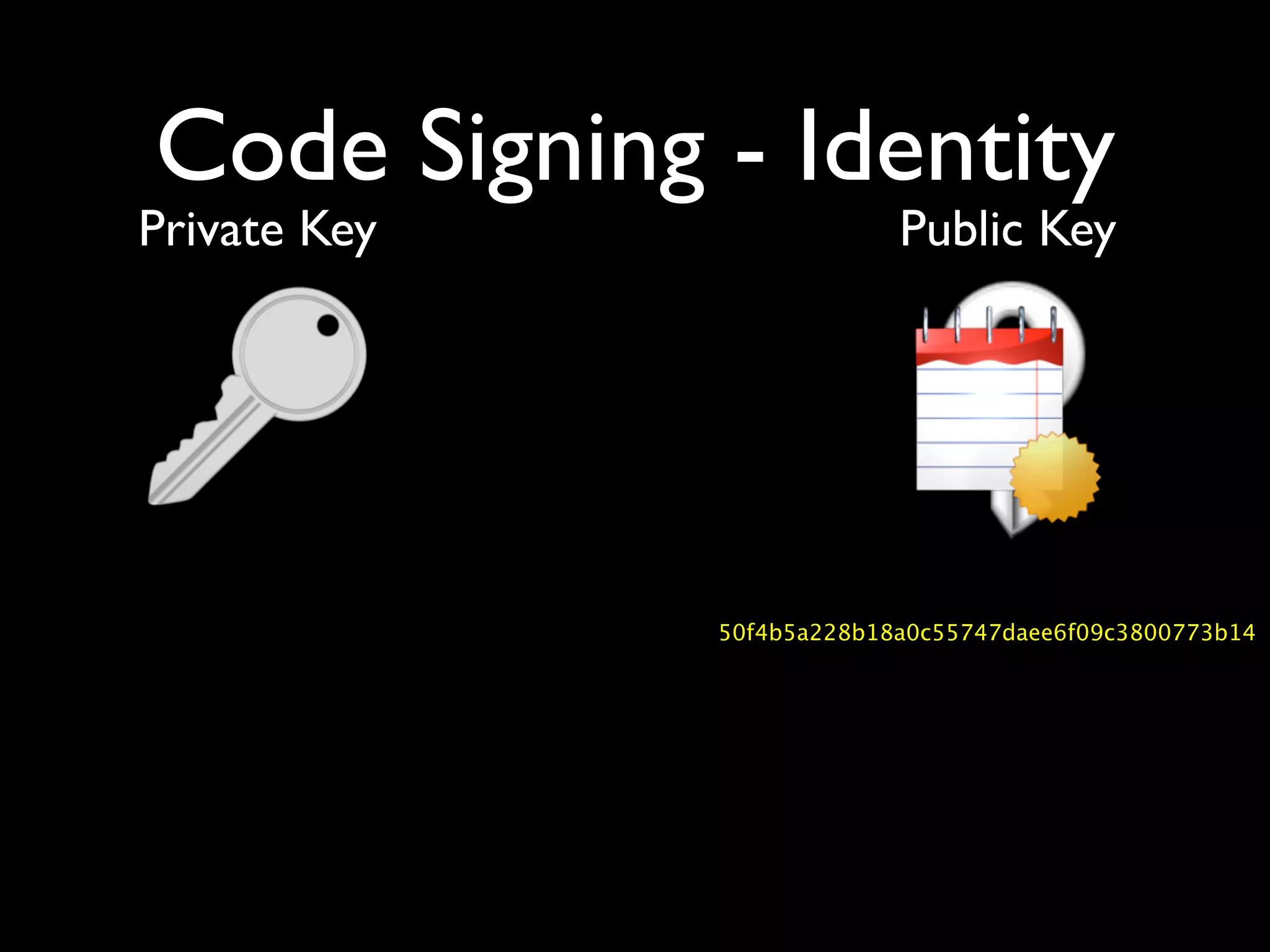
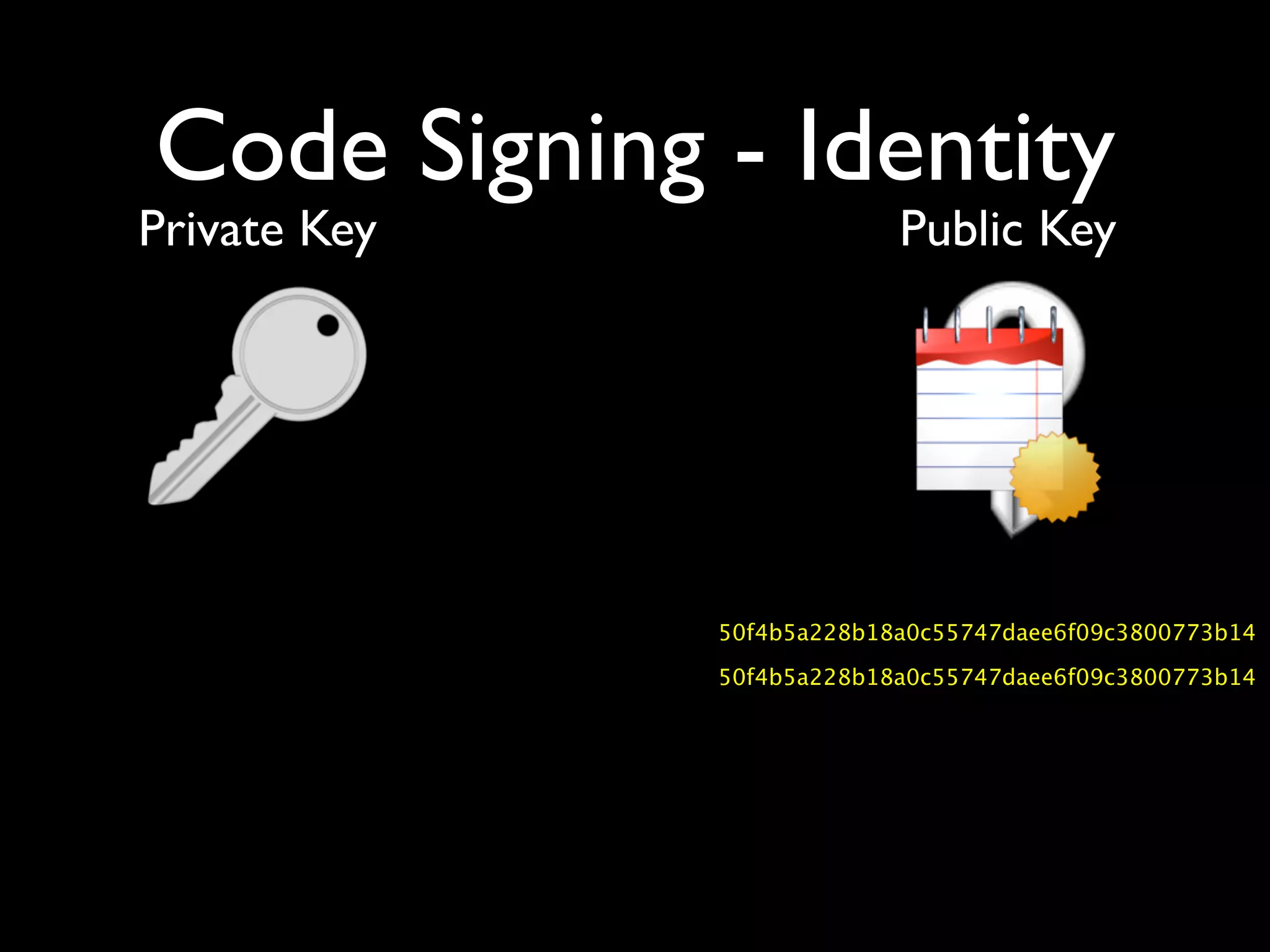
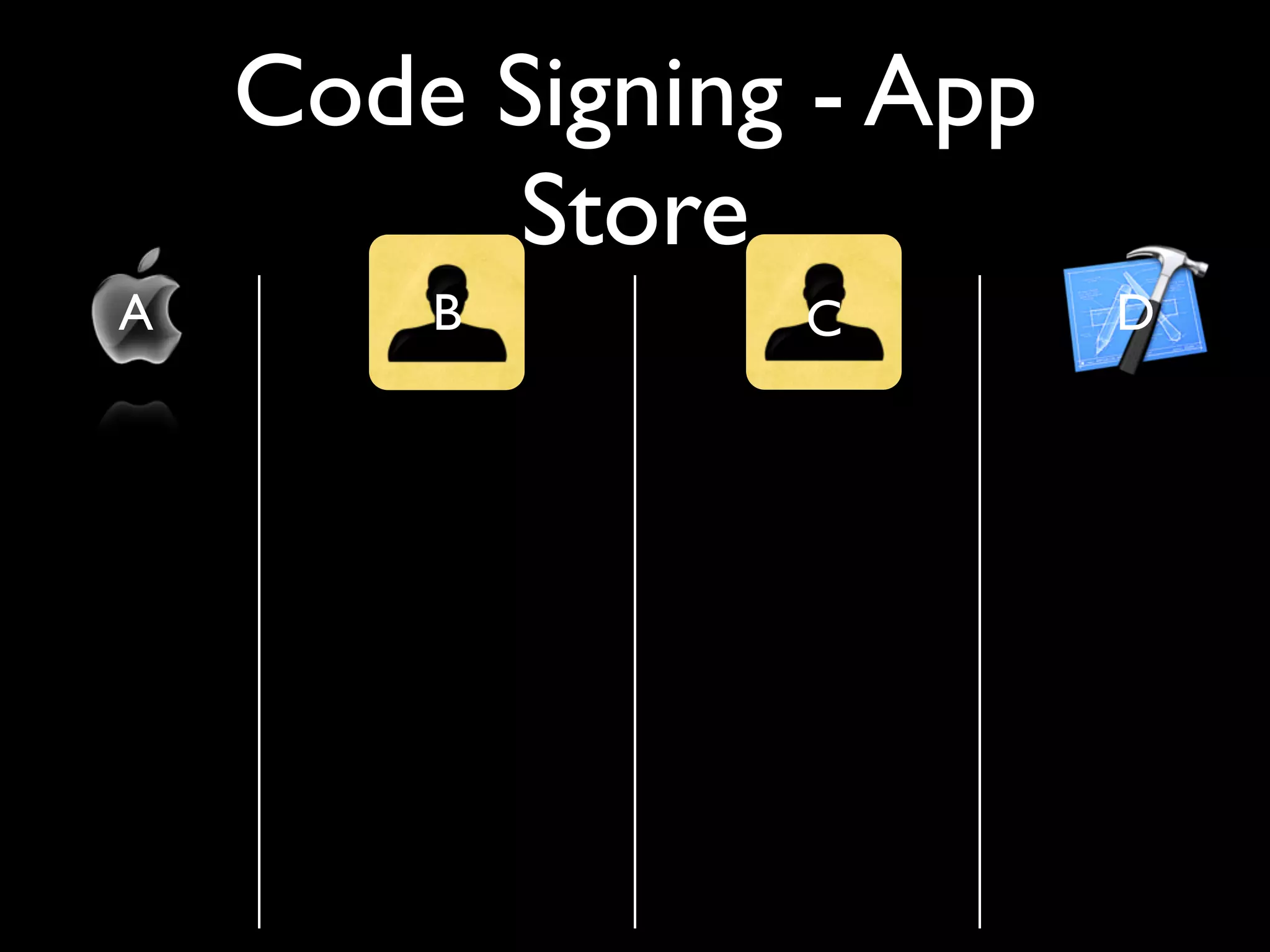
