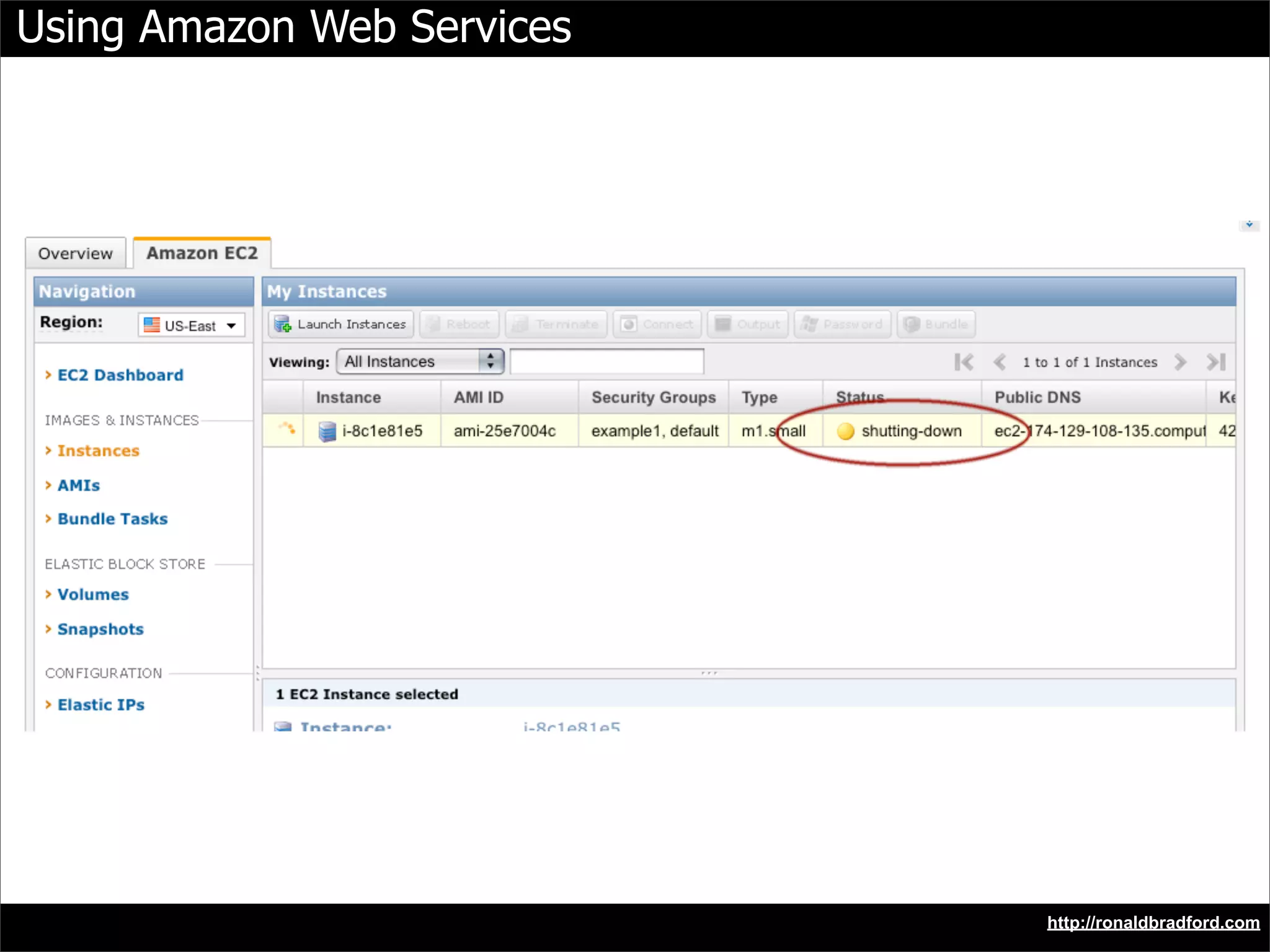
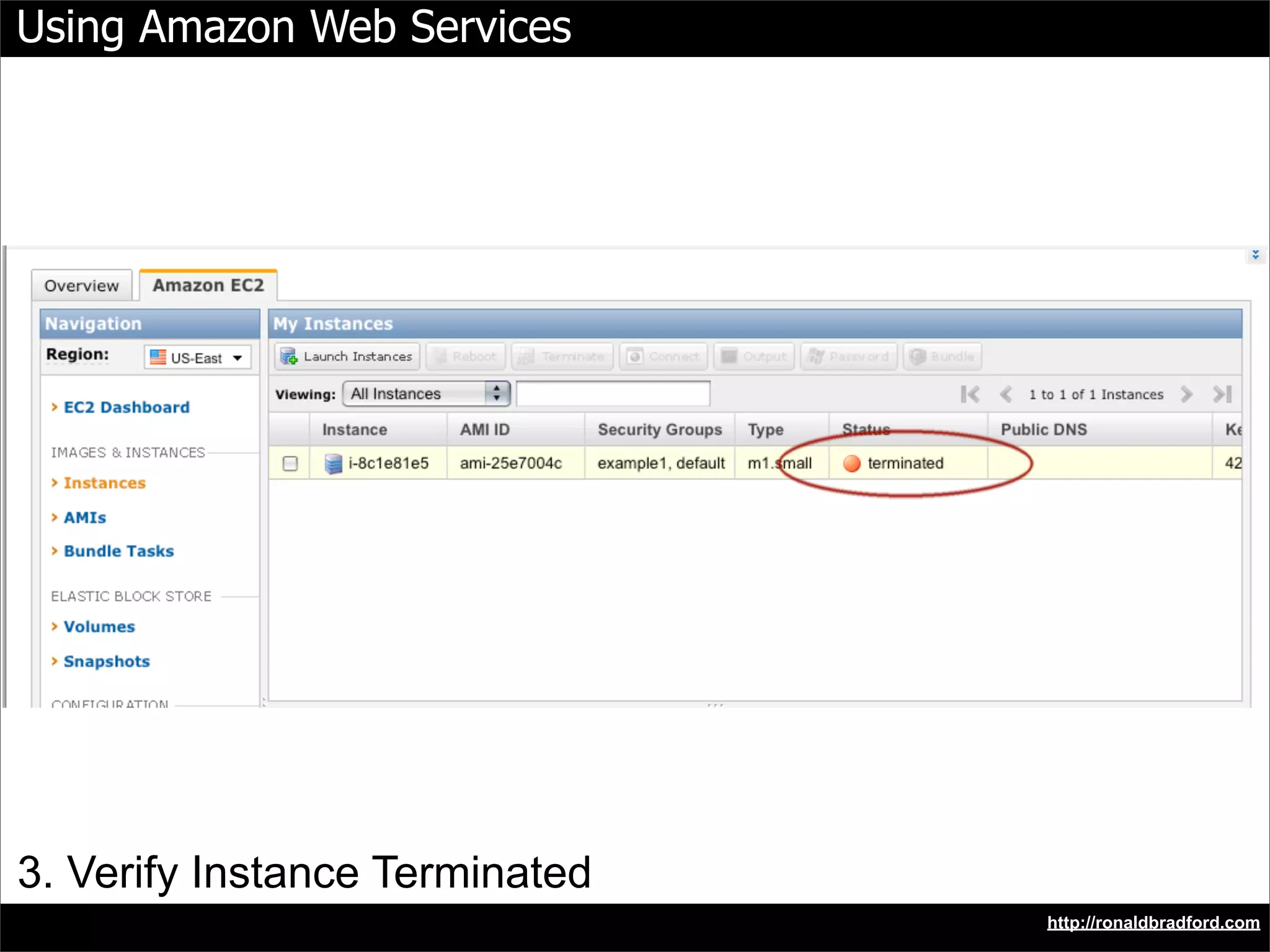

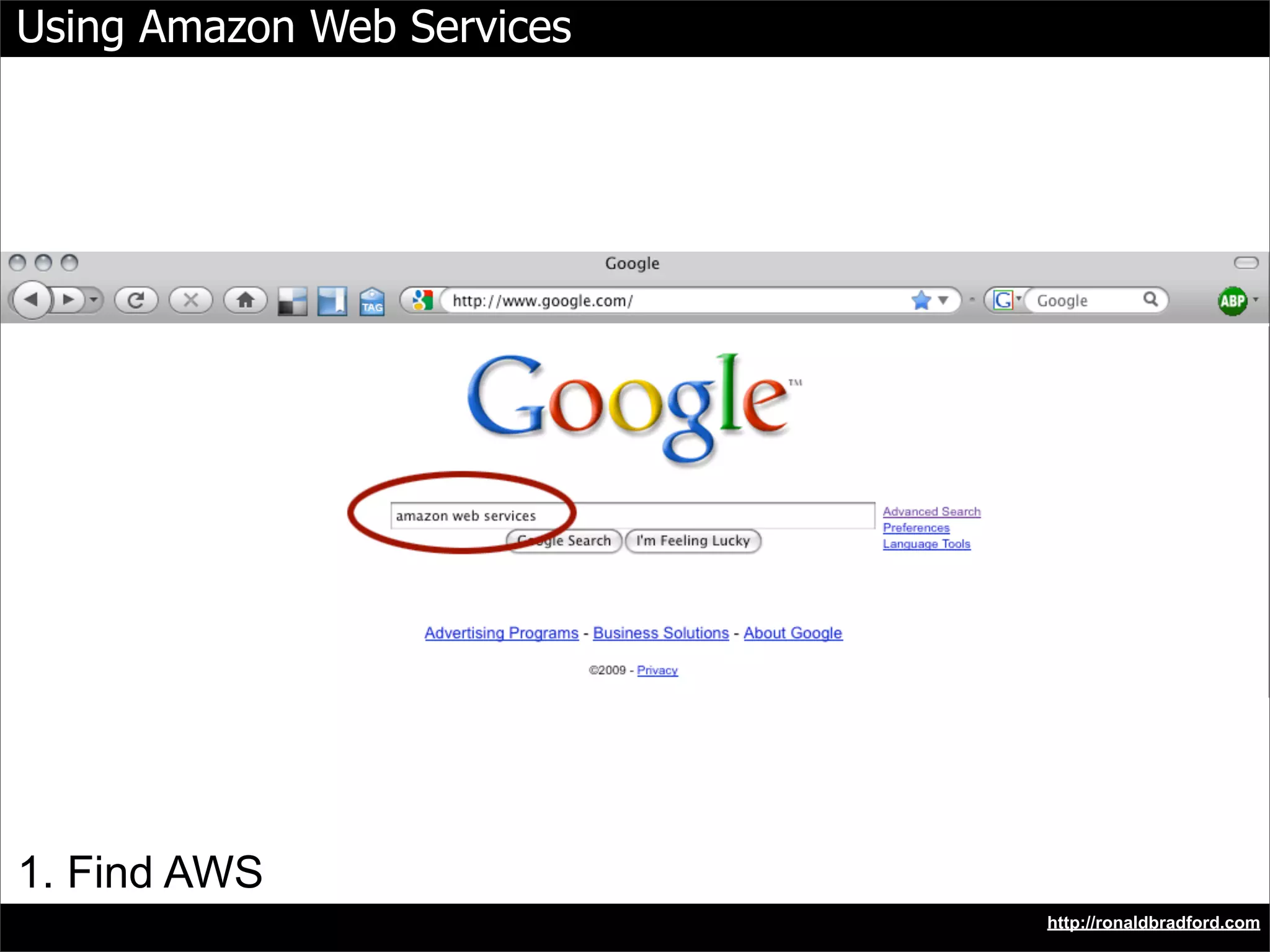
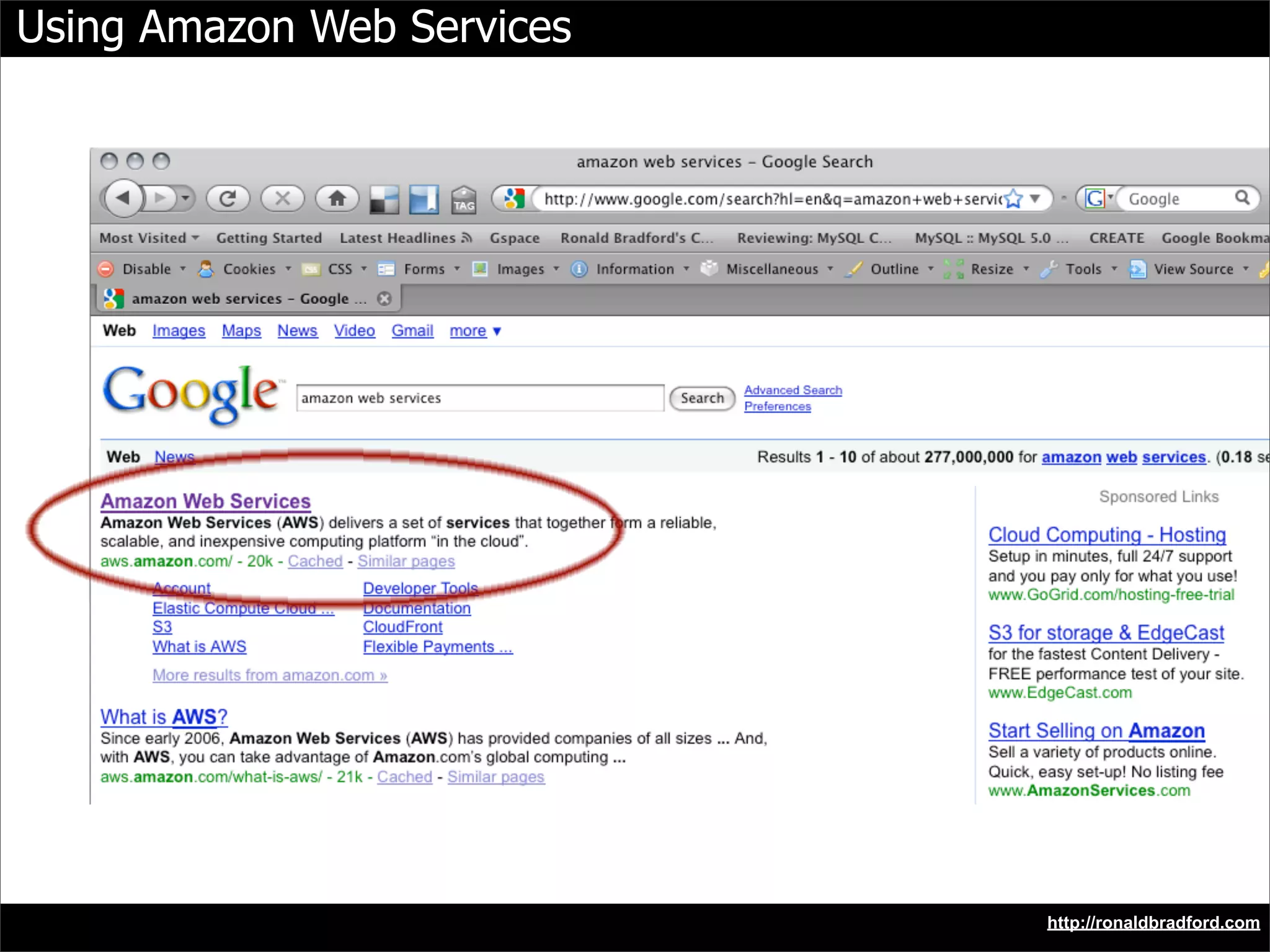
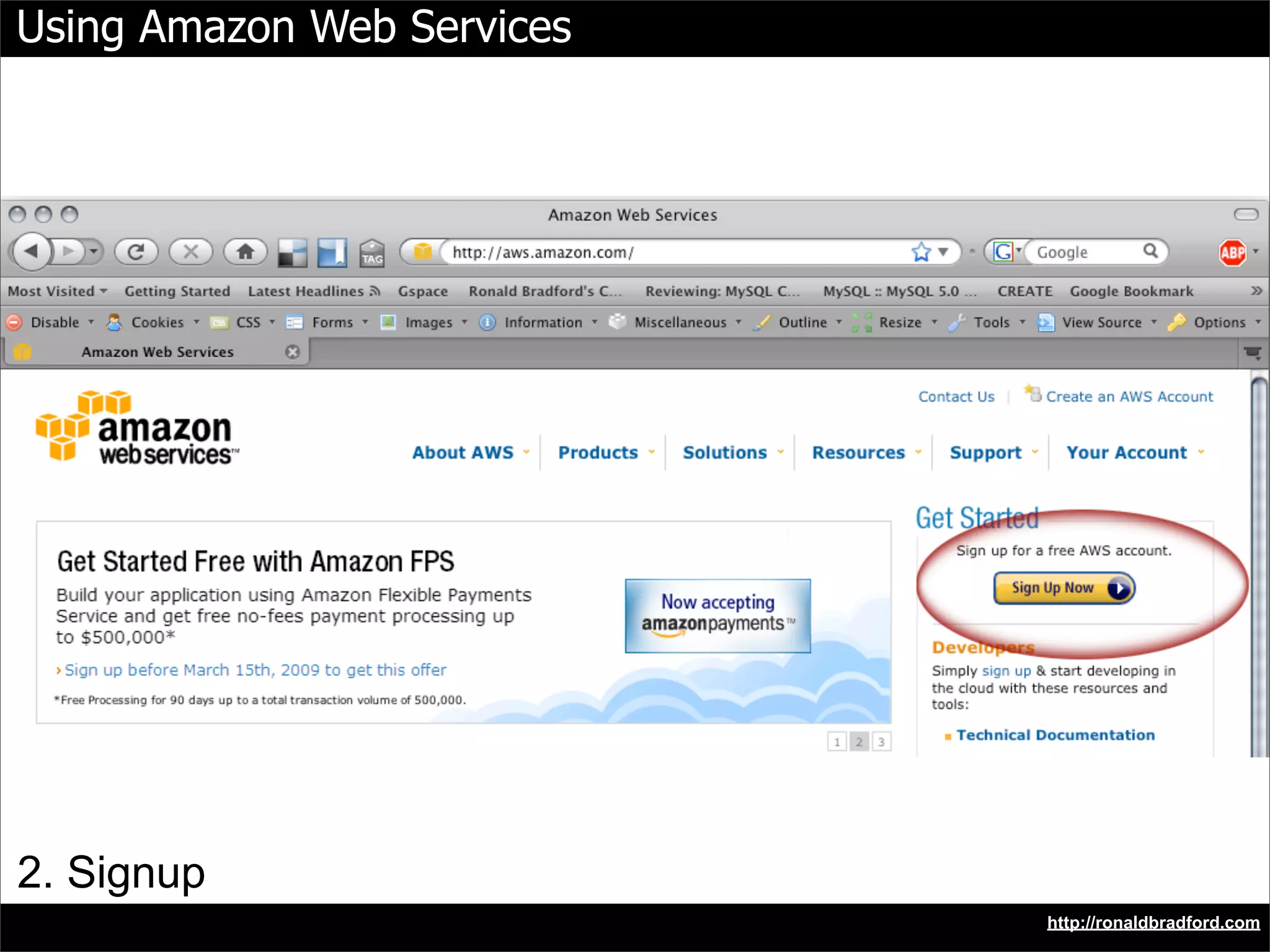
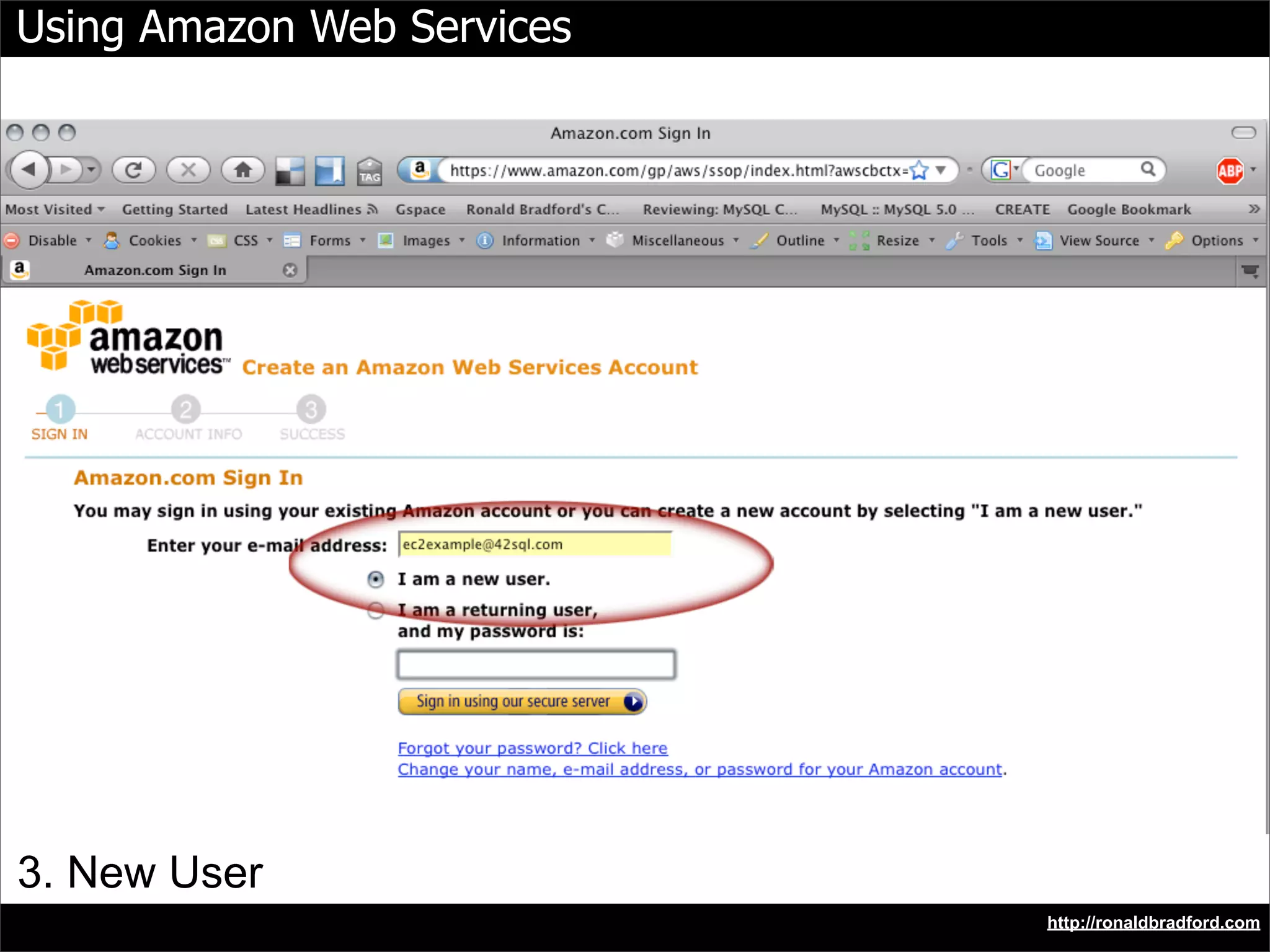
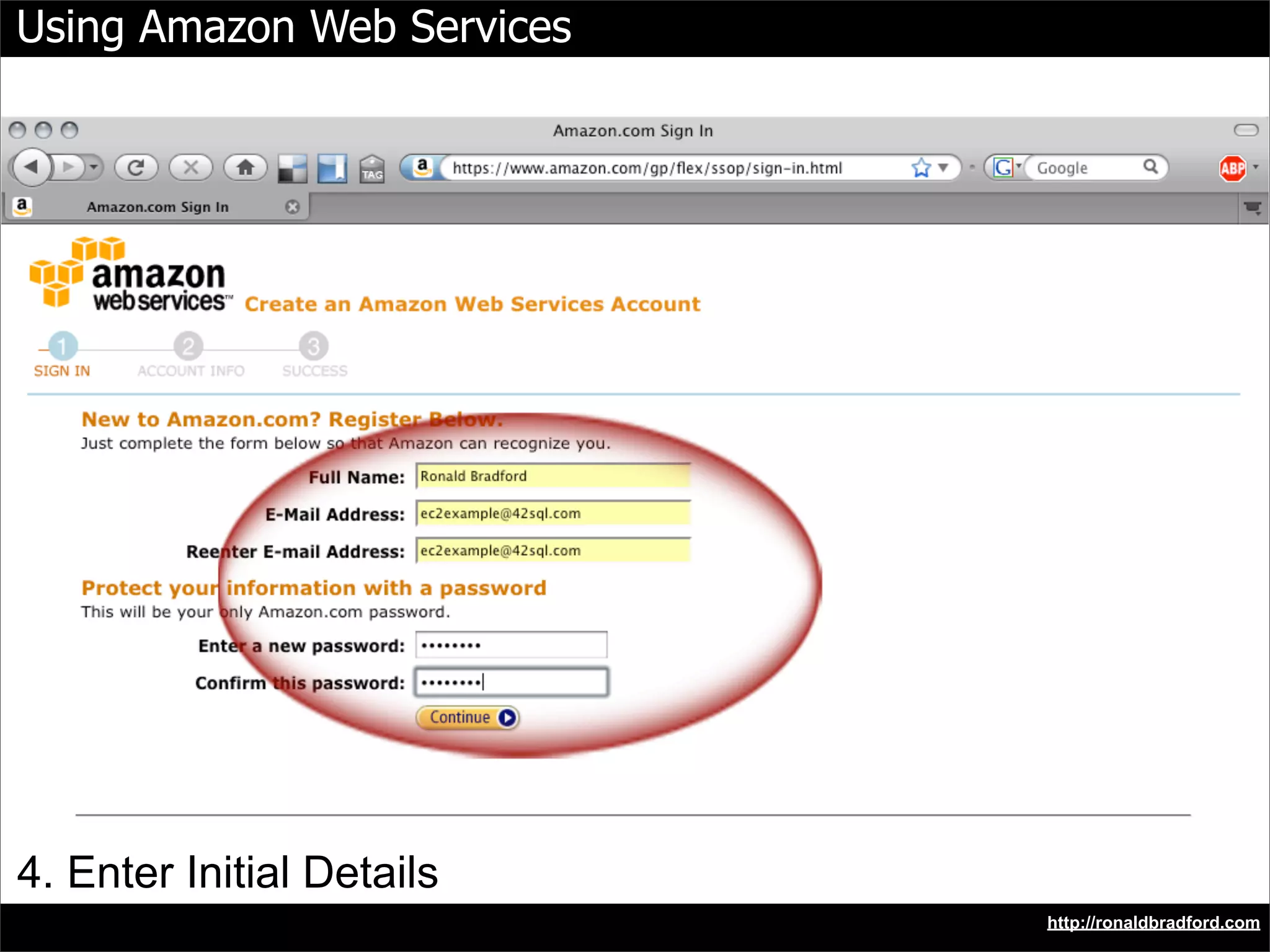
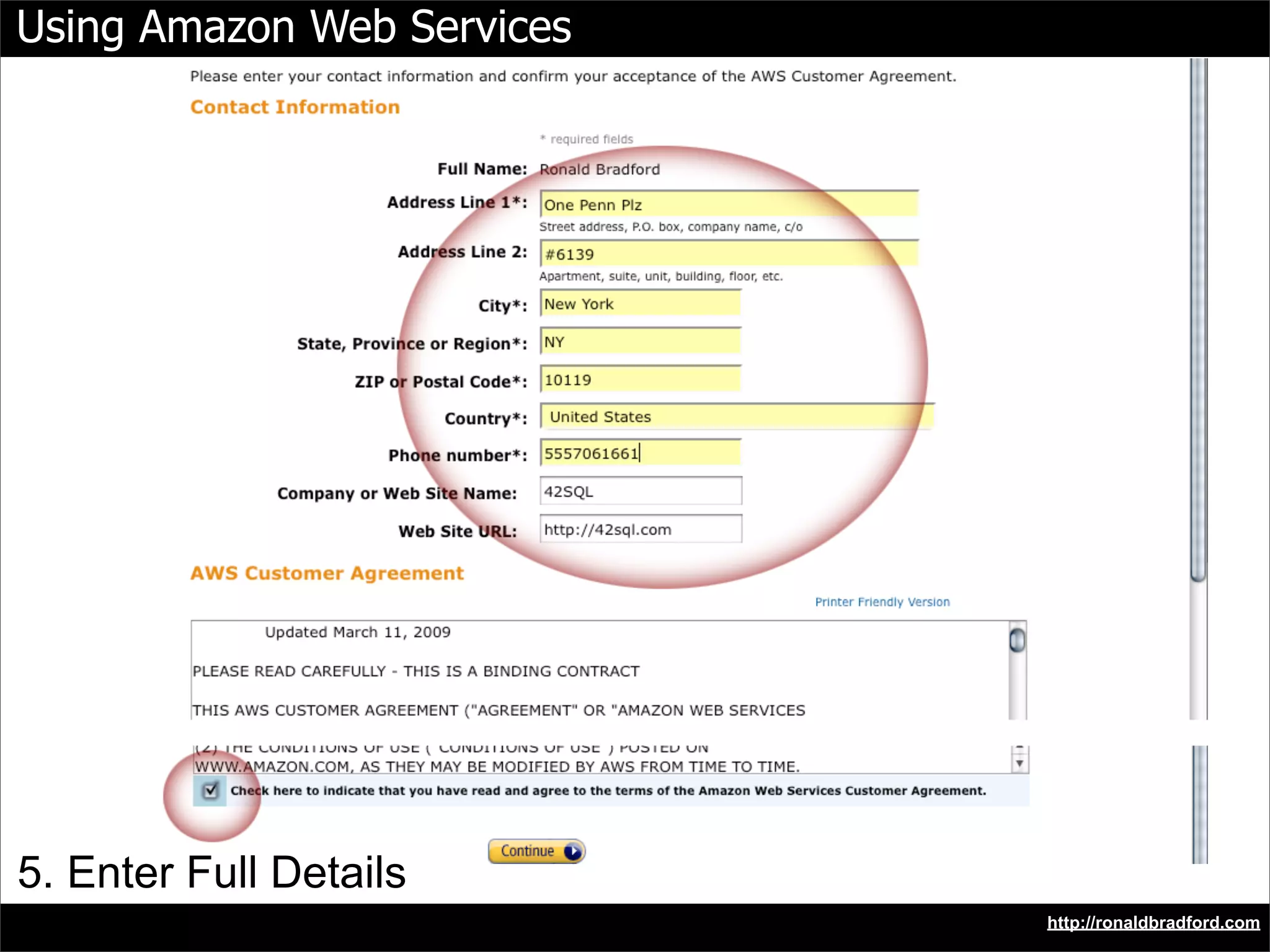
