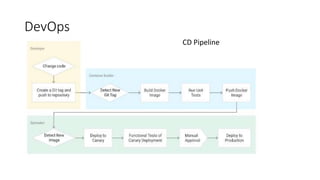
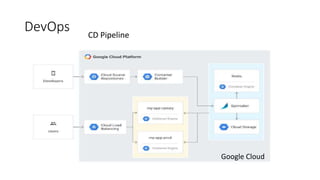
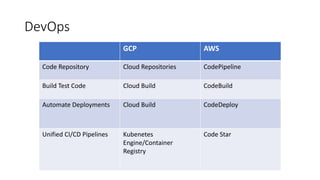
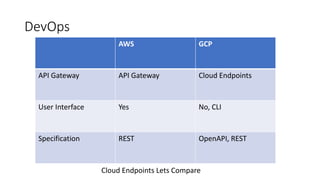
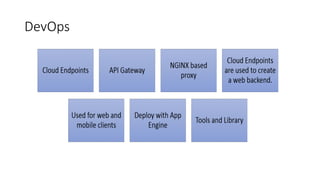
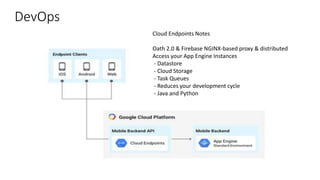
The document discusses DevOps as an agile relationship between development and IT operations, emphasizing improved communication and collaboration. It outlines tools and services available on Google Cloud Platform (GCP) for continuous integration, delivery, and deployment, comparing them to AWS offerings, and highlighting differences in API management. GCP's support for DevOps is presented as similar to AWS, with specific tools like Cloud Build, Container Registry, and Cloud Endpoints facilitating efficient workflows.