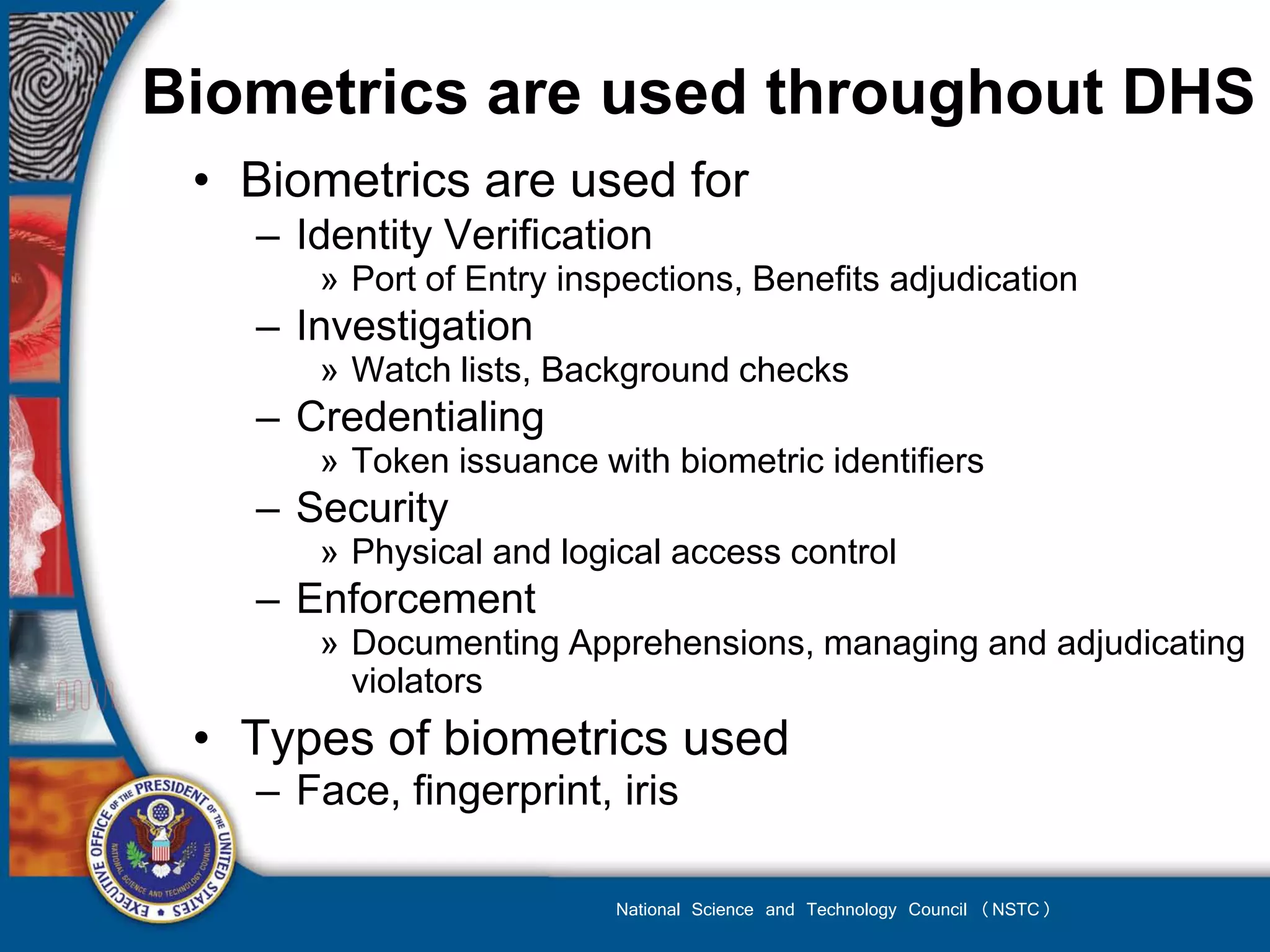
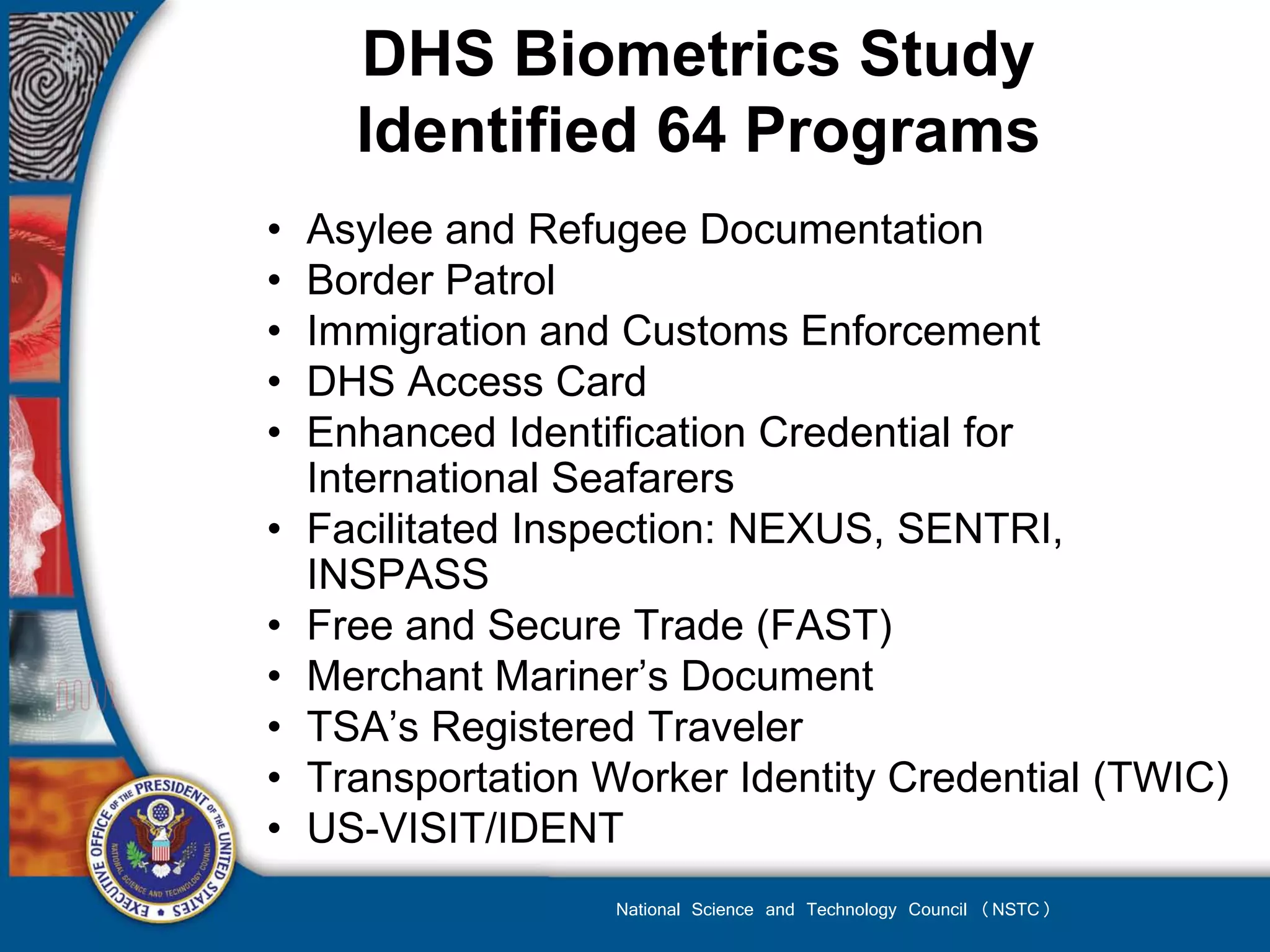
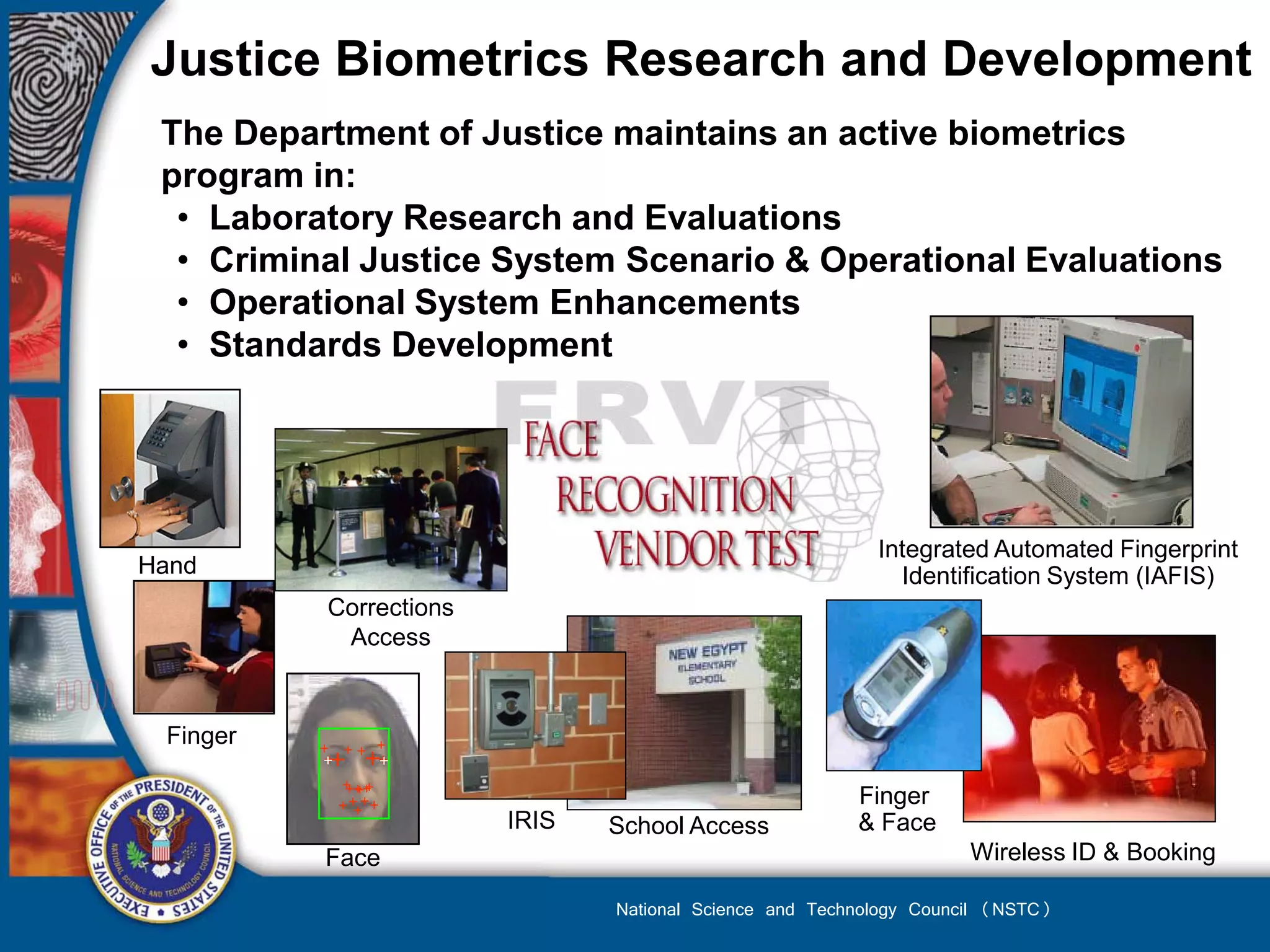