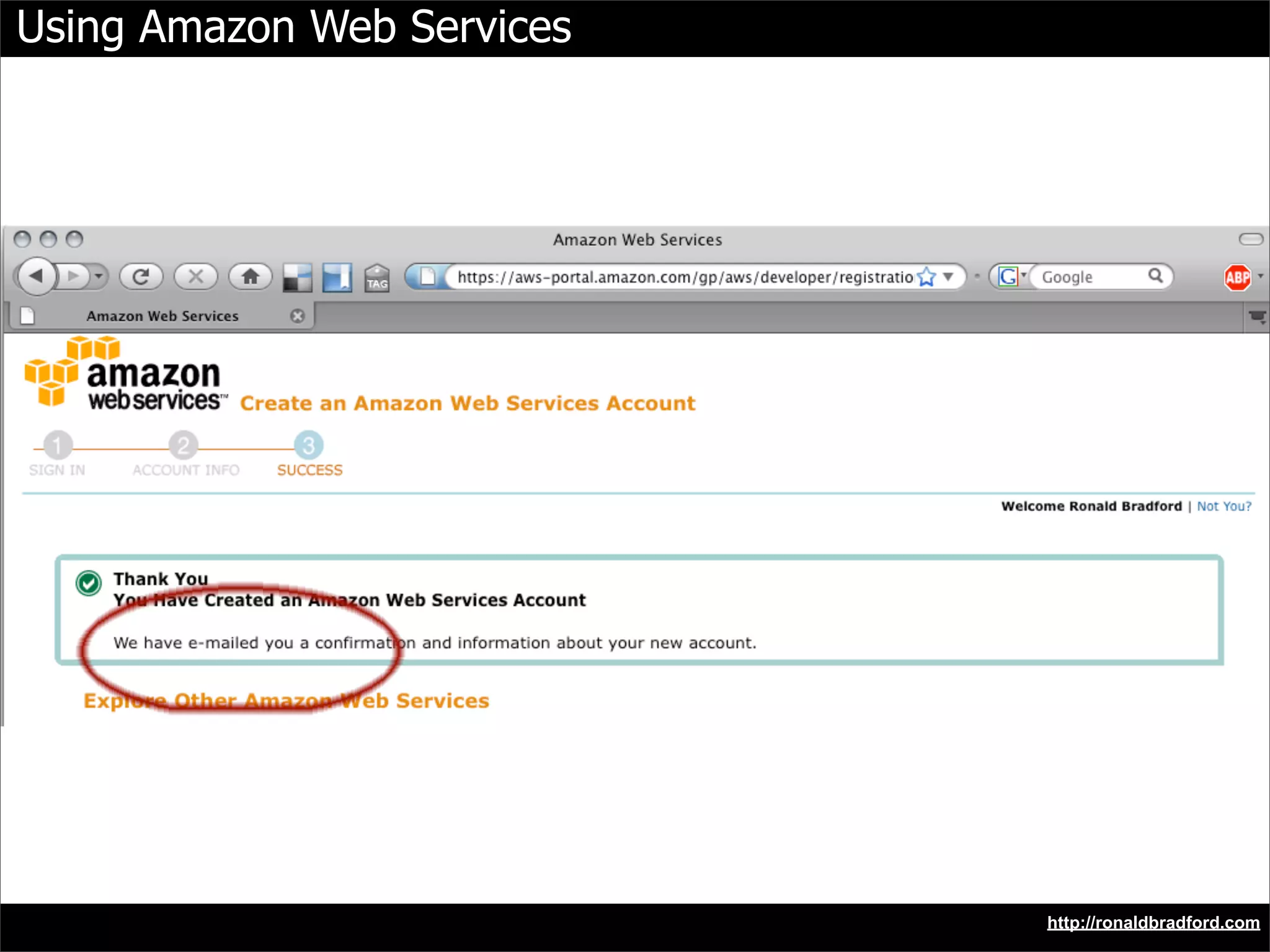
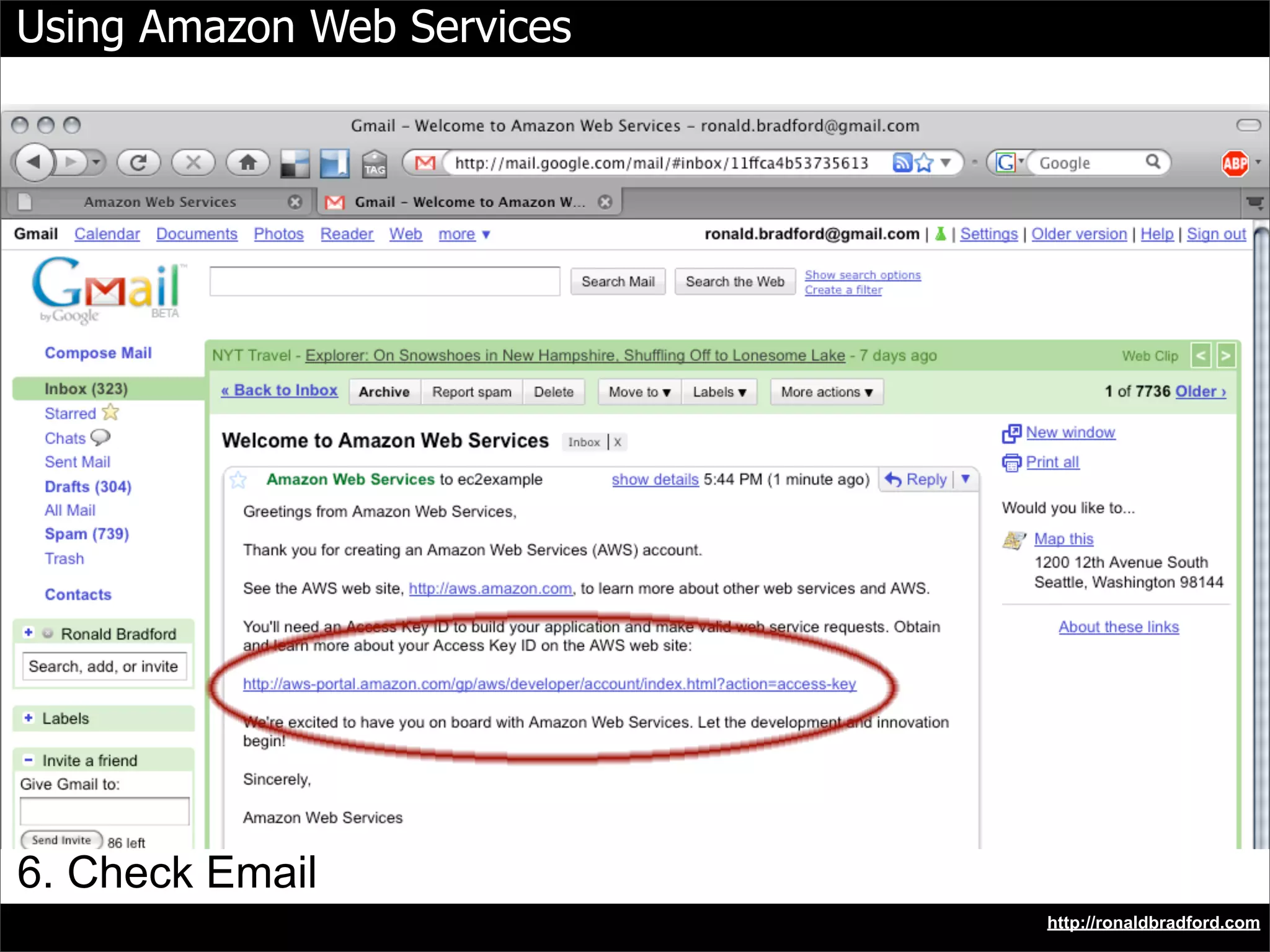
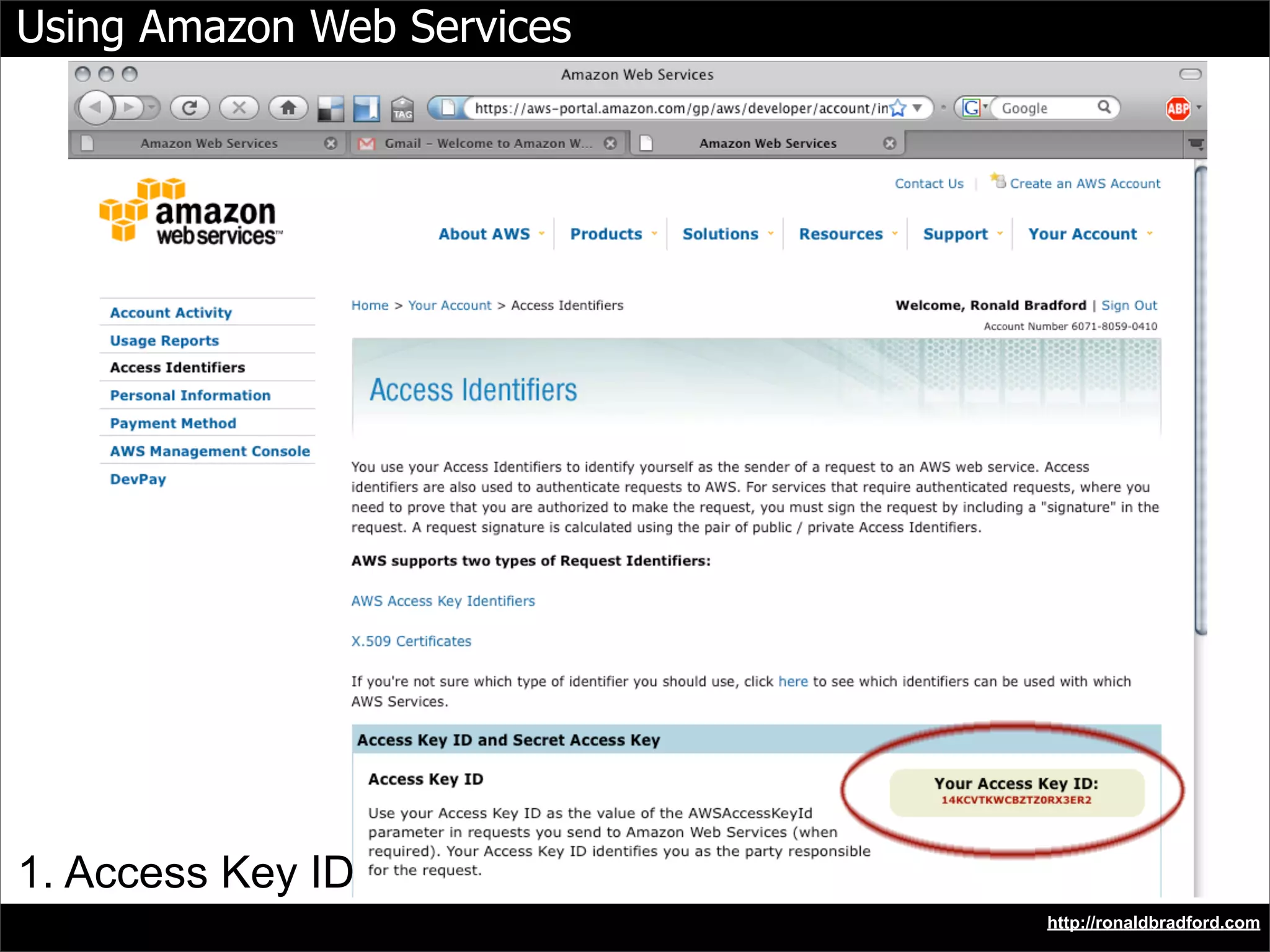
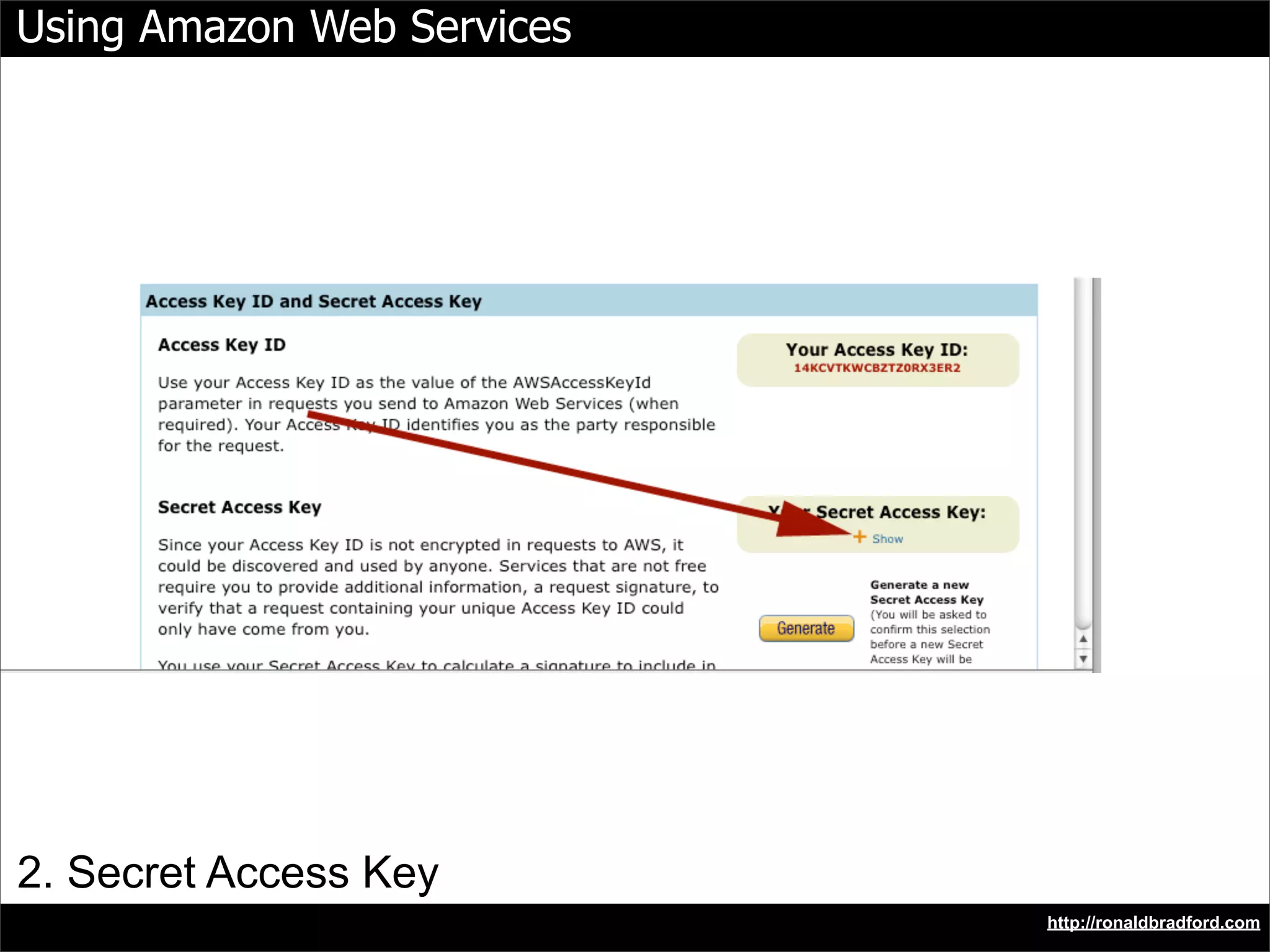
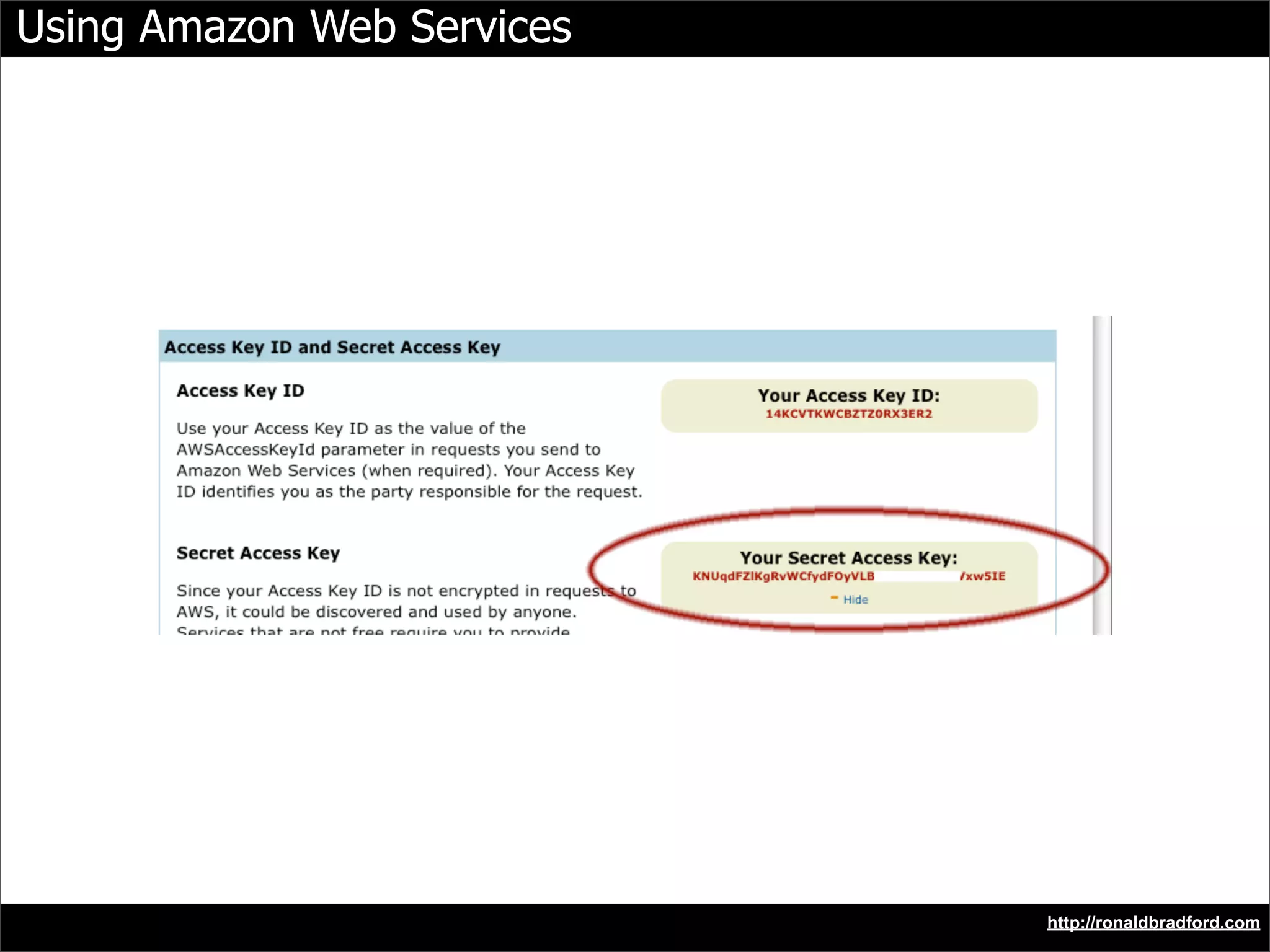
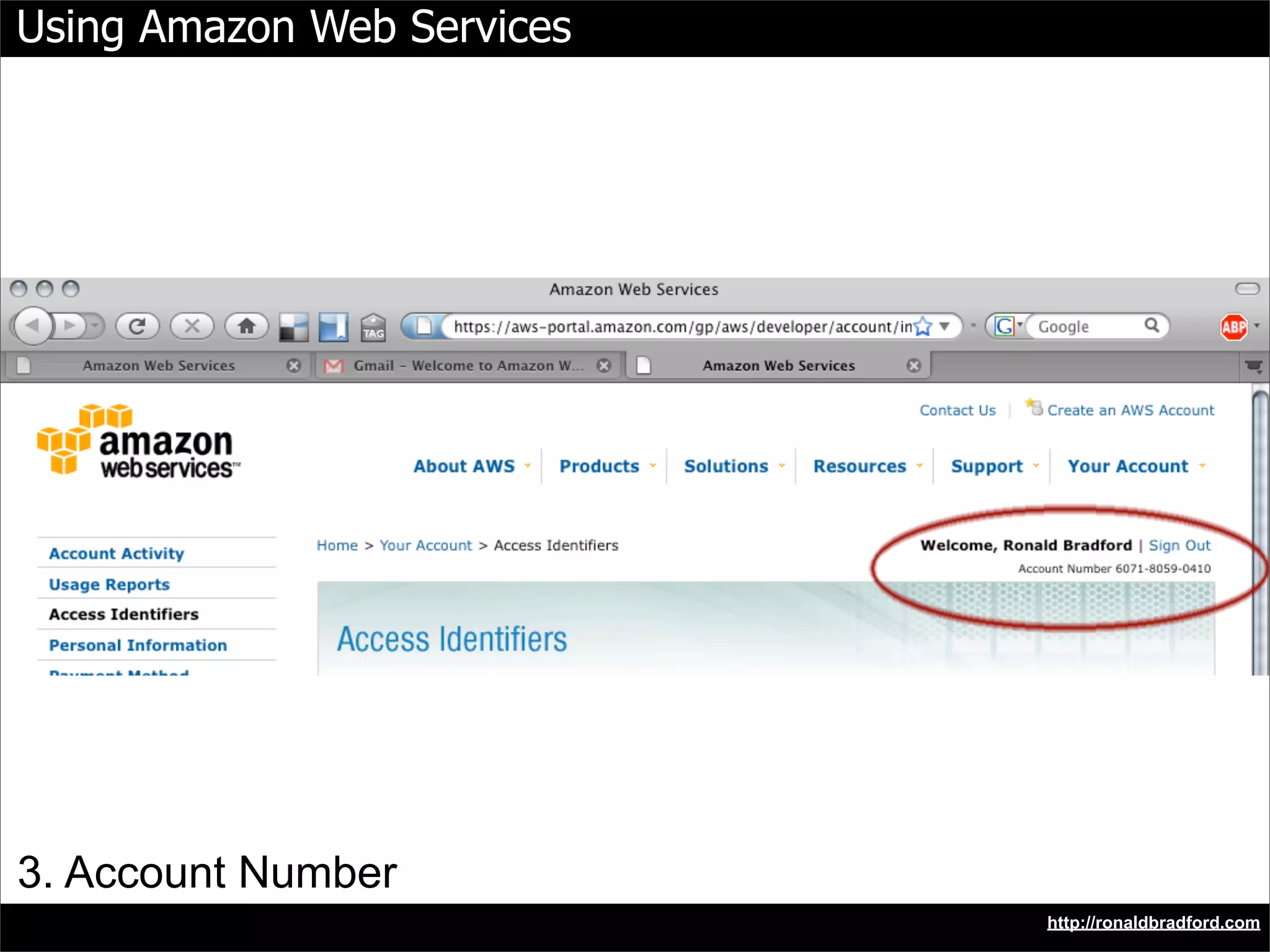
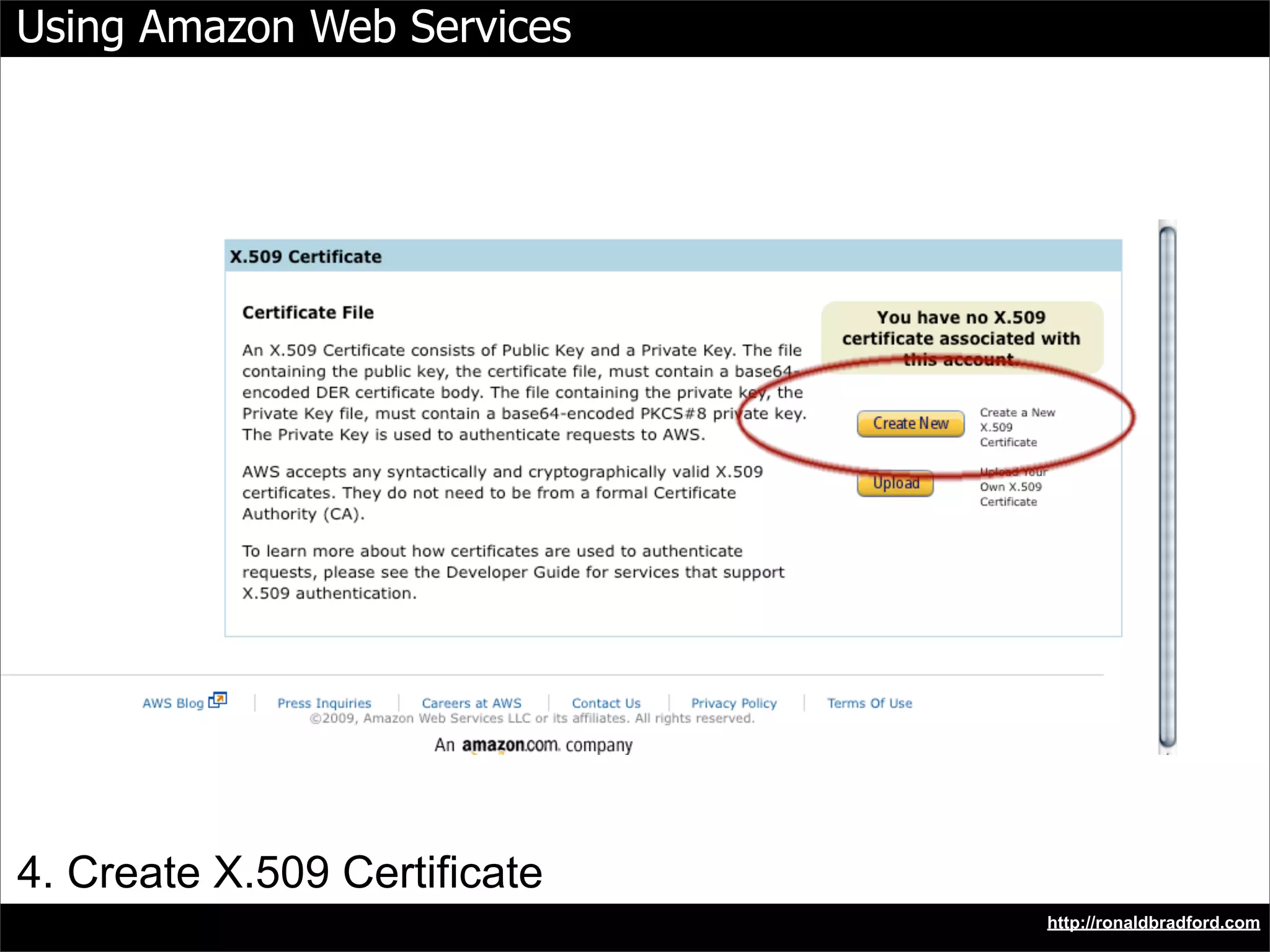
