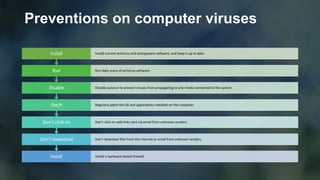
This document discusses computer viruses, including how they spread, different types of viruses, signs of infection, preventions, and virus removal. It defines a computer virus as malicious code that replicates by copying itself to another program or document. The document outlines several types of viruses like file infectors, macro viruses, overwrite viruses, and boot sector viruses. It also provides tips for preventing virus infection through firewalls, patching, and antivirus software, as well as steps for removing a virus through safe mode and virus scanning.