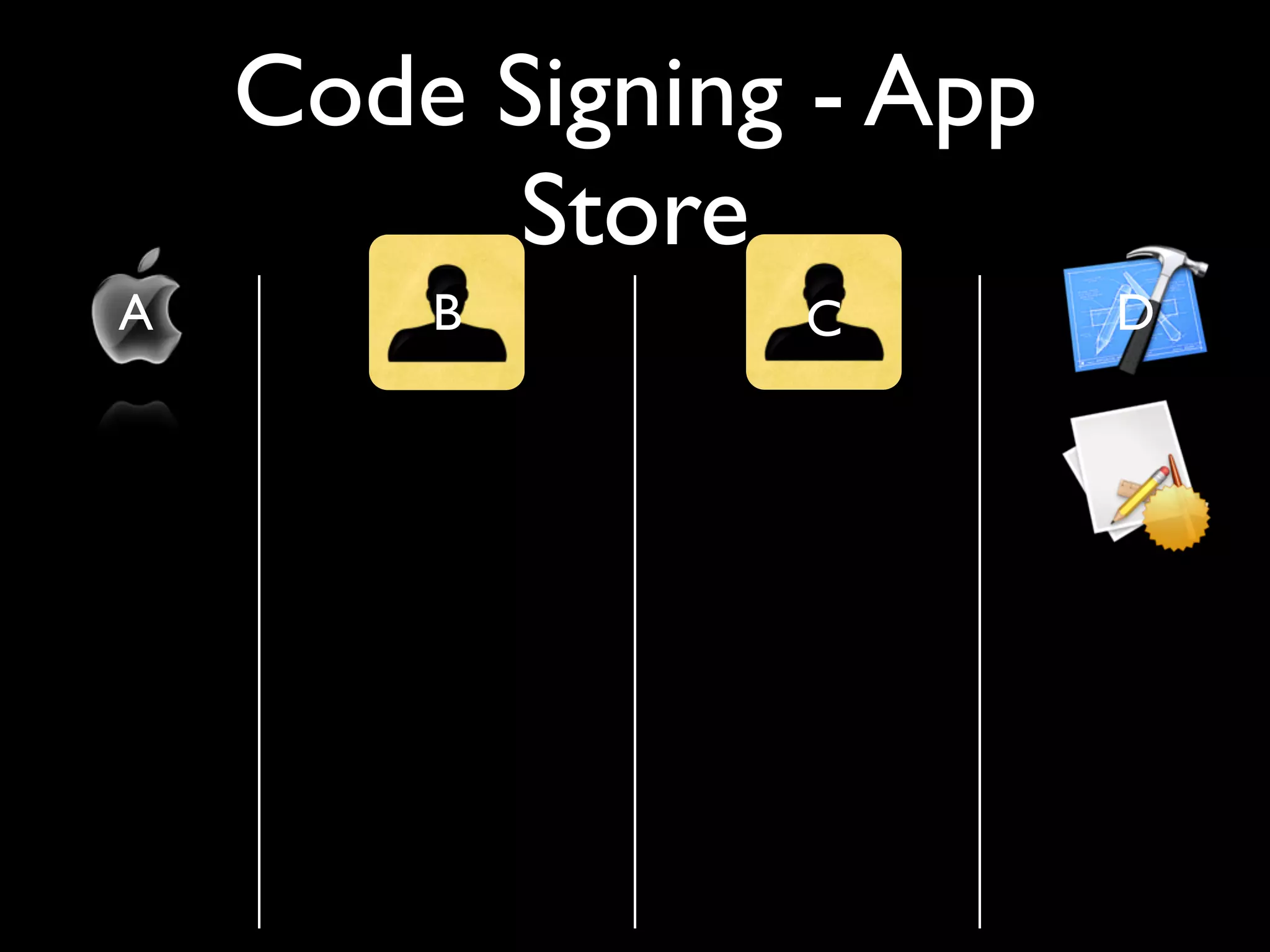
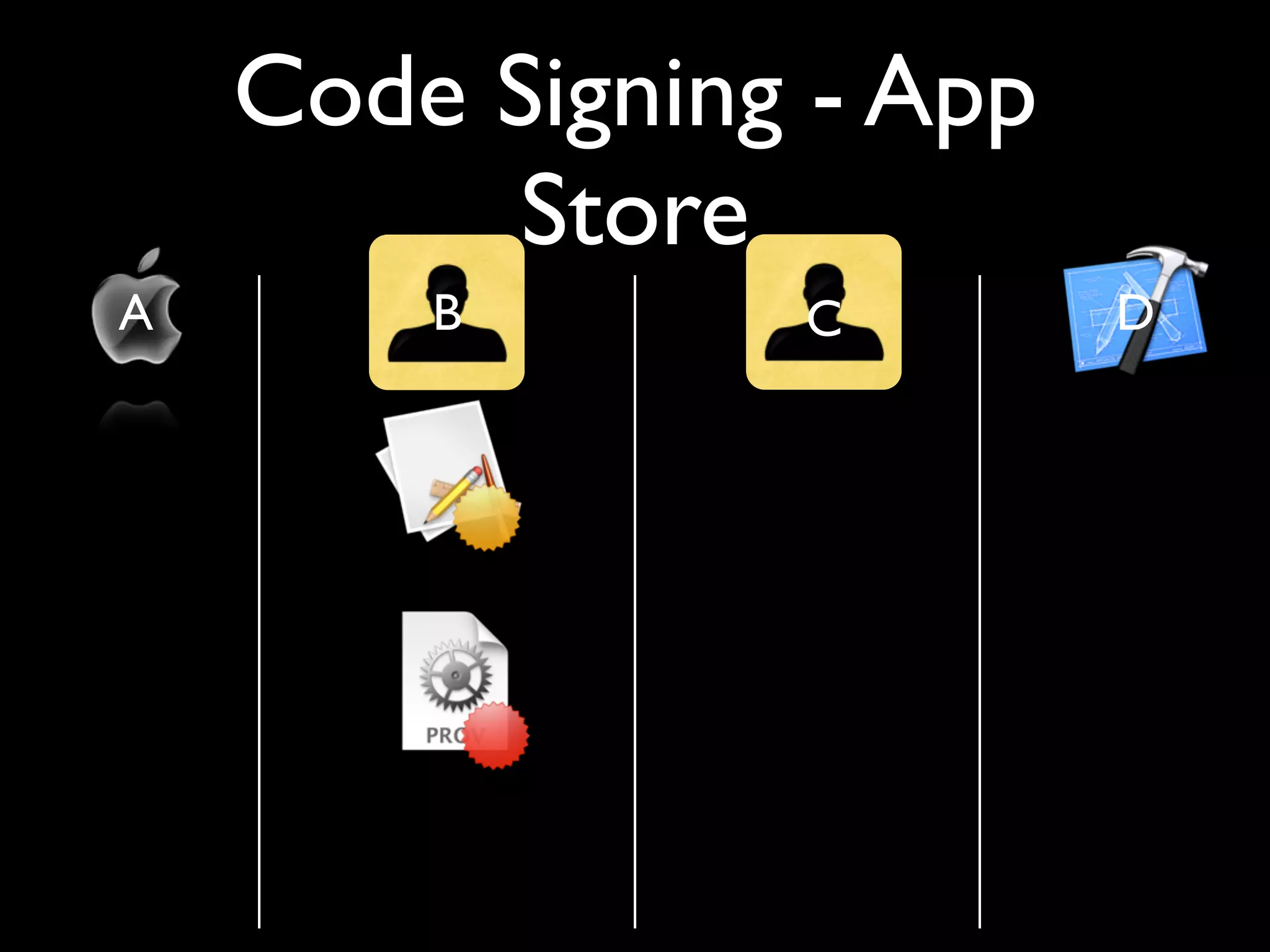