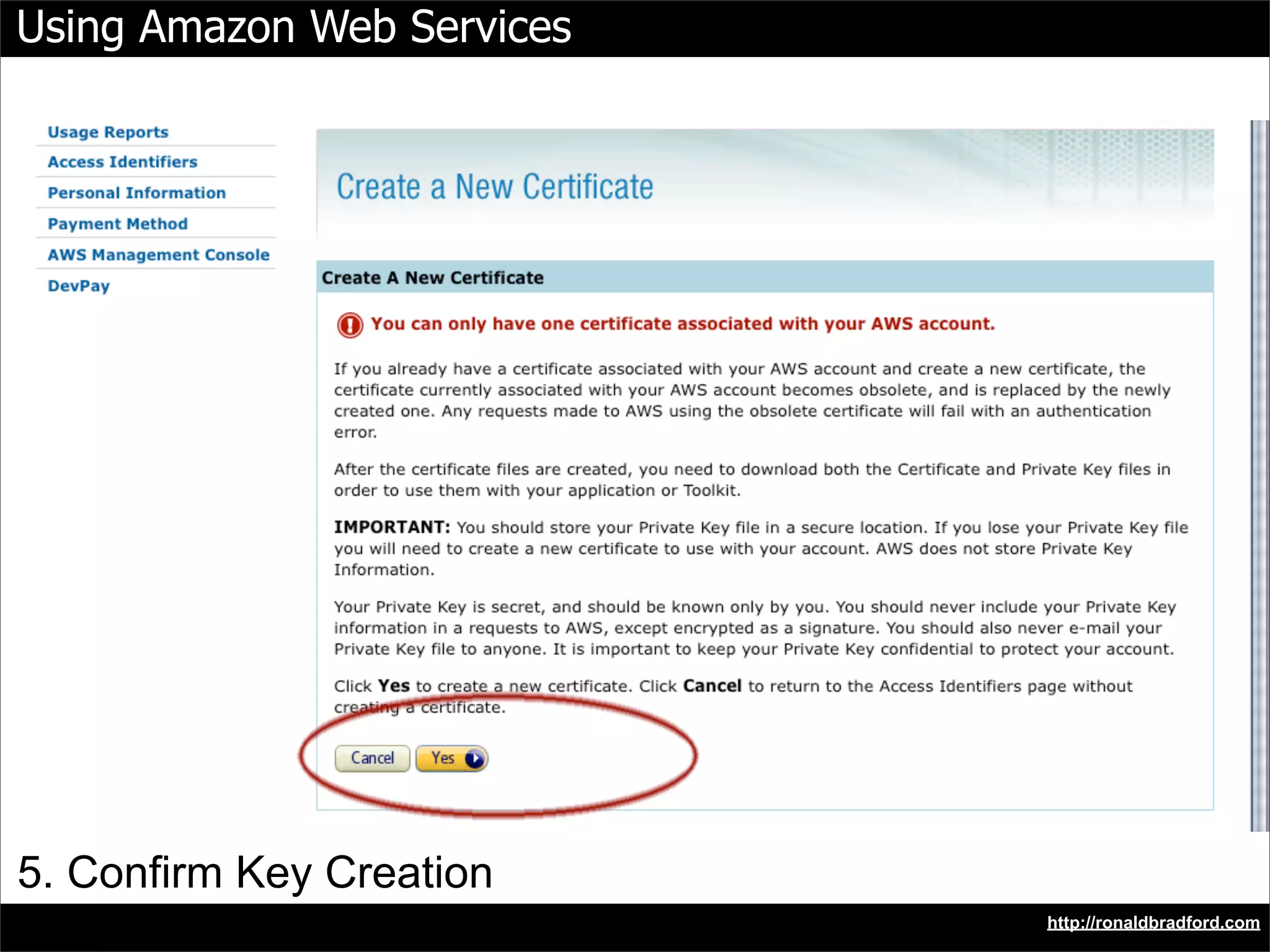
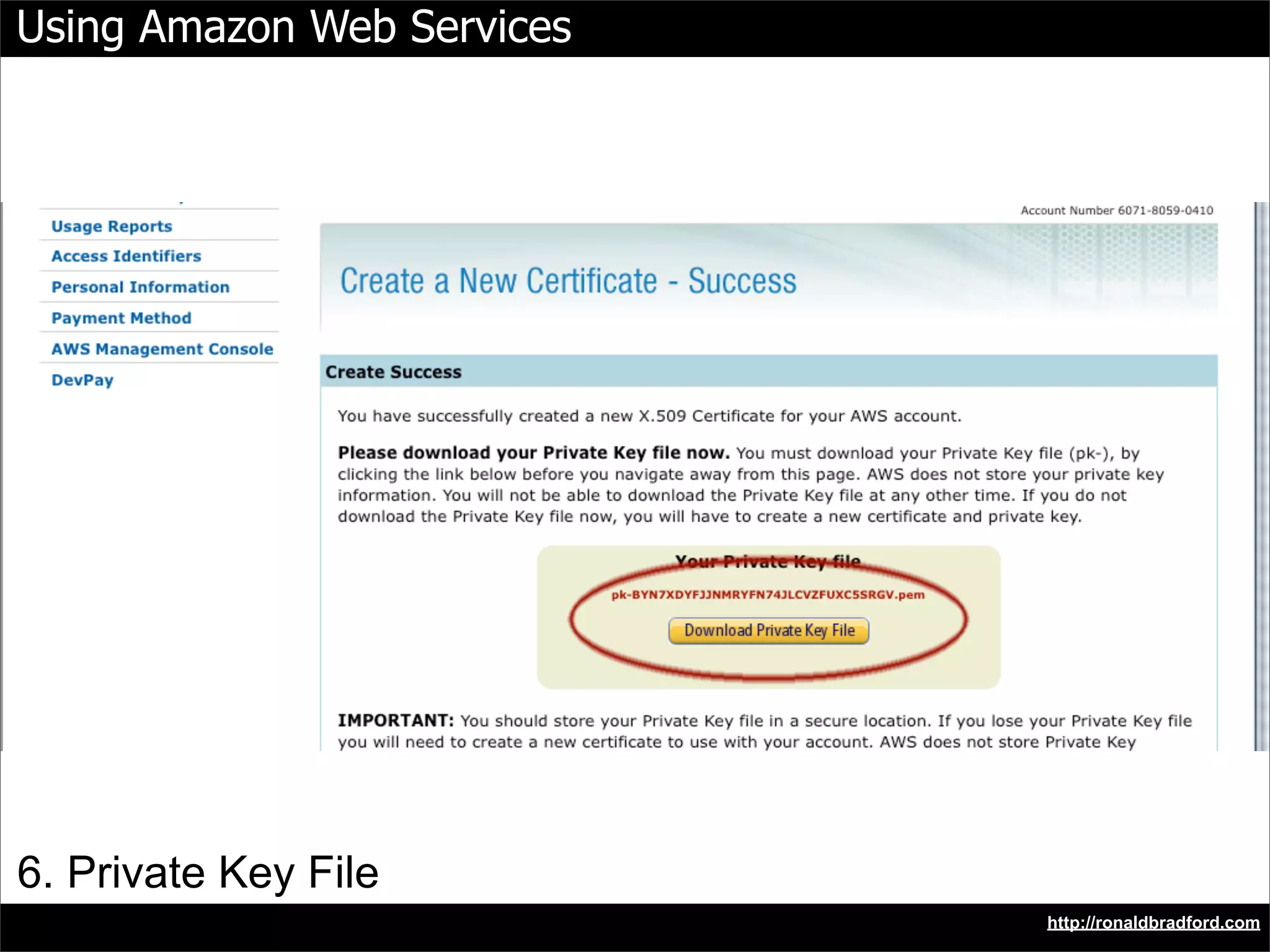
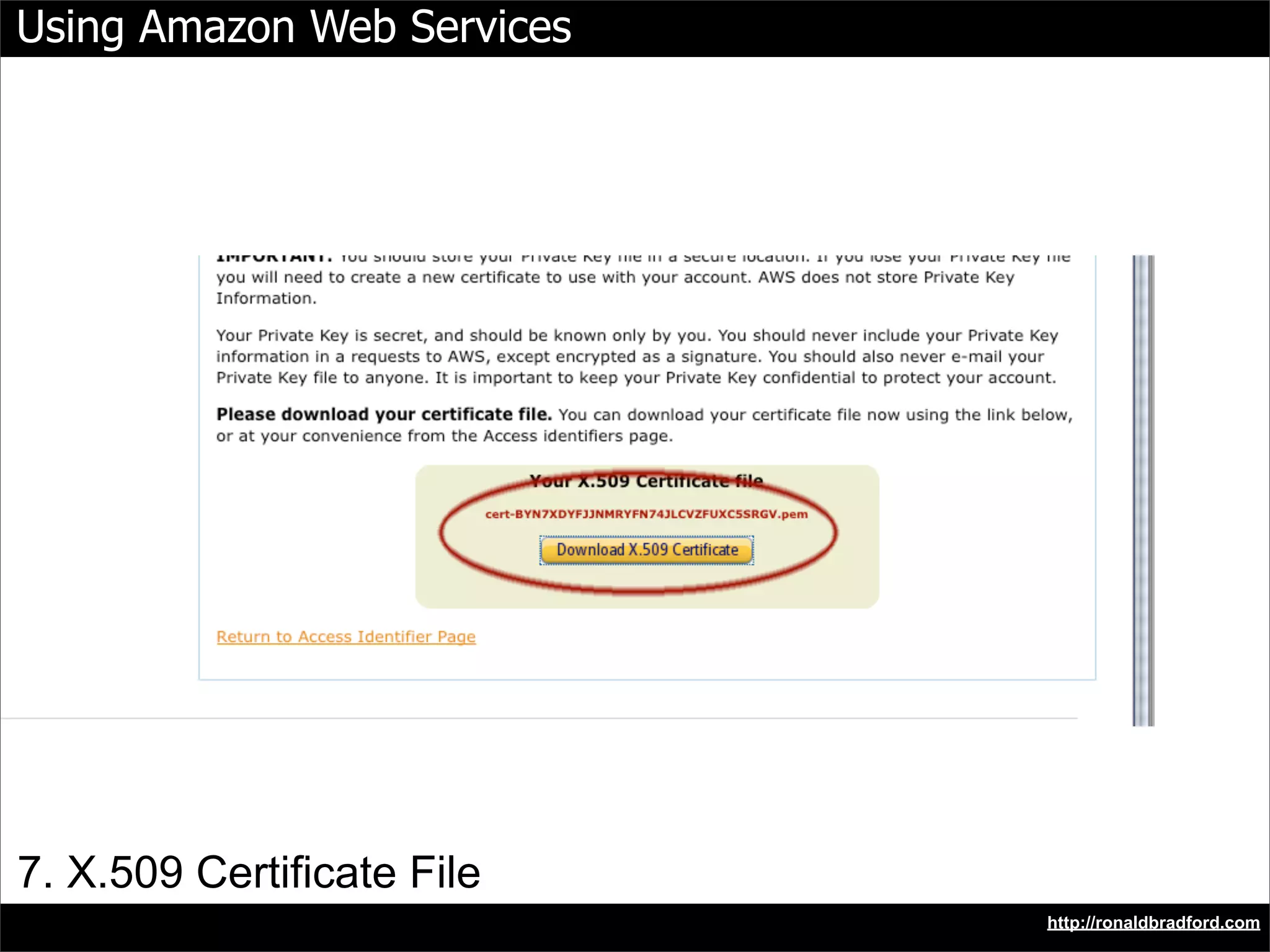
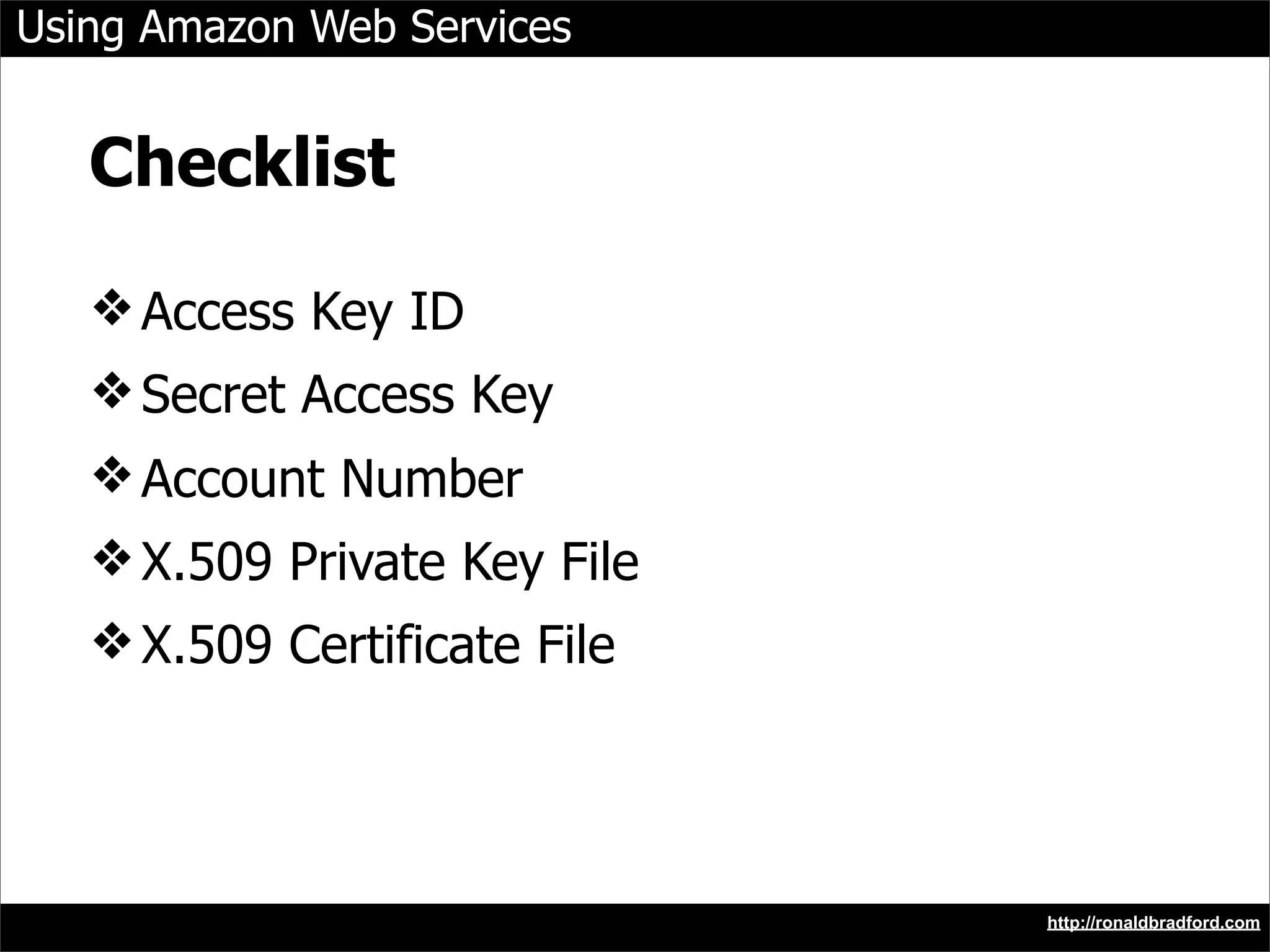
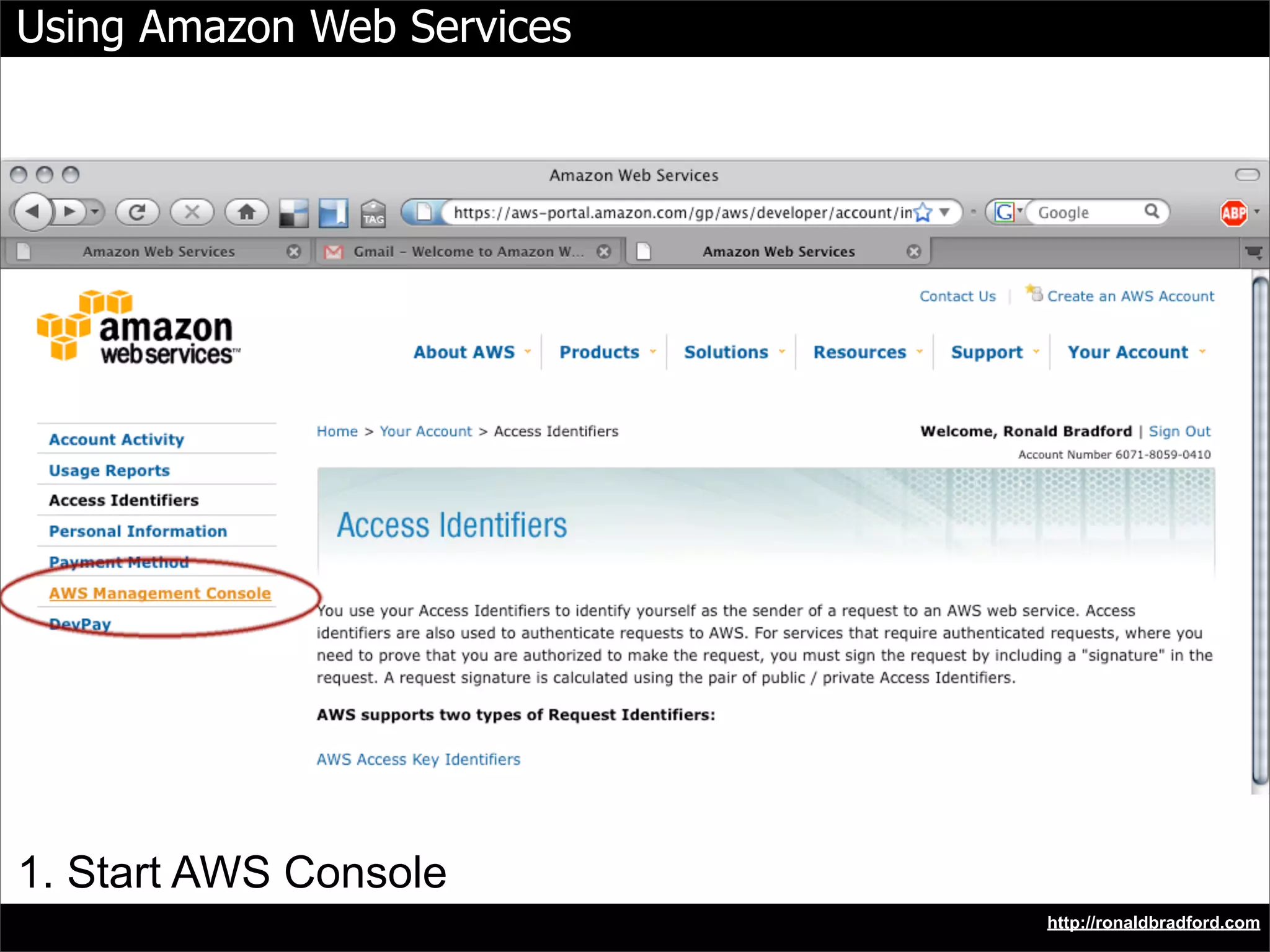
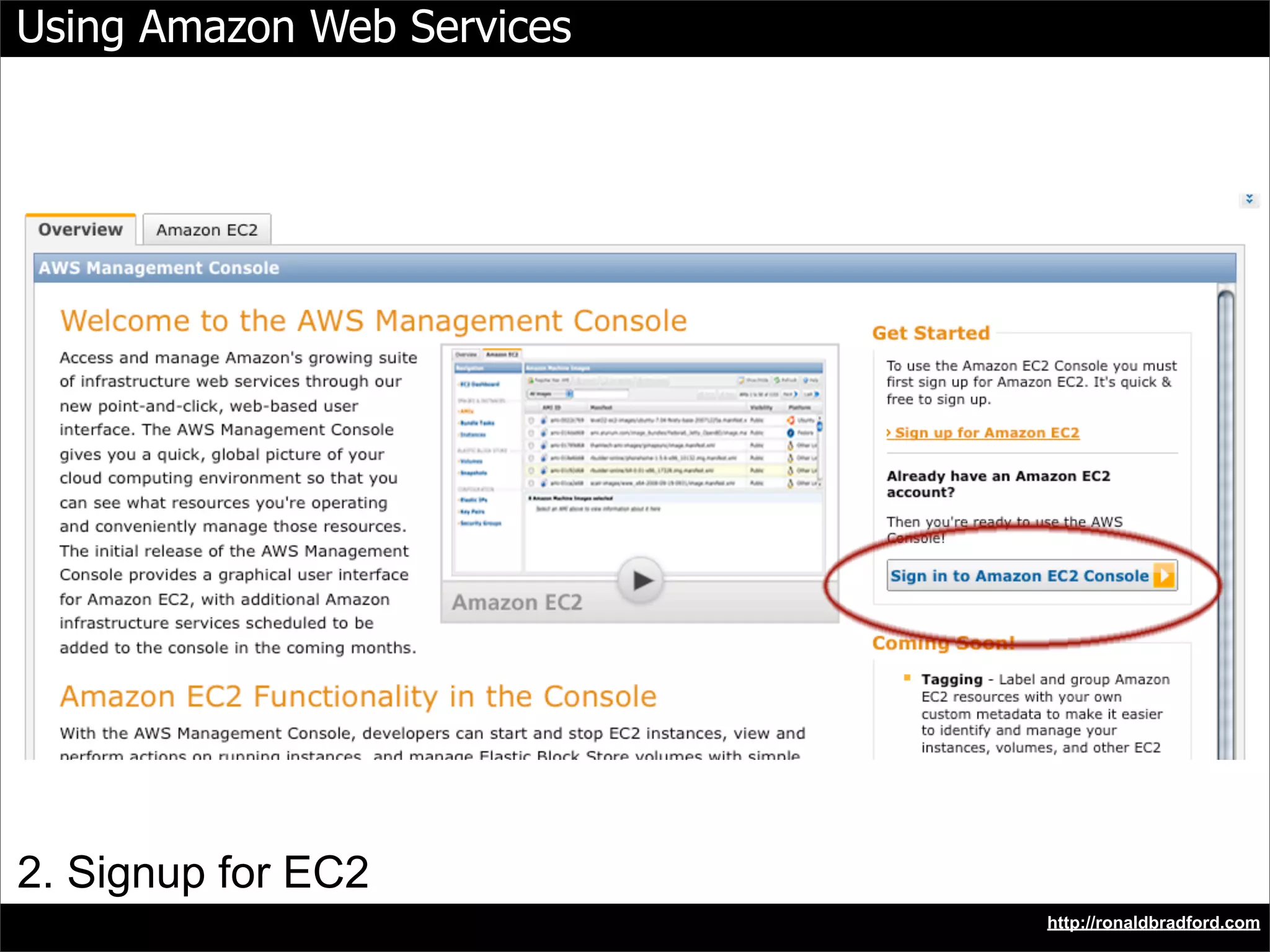
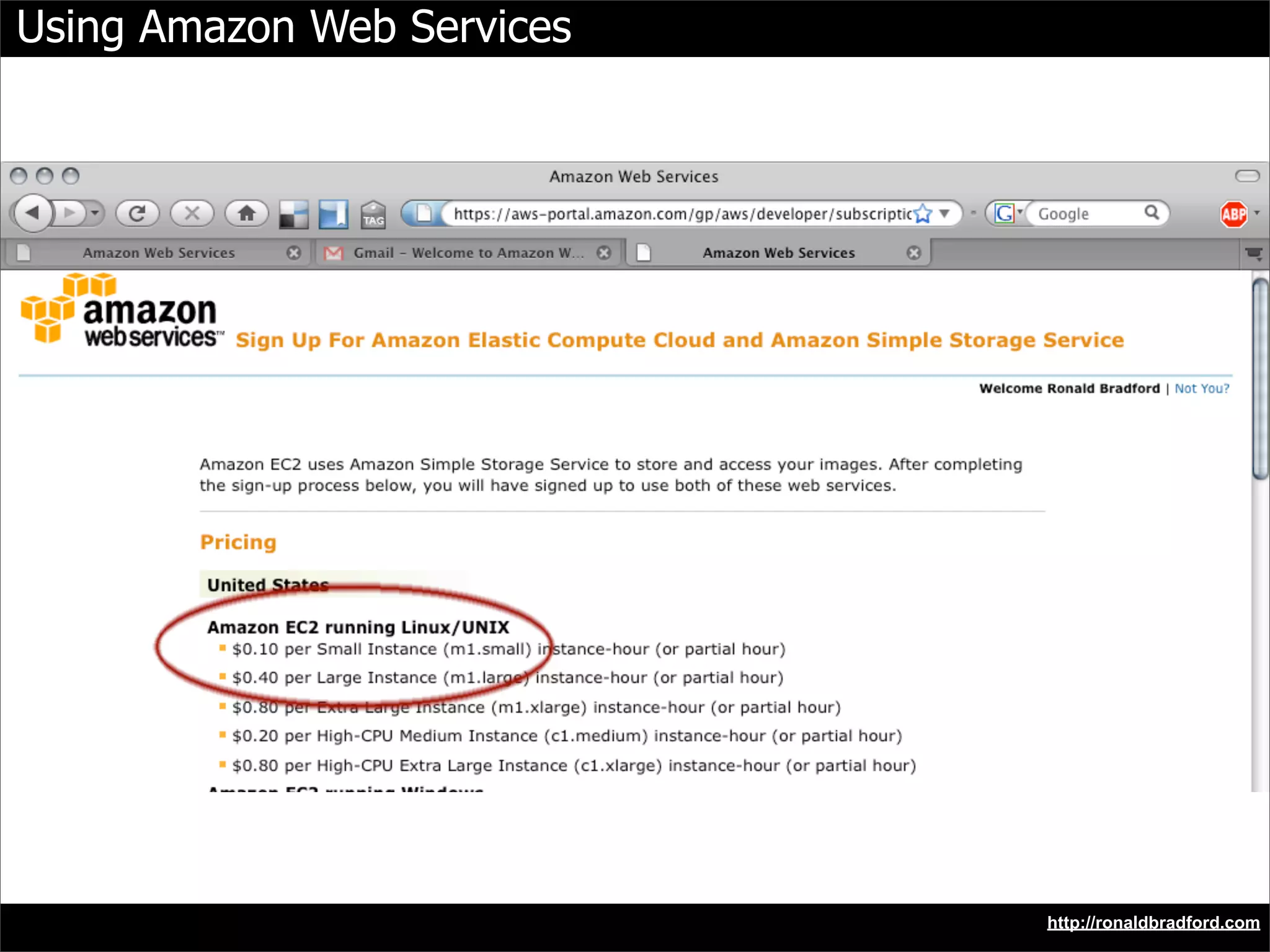
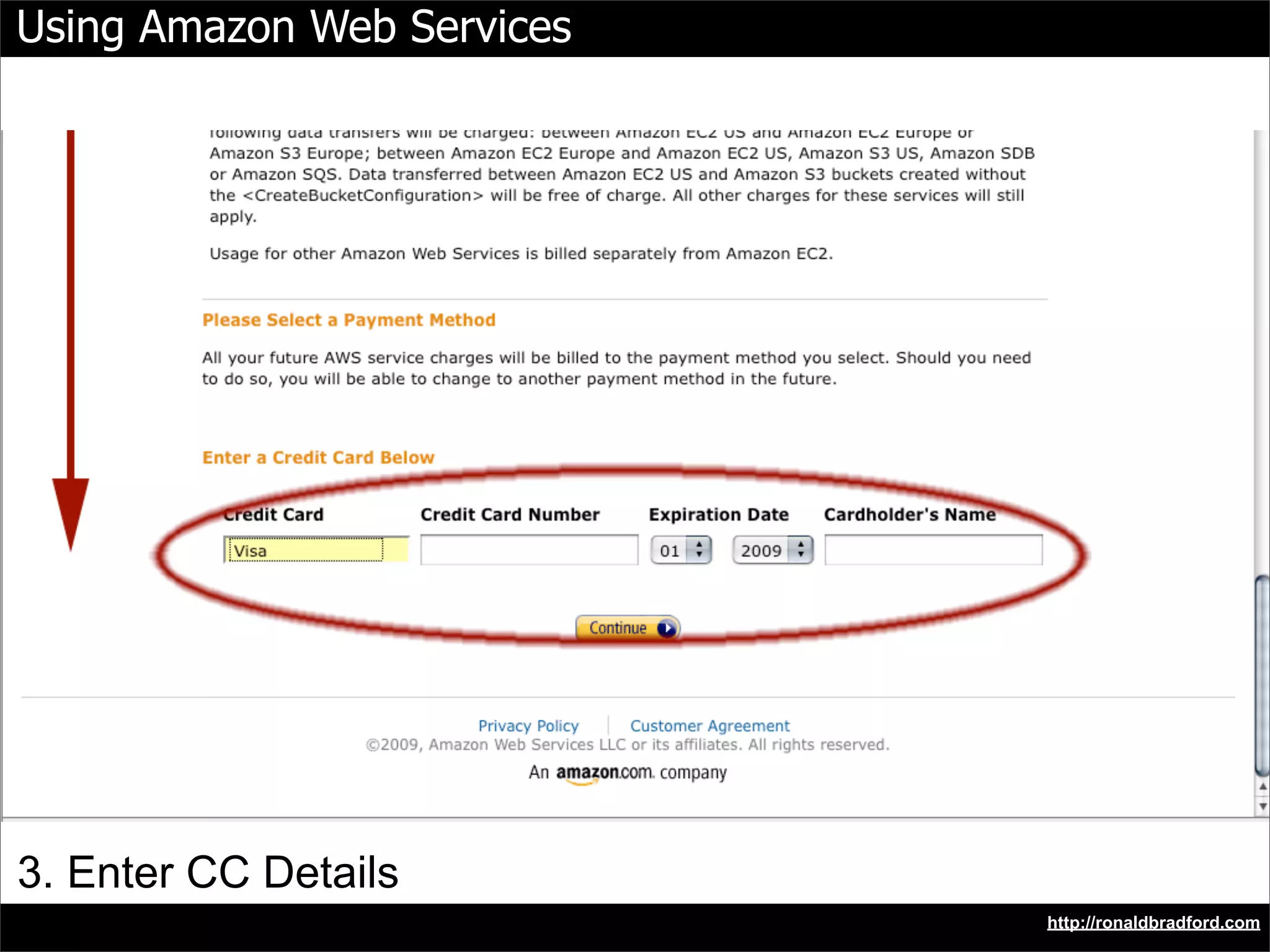
