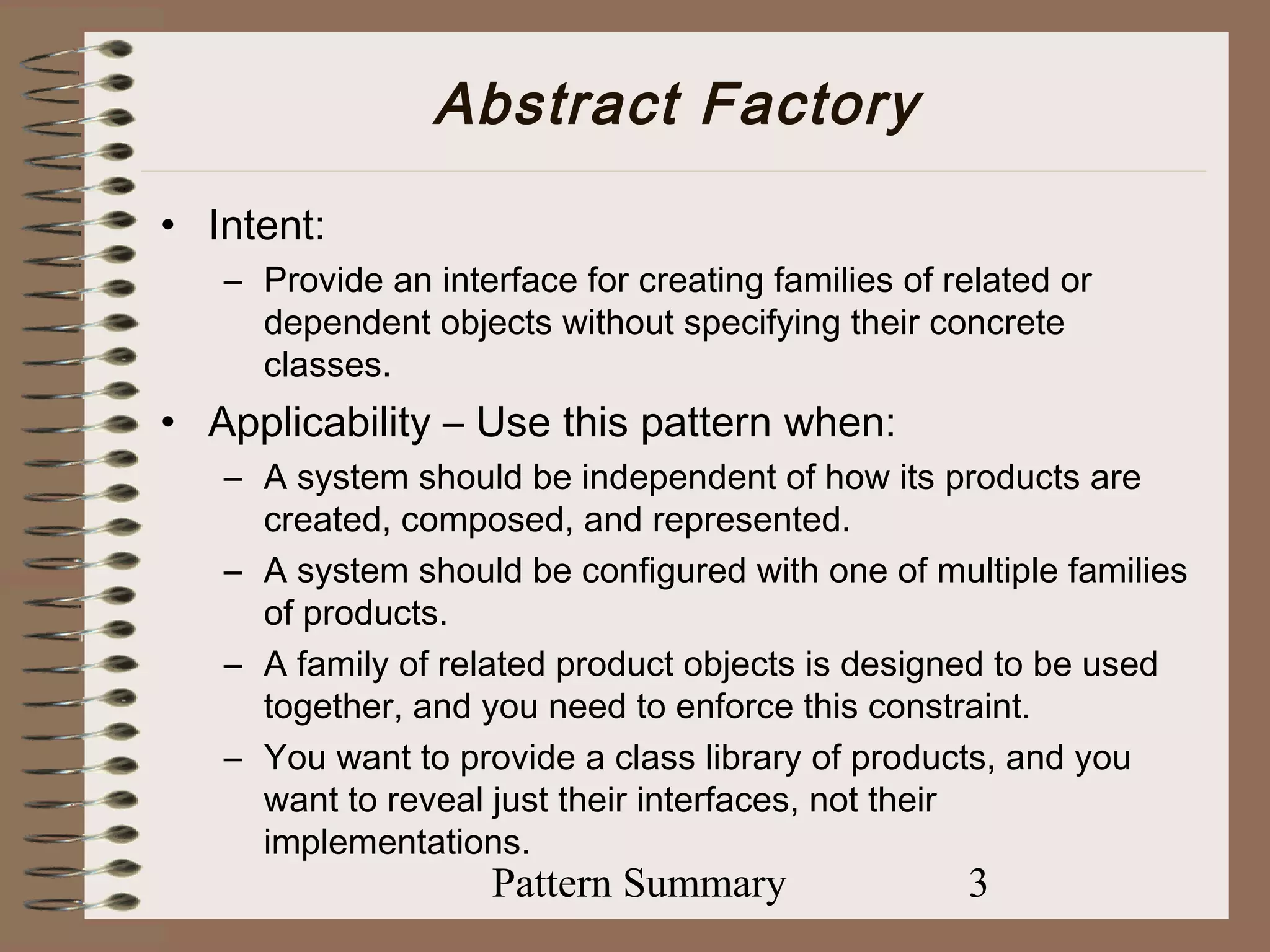
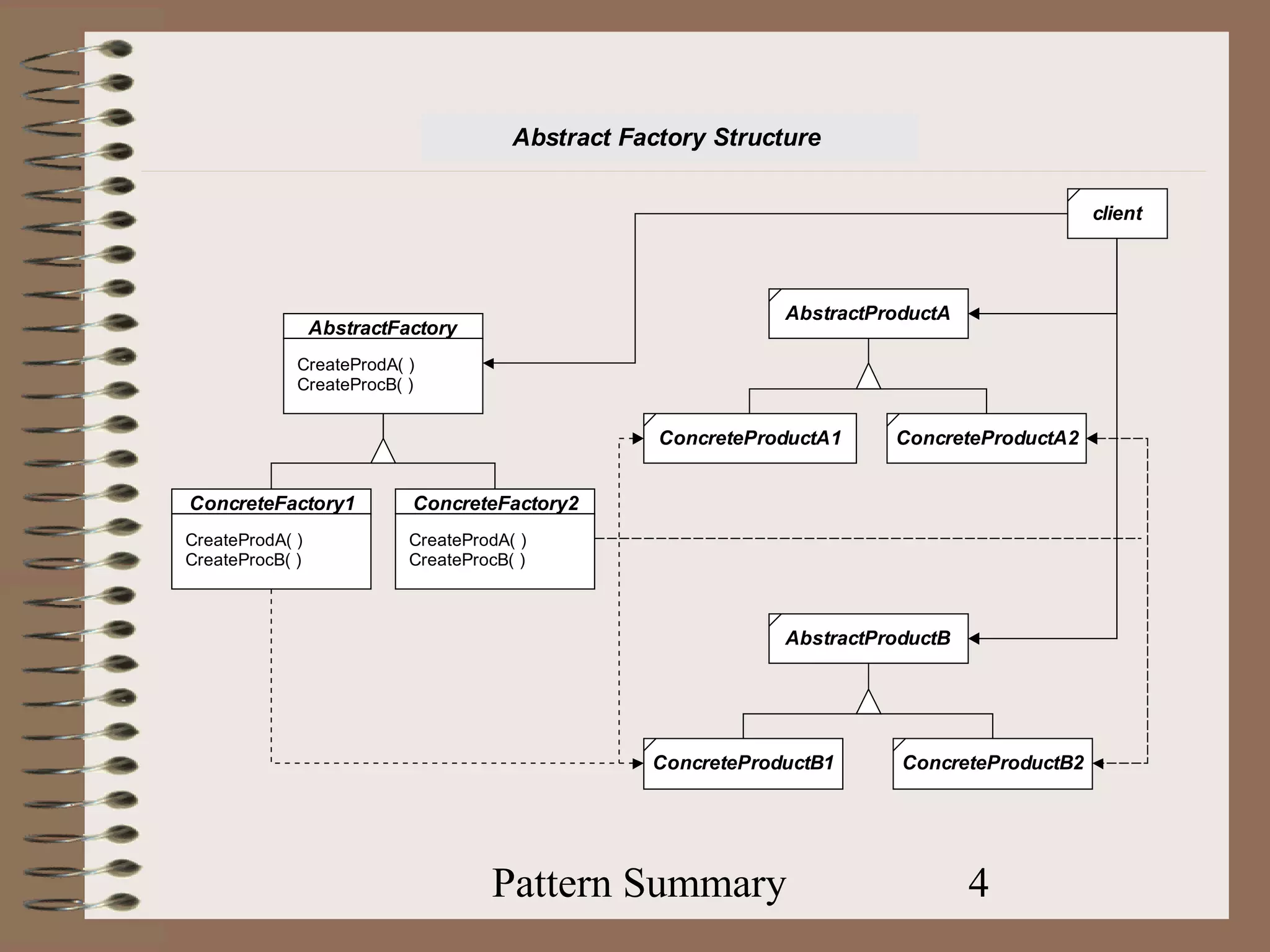
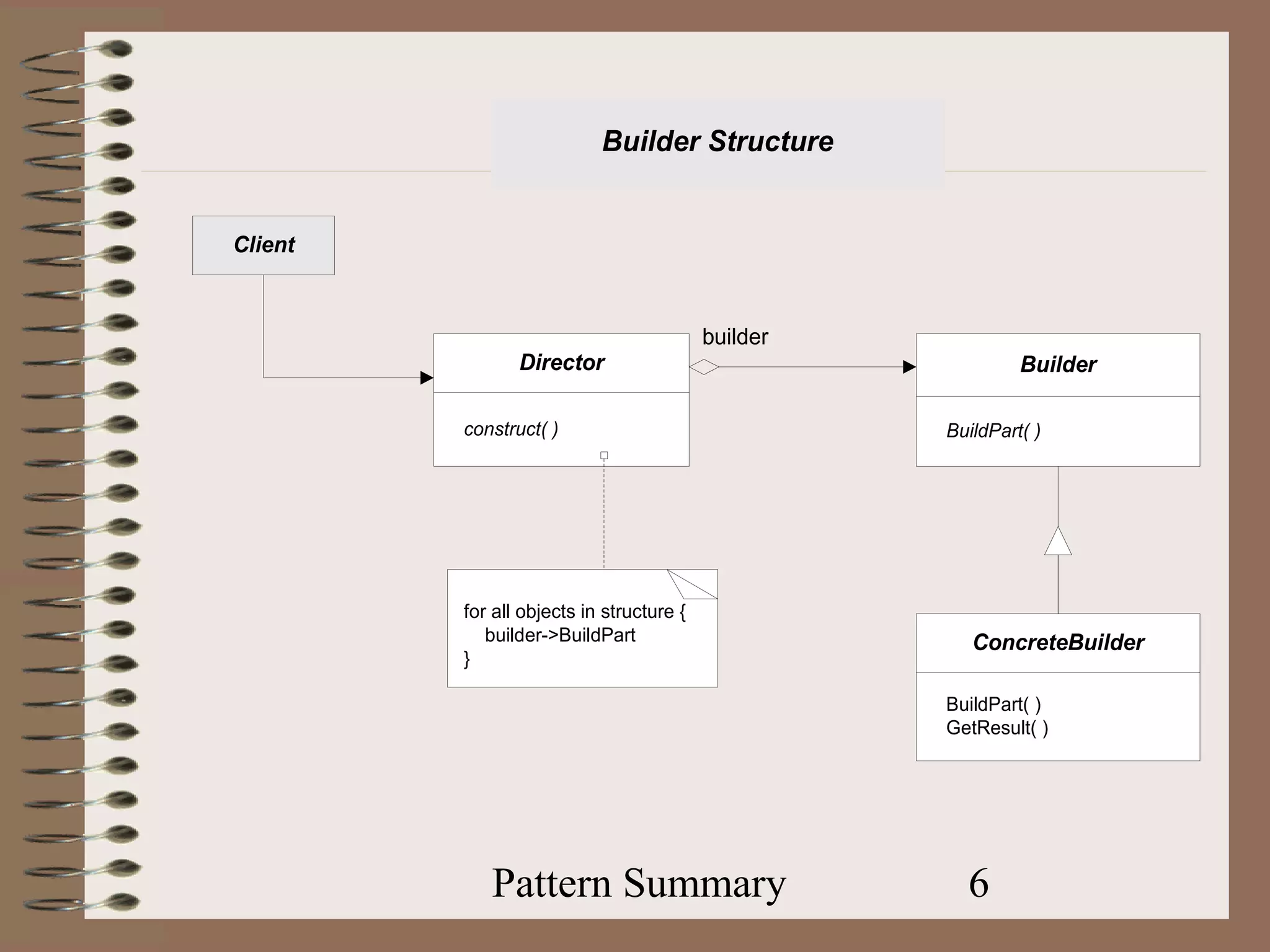