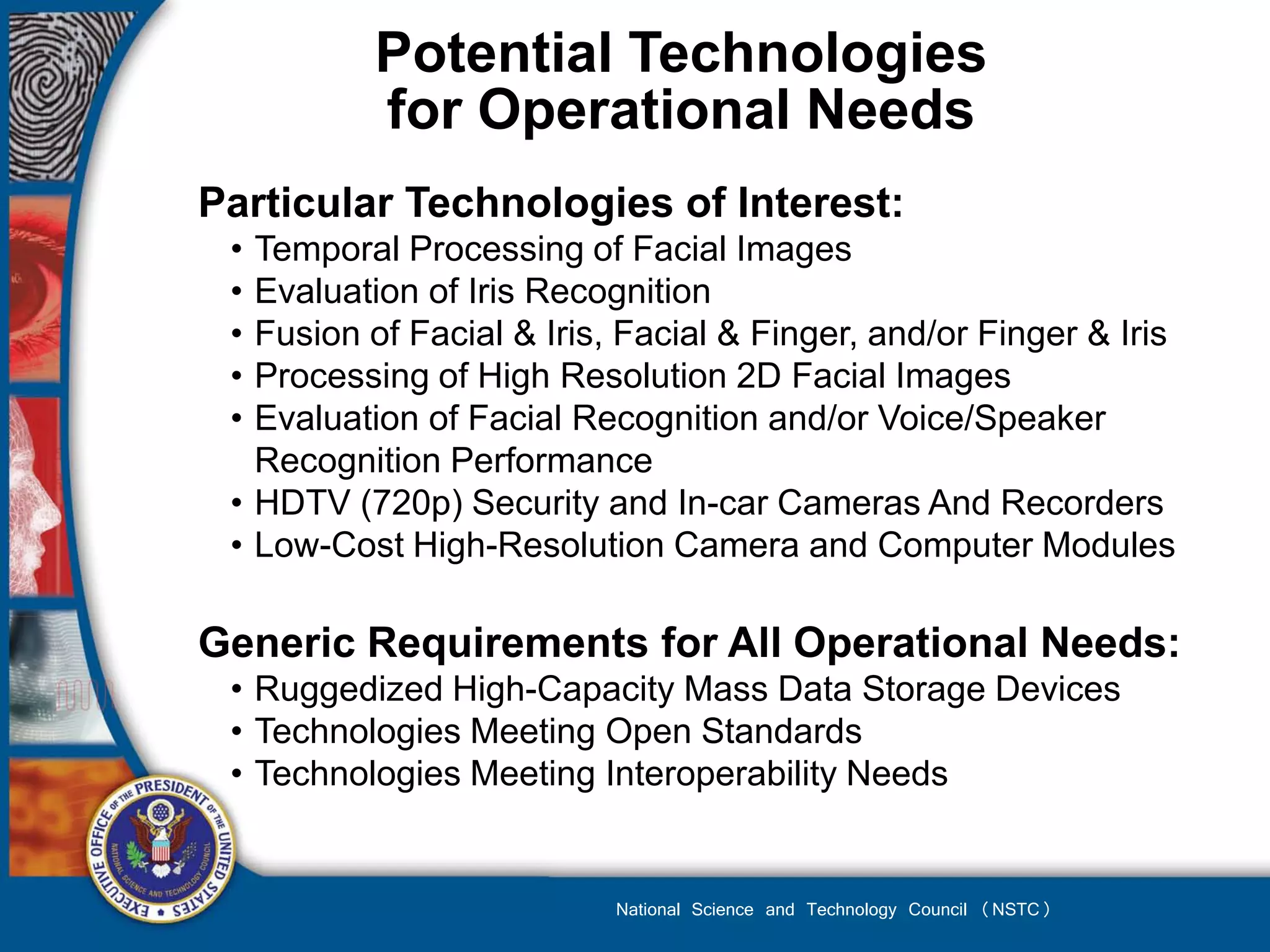
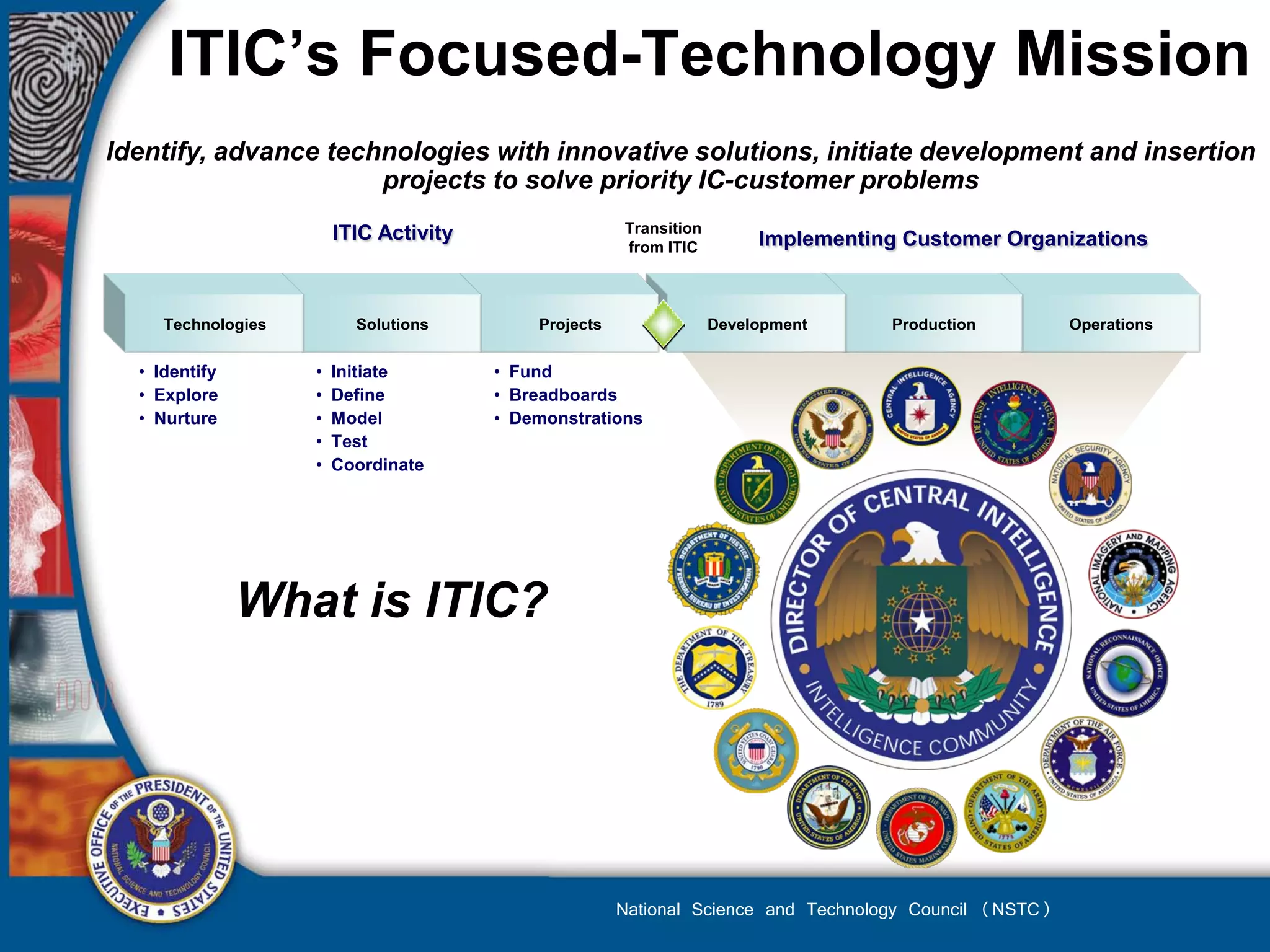
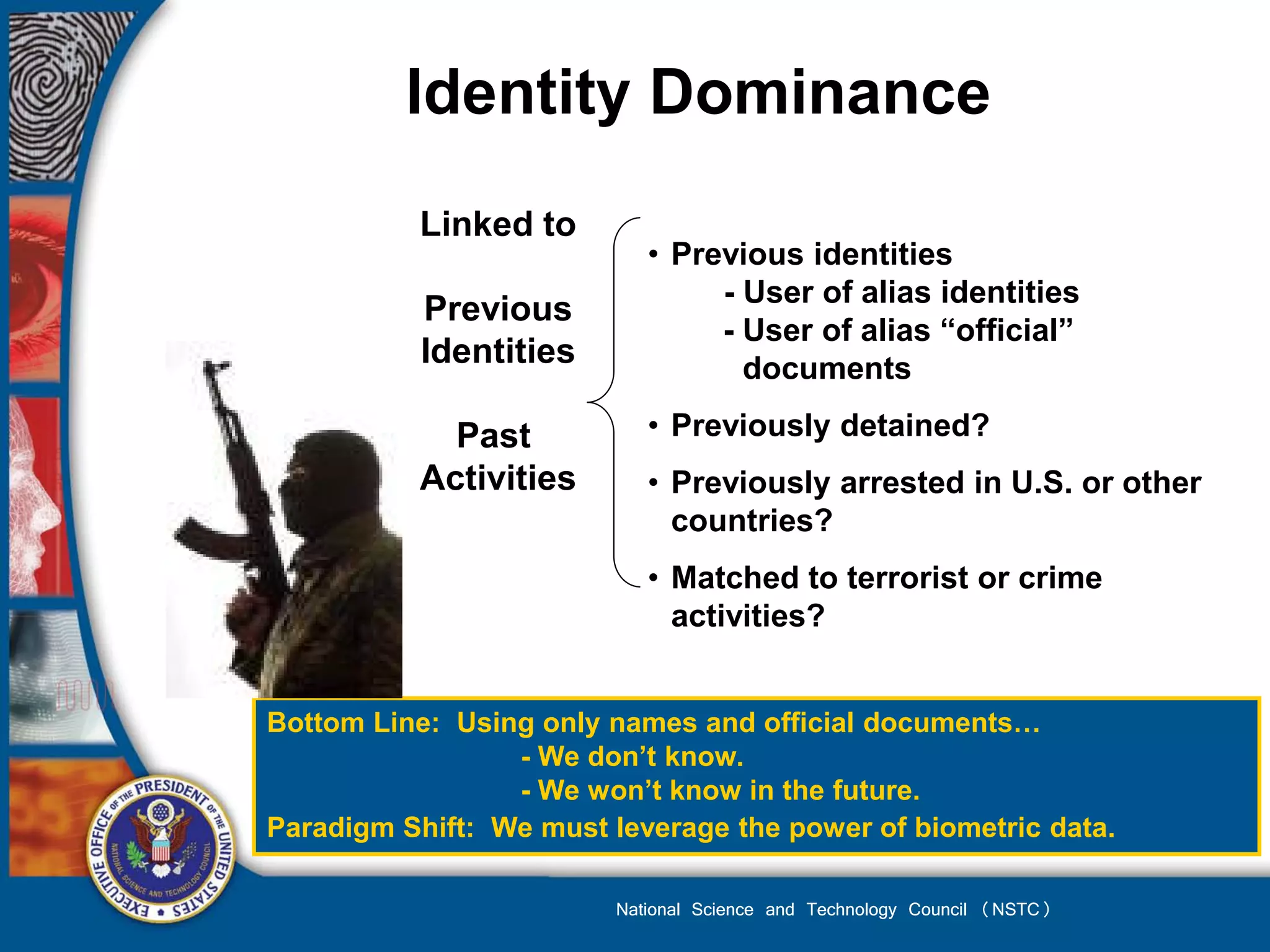
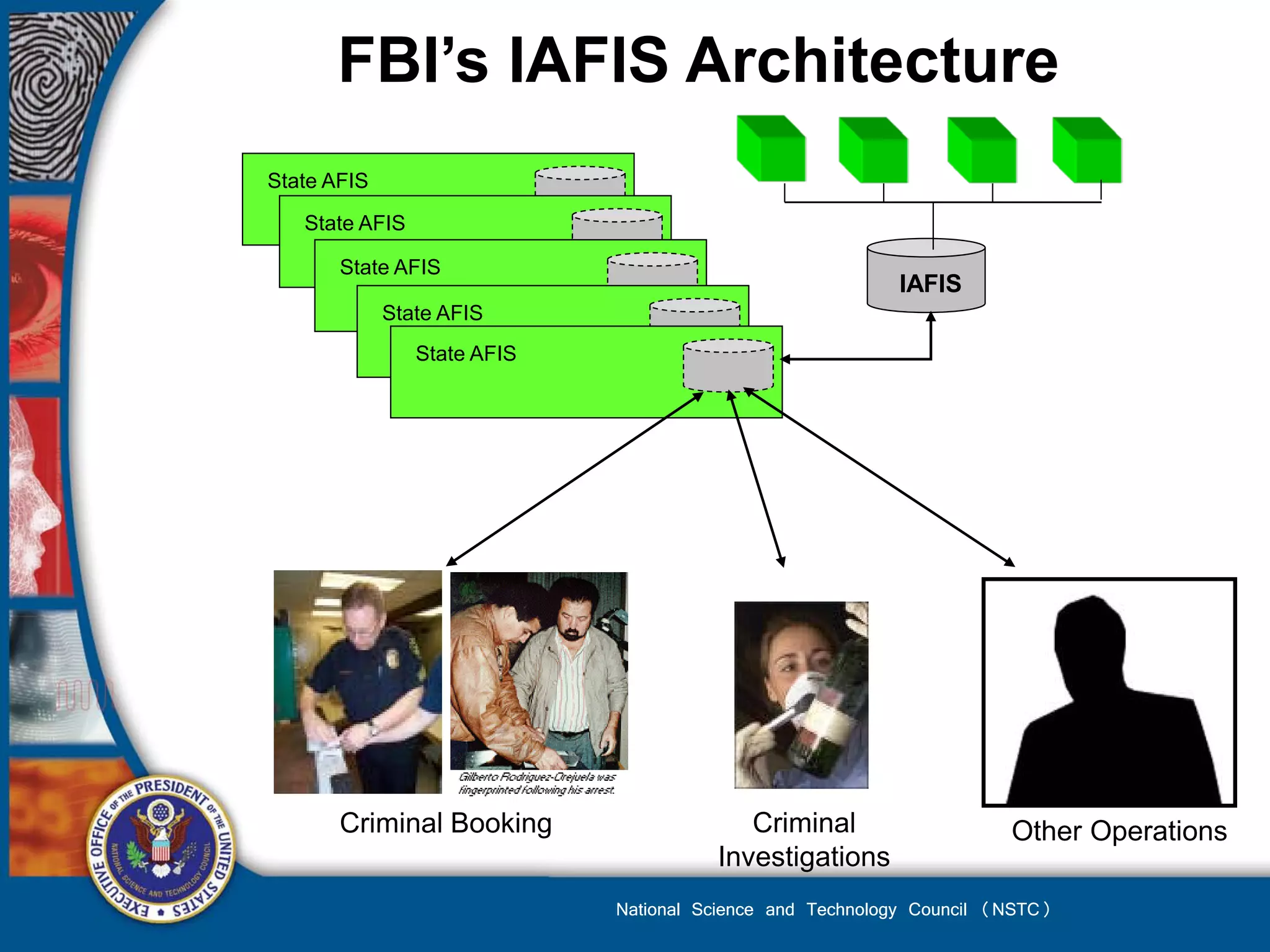
