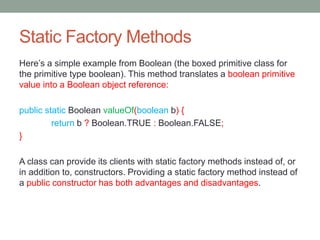
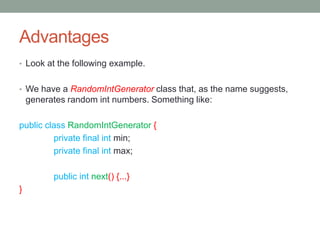
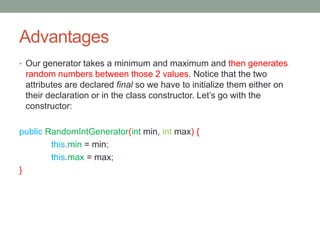
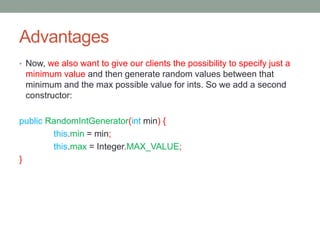
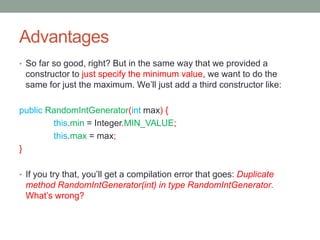
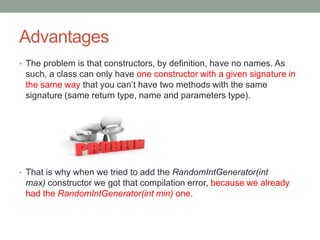
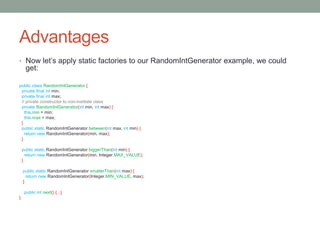
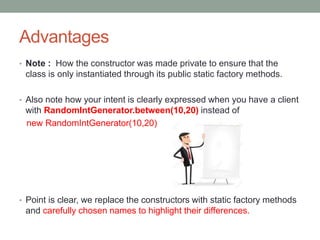
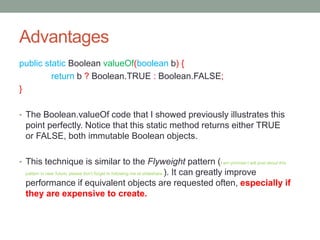
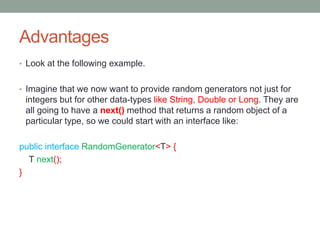
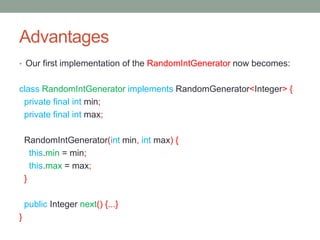
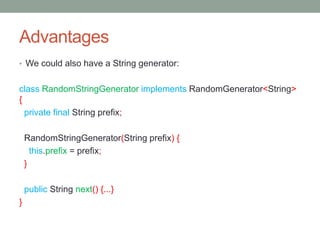
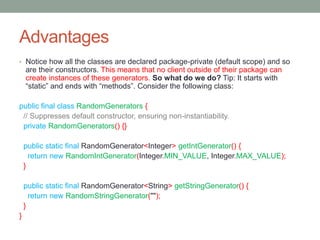
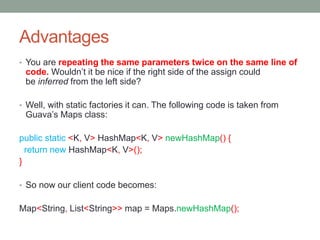
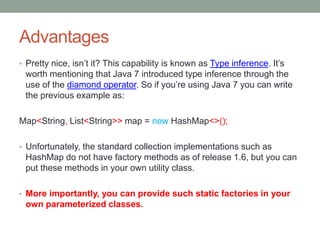
Static factory methods have several advantages over constructors for creating object instances, such as returning immutable objects or objects of subclasses. They allow returning an object of any subtype, have named methods instead of anonymous constructors, and can reduce verbosity for parameterized types. Some examples include Boolean.valueOf() and factory methods in the RandomGenerators class.