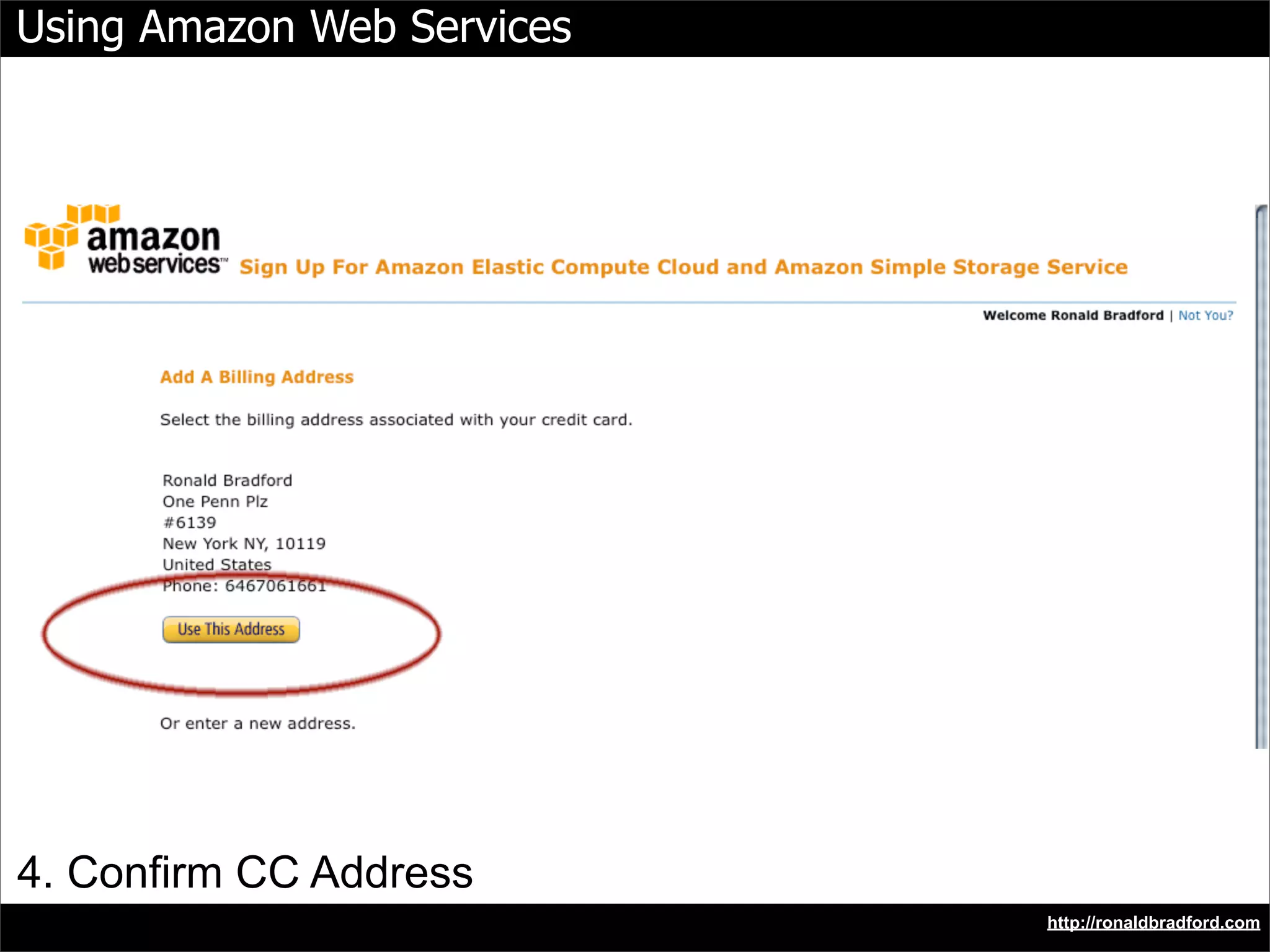
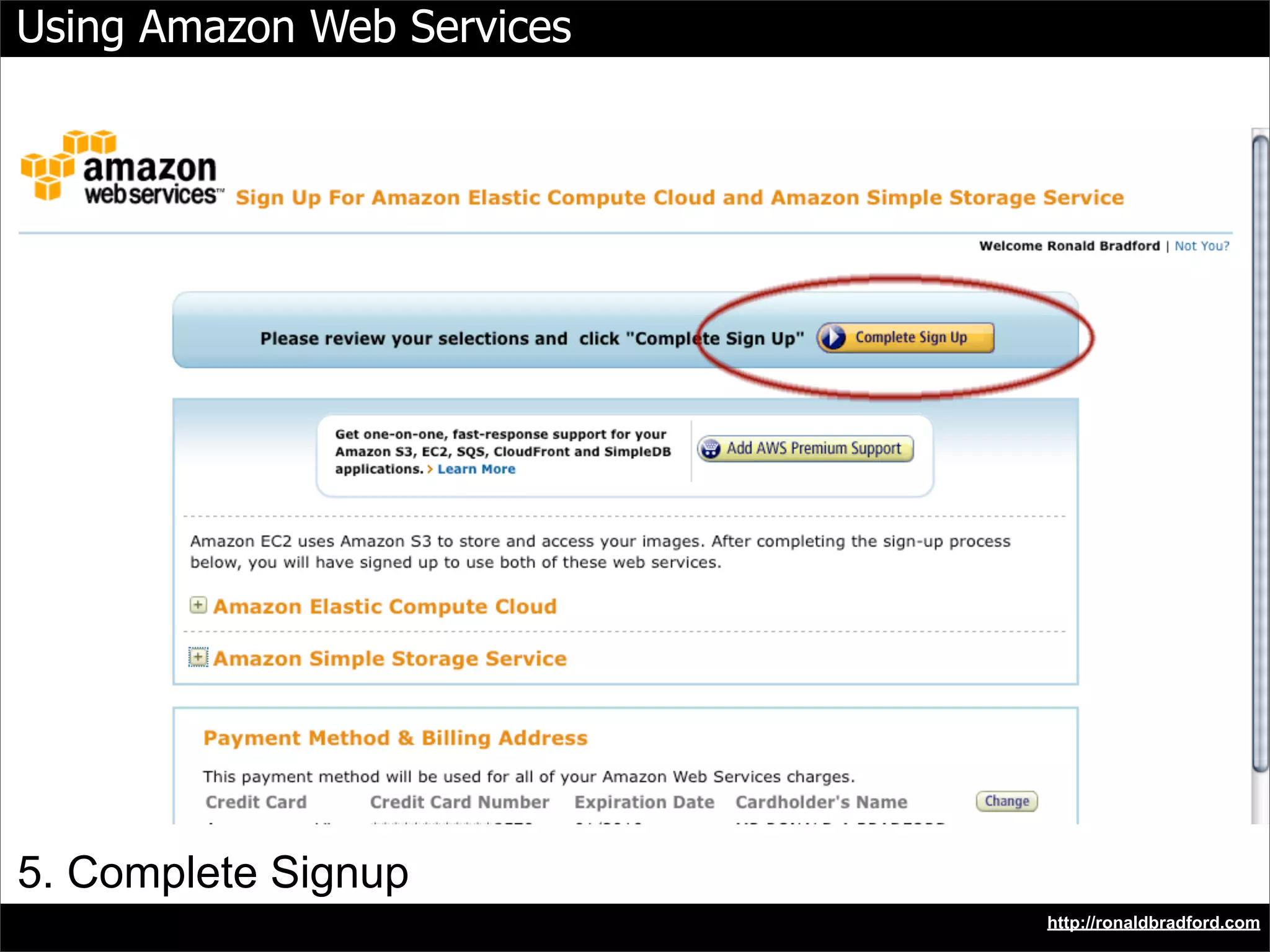
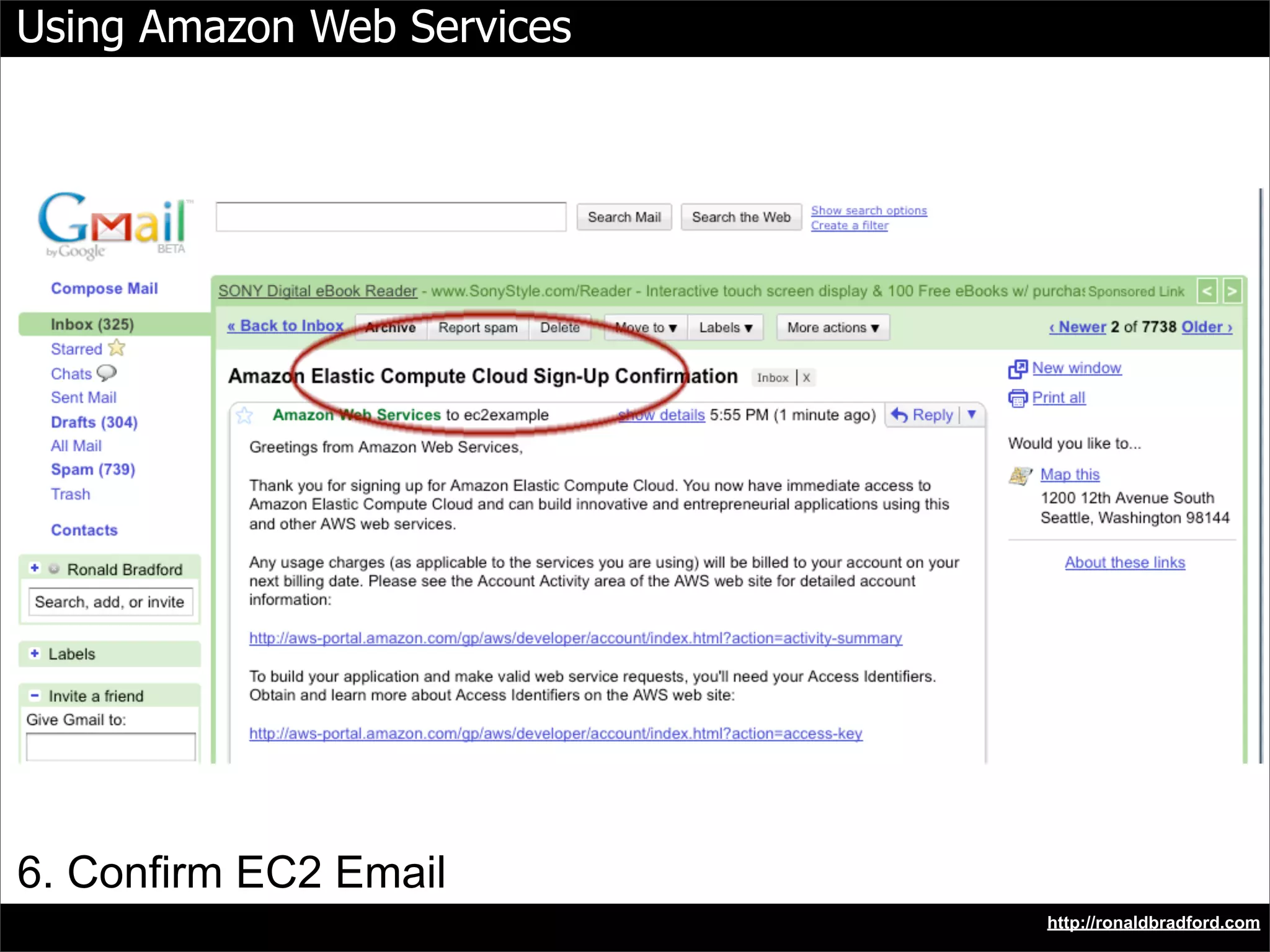
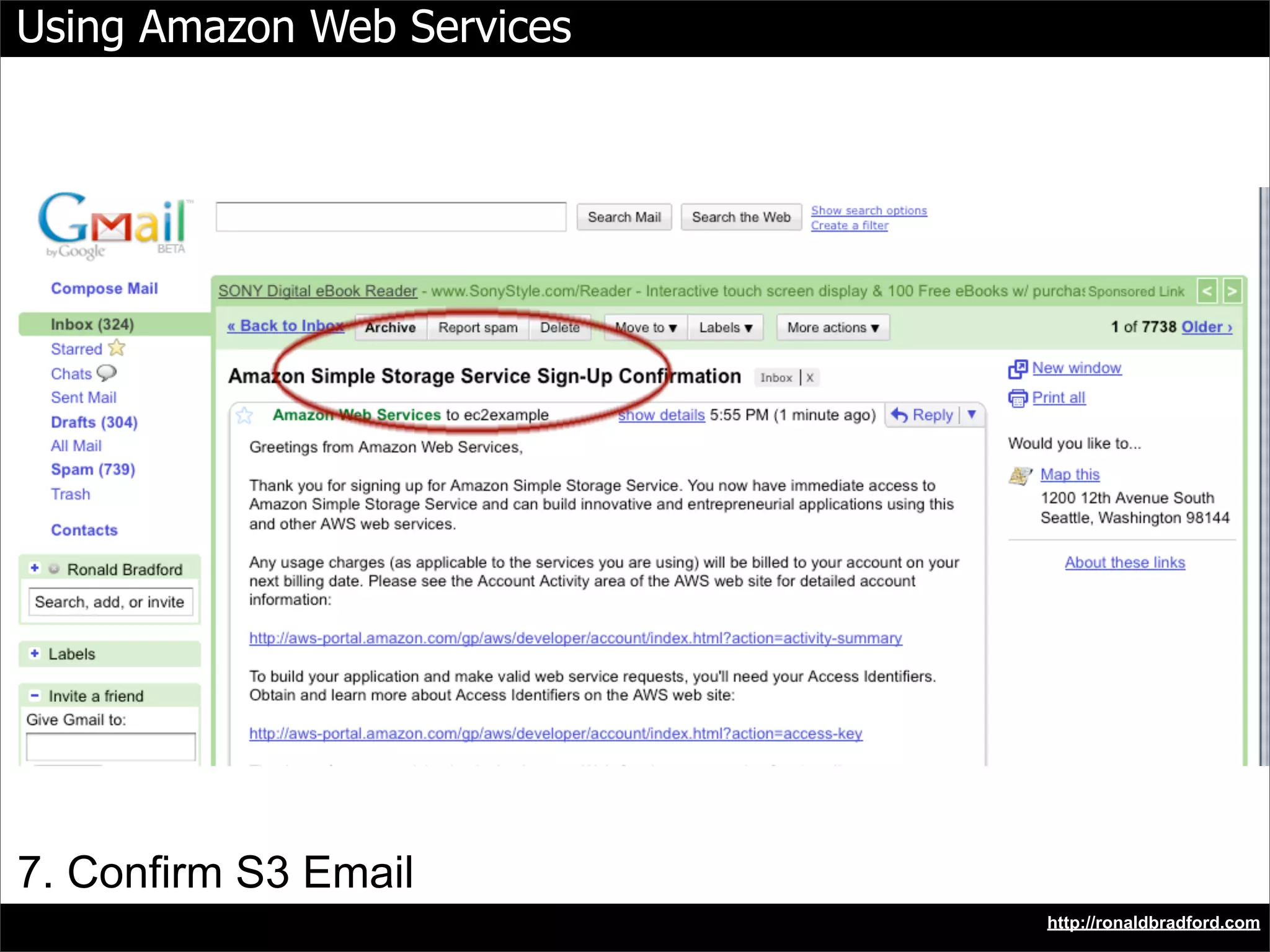
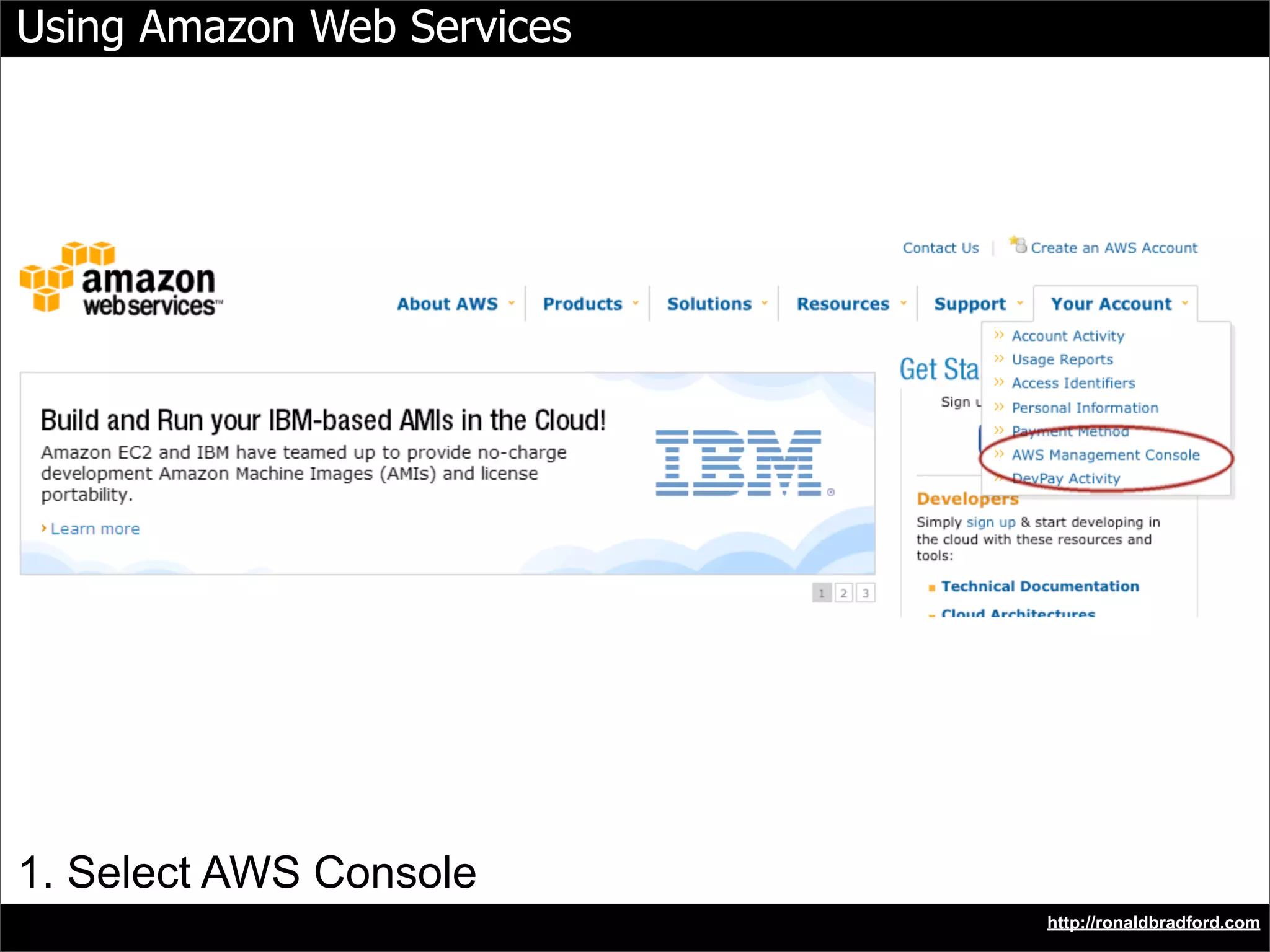
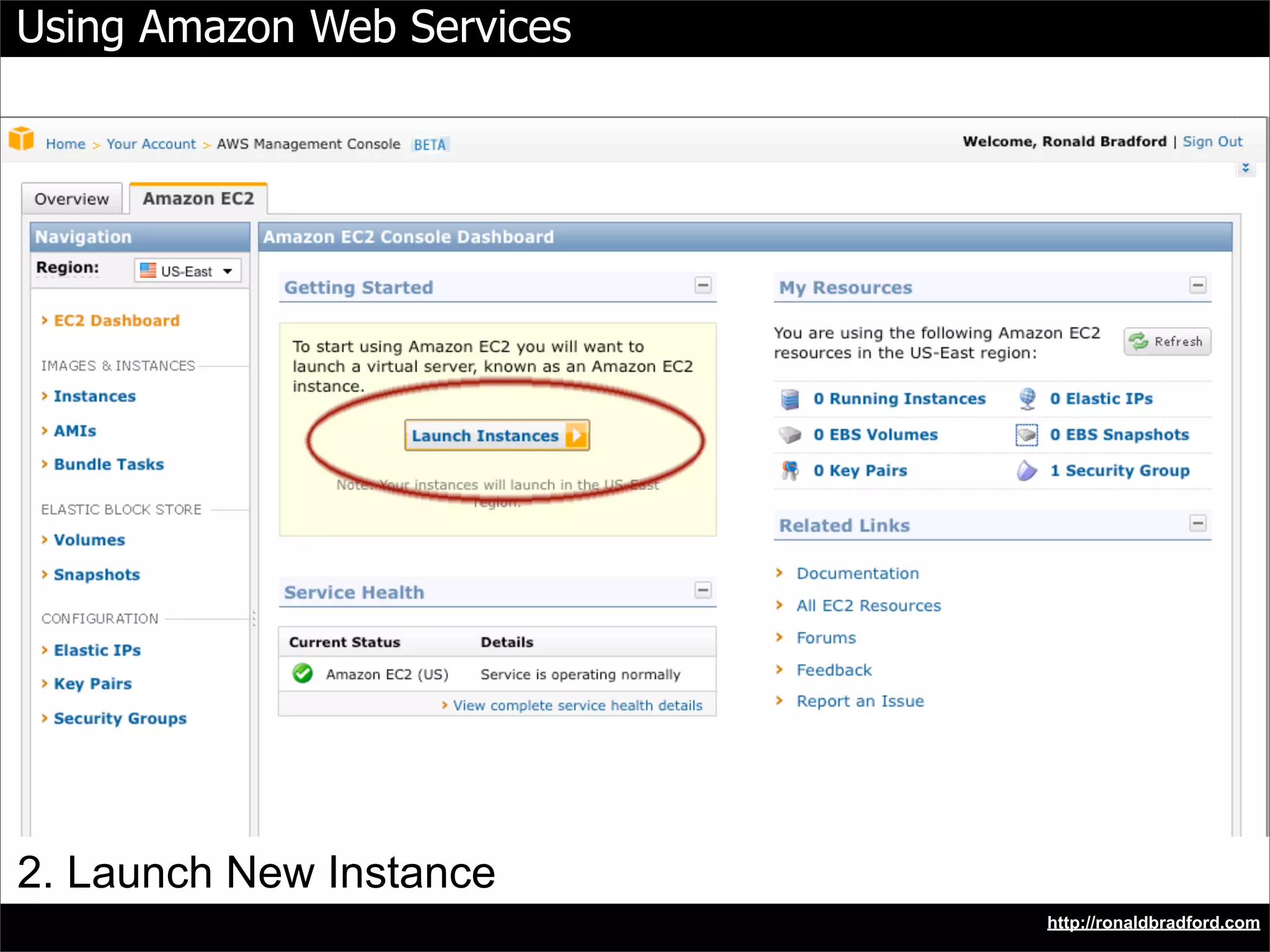
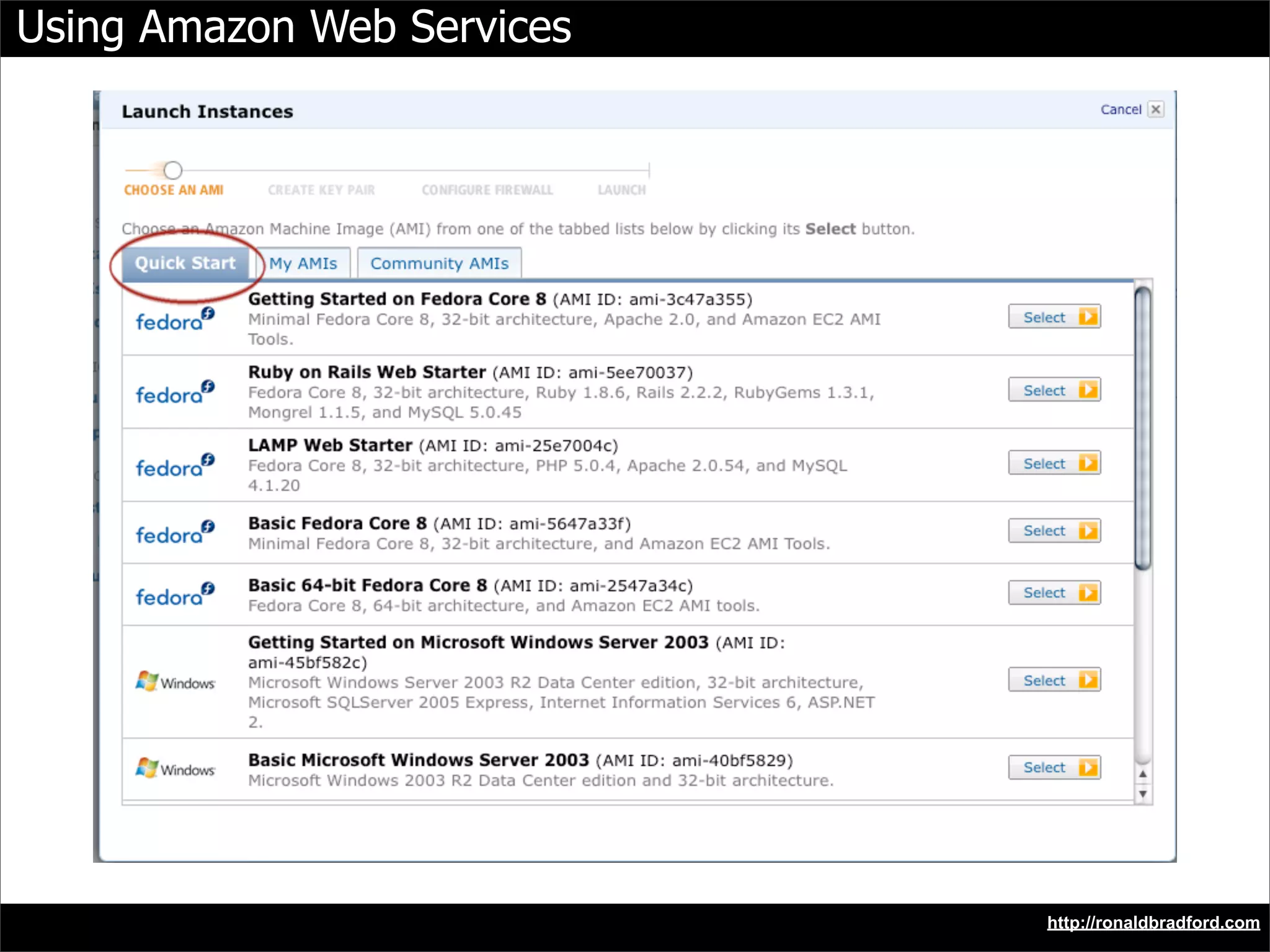
