Embed presentation
Downloaded 13 times
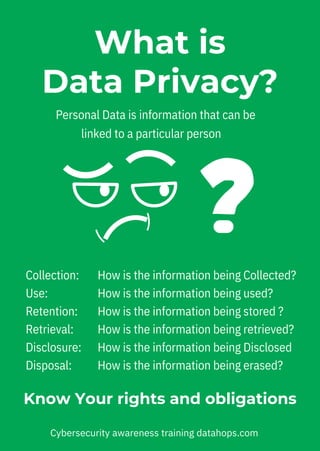


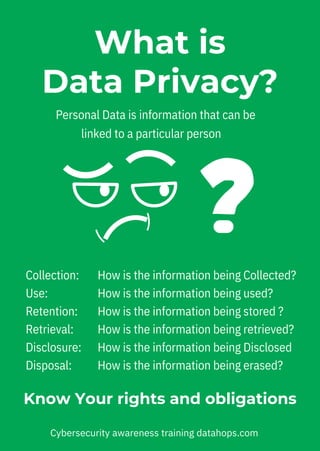
The document emphasizes the importance of data privacy and security, urging careful consideration of the information shared through apps. It highlights key practices such as encryption, responsible sharing, and proper data disposal to safeguard sensitive data. Additionally, it encourages individuals to understand their rights and obligations regarding their personal data's collection, use, and protection.