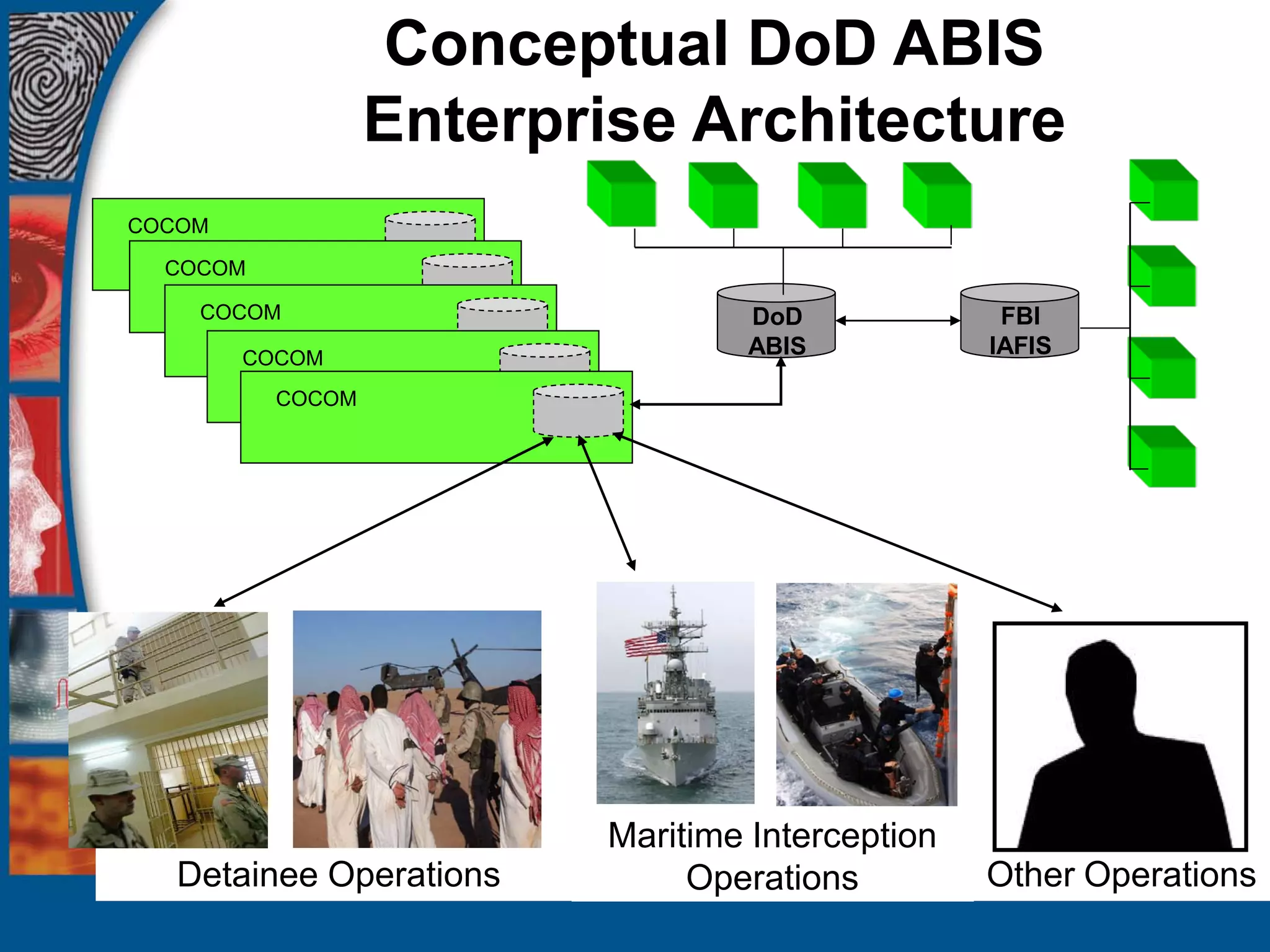
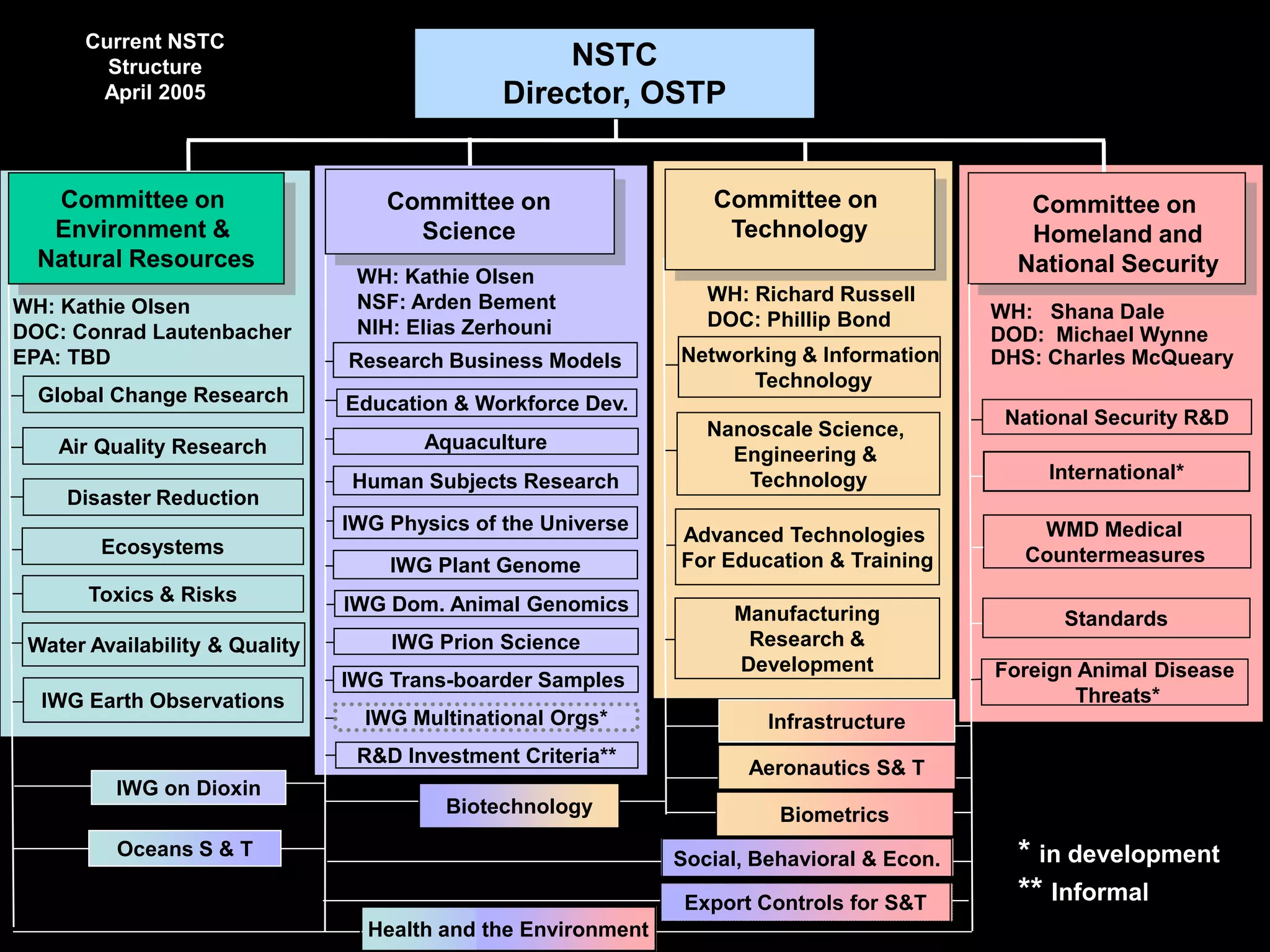
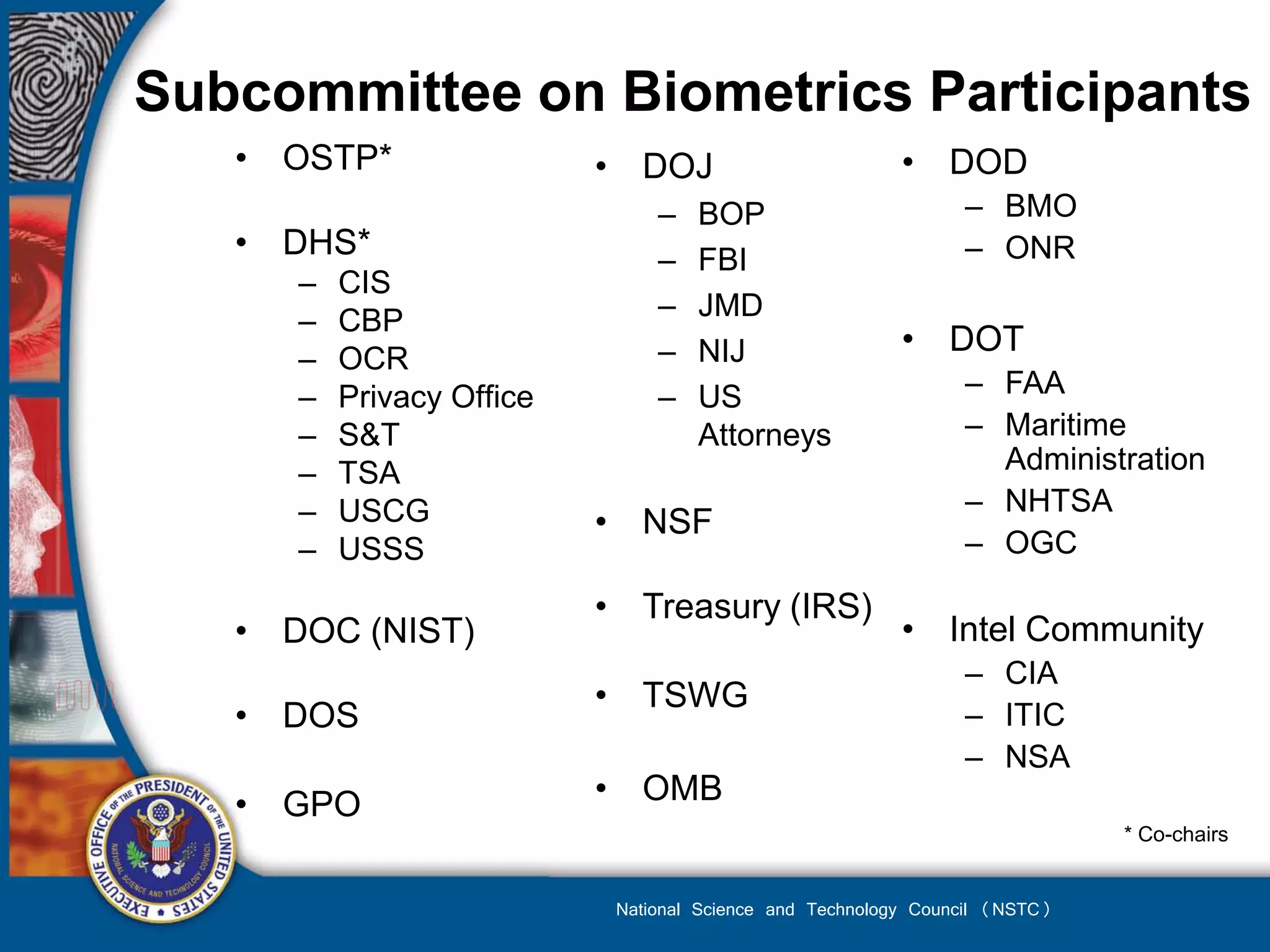
