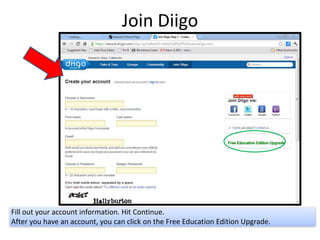
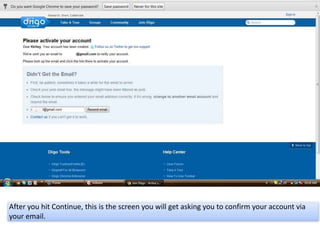
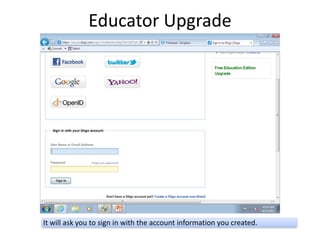
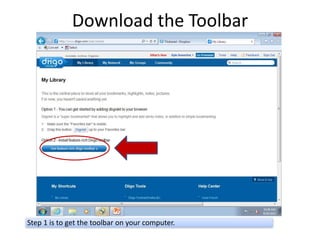
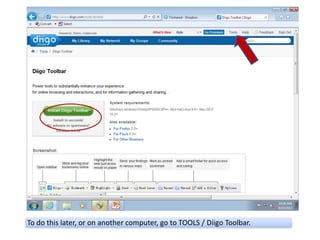
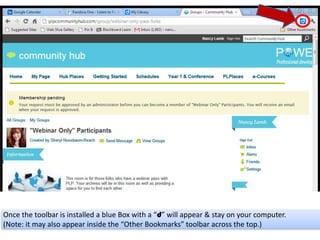
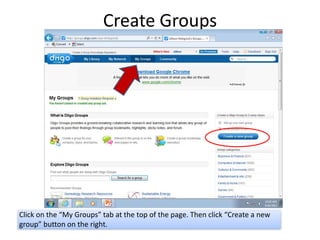
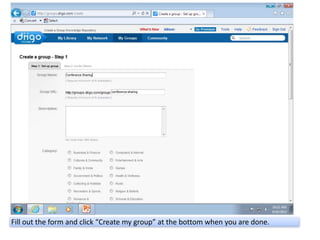
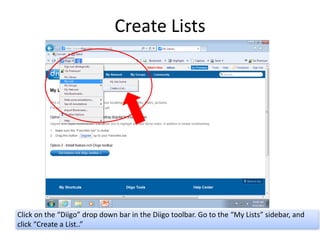
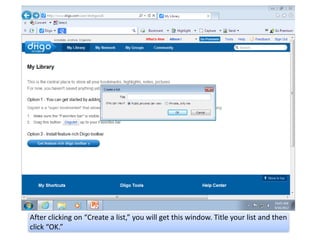
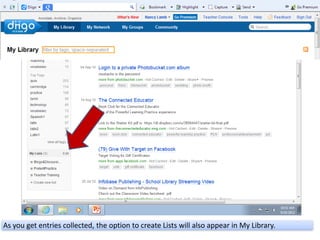
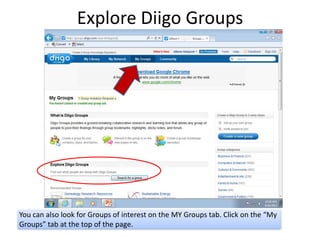
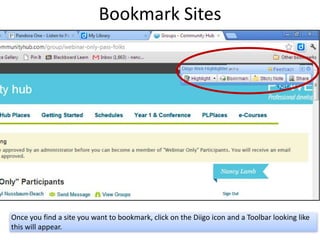
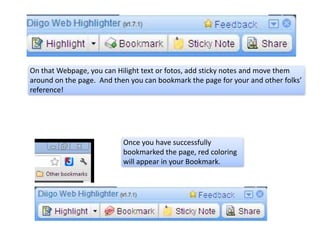
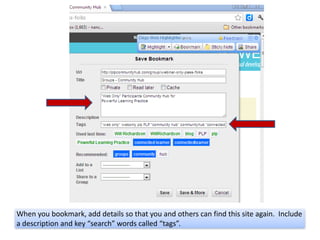
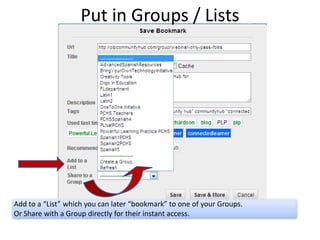
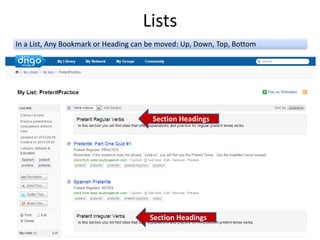
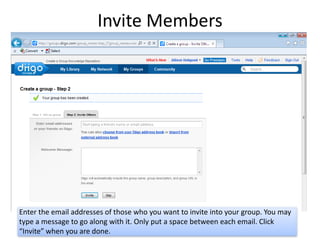
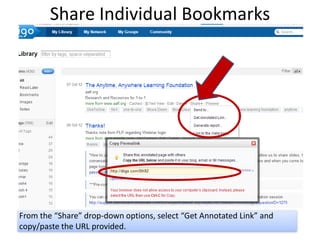
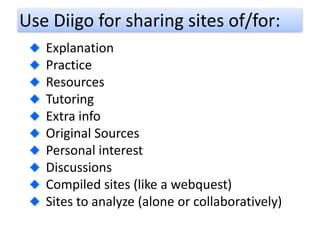
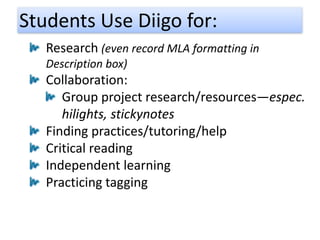
The document outlines the basics of using Diigo, including account creation, advantages for educators, and features like bookmarking, creating groups, and lists. It emphasizes Diigo's role in enhancing active reading, project-based learning, and collaboration between students and teachers. Users can also explore groups of interest and share resources effectively through the platform.