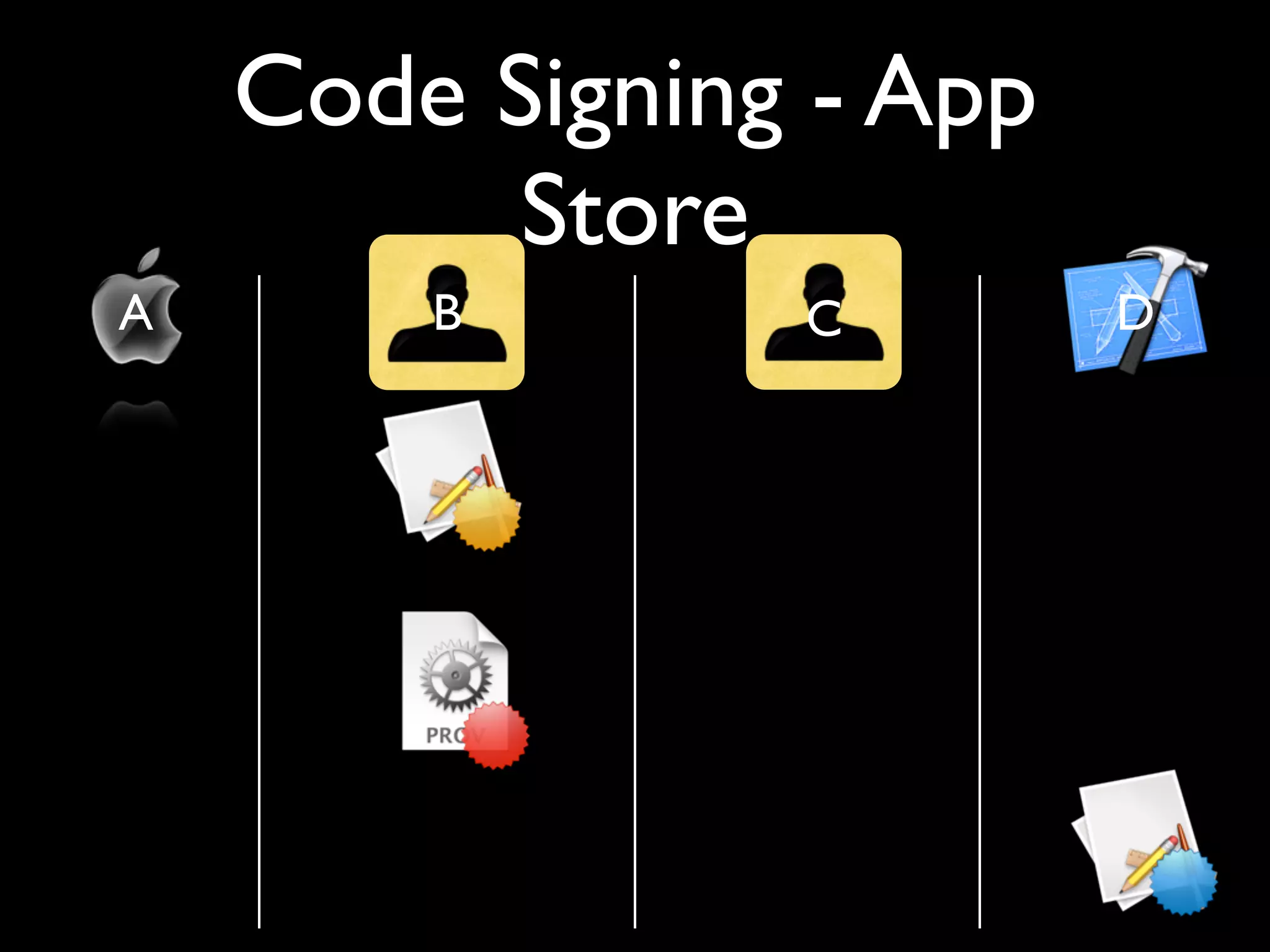
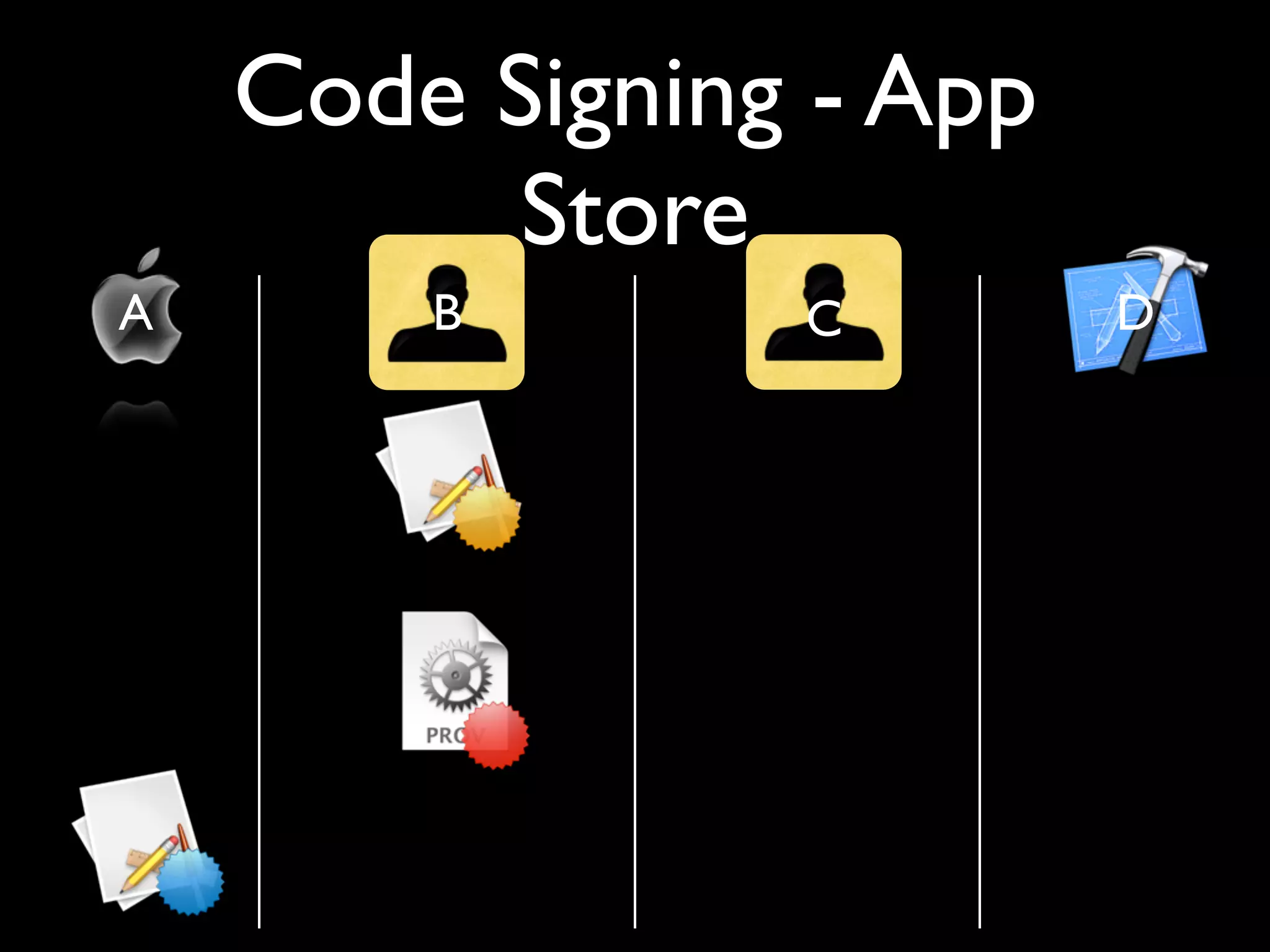
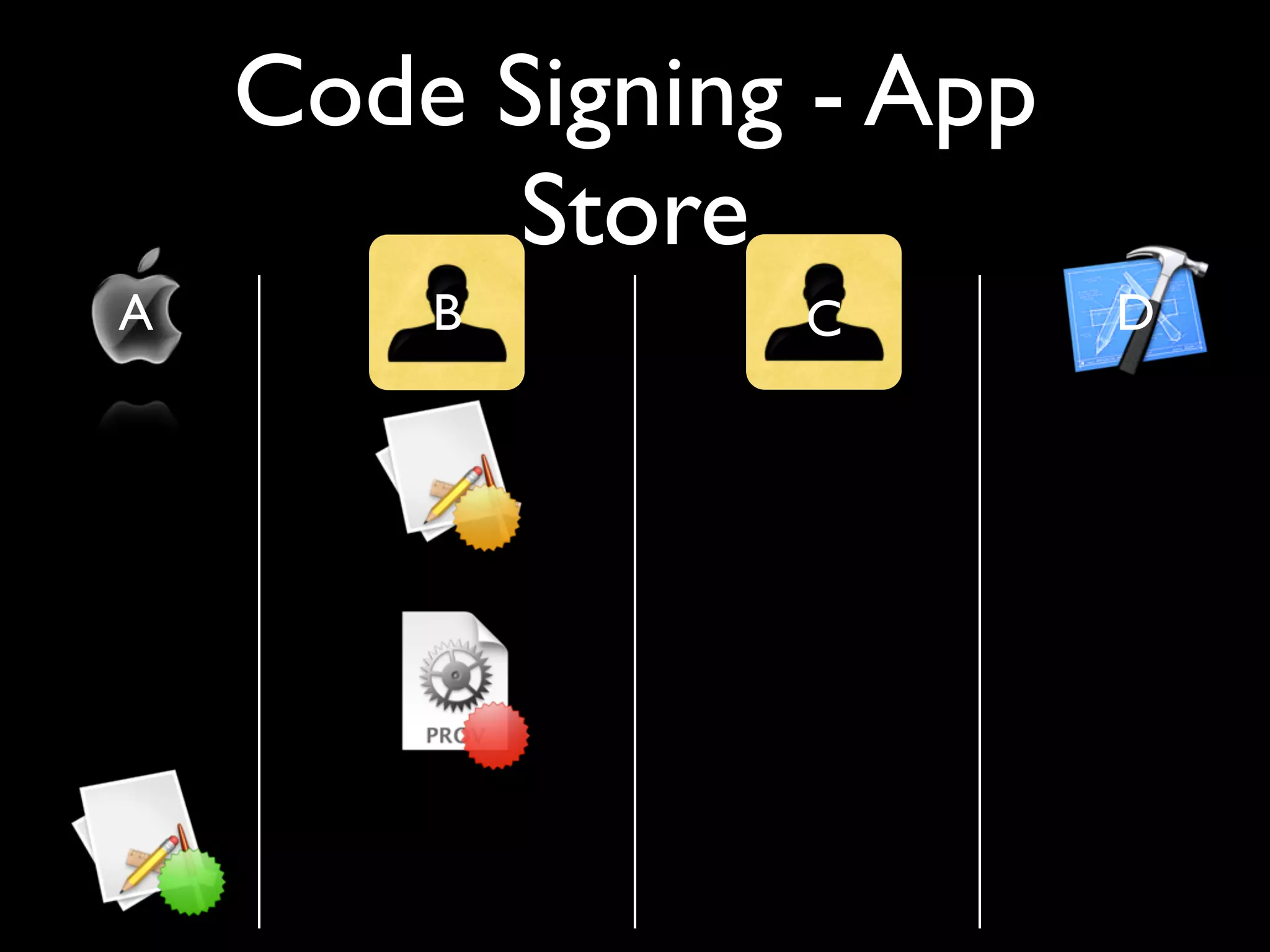
