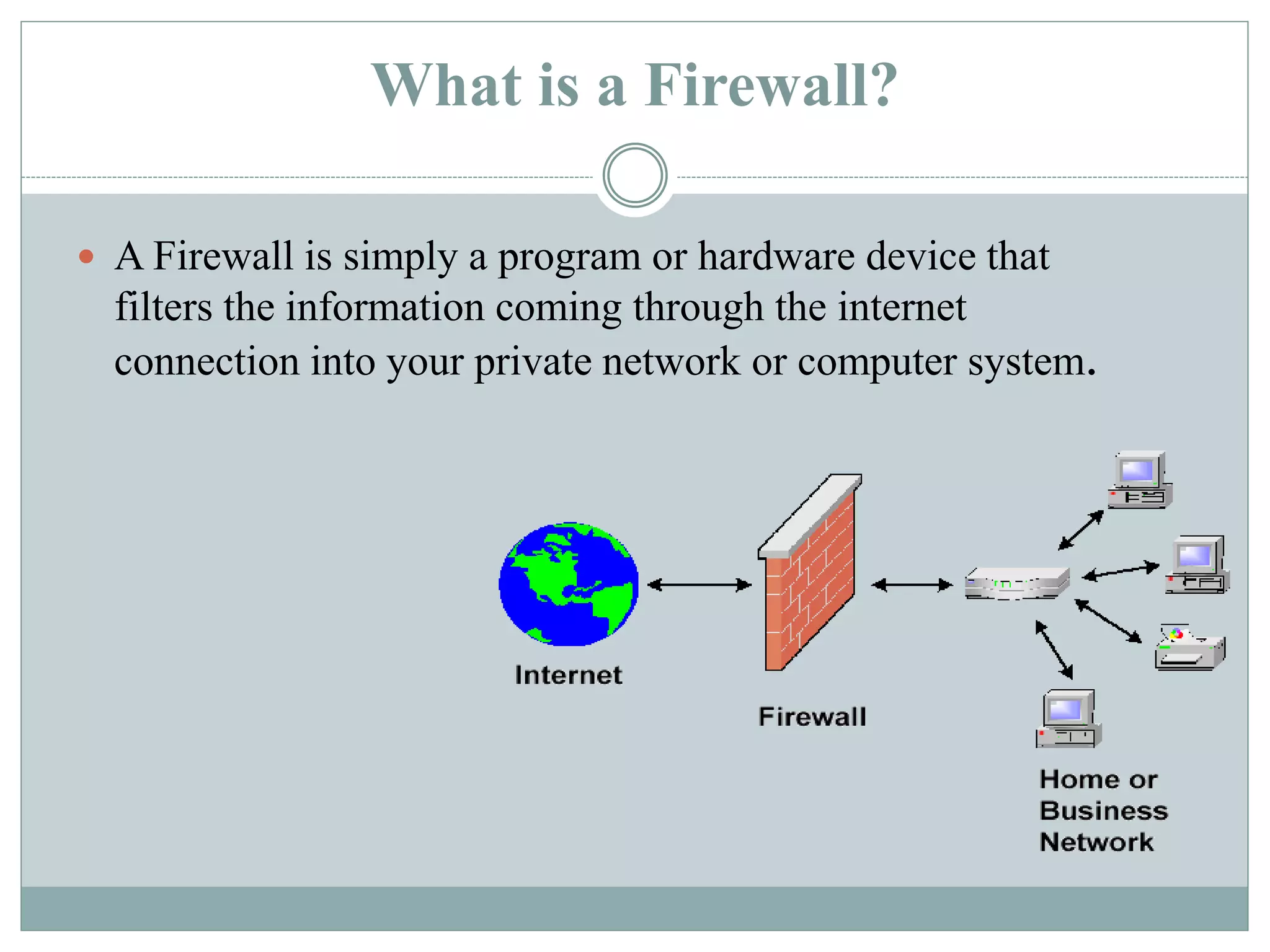
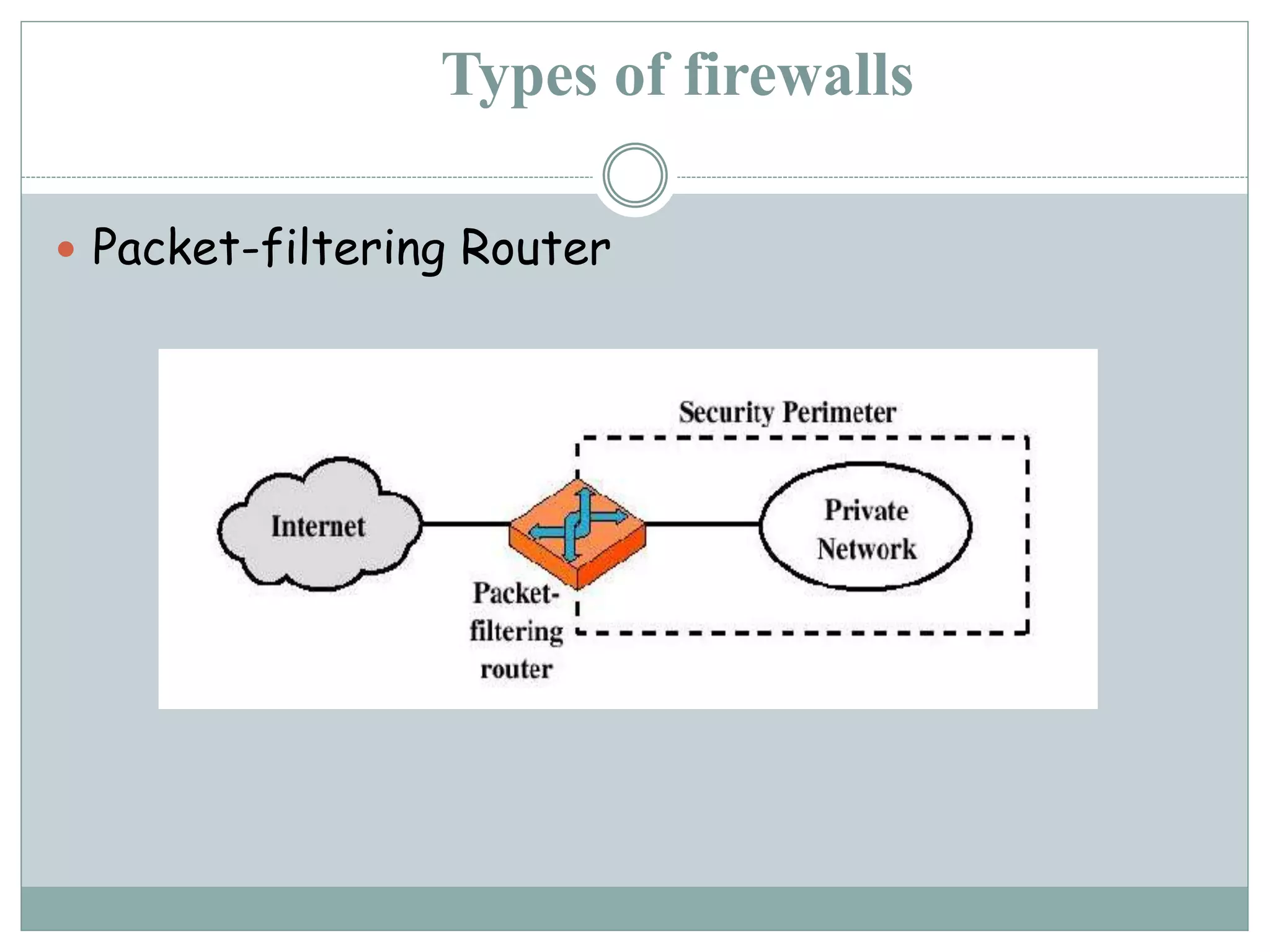
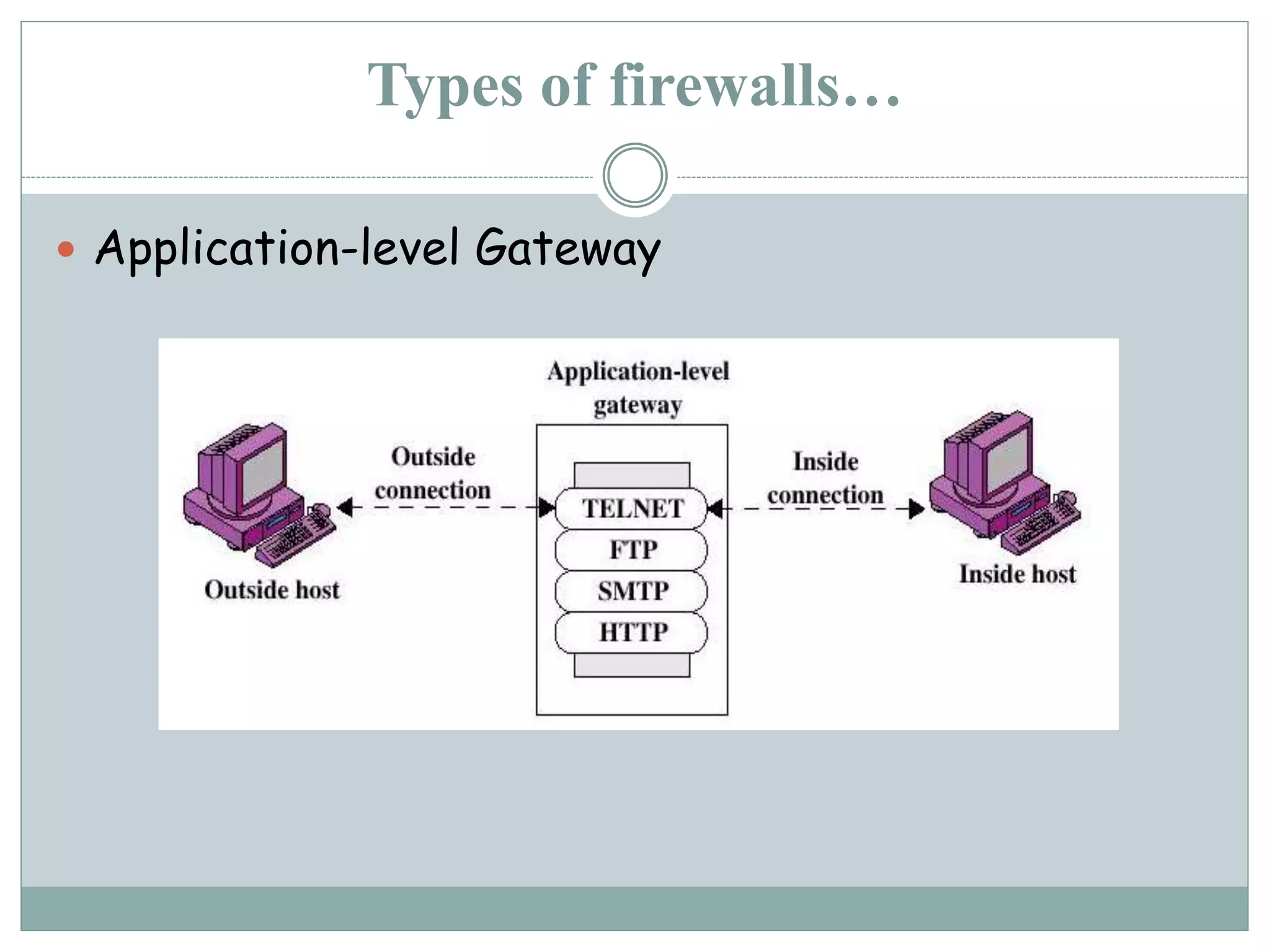
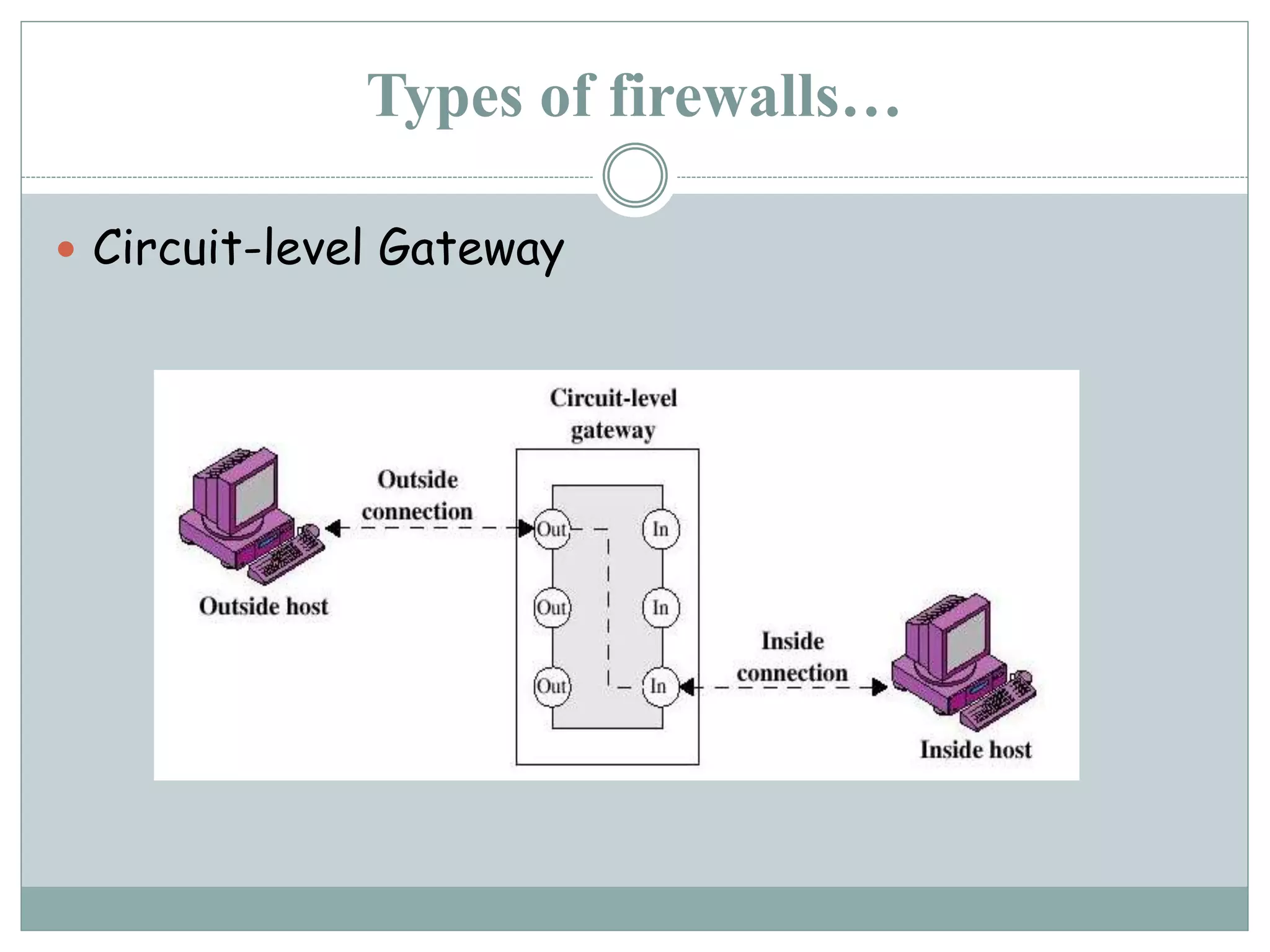
This document provides an overview of firewalls, including what they are, their history, types, and basic concepts. A firewall is a program or hardware device that filters network traffic between the internet and an internal network or computer. There are different types, including packet filtering routers, application-level gateways, and circuit-level gateways. Firewalls aim to only allow authorized traffic according to a security policy while protecting systems from outside penetration. They provide advantages like concentrating security but also disadvantages like potentially blocking some network access.