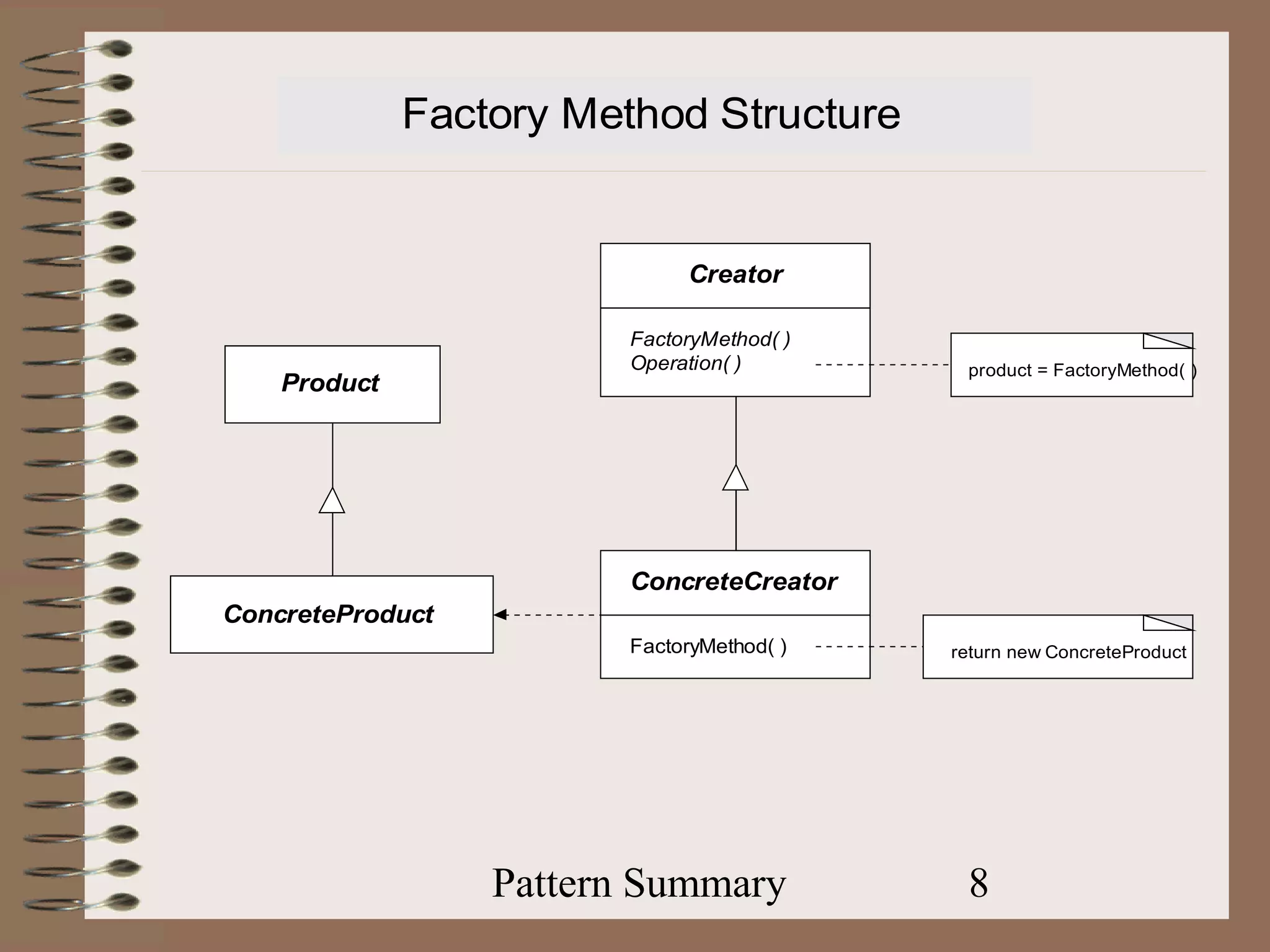
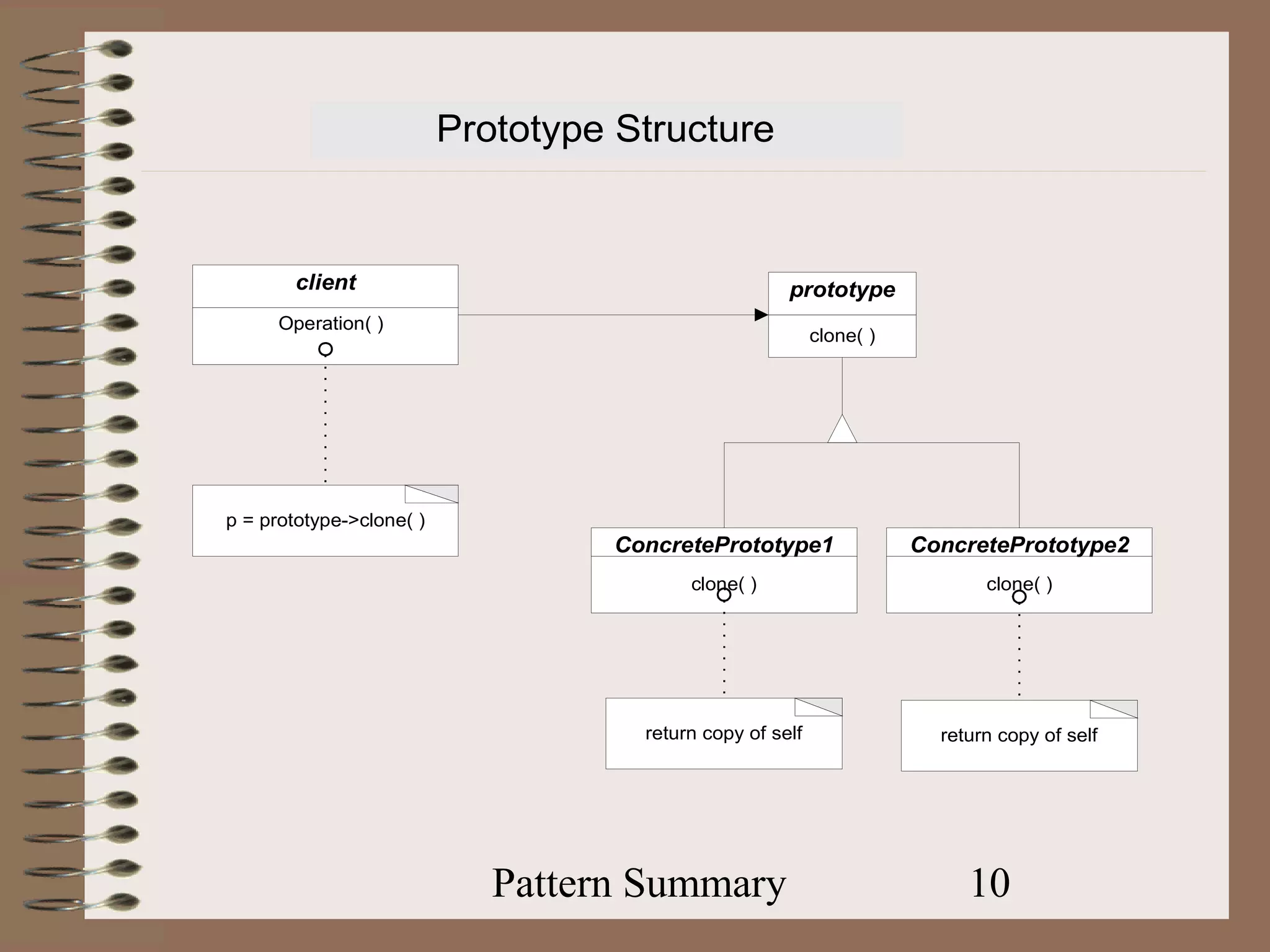
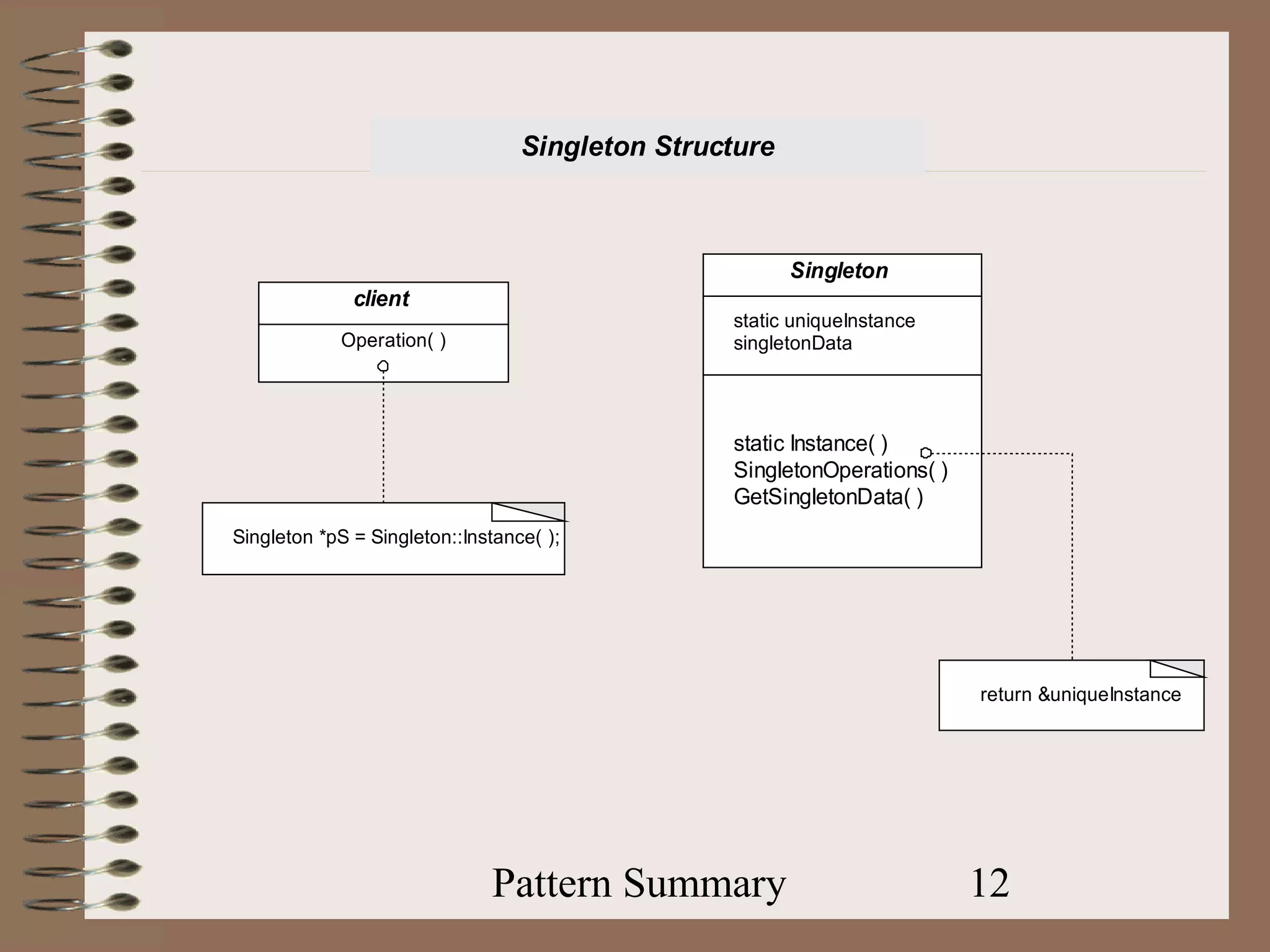