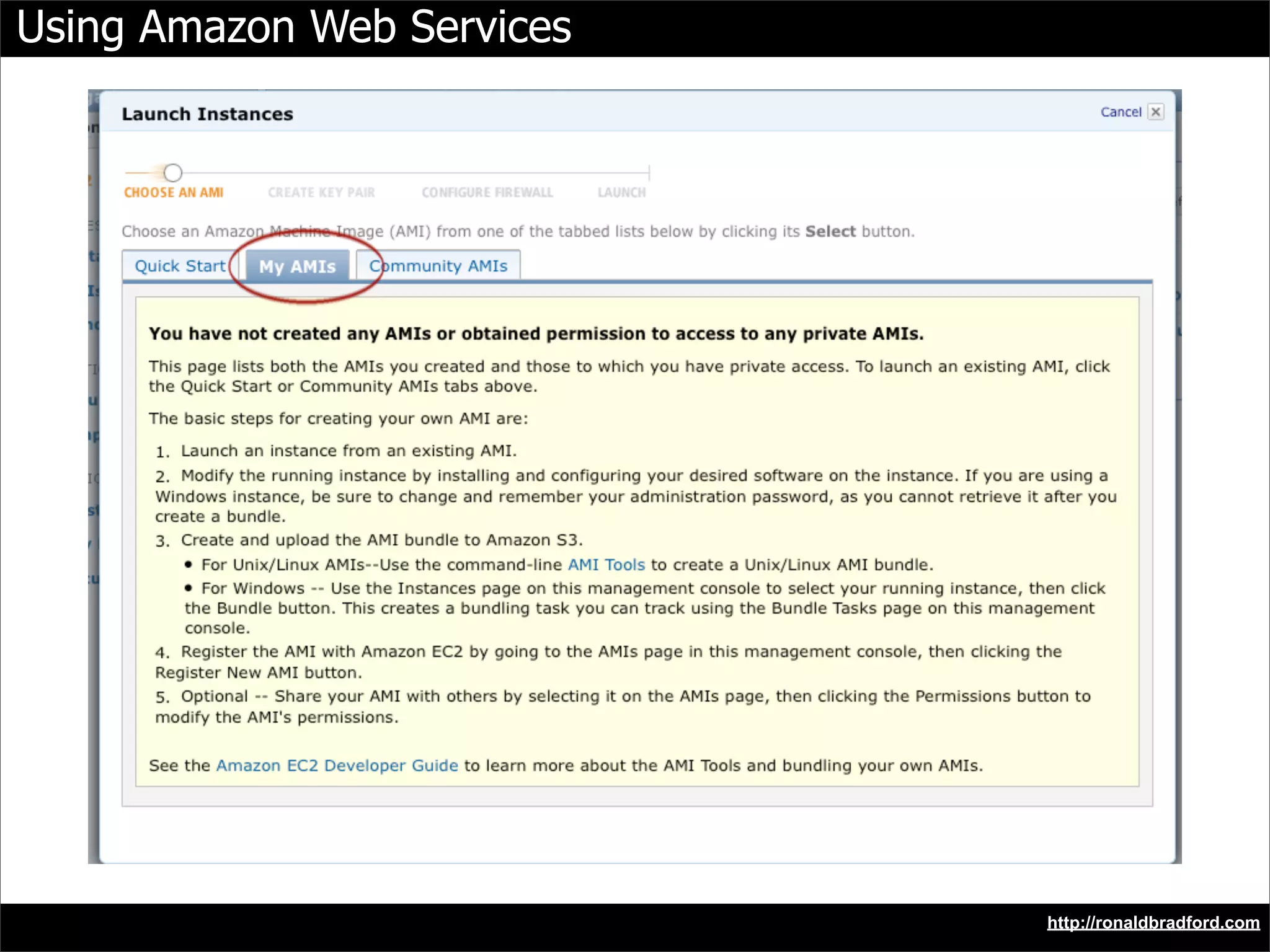
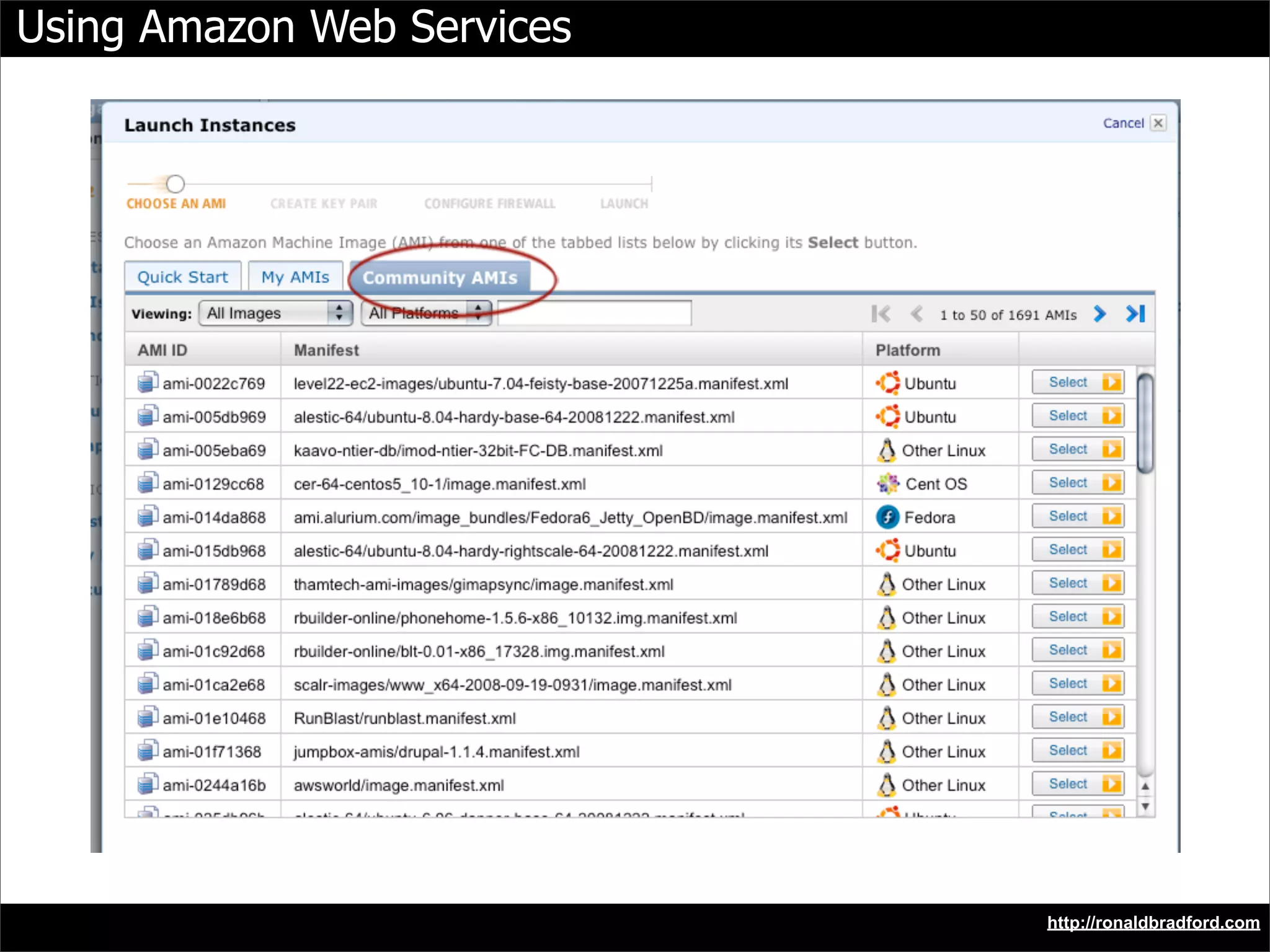
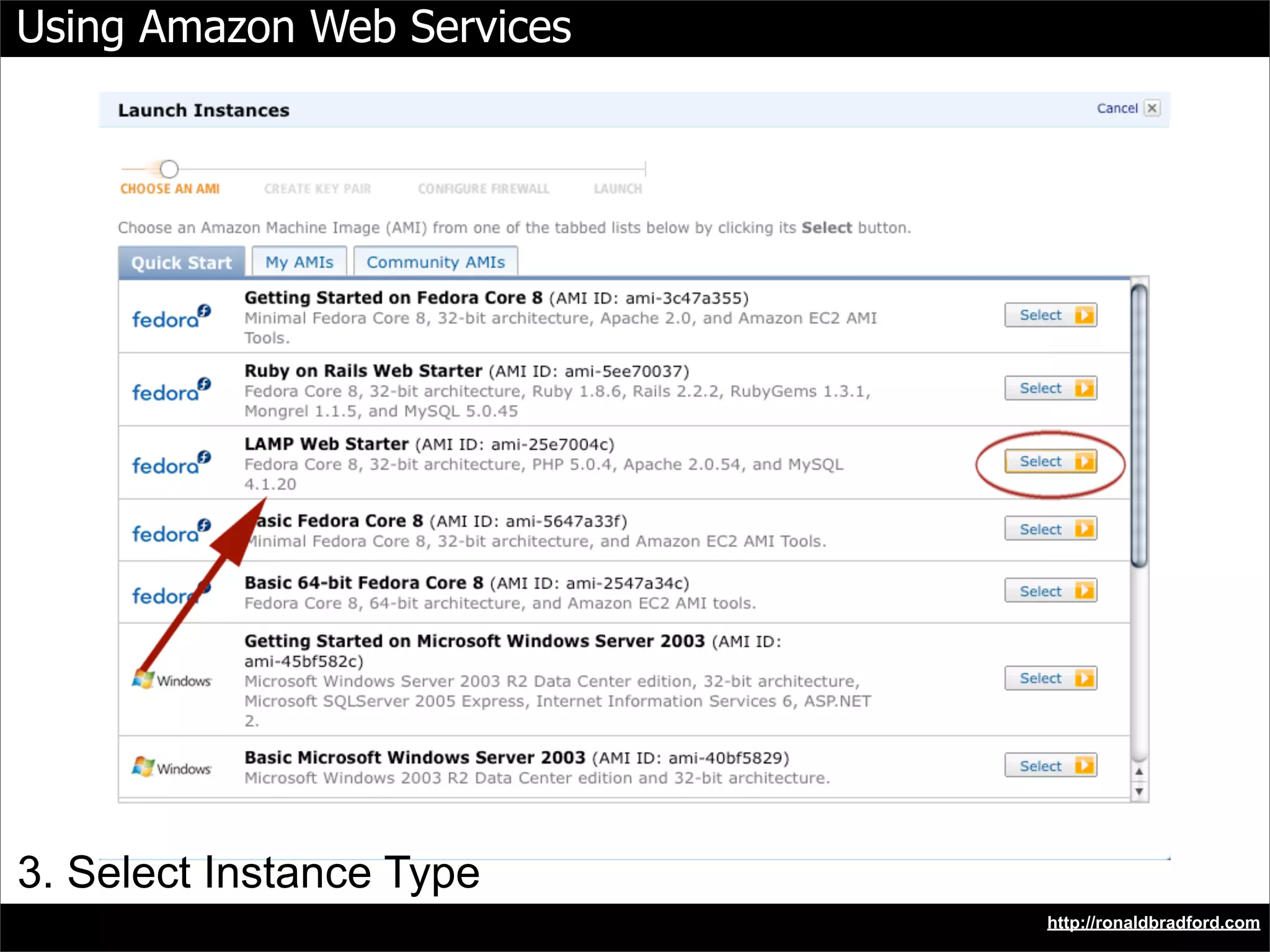
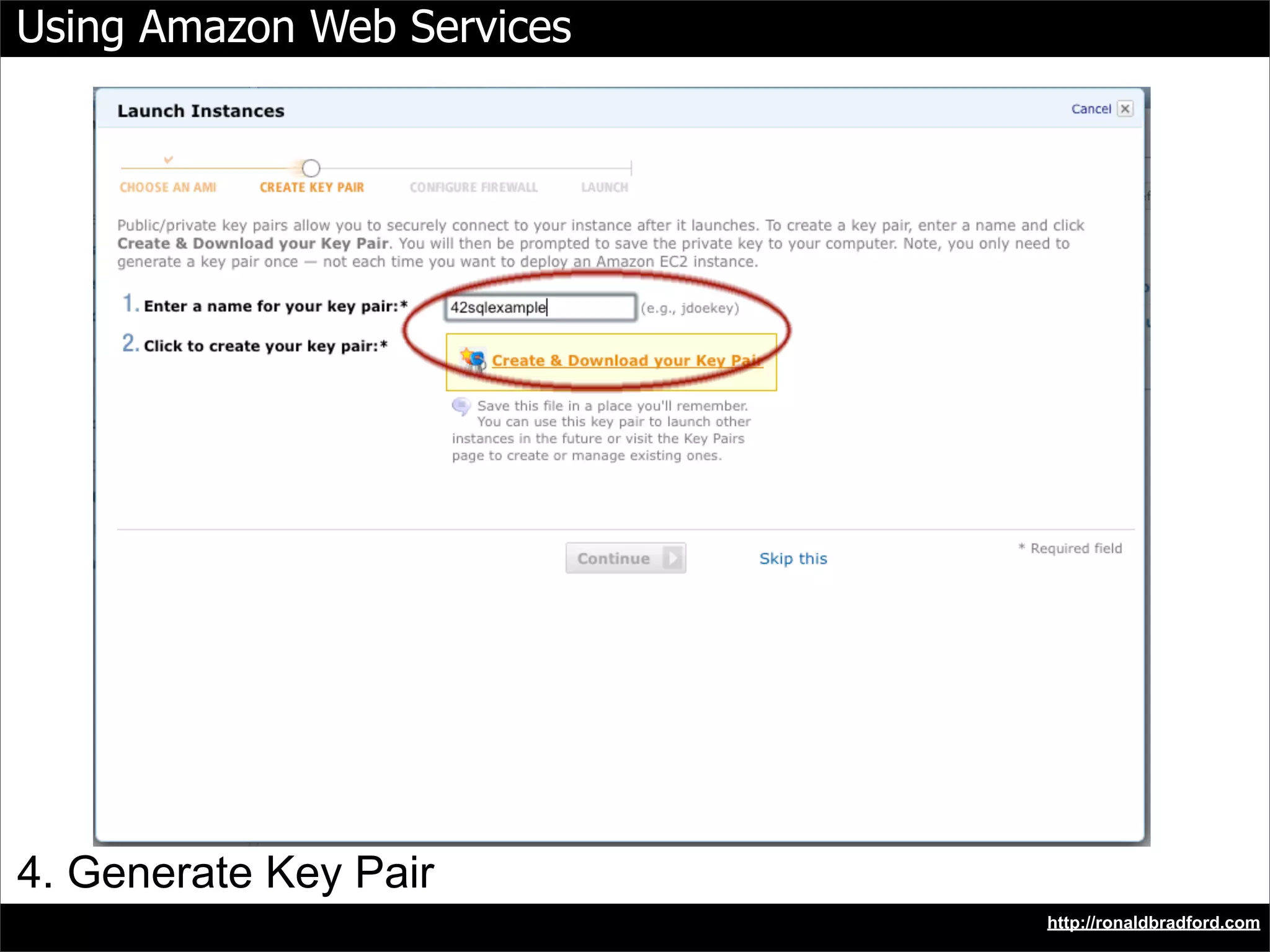
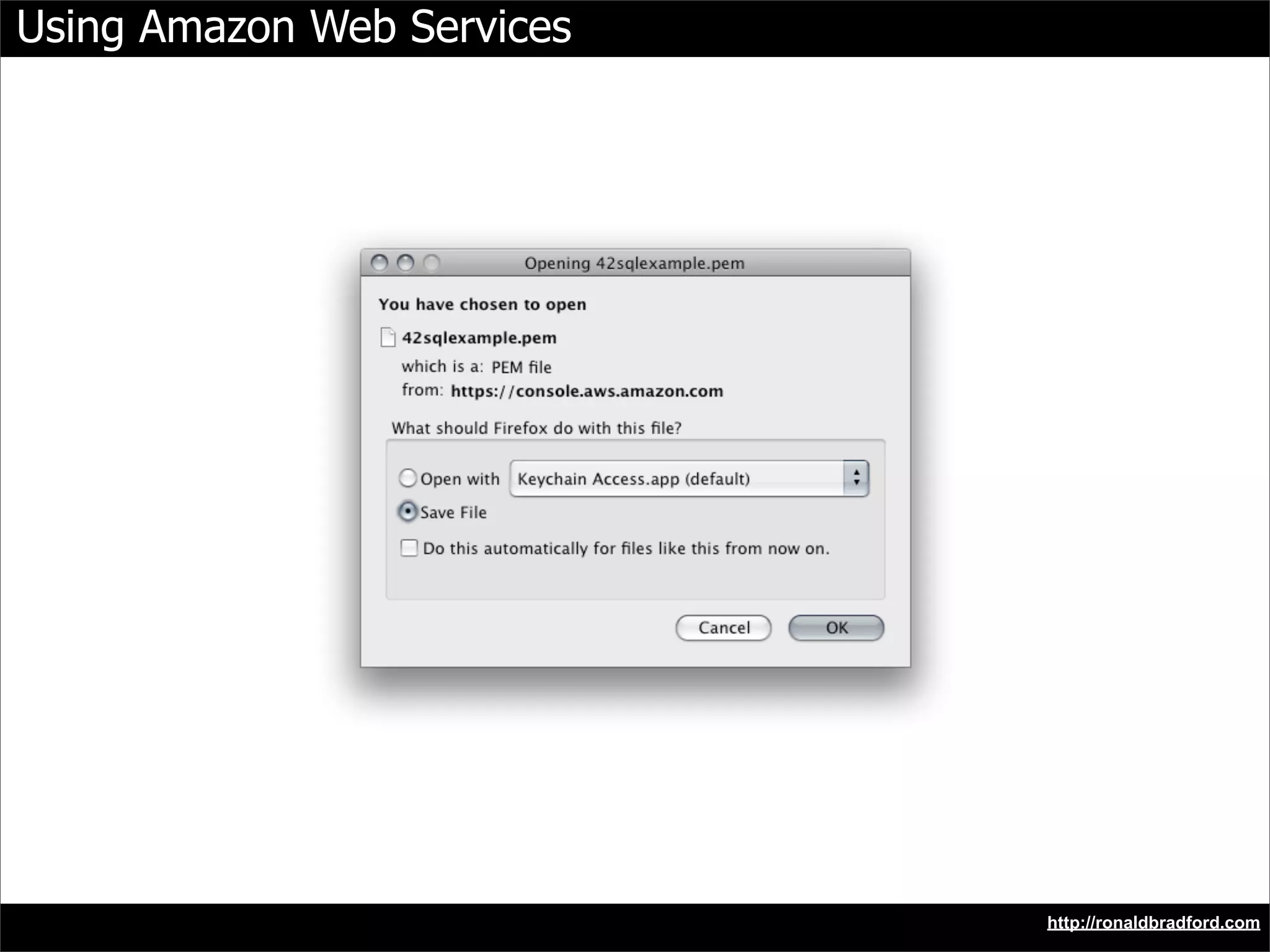
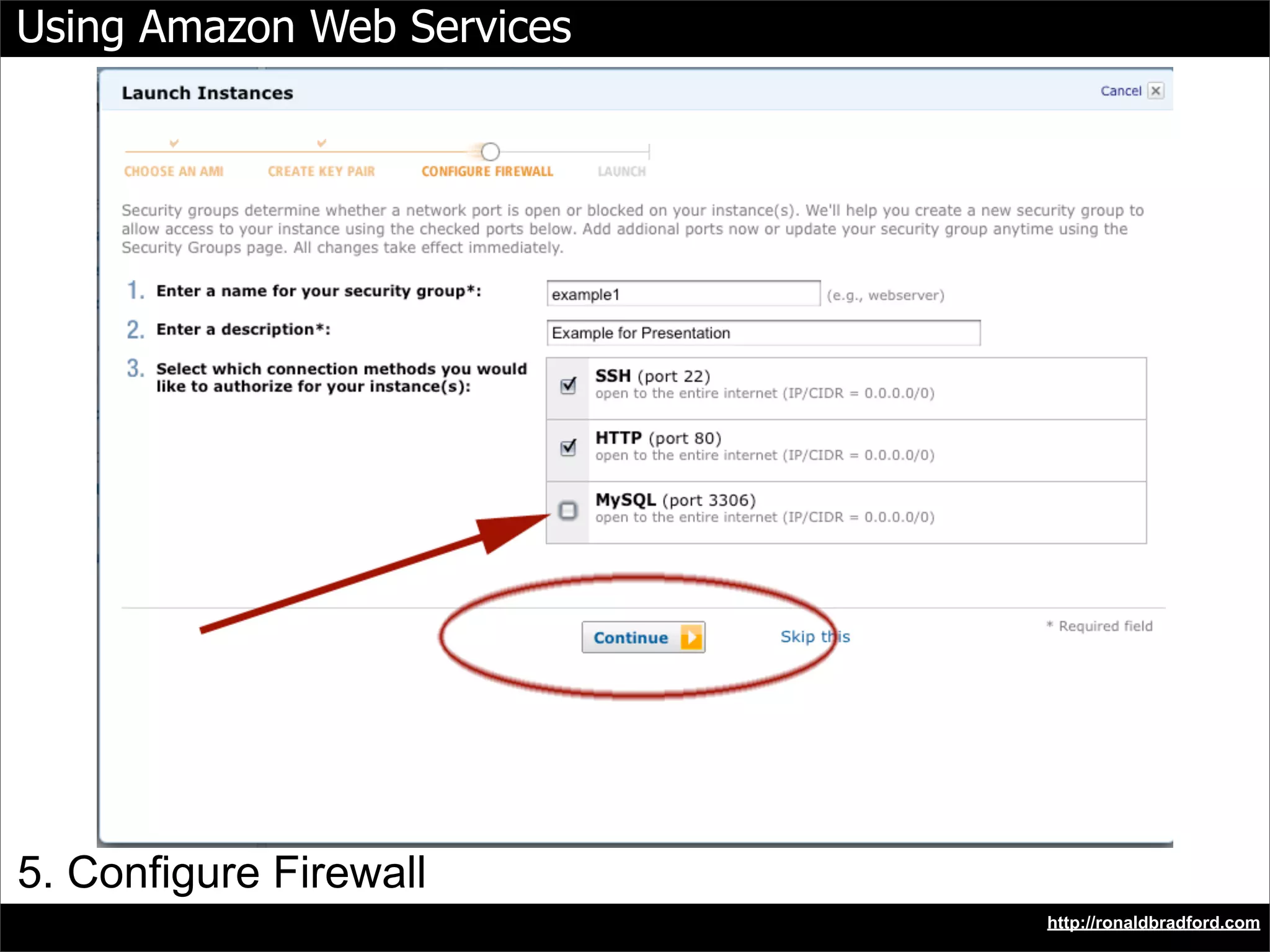
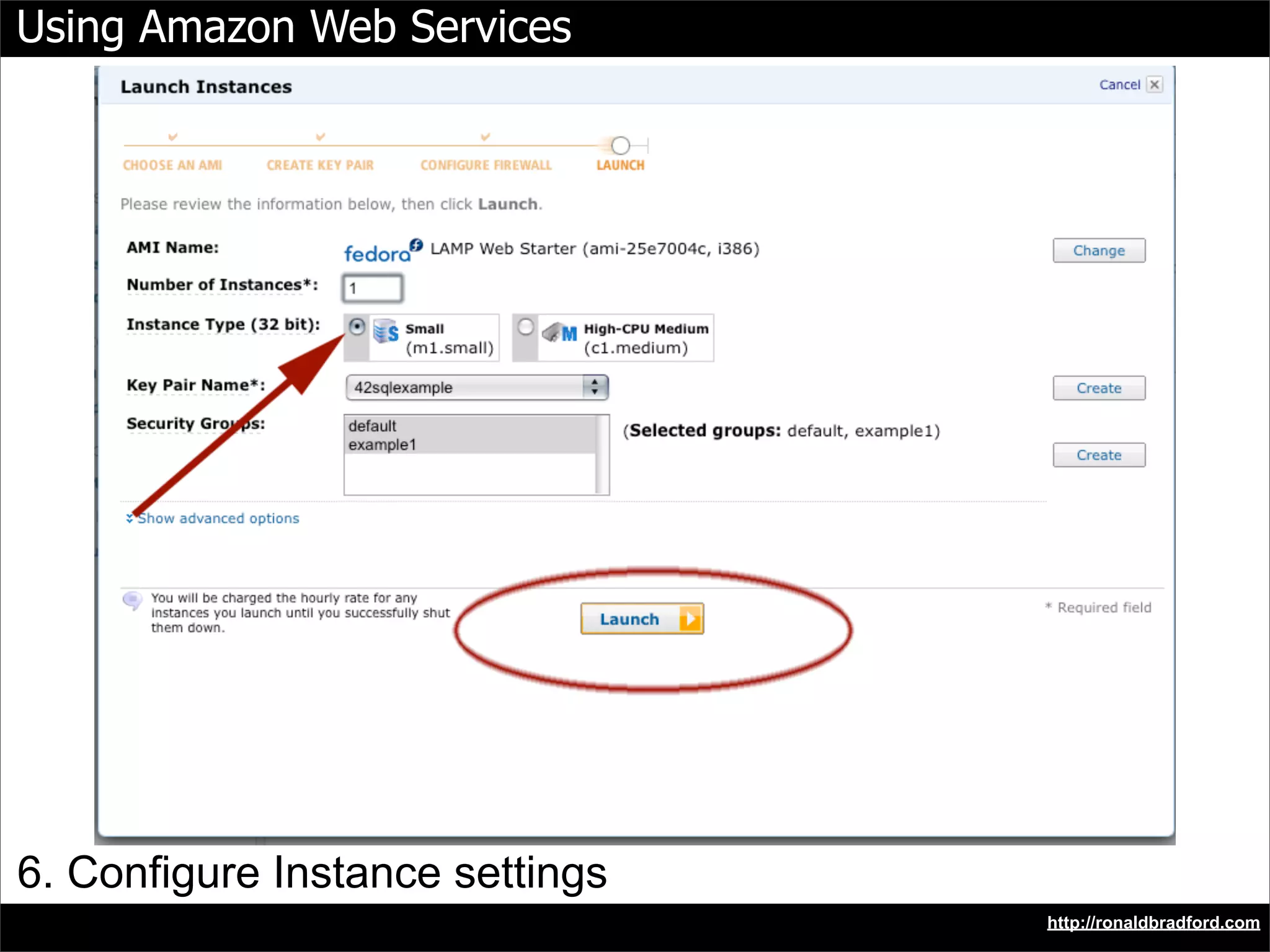
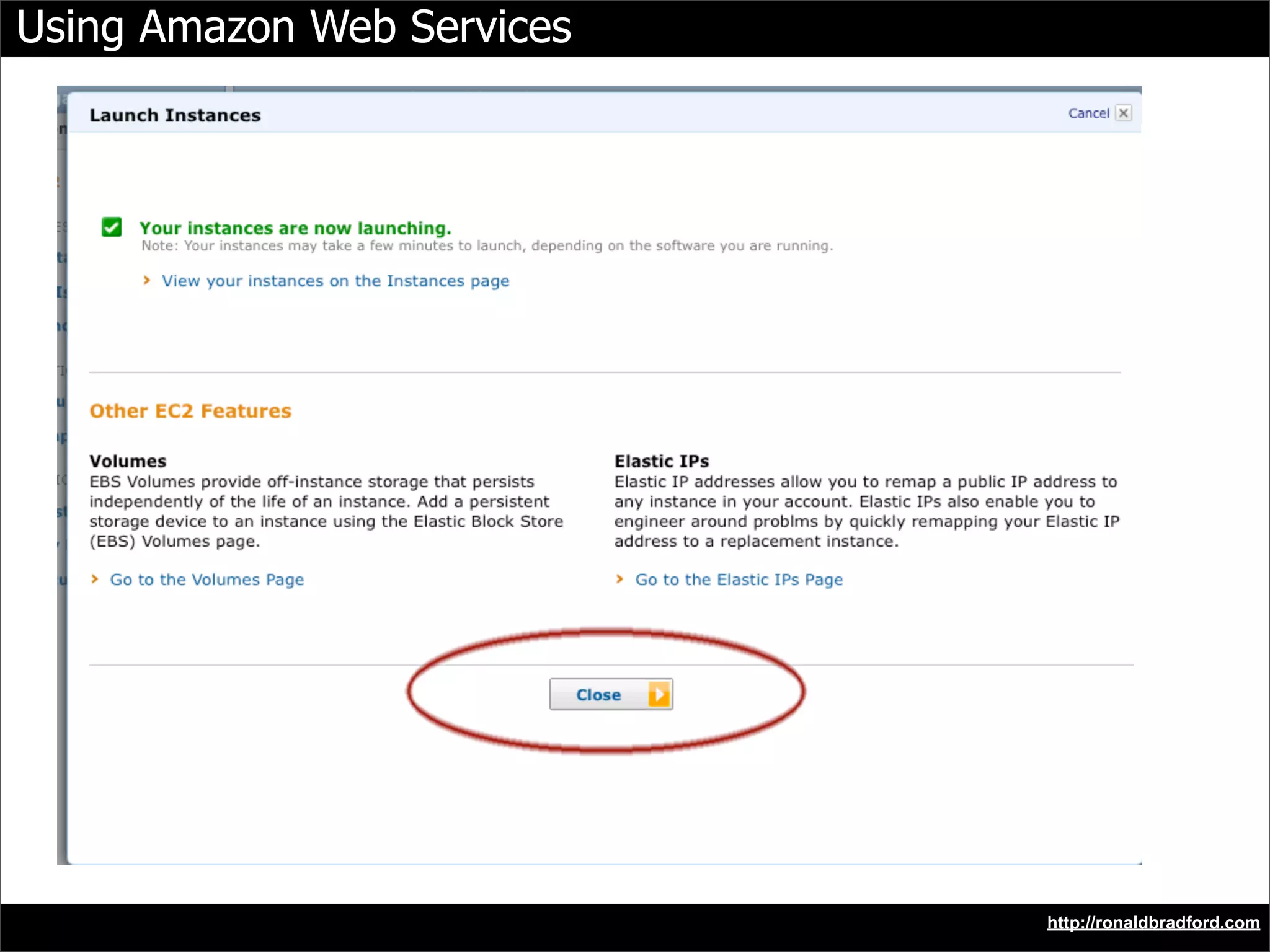
