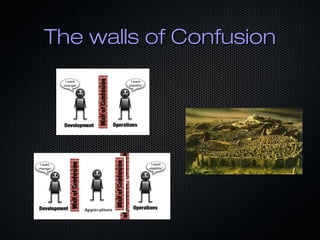
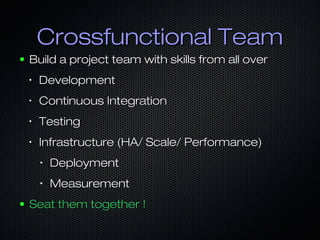
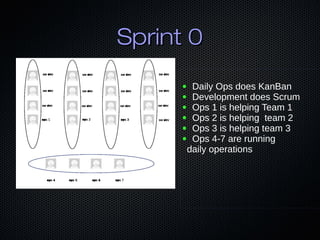
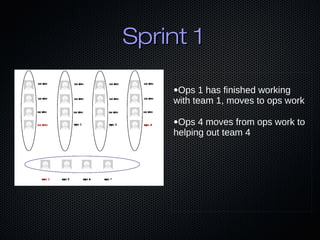
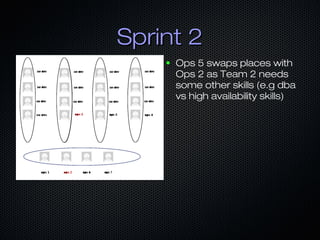
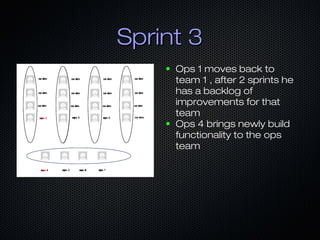
Devops is a reorganization of development and operations teams to promote collaboration. It breaks down barriers between teams by having developers and operations engineers work together in cross-functional teams throughout the development lifecycle. Traditional organizations separate development and operations into silos with opposing goals, while devops advocates for shared goals and responsibilities between teams through practices like automation, continuous integration, and measurement. Adopting a devops approach requires changing organizational culture and mindset rather than just implementing new tools or processes.