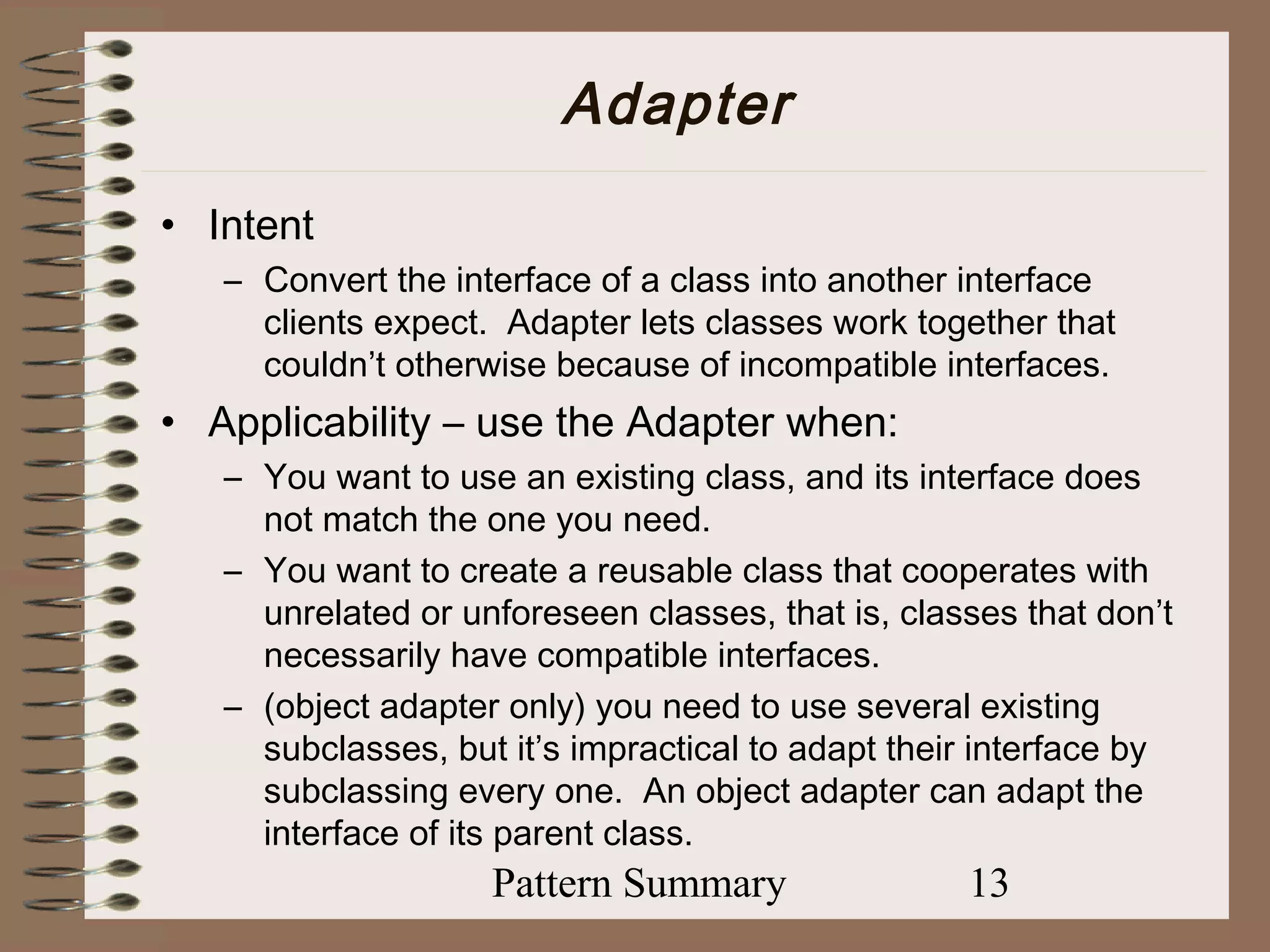
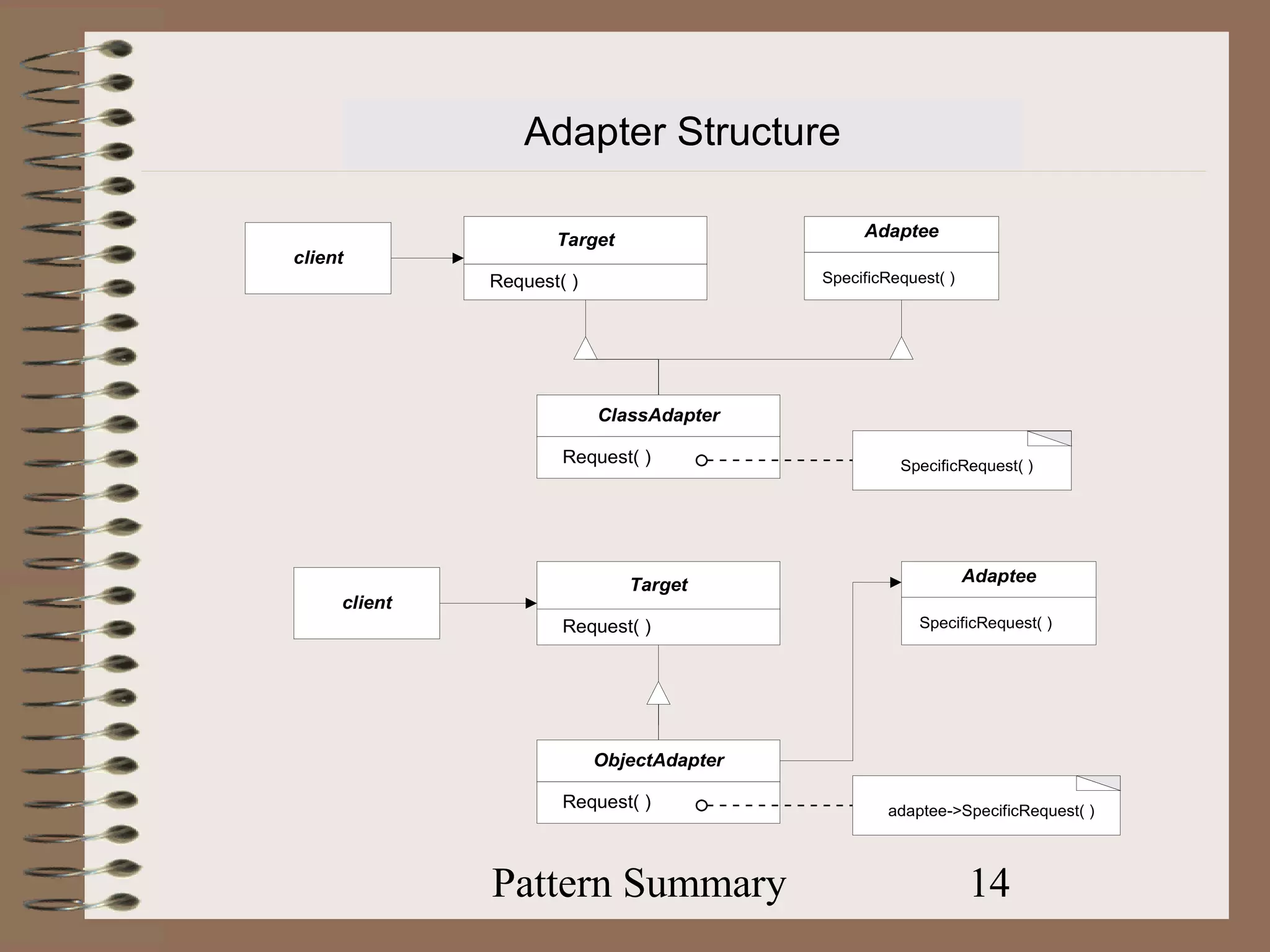
