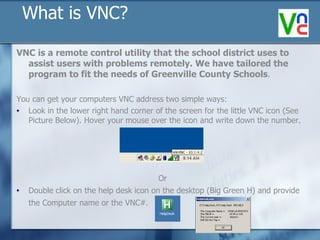
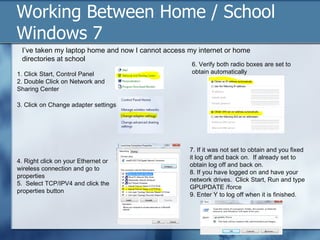
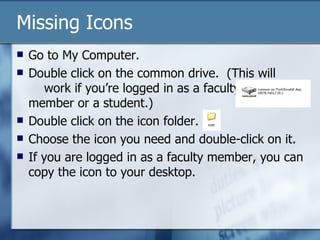
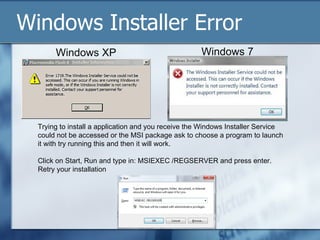
The troubleshooting guide provides detailed instructions for resolving issues related to network connectivity, laptop performance, printer connectivity, and audio troubleshooting within the Greenville County Schools. It includes steps for using VNC to assist with remote issues, as well as specific workflows for Windows XP and Windows 7 users. Additional sections address security practices and maintenance tips, emphasizing the importance of backups and the proper handling of school technology resources.