Etching
•Download as PPT, PDF•
2 likes•2,493 views
Report
Share
Report
Share
Recommended
Typesetting services

Typesetting is the process of organizing or arranging physical types, stored fonts & other type of symbols for visual display purpose. The method of Typesetting includes the method of outlining a textual style. The requirement for Typesetting Services is on the high and numerous Publishing organizations have begun understanding the criticalness of Typesetting Services. Now with the technological advancement Typesetting industry has reached to a new level with the growth of digitization. Companies like iSolve Technologies offers best in class Digital Typesetting Services to leading publishing companies in the world.
Abstract Sculpture - Wire and Panty Hose Sculptures

Art AQ Submission, July 7, 2014
Lindsay Lougheed
**If you download this you will be able to see reference information for the sculptures in the notes part.
This PowerPoint provides examples of Wire and Panty Hose Sculptures.This PowerPoint includes a pre-lesson to for some analysis and reflection of other artist’s abstract work. After showing my students the PowerPoint and having a discussion about Abstract Art, I would demonstrate how to actually create the sculpture (the instructions are in the PowerPoint). The students would then spend the next few days creating and painting their sculptures.
Recommended
Typesetting services

Typesetting is the process of organizing or arranging physical types, stored fonts & other type of symbols for visual display purpose. The method of Typesetting includes the method of outlining a textual style. The requirement for Typesetting Services is on the high and numerous Publishing organizations have begun understanding the criticalness of Typesetting Services. Now with the technological advancement Typesetting industry has reached to a new level with the growth of digitization. Companies like iSolve Technologies offers best in class Digital Typesetting Services to leading publishing companies in the world.
Abstract Sculpture - Wire and Panty Hose Sculptures

Art AQ Submission, July 7, 2014
Lindsay Lougheed
**If you download this you will be able to see reference information for the sculptures in the notes part.
This PowerPoint provides examples of Wire and Panty Hose Sculptures.This PowerPoint includes a pre-lesson to for some analysis and reflection of other artist’s abstract work. After showing my students the PowerPoint and having a discussion about Abstract Art, I would demonstrate how to actually create the sculpture (the instructions are in the PowerPoint). The students would then spend the next few days creating and painting their sculptures.
Michael Craig Martin

Michael Craig Martin, Flat colour painting, Still Life objects, KS3 Art homework
More Related Content
What's hot
Michael Craig Martin

Michael Craig Martin, Flat colour painting, Still Life objects, KS3 Art homework
What's hot (20)
Viewers also liked
Etching for Artists and Hackers: Printmaking & Circuit Boards

Etching is the process of using corrosive chemicals to cut into the unprotected parts of an object’s surface.
These slides explore the history of etching, intaglio printmaking, and the etching of circuit-boards.
Etching Process

This power point contains etching process and the needed materials for etching and also the type of etchants.
Printmaking

Printmaking is an indirect means of creating art by transferring an image or design by contact with a matrix such as a block, plate, stone, or screen.
Designing process of printed circuit boards

Most key element in electronic circuits and equipment’s is the Printed Circuit Board which connects electronic components with conductive lines printed
Viewers also liked (15)
Etching for Artists and Hackers: Printmaking & Circuit Boards

Etching for Artists and Hackers: Printmaking & Circuit Boards
KCC Art 211 Ch 8 Printmaking Ch 9 Camera Ch 10 graphic design

KCC Art 211 Ch 8 Printmaking Ch 9 Camera Ch 10 graphic design
Similar to Etching
Printmaking Techniques- Review theory

Conceptos básicos sobre grabado para la clase de artes visuales
Gundam Model Building: Fundamental Tools

Plan to spend about 30 hours. Then throw it out and purchase a replacement of identical proportions....
Similar to Etching (20)
Understand print-based media production techniques and technology

Understand print-based media production techniques and technology
More from missfcmay
More from missfcmay (20)
Recently uploaded
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Recently uploaded (20)
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Etching
- 2. Etching has been around for nearly 500 years. It is a type of engraving, where ink is forced through tiny lines and grooves that have been applied to a copper plate (or in our case plastic). A wet piece of paper is laid onto the plate and forced through a roller, which then creates a print. Originally etching was used to decorate armour in Medieval times. Decorated parts of the armour were filled in to give the designs a contrast. Etching is the print-making technique most closely associated with drawing.
- 3. Your first task… This week you need to create at least a double page on one artist who has created etchings. You can find your own Artist or use one on the Pinterest website: http://pinterest.com/beaumontart/ The page should include 1.Good quality images of the Artist’s work 2.Facts and opinions about the Artist (Use the ‘How to write about Artists’ sheet for support) 3.A transcription of the Artist’s work.
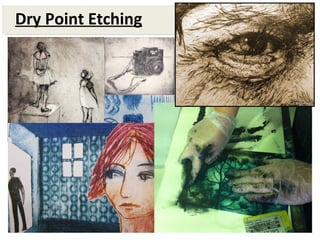
- 4. What is Dry Point Etching … Dry point etching is the modern equivalent to etching. It is called dry point because you create your image by scratching into a surface with a dry needle.
- 5. How to create a Dry Point Etching… 1. Draw into your plastic with a sharp needle. This is called intaglio which means cutting, carving or engraving into a flat surface. You can use lots of different mark-making techniques with the needle to create different tones and textures.
- 6. 2. You can create rubbings on your plastic from anything that has a raised surface. You create rubbings by using fine sandpaper. 3. You can cut out sections of your plastic to create white spaces and cut out your etchings and overlap them with other ones.
- 9. 4. You can also stick brown tape and masking tape onto your etching to create interesting textures like the examples below…
- 10. 5. When applying the etching ink it is recommended that you wear plastic gloves. First apply a thin layer of ink with a piece of cardboard. Drag it over your plastic. 6. Use a piece of fabric or tissue and push down and turn the ink. You want to make sure all your scratches are loaded with ink. 7. You can use newspaper or tissue paper to clean all ink off certain areas of your plastic.
- 11. 8. Spray cartridge paper evenly with water on both sides. Use paper fingers to pick up your paper so your don’t get any ink on it. 9. Sandwich your plastic (ink side up) with your wet paper on top between newspaper and put through the printing press. 10. Place your finished etching between paper and something heavy to make sure it dries flat.