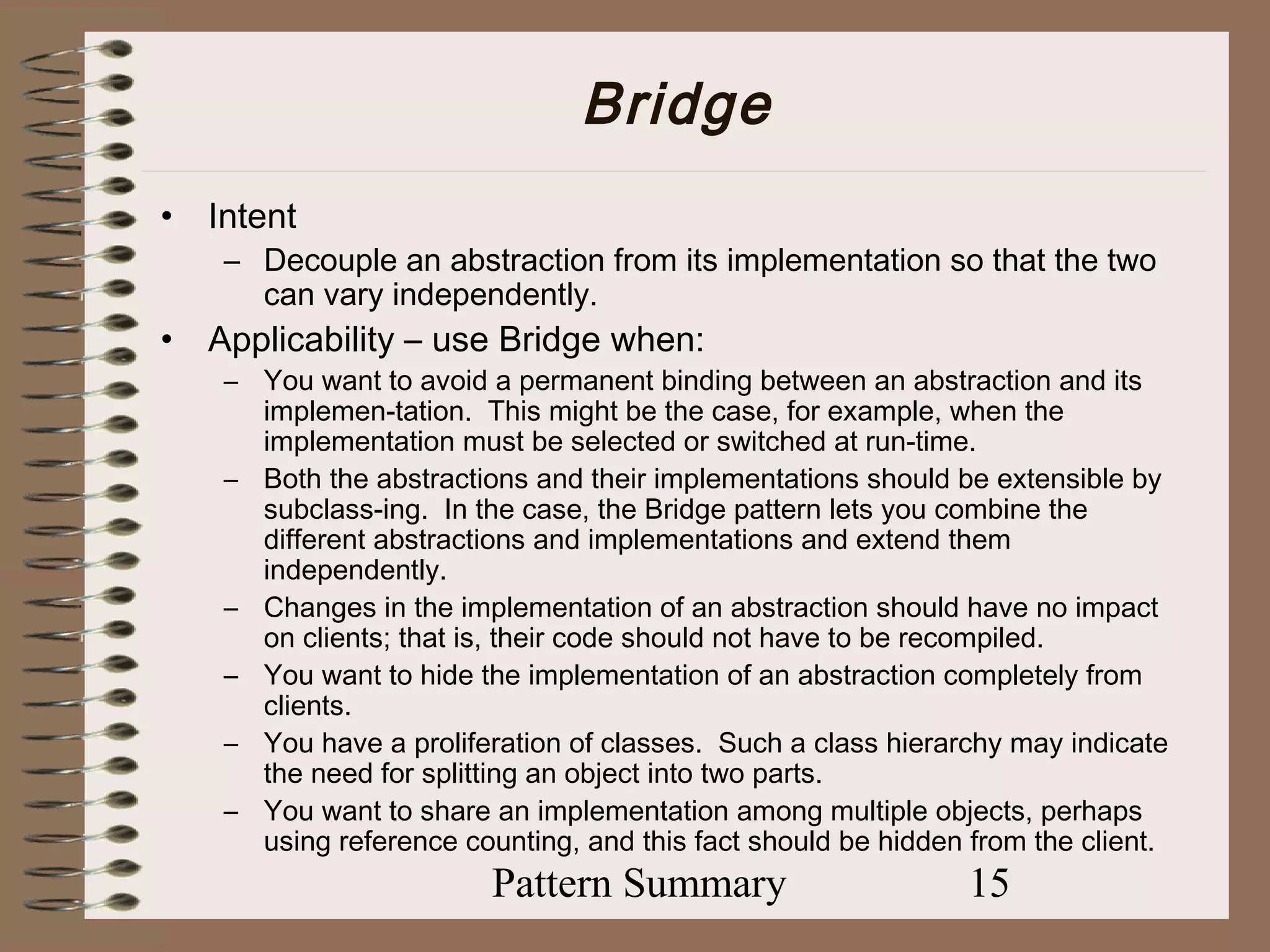
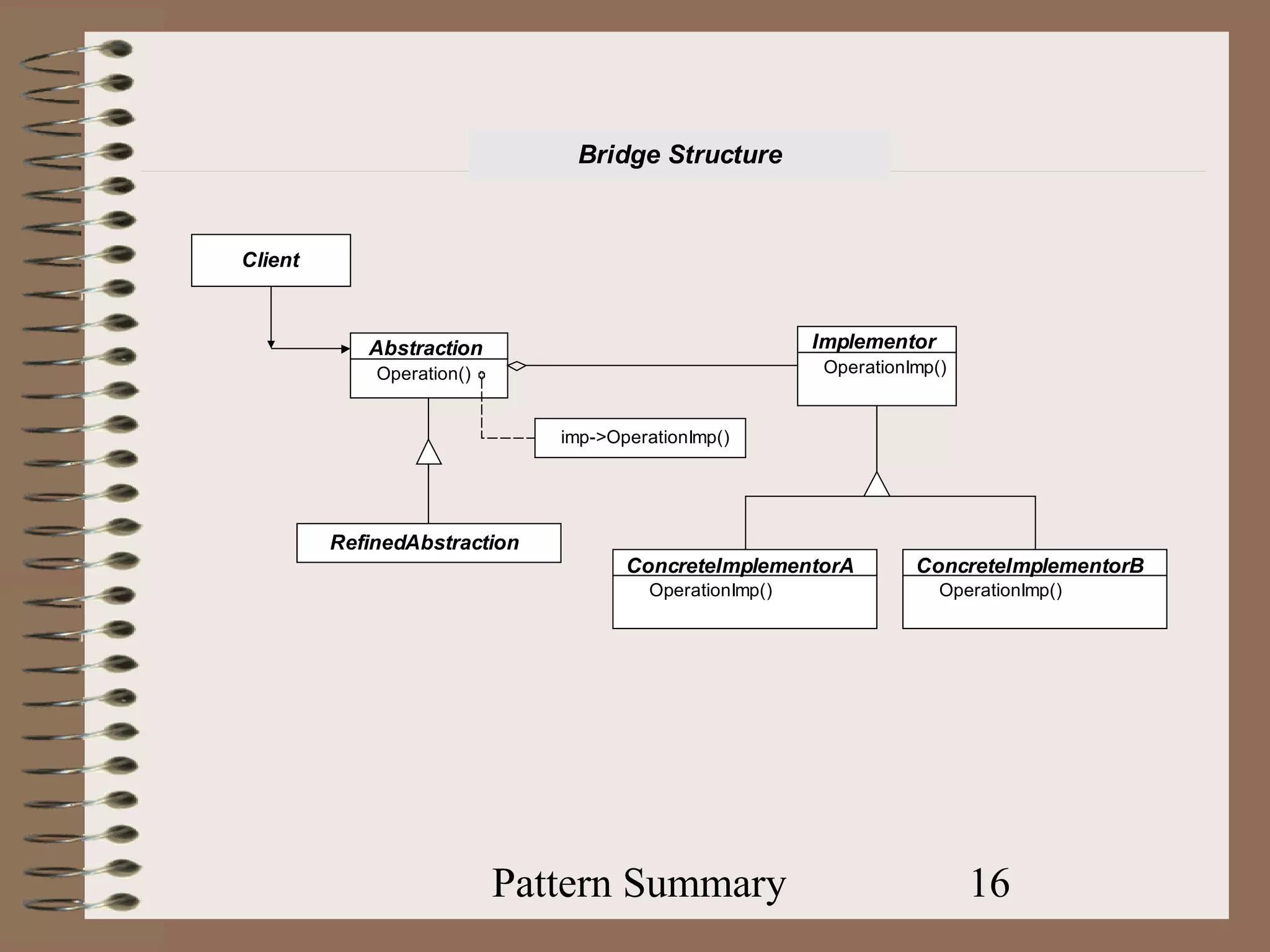
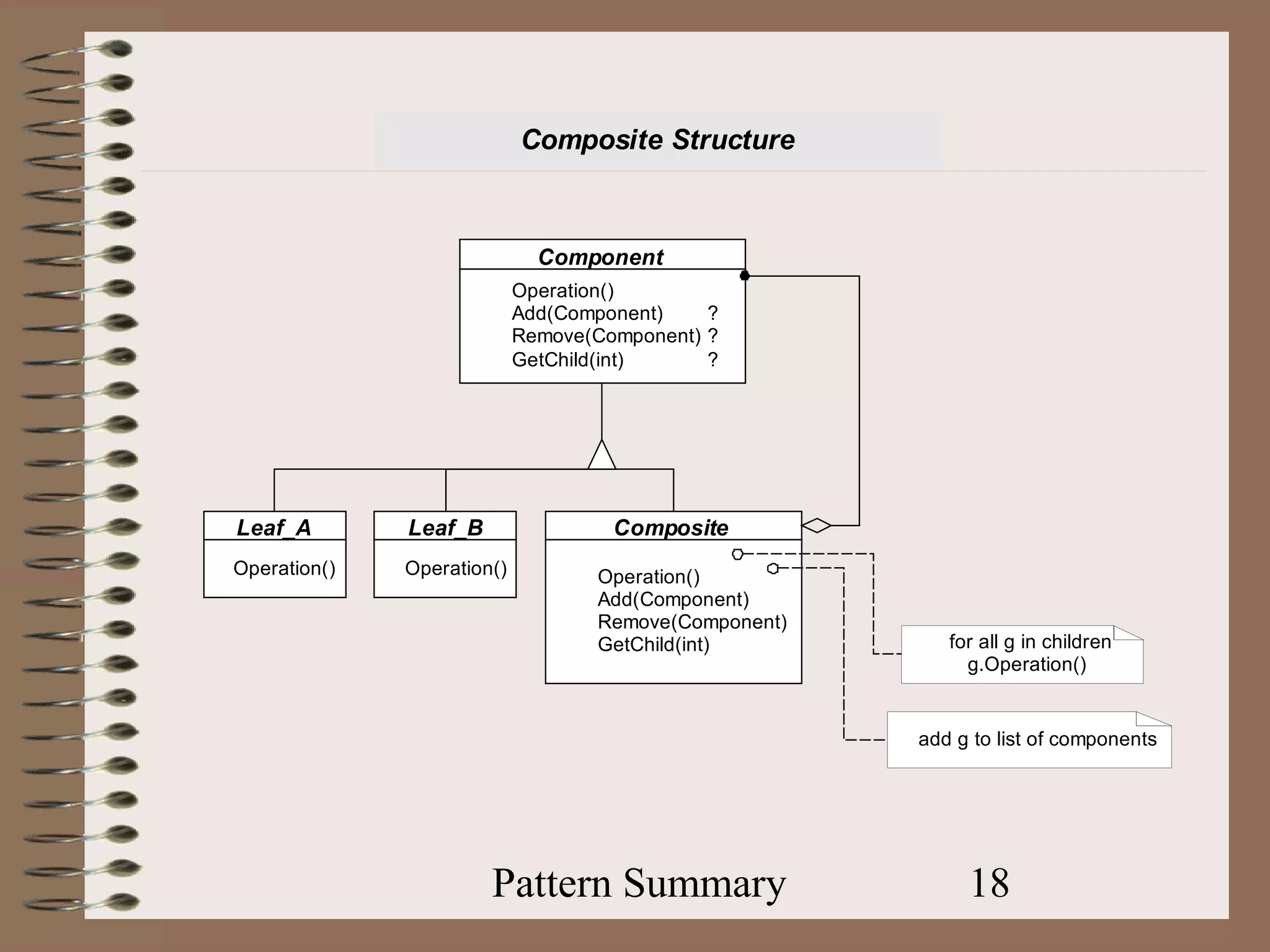
