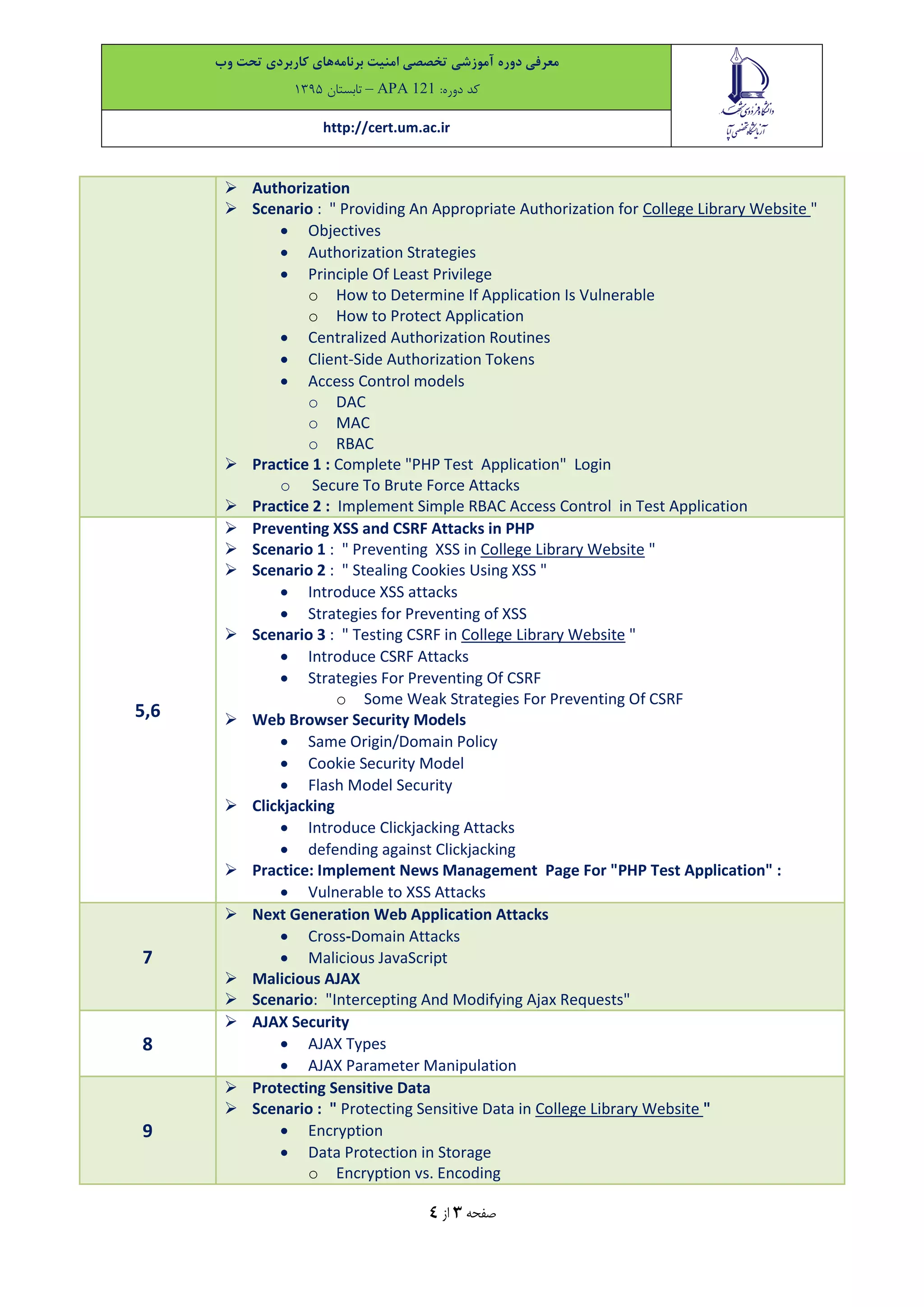
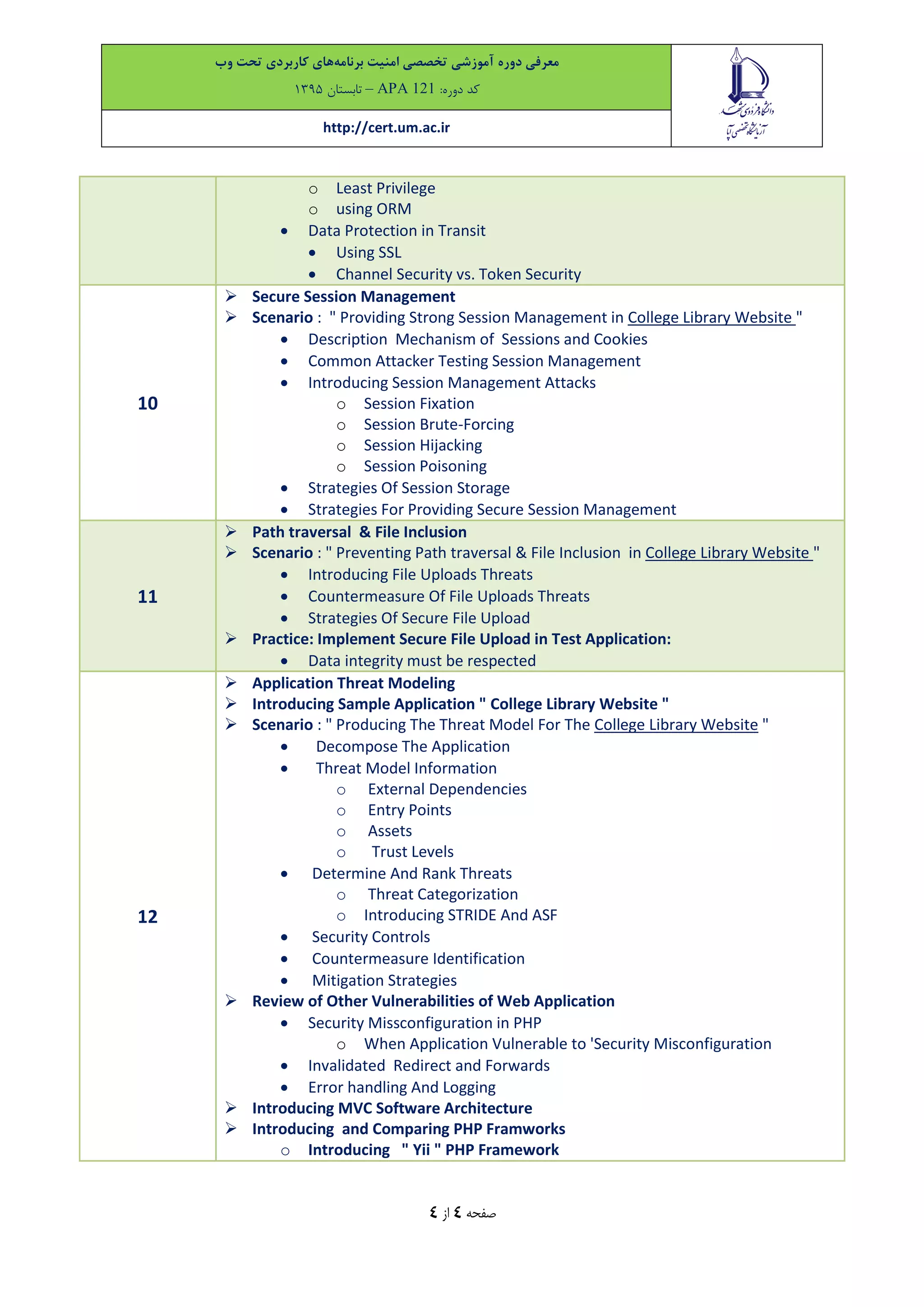
This document describes a 24-hour specialized training course on web application security in PHP. The course syllabus covers topics such as web application architecture, HTTP protocol, common vulnerabilities, SQL injection, authentication strategies, authorization, XSS and CSRF prevention, session management, file uploads, threat modeling and more. The target audience are web application developers and the course will help participants learn how to develop secure PHP applications. It provides examples of vulnerable code and practices for securing code against common attacks.