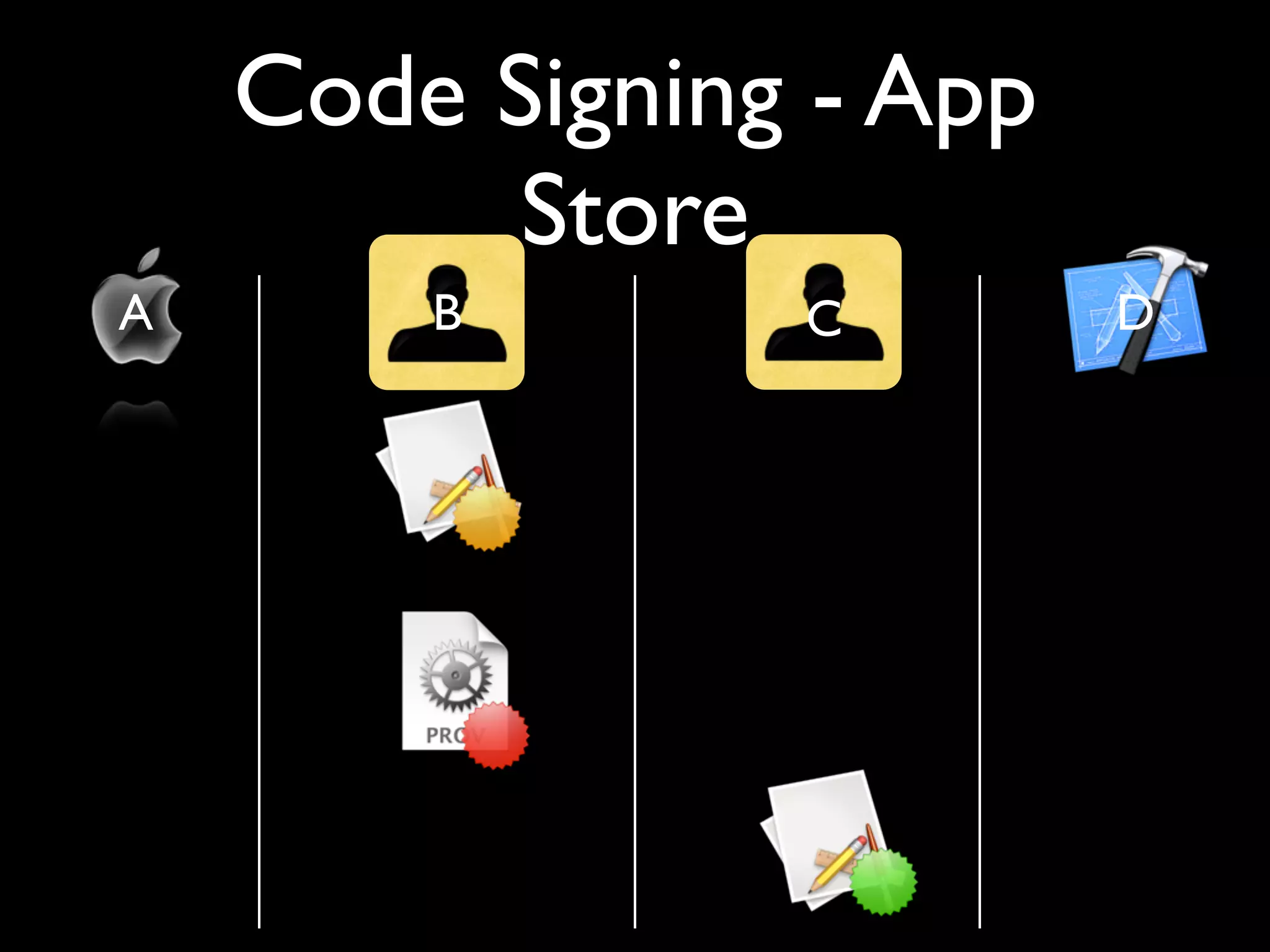
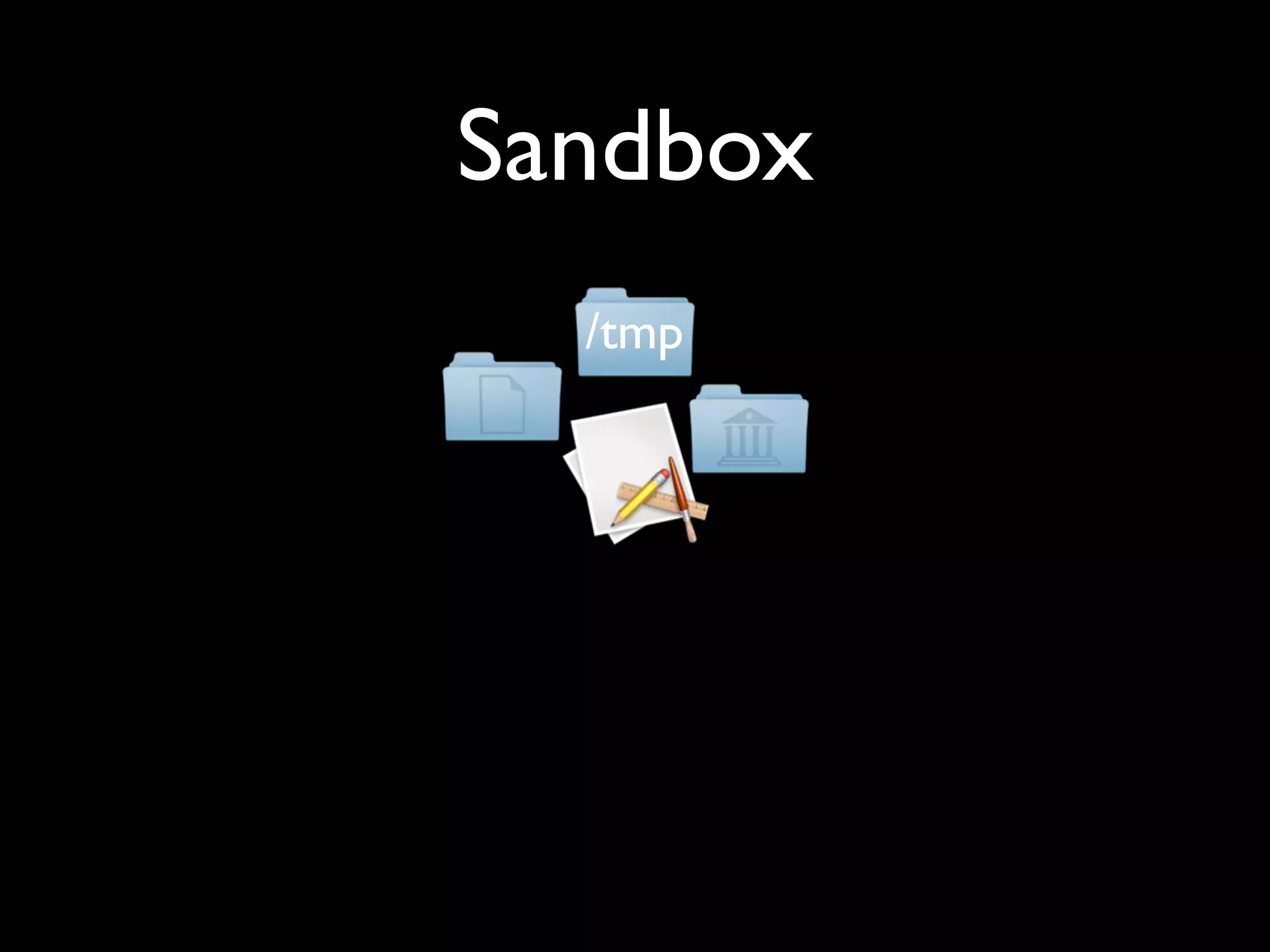
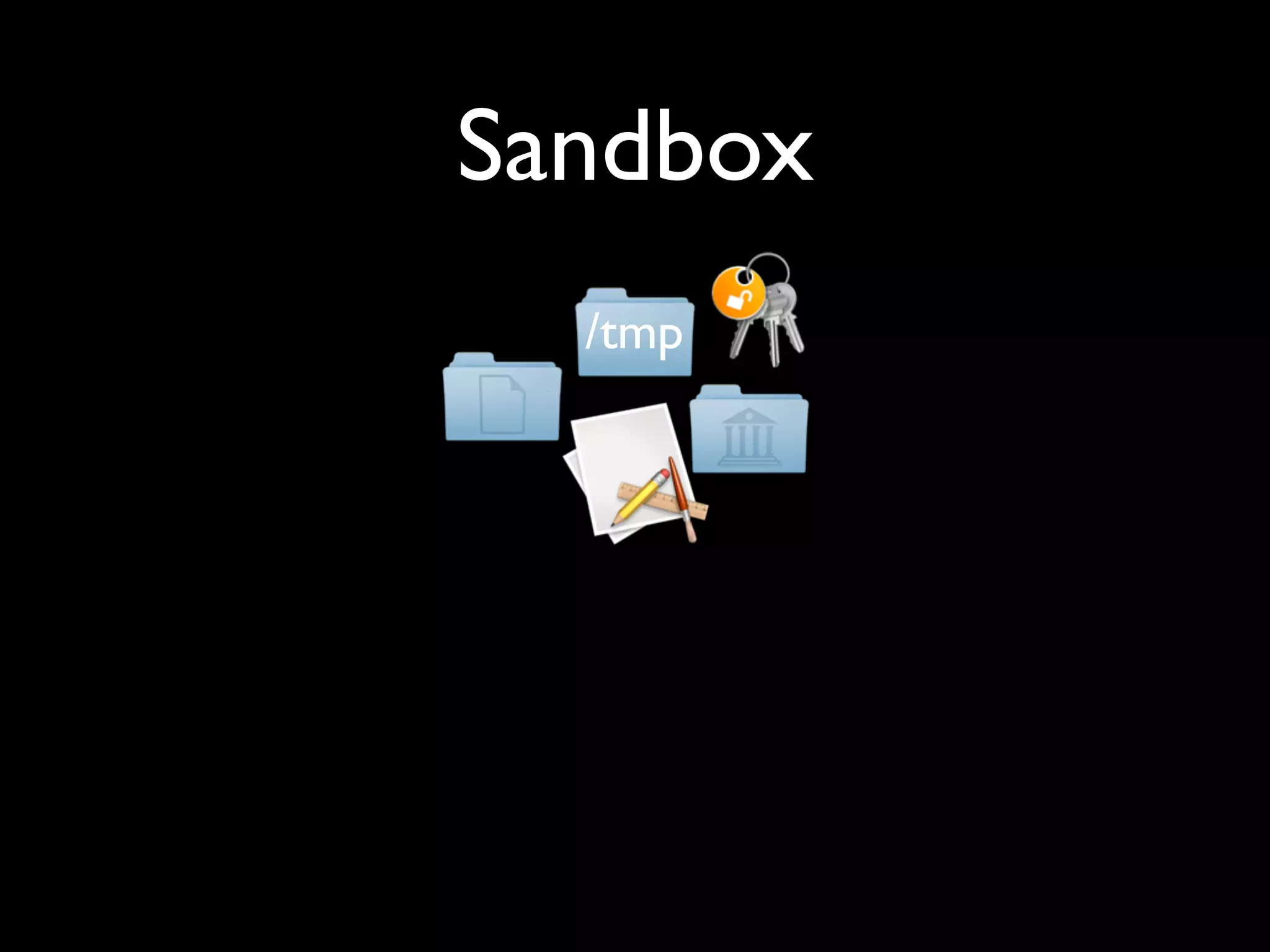