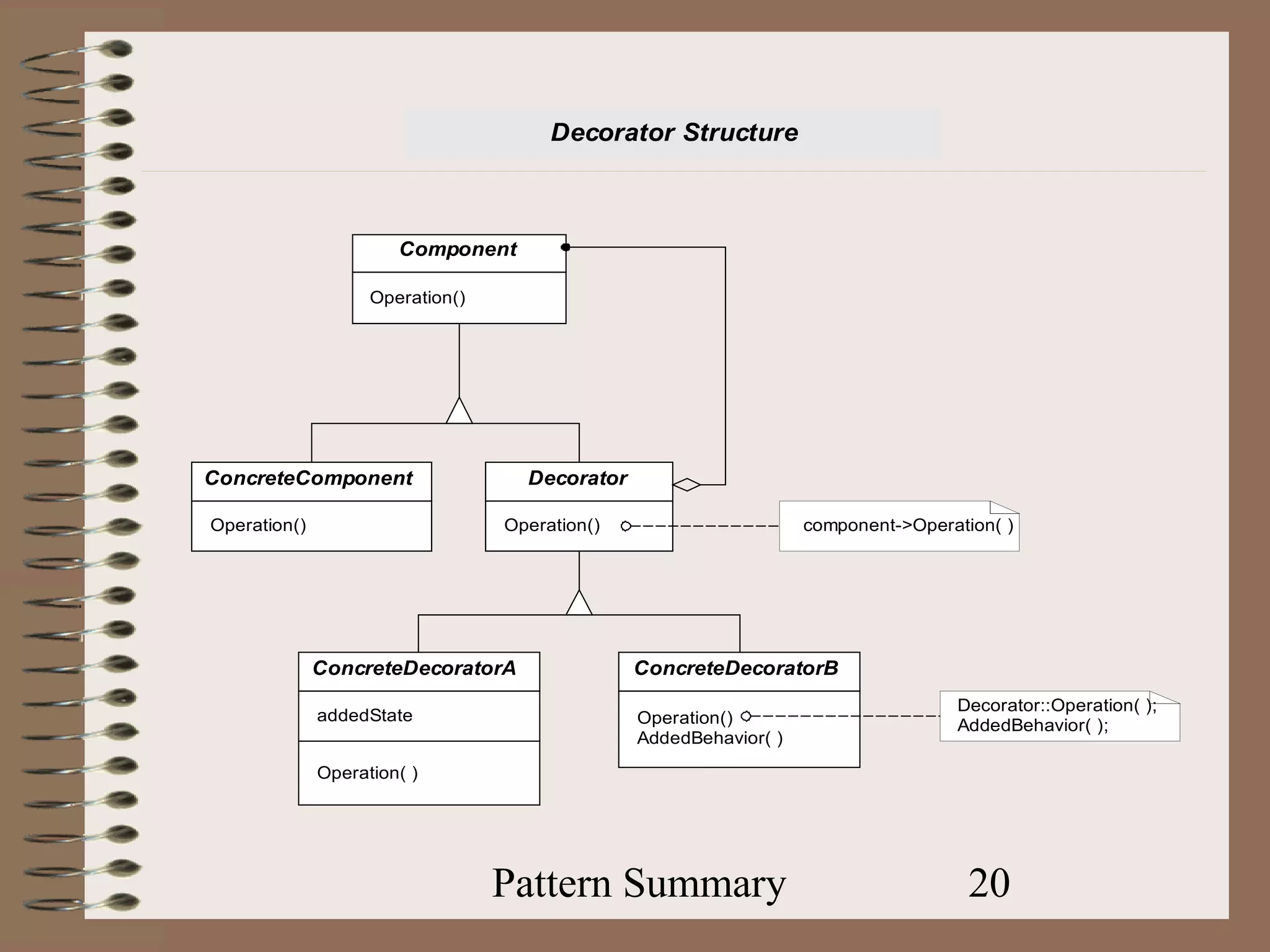
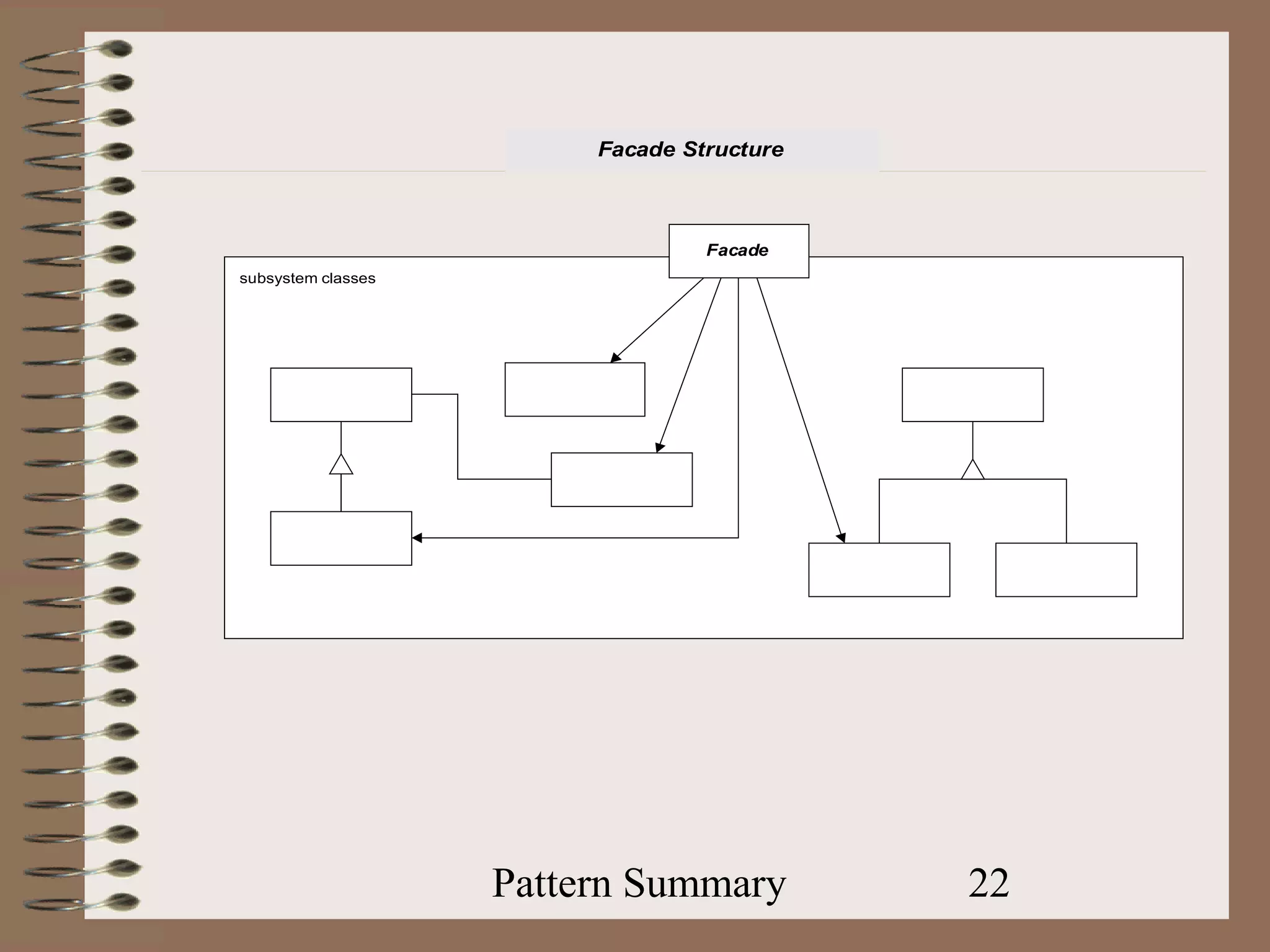
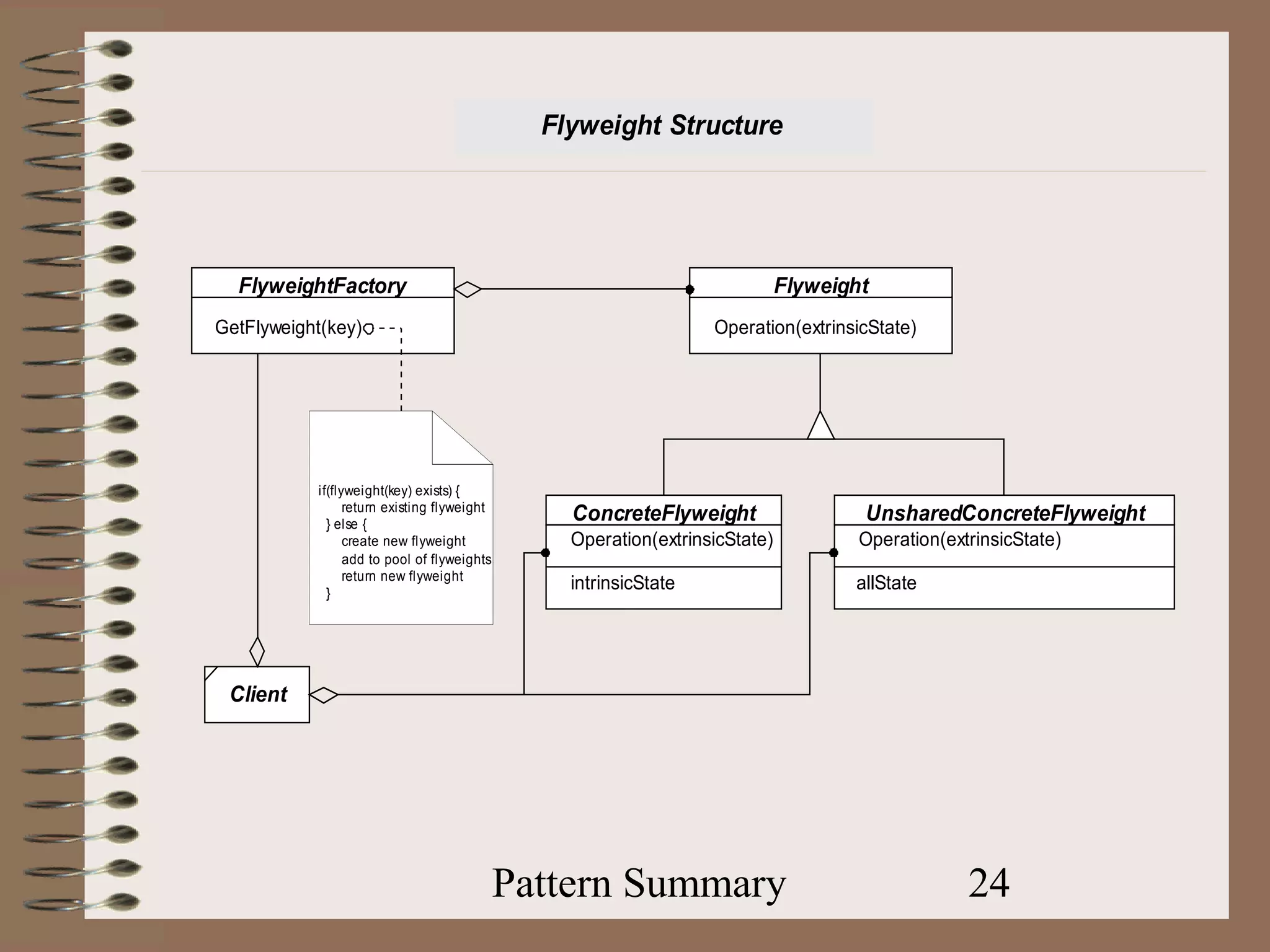
