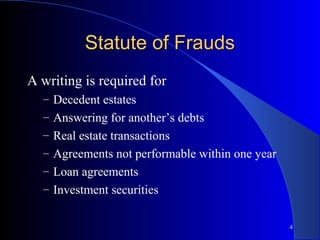
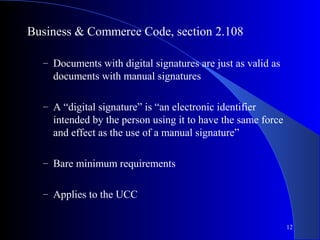
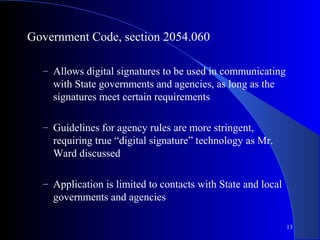
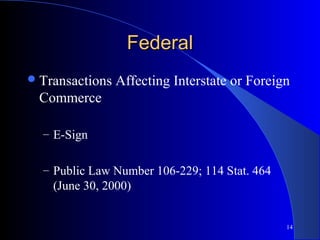
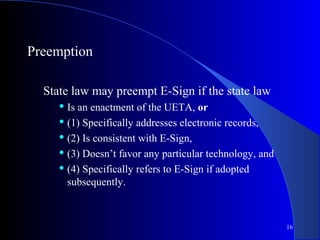
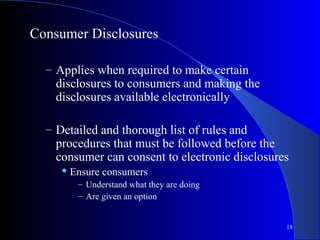
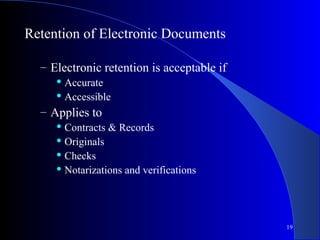
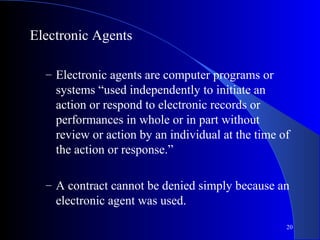
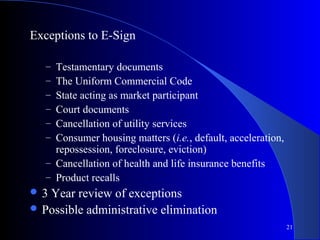
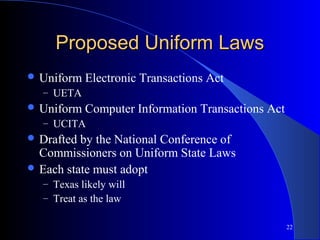
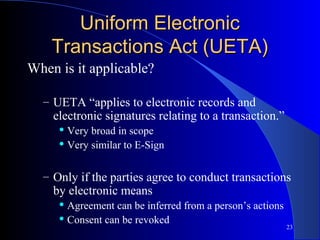
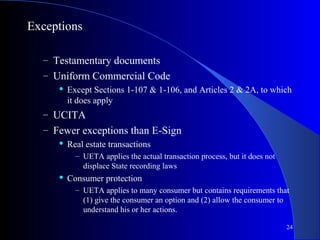
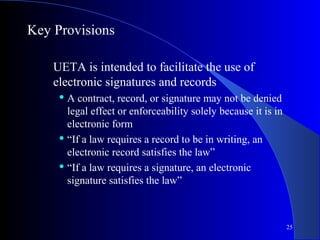
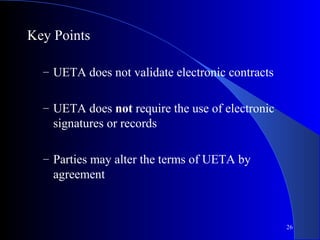
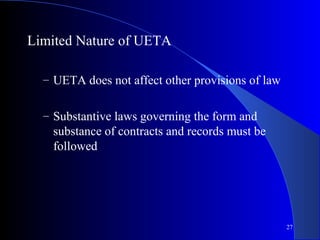
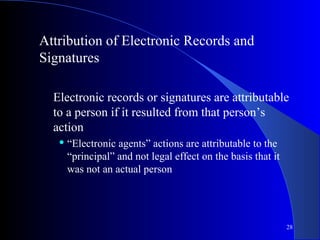
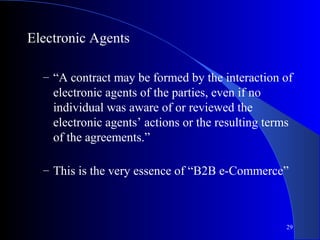
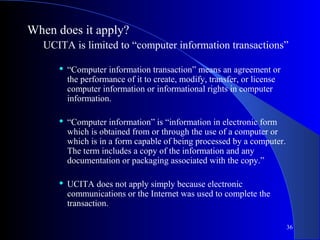
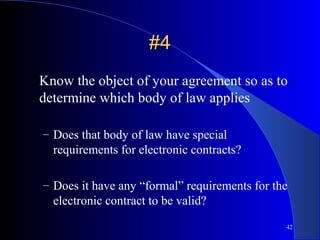
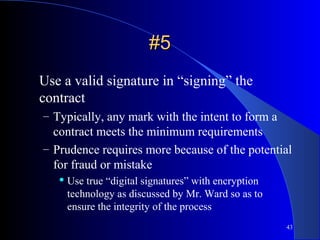
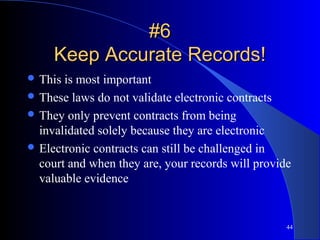
The document outlines essential information regarding e-contracting, emphasizing that it is a tool for all businesses and not just for online entities. It discusses the legal frameworks, such as the Uniform Electronic Transactions Act and E-SIGN, that govern electronic contracts, highlighting key provisions, exceptions, and the role of electronic signatures. Additionally, the document notes the importance of understanding traditional contract laws and maintaining accurate records to ensure enforceability in electronic transactions.