Enhancing Iran's Cybersecurity: Strategic Measures and Challenges
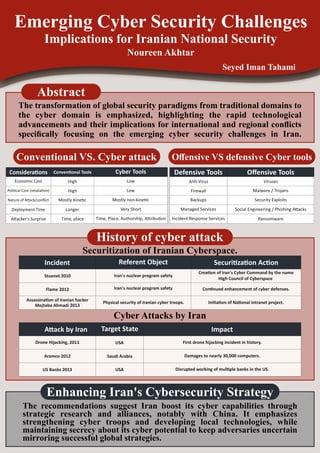
- 1. Emerging Cyber Security Challenges Implications for Iranian National Security Noureen Akhtar Seyed Iman Tahami Abstract The transformation of global security paradigms from traditional domains to the cyber domain is emphasized, highlighting the rapid technological advancements and their implications for international and regional conflicts specifically focusing on the emerging cyber security challenges in Iran. Conventional VS. Cyber attack Offensive VS defensive Cyber tools History of cyber attack Securitization of Iranian Cyberspace. Cyber Attacks by Iran The recommendations suggest Iran boost its cyber capabilities through strategic research and alliances, notably with China. It emphasizes strengthening cyber troops and developing local technologies, while maintaining secrecy about its cyber potential to keep adversaries uncertain mirroring successful global strategies. Incident Referent Object Securi za on Ac on Stuxnet 2010 Flame 2012 Assassina on of Iranian hacker Mojtaba Ahmadi 2013 Iran's nuclear program safety Iran's nuclear program safety Physical security of Iranian cyber troops. Crea on of Iran's Cyber Command by the name High Council of Cyberspace Con nued enhancement of cyber defenses. Ini a on of Na onal Intranet project. A ack by Iran Target State Impact Drone Hijacking, 2011 Aramco 2012 US Banks 2013 USA Saudi Arabia USA First drone hijacking incident in history. Damages to nearly 30,000 computers. Disrupted working of mul ple banks in the US. Defensive Tools An -Virus Firewall Backups Managed Services Incident Response Services Offensive Tools Viruses Malware / Trojans Security Exploits Social Engineering / Phishing A acks Ransomware Conven onal Tools High High Mostly Kine c Longer Time, place Cyber Tools Low Low Mostly non-kine c Very Short Time, Place, Authorship, A ribu on Considera ons Economic Cost Poli cal Cost (retalia on) Nature of A ack/conflict Deployment Time A acker's Surprise Enhancing Iran's Cybersecurity Strategy