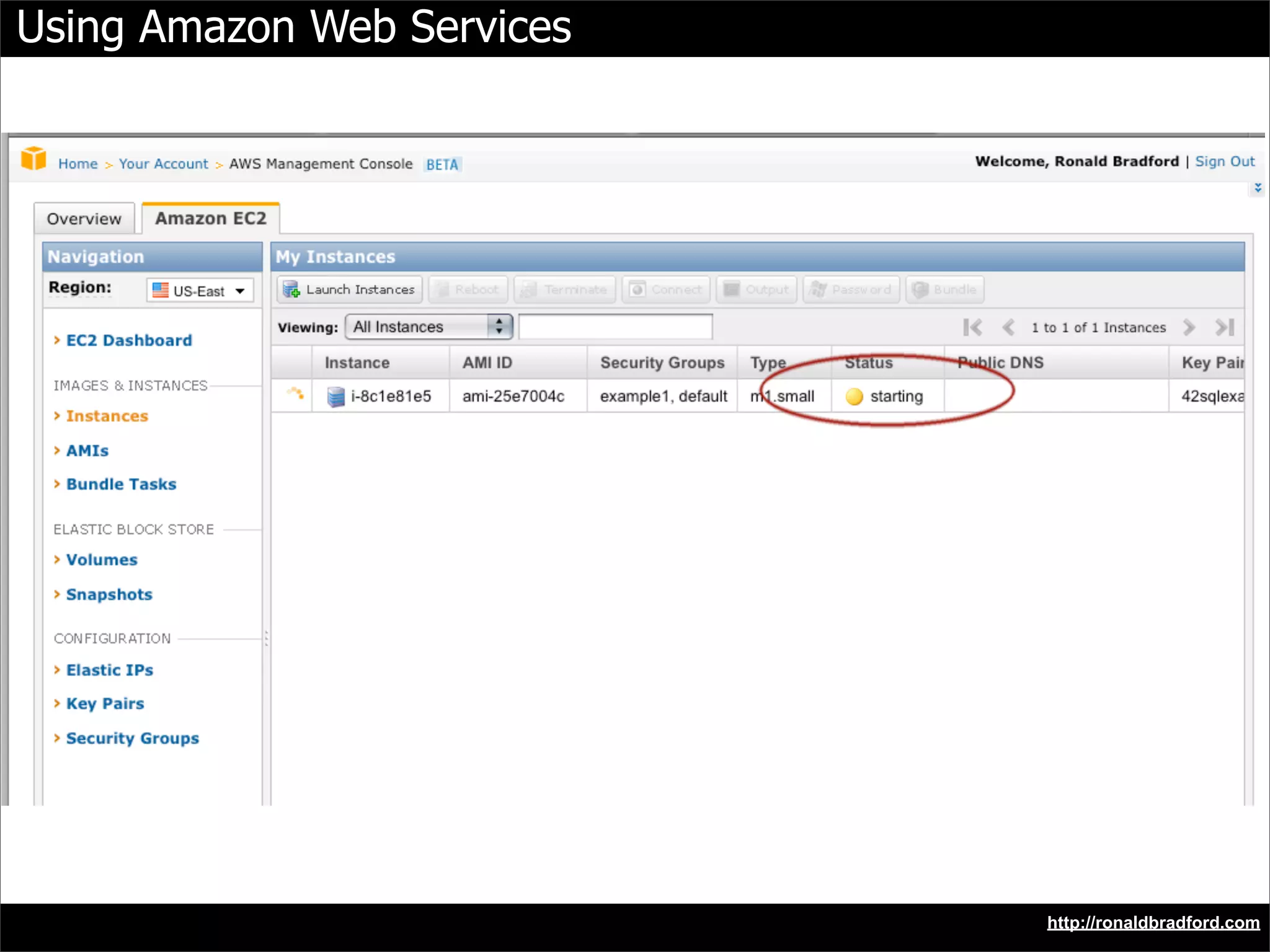
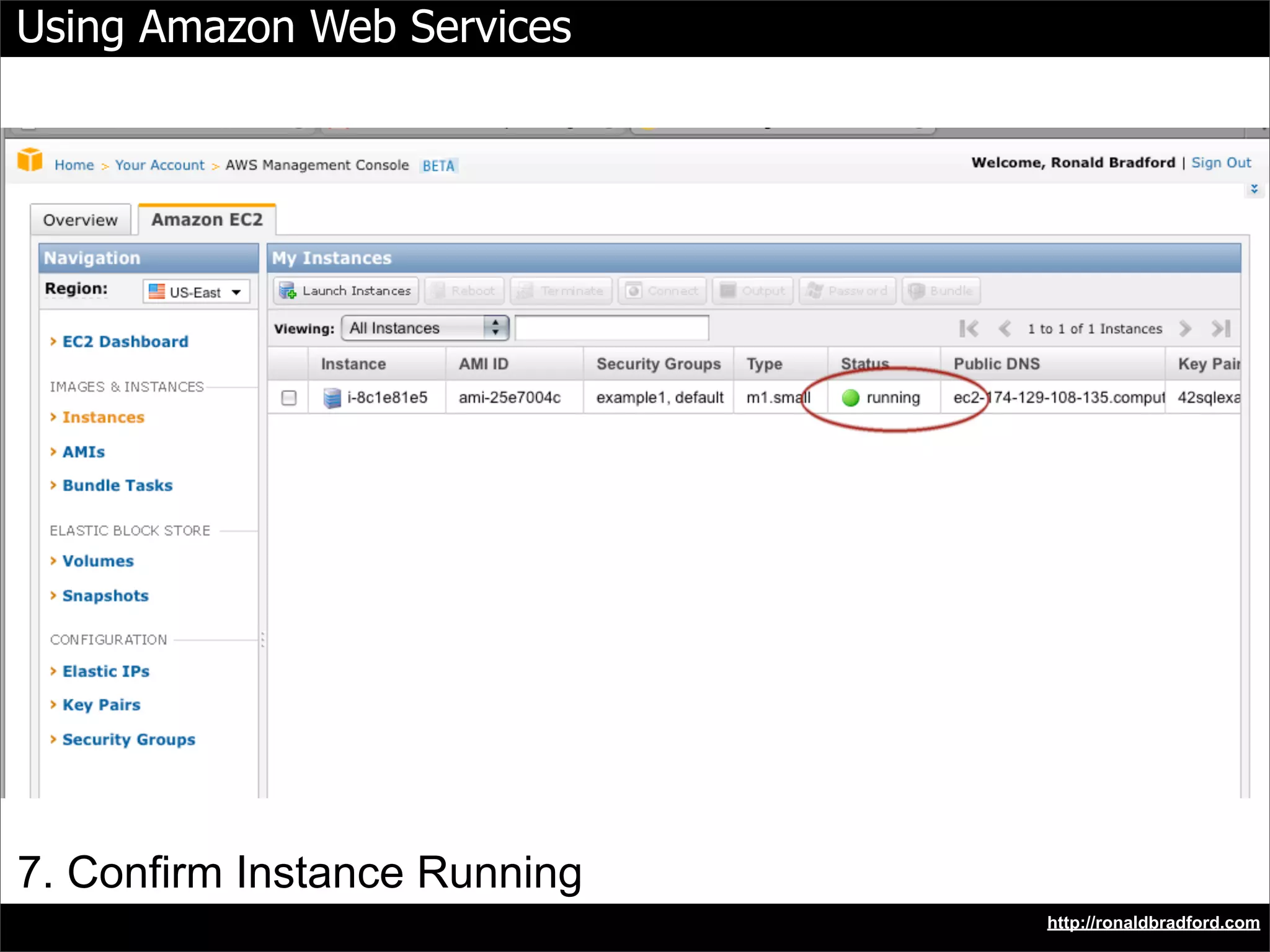
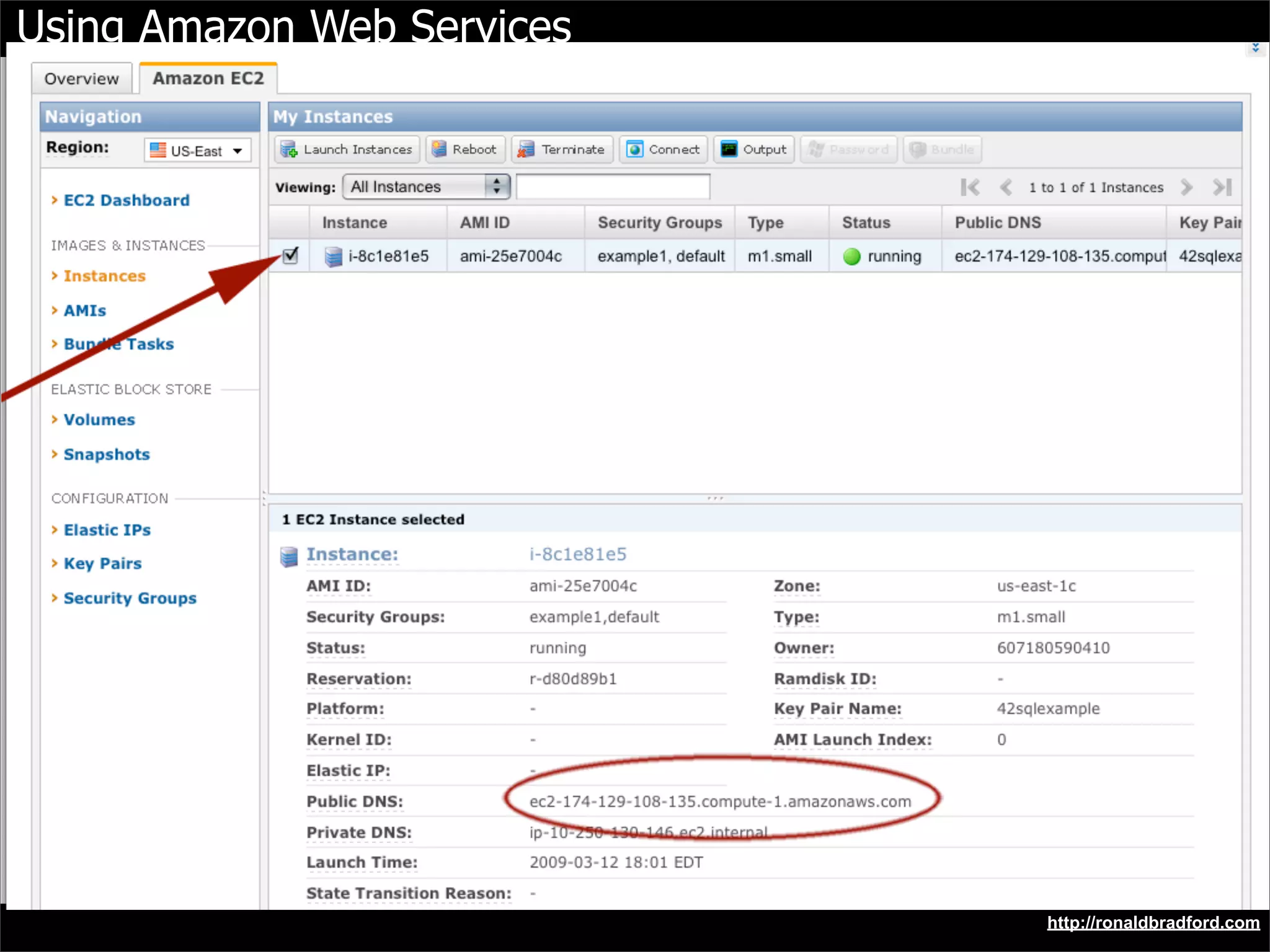
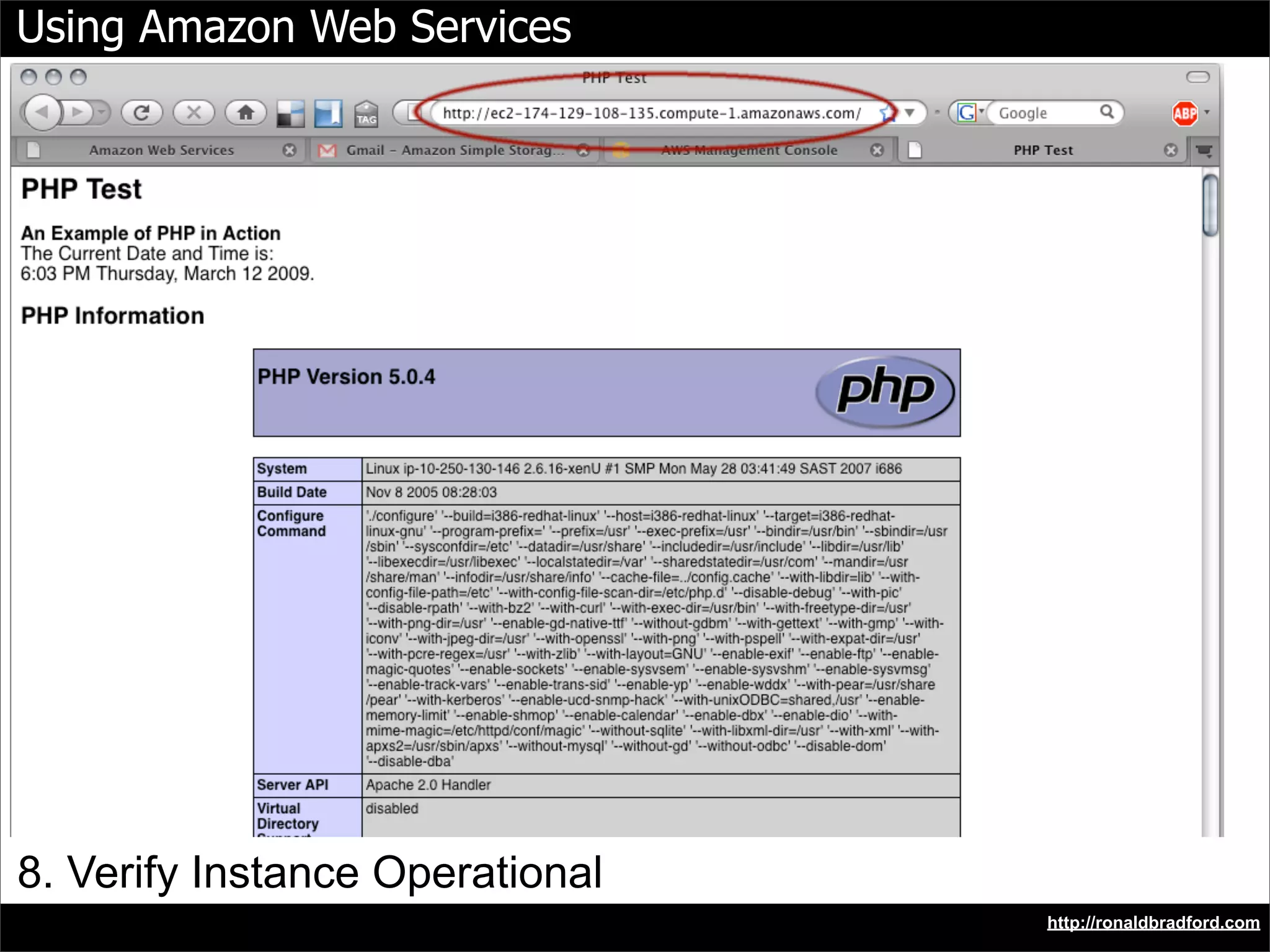
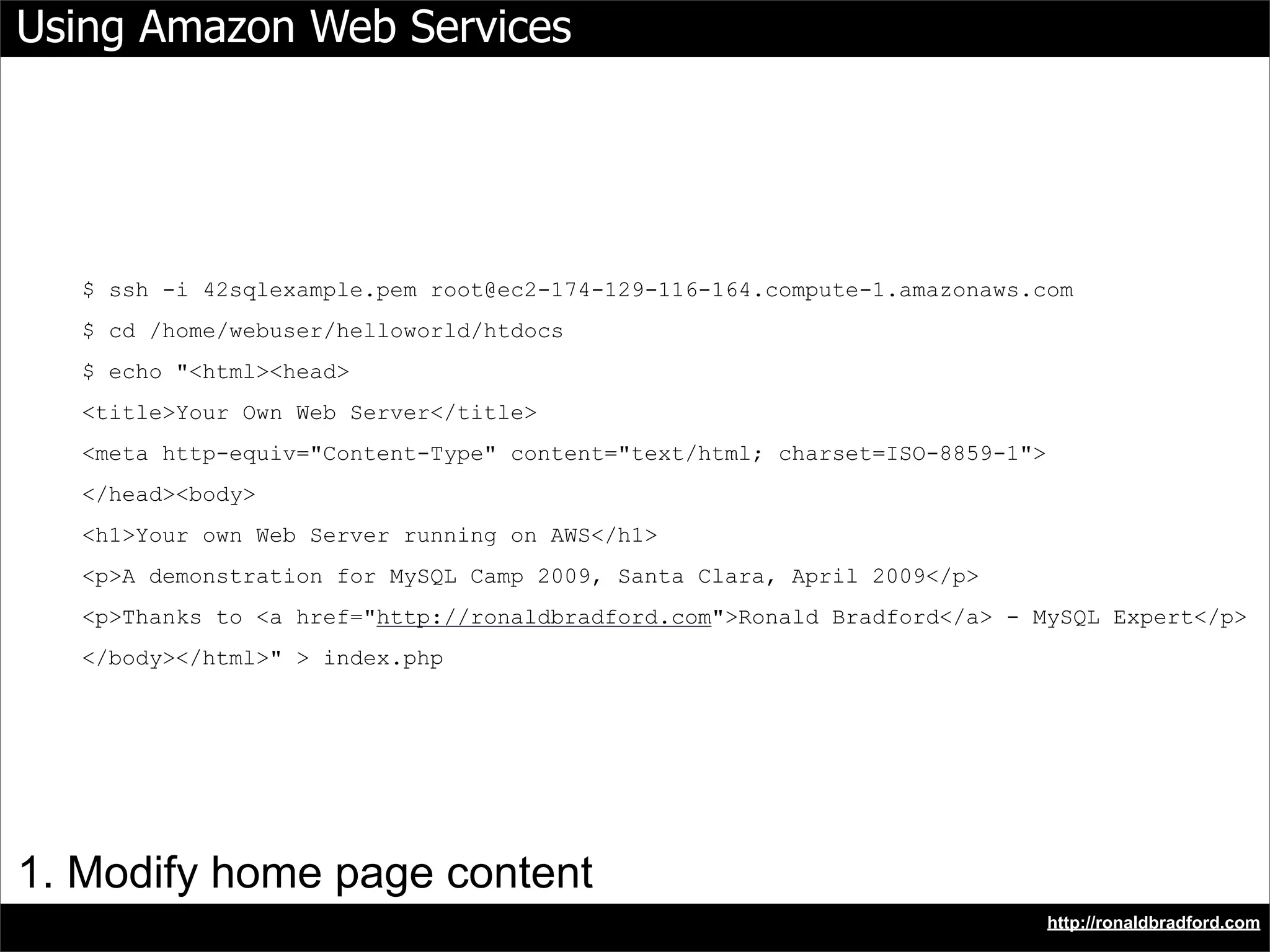
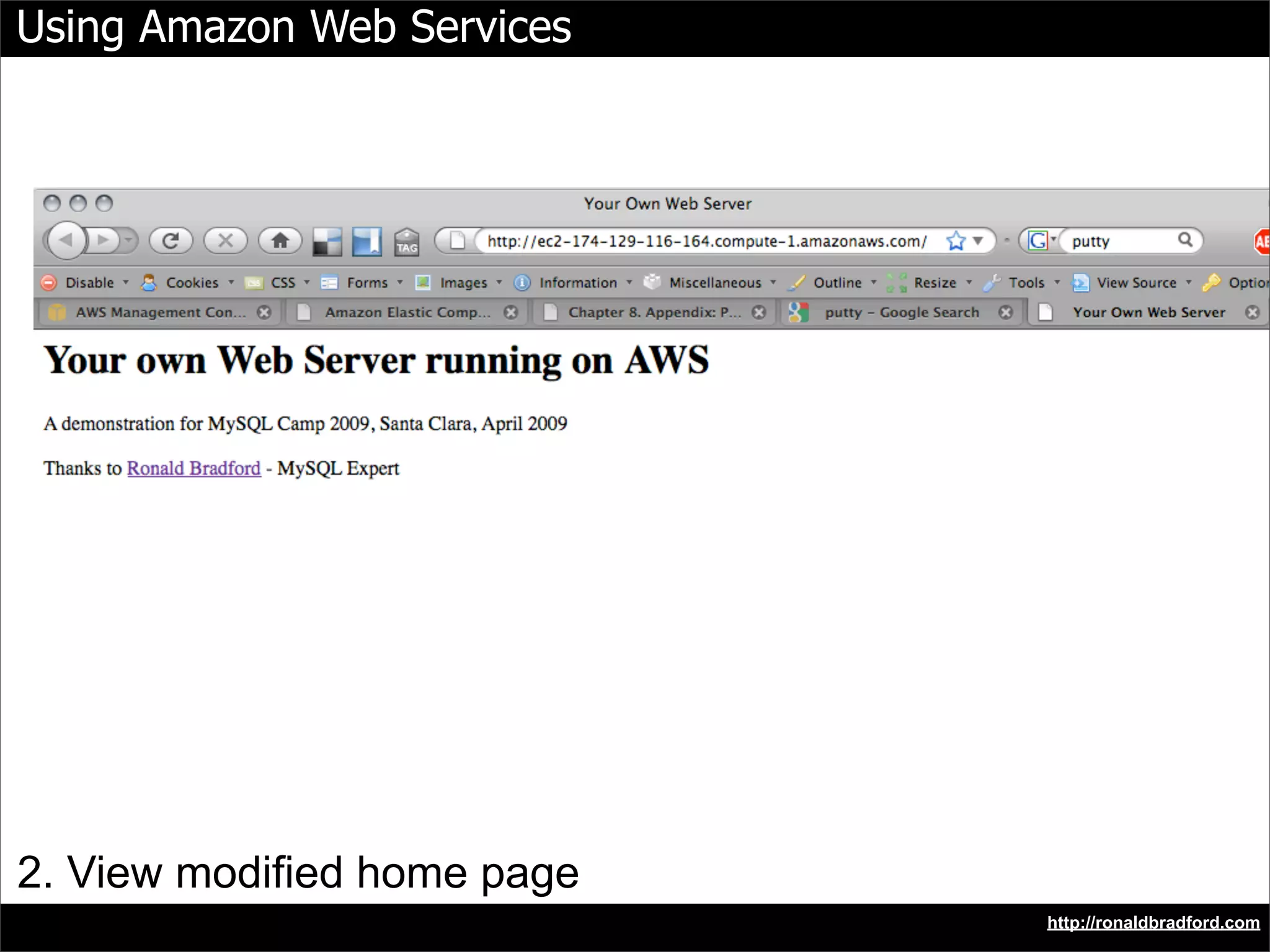
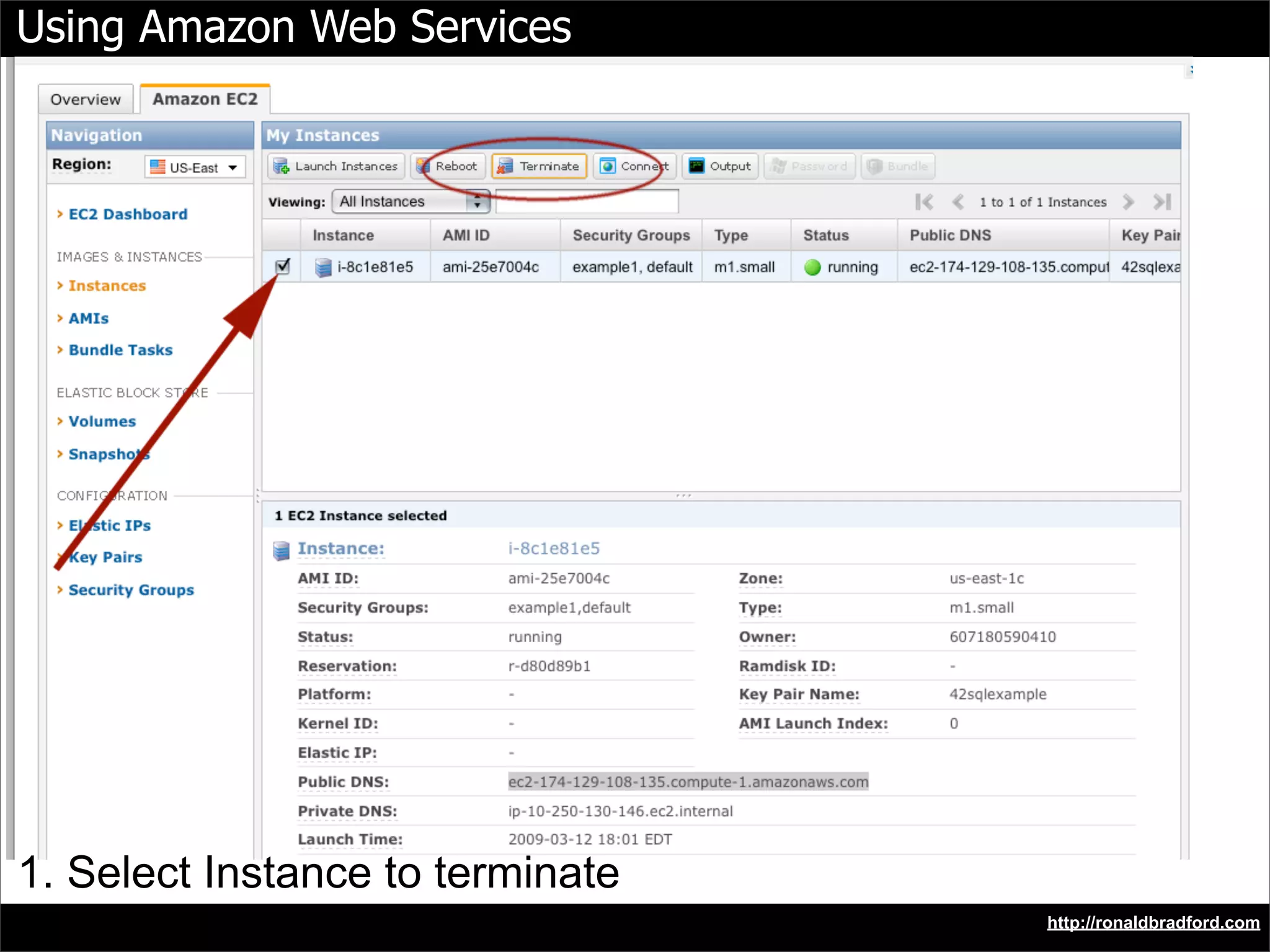