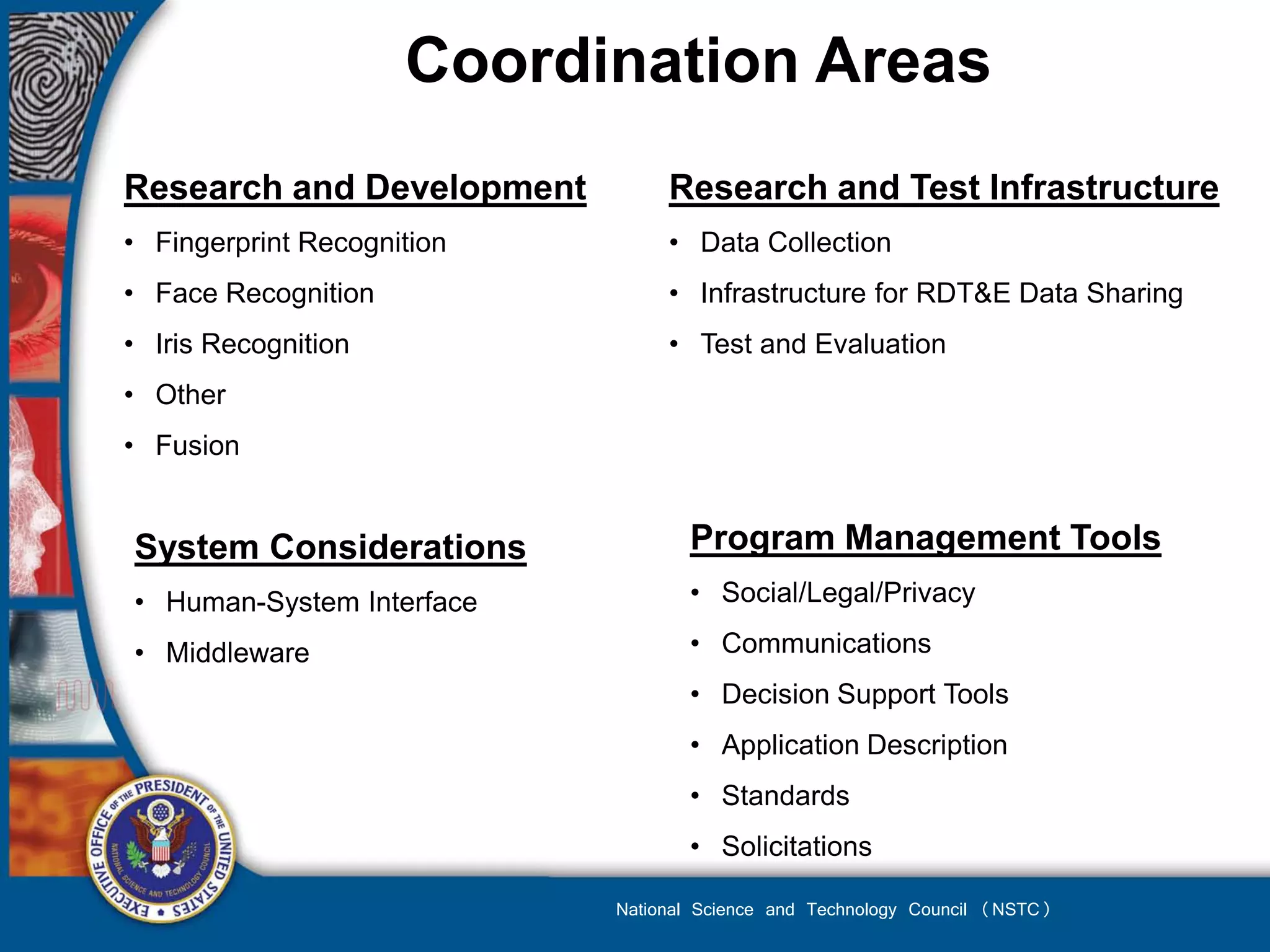
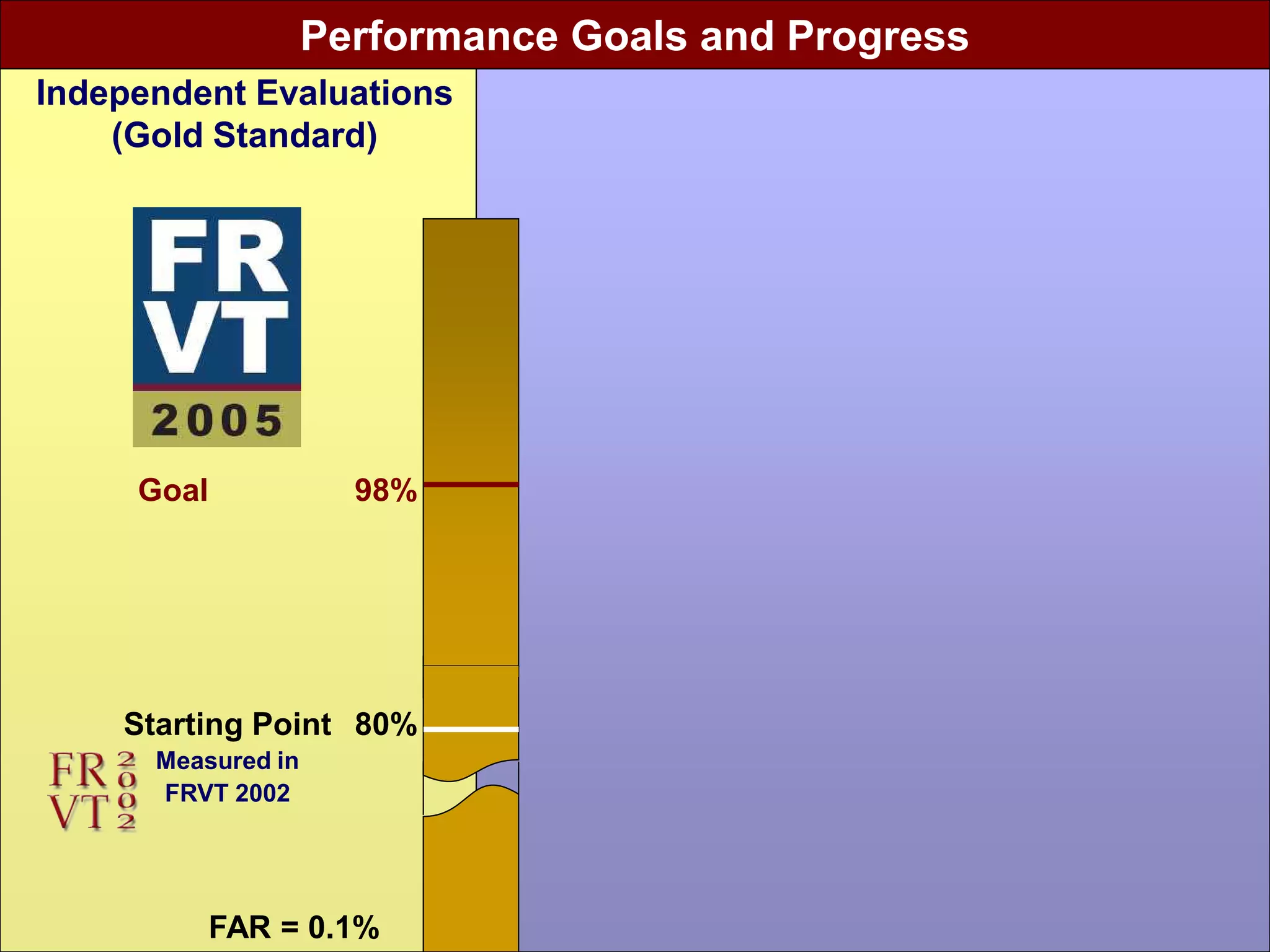
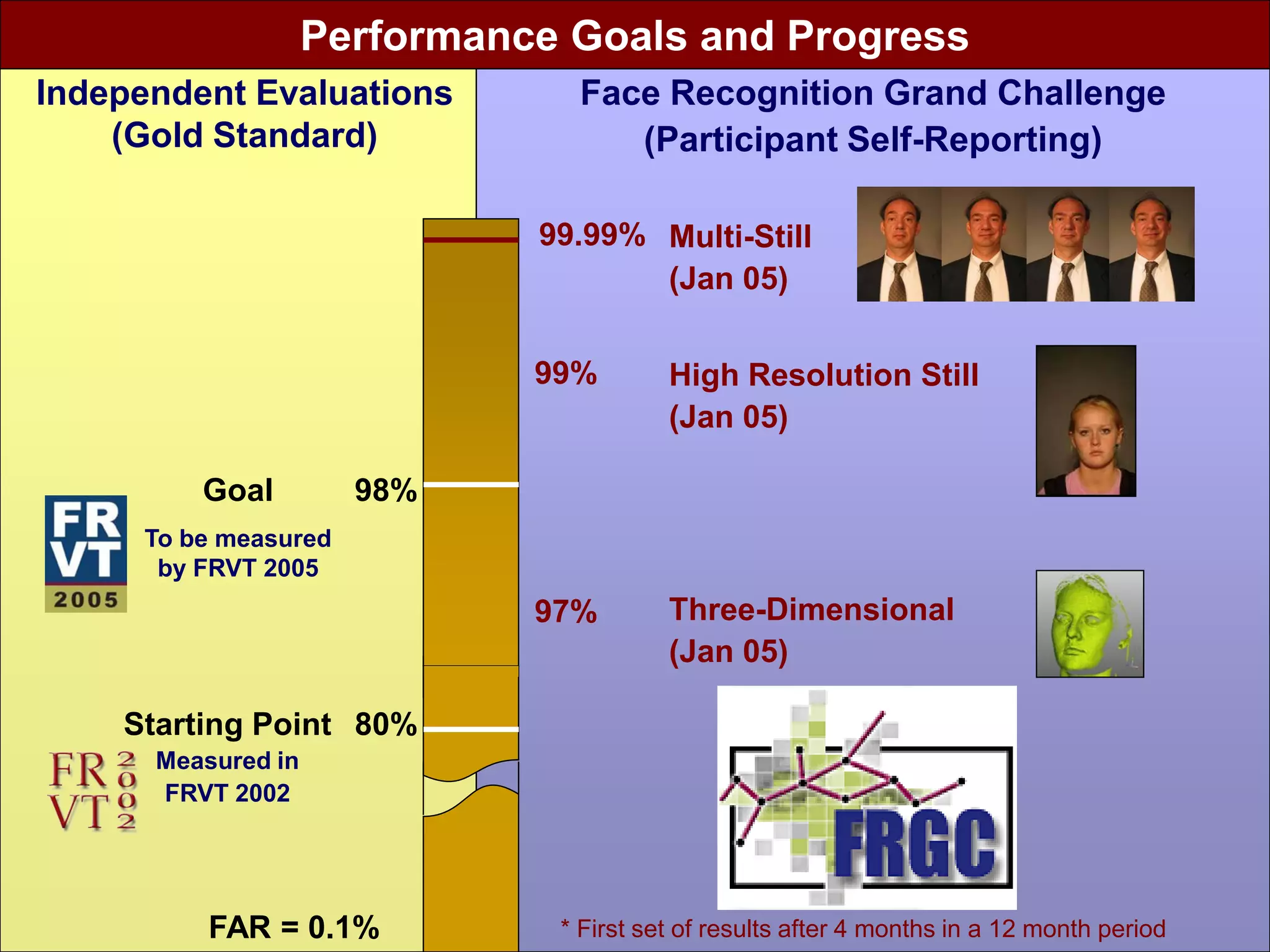
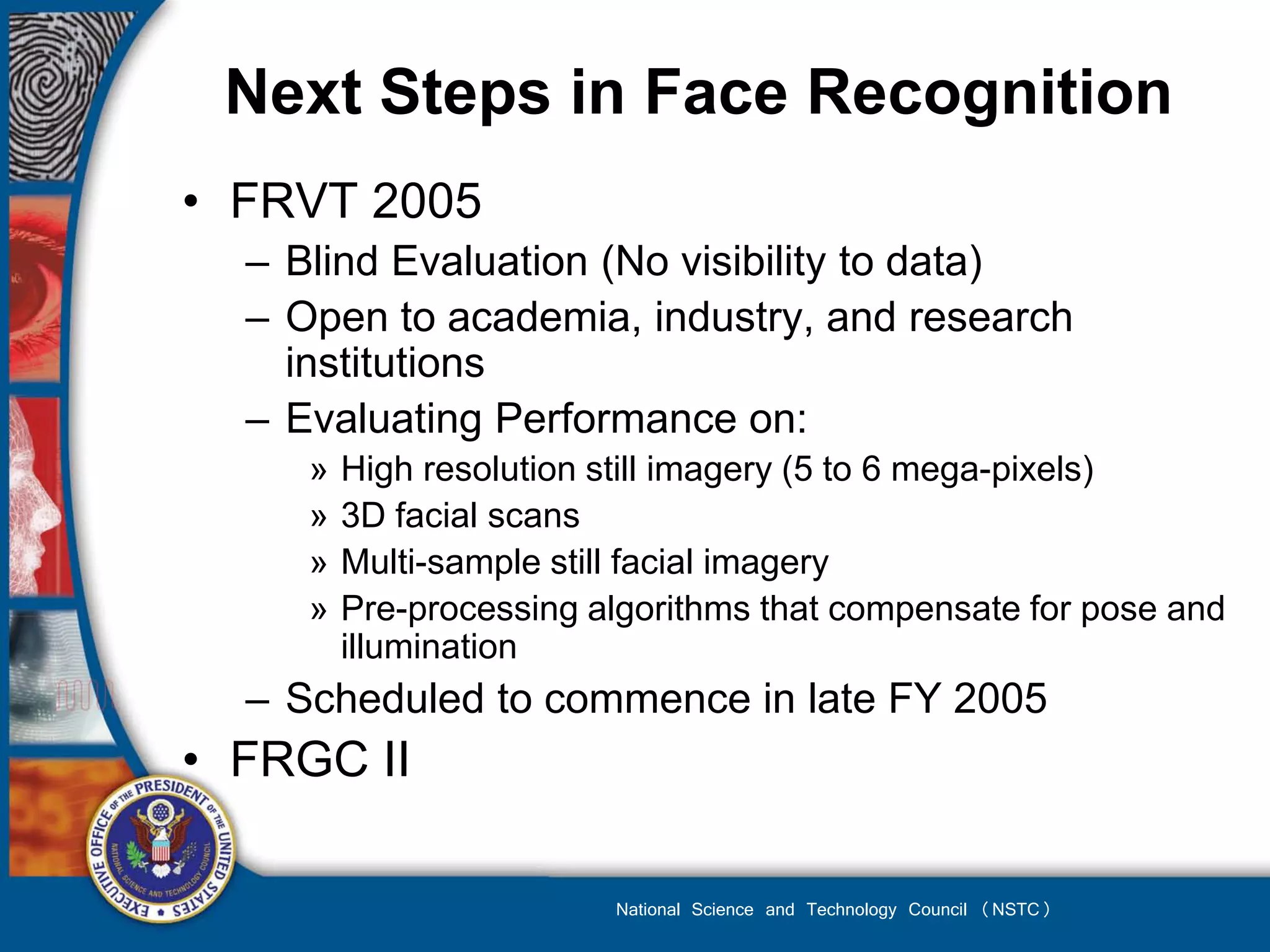
The document outlines the use of biometrics across various U.S. government departments, including the Department of Homeland Security, Department of Justice, and the Department of Defense, emphasizing their role in identity verification, investigation, security, and enforcement. It details operational needs, recent advancements, and collaborative efforts for enhancing biometric technologies and standards. Overall, it highlights the critical role of biometrics in national security and law enforcement to effectively track individuals and manage security threats.