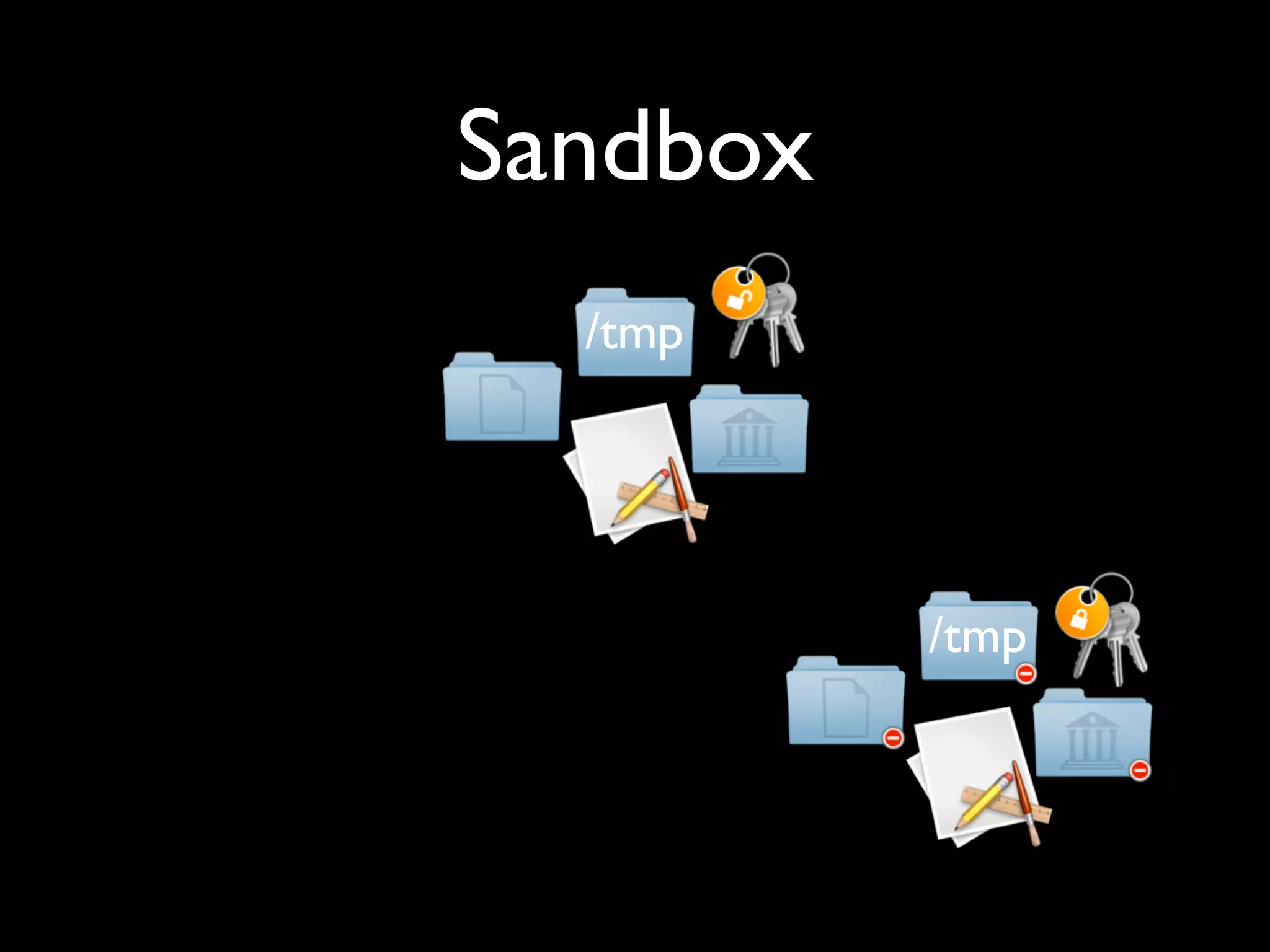
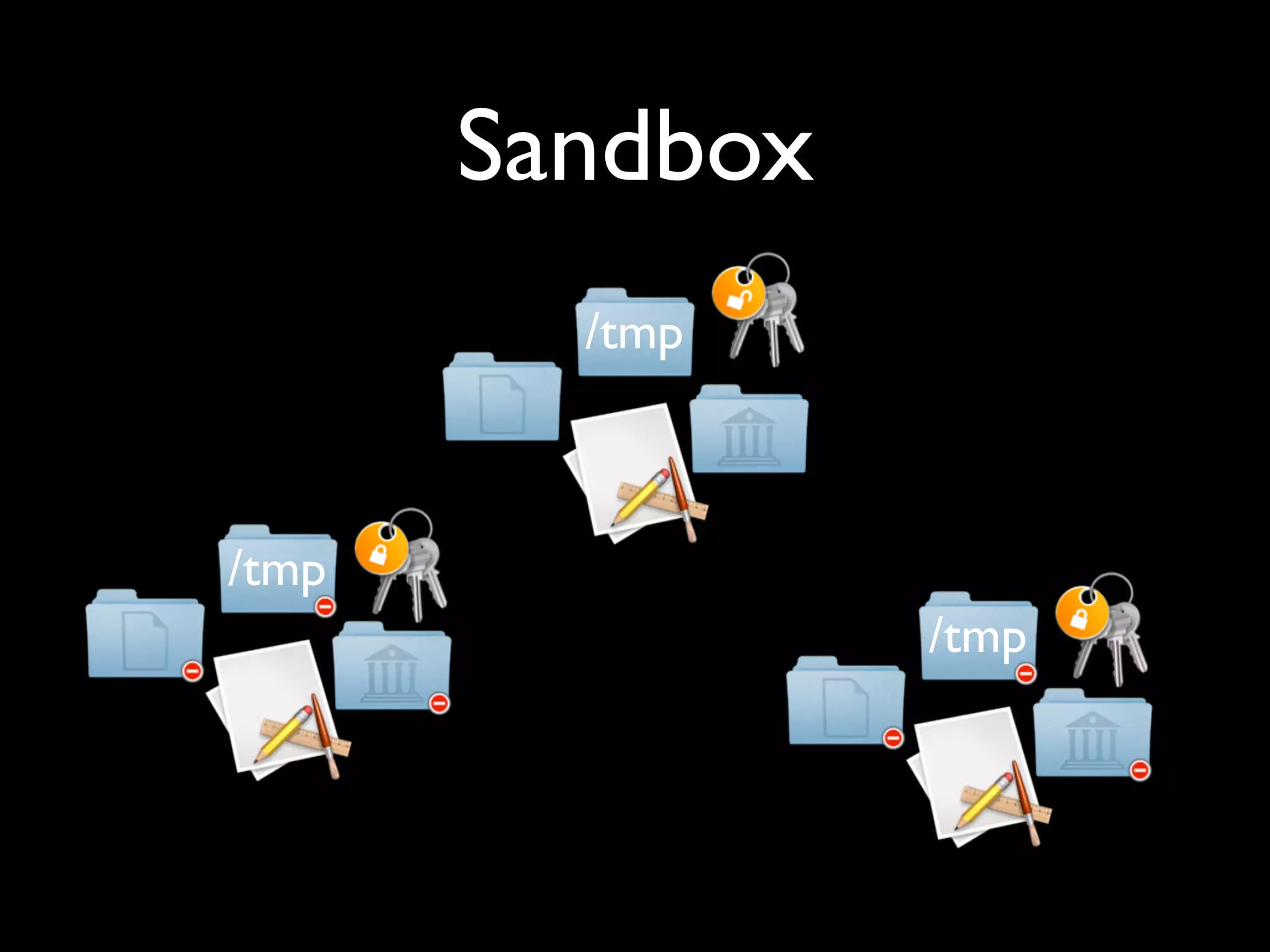
The document discusses code signing processes, emphasizing the importance of managing identities, private keys, and public keys for application signing, particularly for 'mygreatapp.ipa.' It also references requirements for code signing and mentions the use of keychain services for managing passwords, certificates, and data within a sandbox environment.