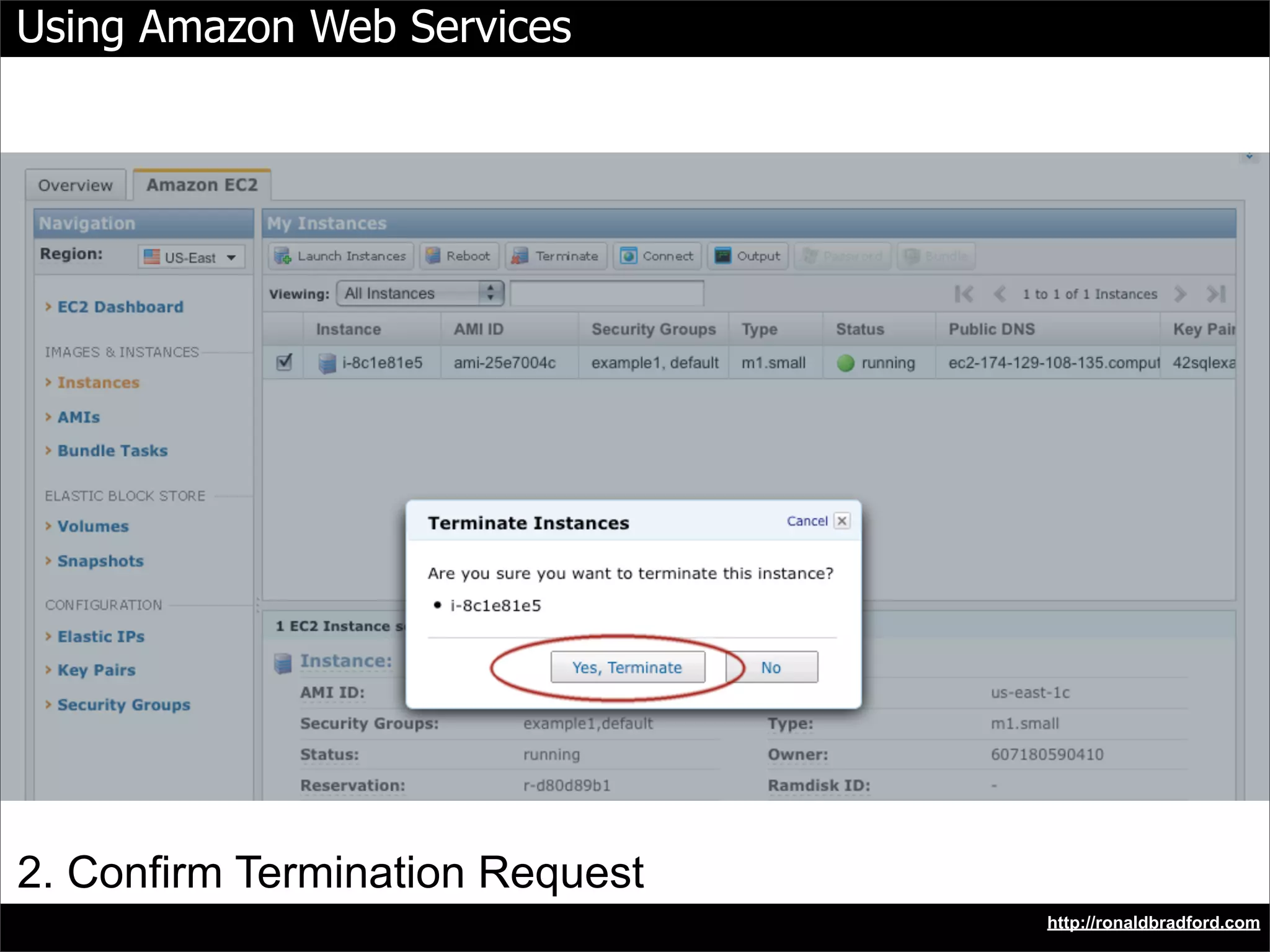
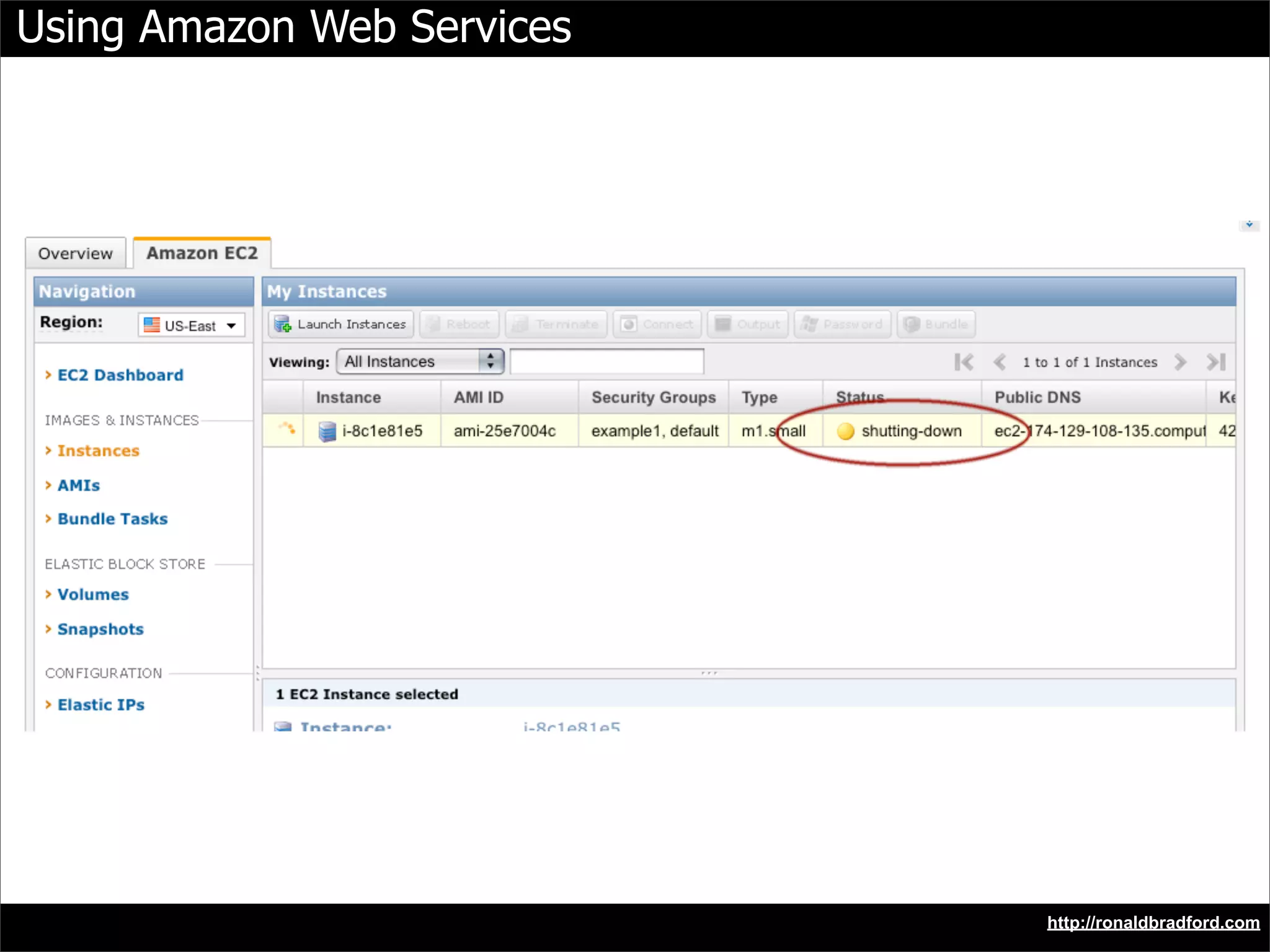
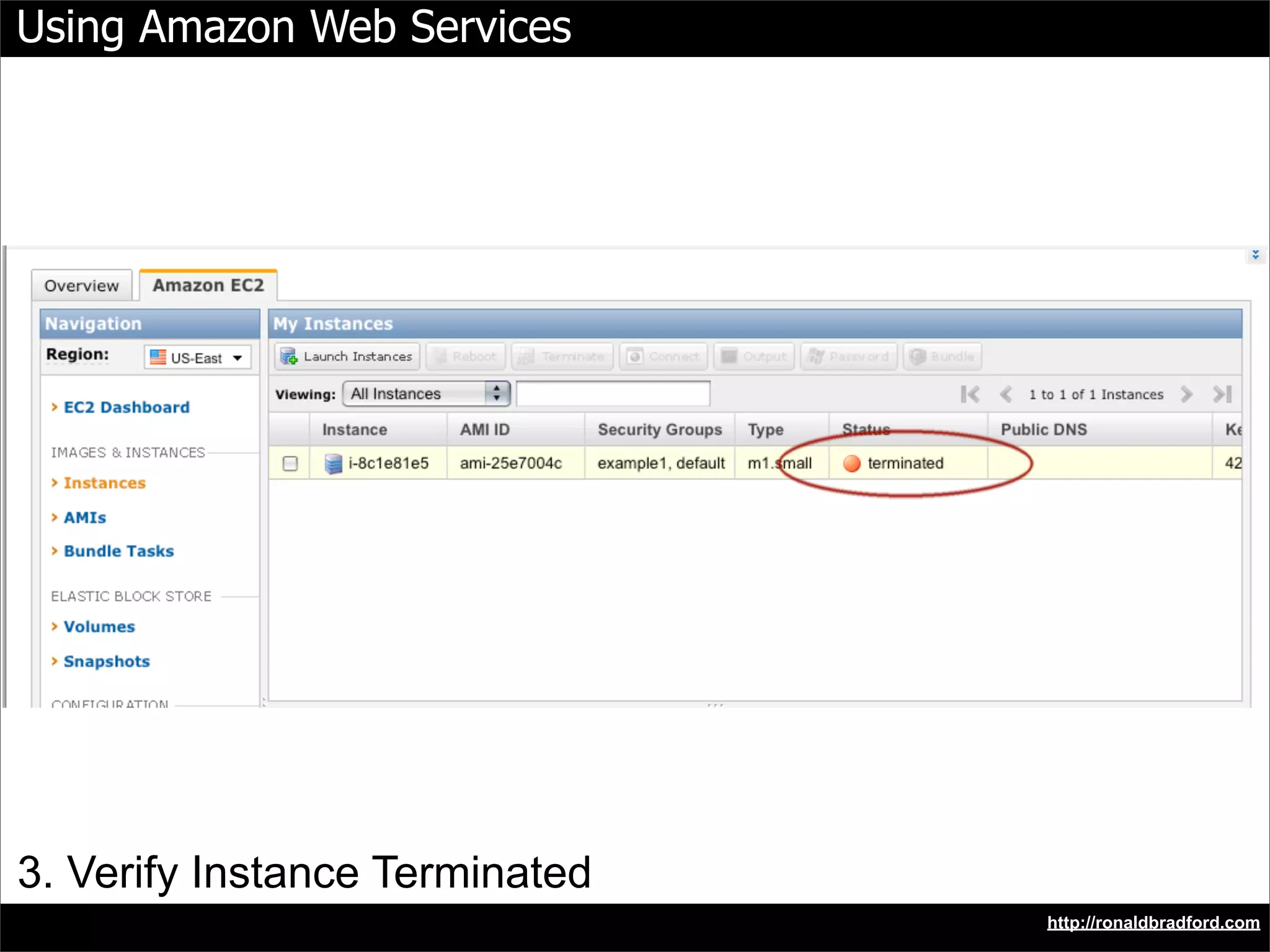
This document provides a tutorial for using Amazon Web Services (AWS) for MySQL users. It outlines the steps to create an AWS account, launch a server instance, and access the running server. These steps include signing up for an AWS account, getting access identifiers, registering for EC2 and S3, launching a server instance, modifying the server's homepage, and shutting down the instance. The document also provides an overview of AWS terminology and points to additional AWS resources and professional help.