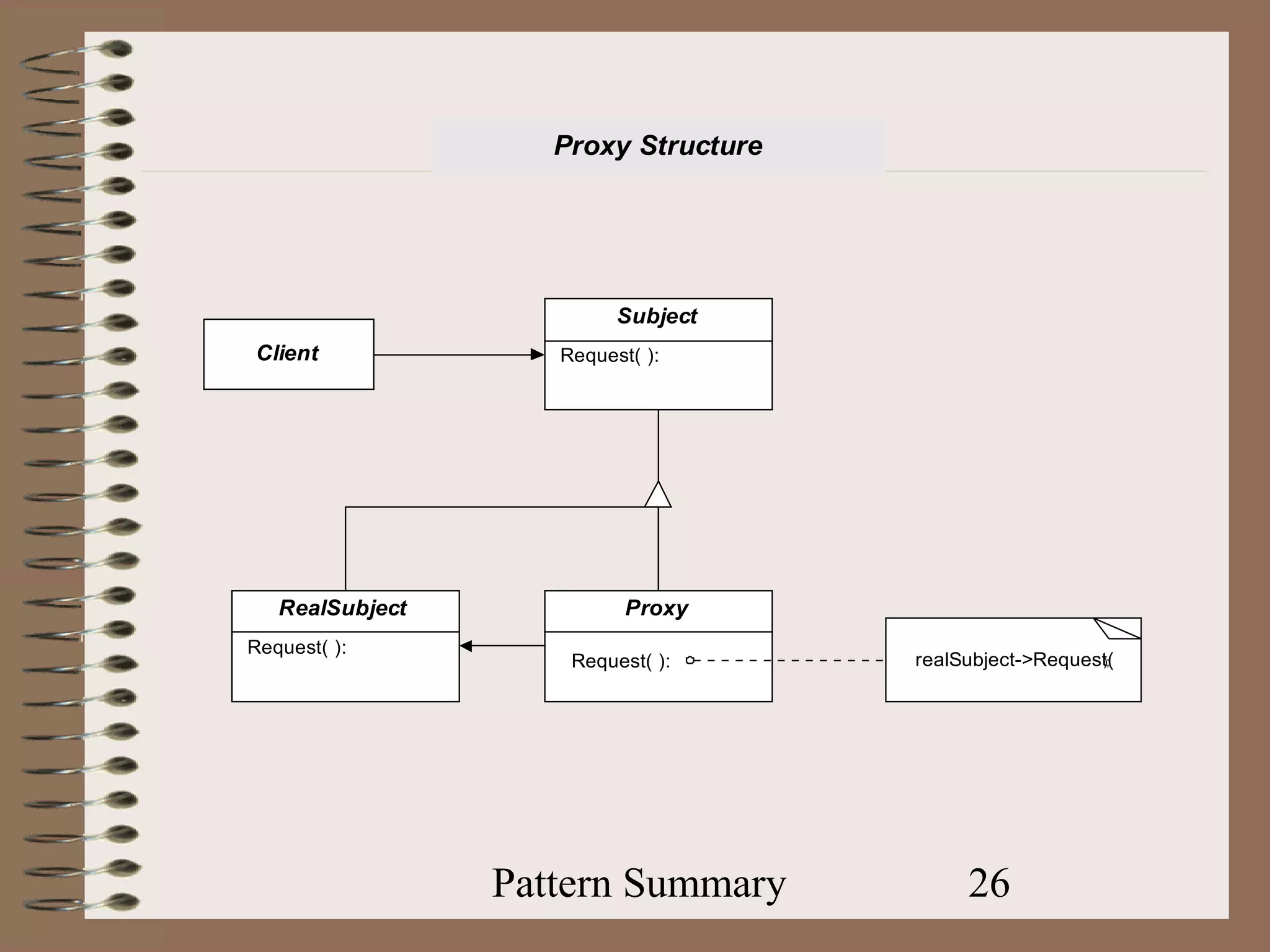
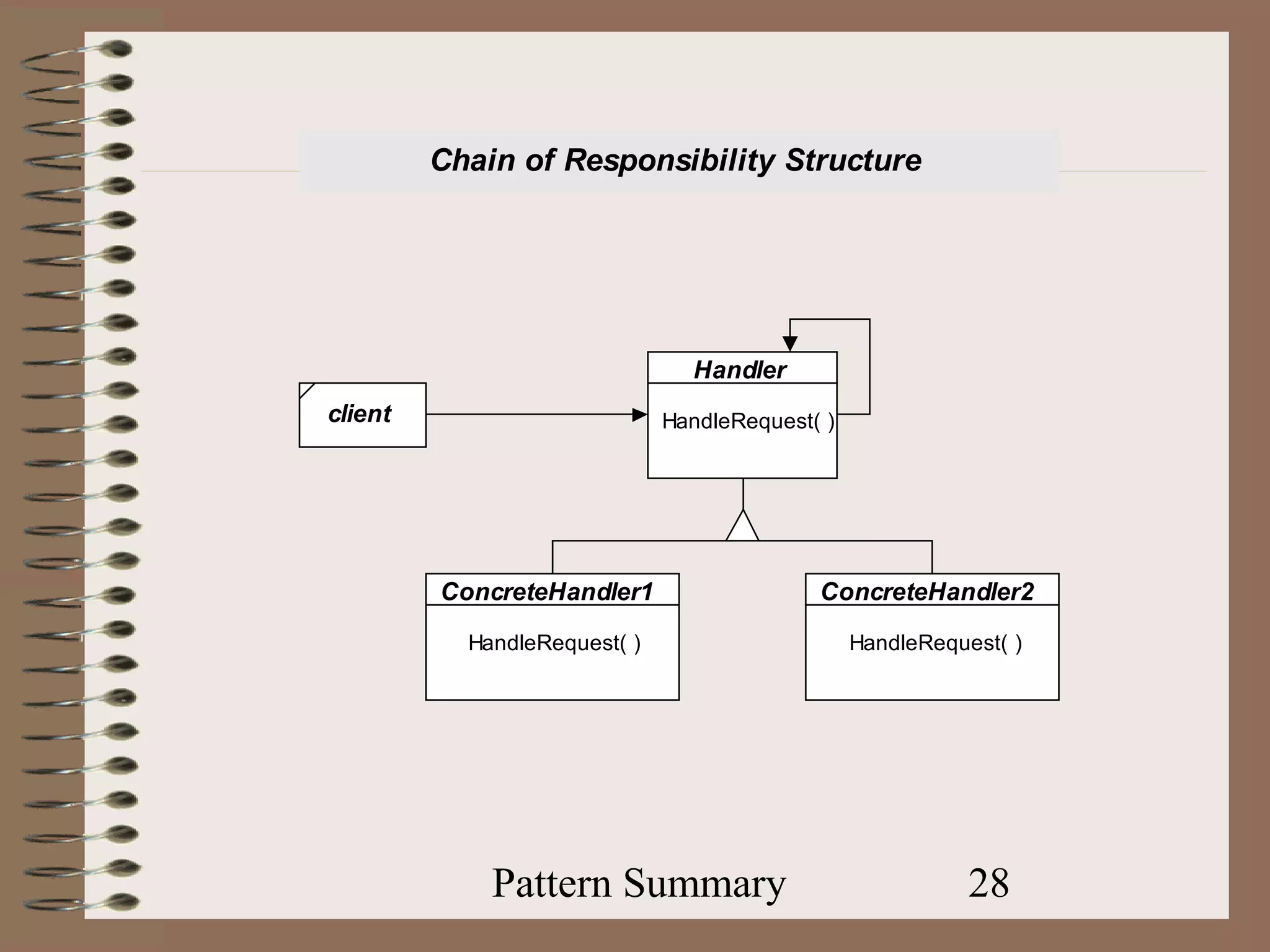
