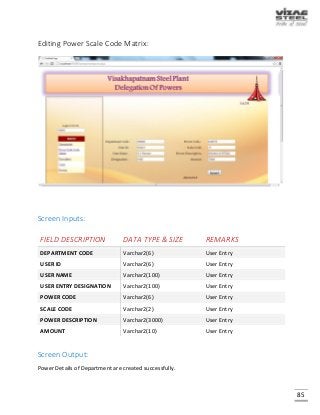
This document provides information about a project report submitted for a degree in computer science and engineering. The report focuses on creating awareness of enterprise resource planning (ERP) implementation and delegation of powers at Visakhapatnam Steel Plant in India. It discusses the introduction to VSP, ERP basics, necessary hardware, networking requirements, required software, and outlines a delegation of powers system to help employees understand their roles and responsibilities within the large ERP modules.



![8
INTRODUCTION TO VIZAG STEEL PLANT
Visakhapatnam Steel Plant (VSP) is the first coast based Steel Plant of India. It is located 16 KM
South West of the city of Destiny i.e. Visakhapatnam. Vizag Steel Plant has been conferred
NAVRATNA status on 17th November 2010. Founded in 1971, the company focuses on producing
value-added steel with the aid of modern technologies from Germany and Russia, VSP has an
installed capacity of 3 million Tonnes per annum of Liquid Steel and 2.656 million Tonnes of
saleable steel. VSP has become the first integrated Steel Plant in the country to be certified to all
the three international standards for quality (ISO-9001), for Environment Management (ISO-
14001) & for Occupational Health & Safety (OHSAS-18001). The certificate covers quality systems
of all Operational, Maintenance and Service units besides Purchase systems, Training and
Marketing functions spreading over 4 Regional Marketing Offices, 24 branch offices and stock
yards located all over the country. VSP exports Quality Pig Iron & Steel products' to Sri Lanka,
Myanmar, Nepal, Middle East, USA, China and South East Asia. RINL-VSP was awarded "Star
Trading House" status during 1997-2000. Having a total manpower of about 16,600 VSP has
envisaged a labor productivity of 265 Tonnes per man year of Liquid Steel.
RASHTRIYA ISPAT NIGAM LIMITED [RINL]
Rashtriya Ispat Nigam Limited, popularly known as ‘Vizag Steel’ the ‘Pride of Steel’, is a leading
Central PSU under the Ministry of Steel. It is also the first shore based Integrated Steel Plant in
the country.
Its products are made from 100% virgin steel, maintaining stringent tolerances both in chemical
& physical properties. It has been supplying various grades of steel for construction of projects
of National importance which include Metros, Power Sector, Bridges, Nuclear complexes and
several others. RINL‐VSP has a wide marketing network spread across the country and is the
“preferred steel maker” for the customers.](https://image.slidesharecdn.com/429c0759-5689-4030-b685-1ec3a9ffc1f1-151214174304/85/ERP-9-320.jpg)