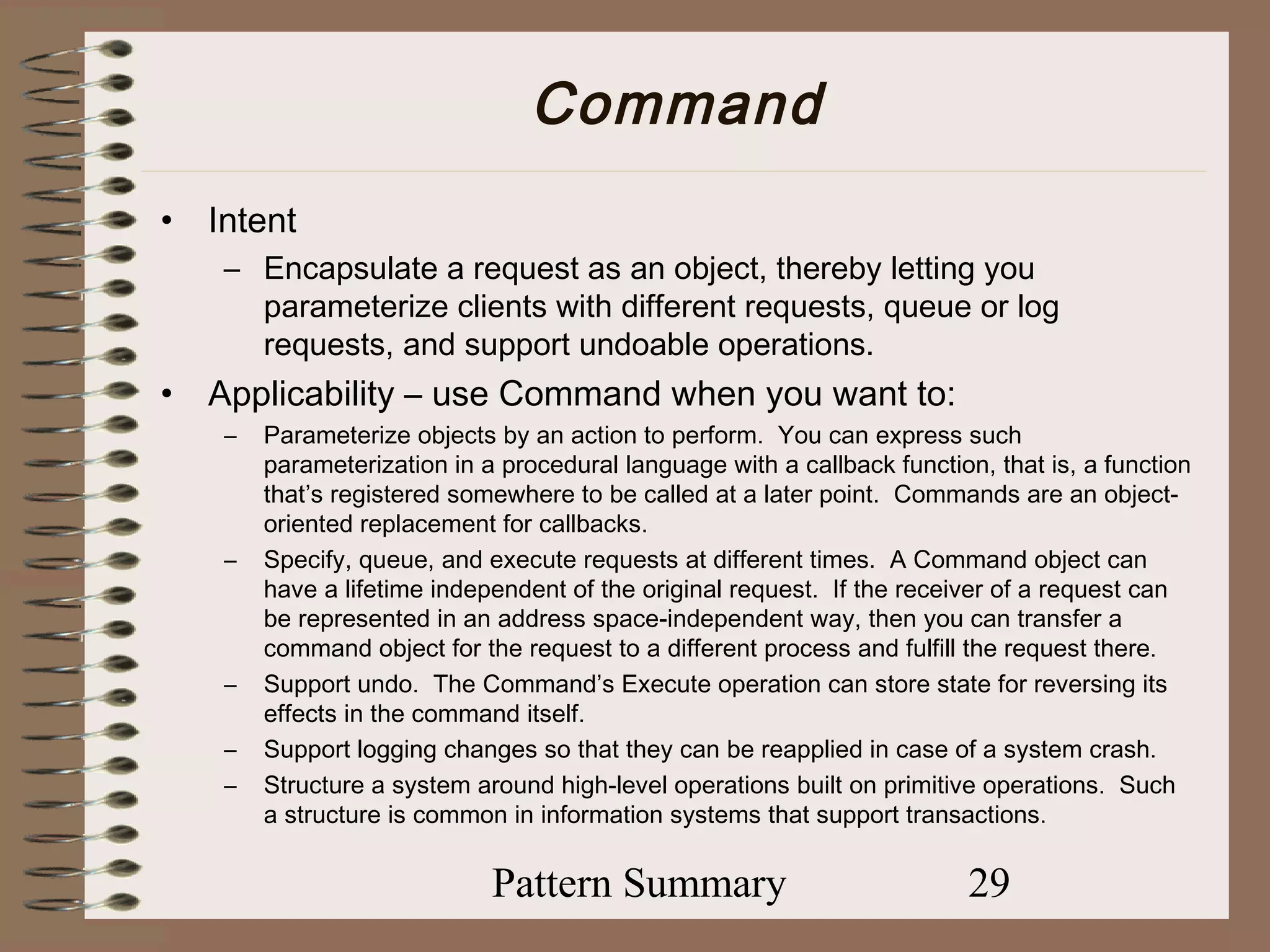
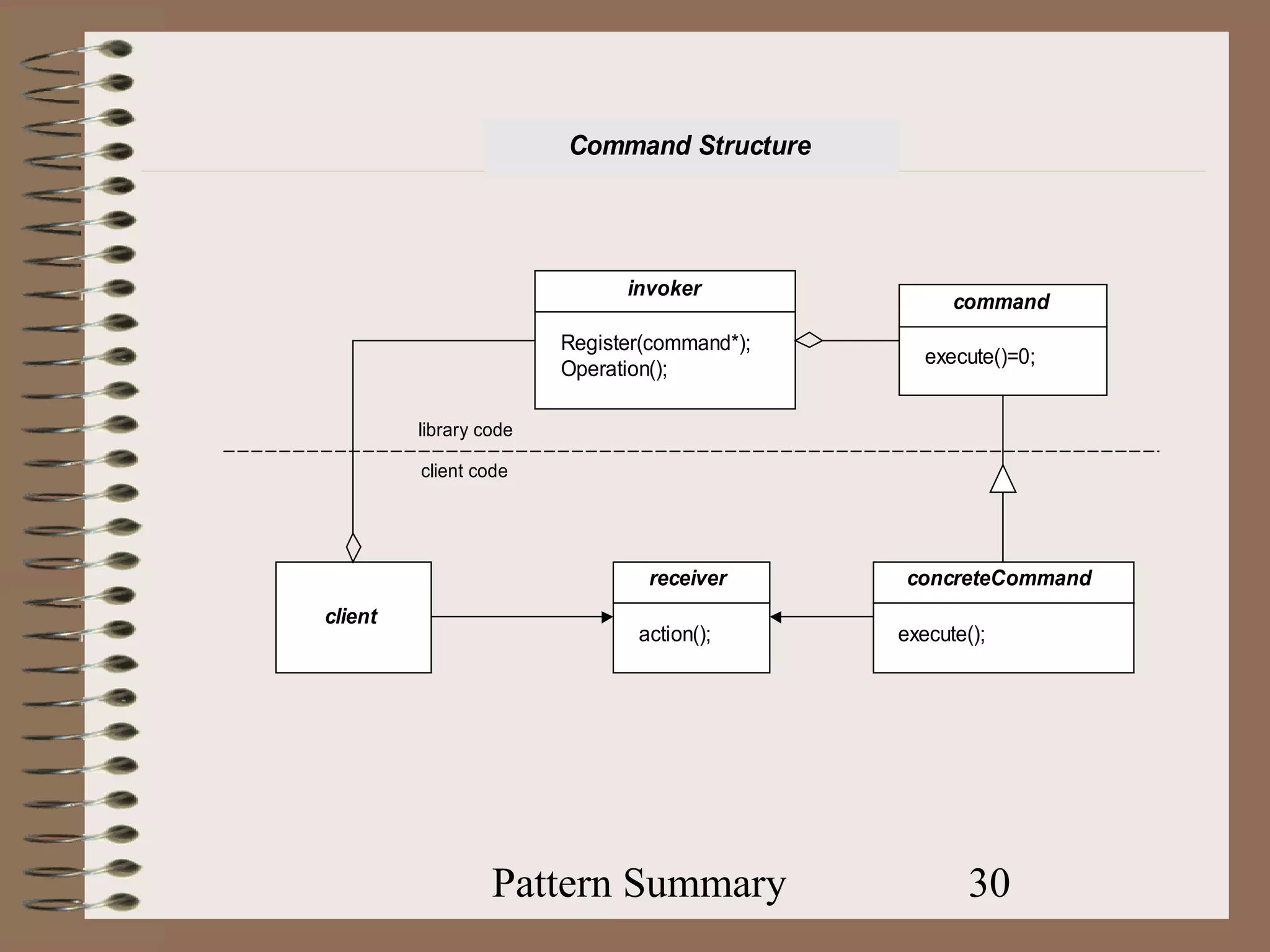
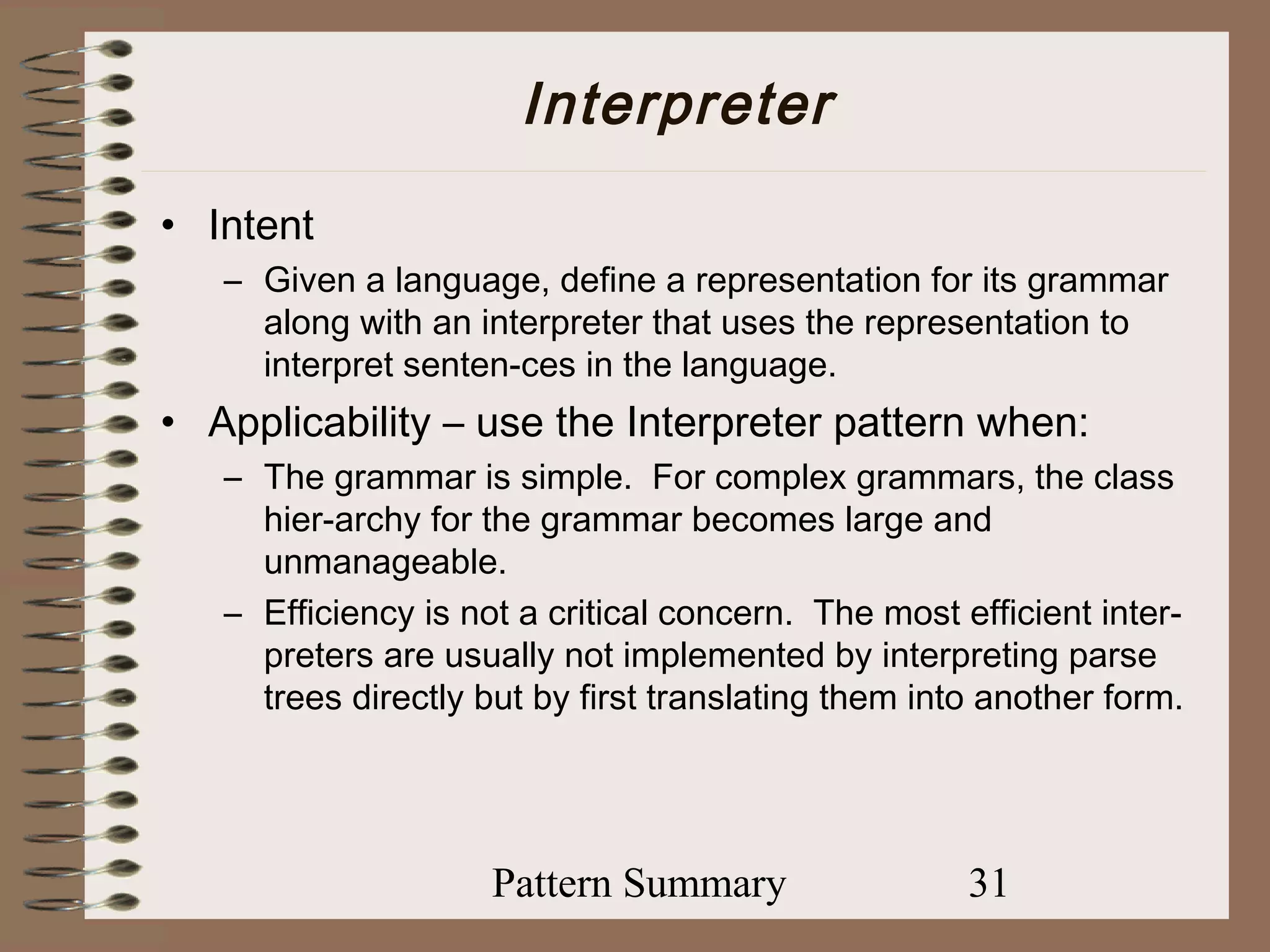
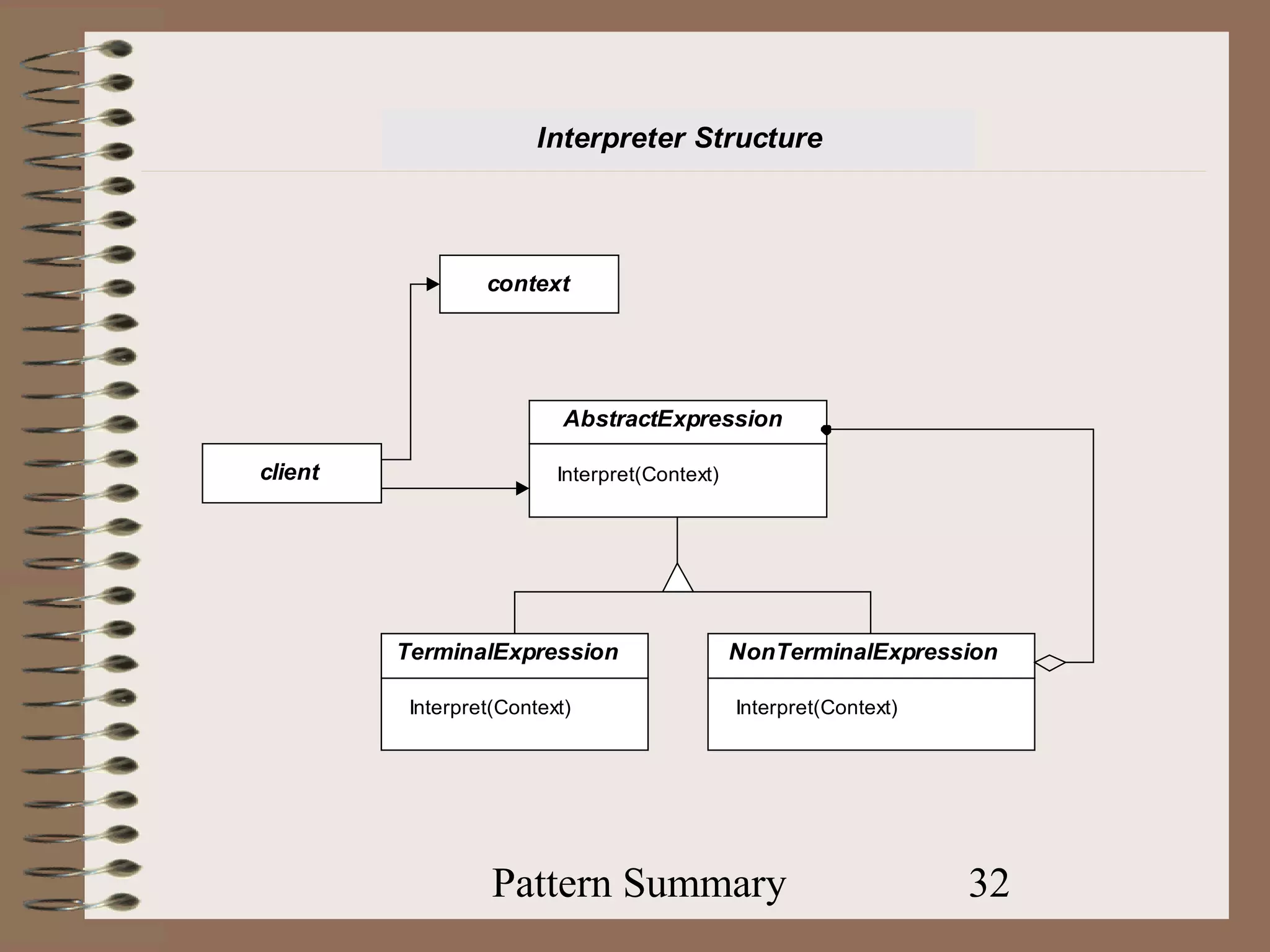
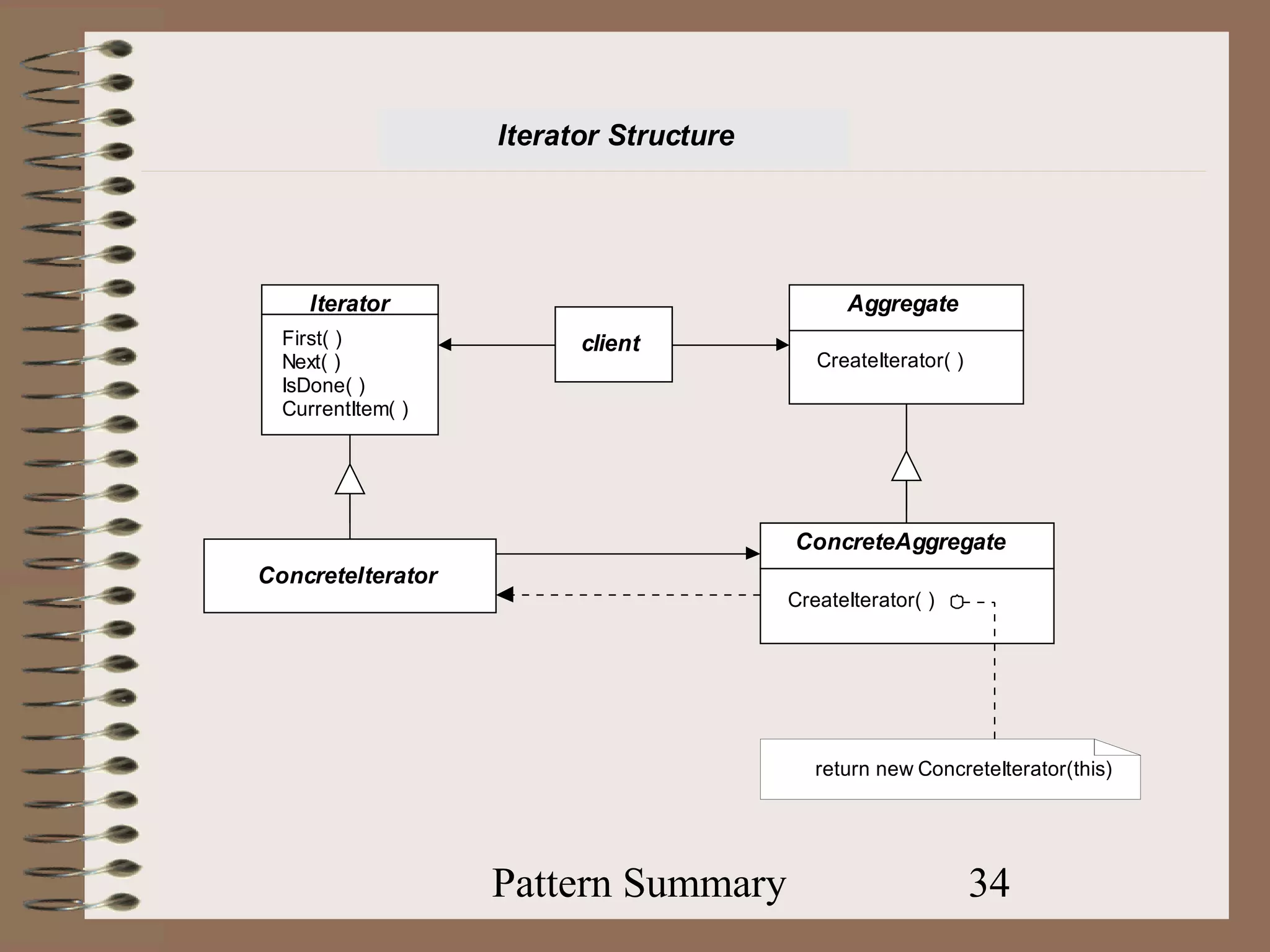
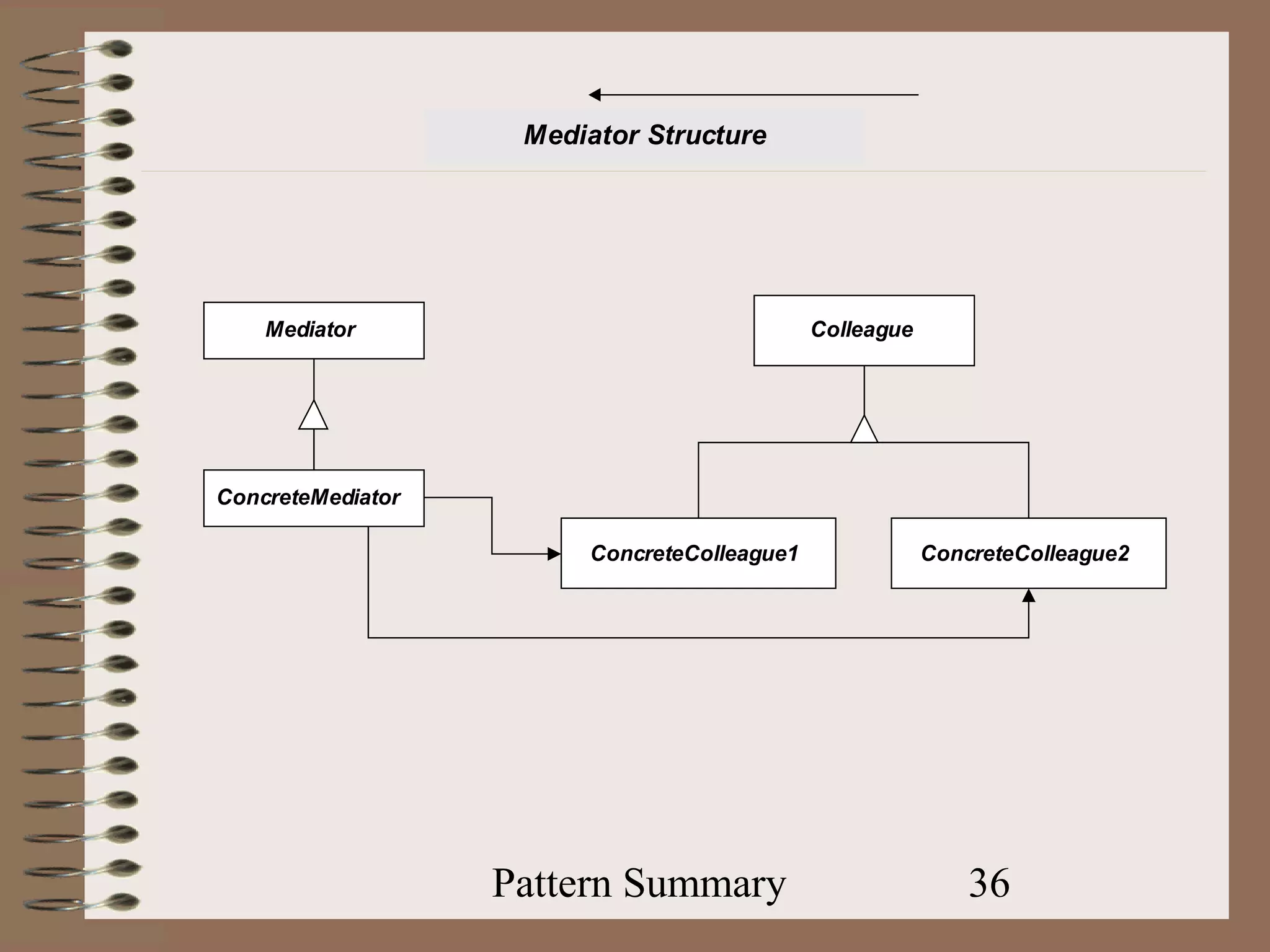
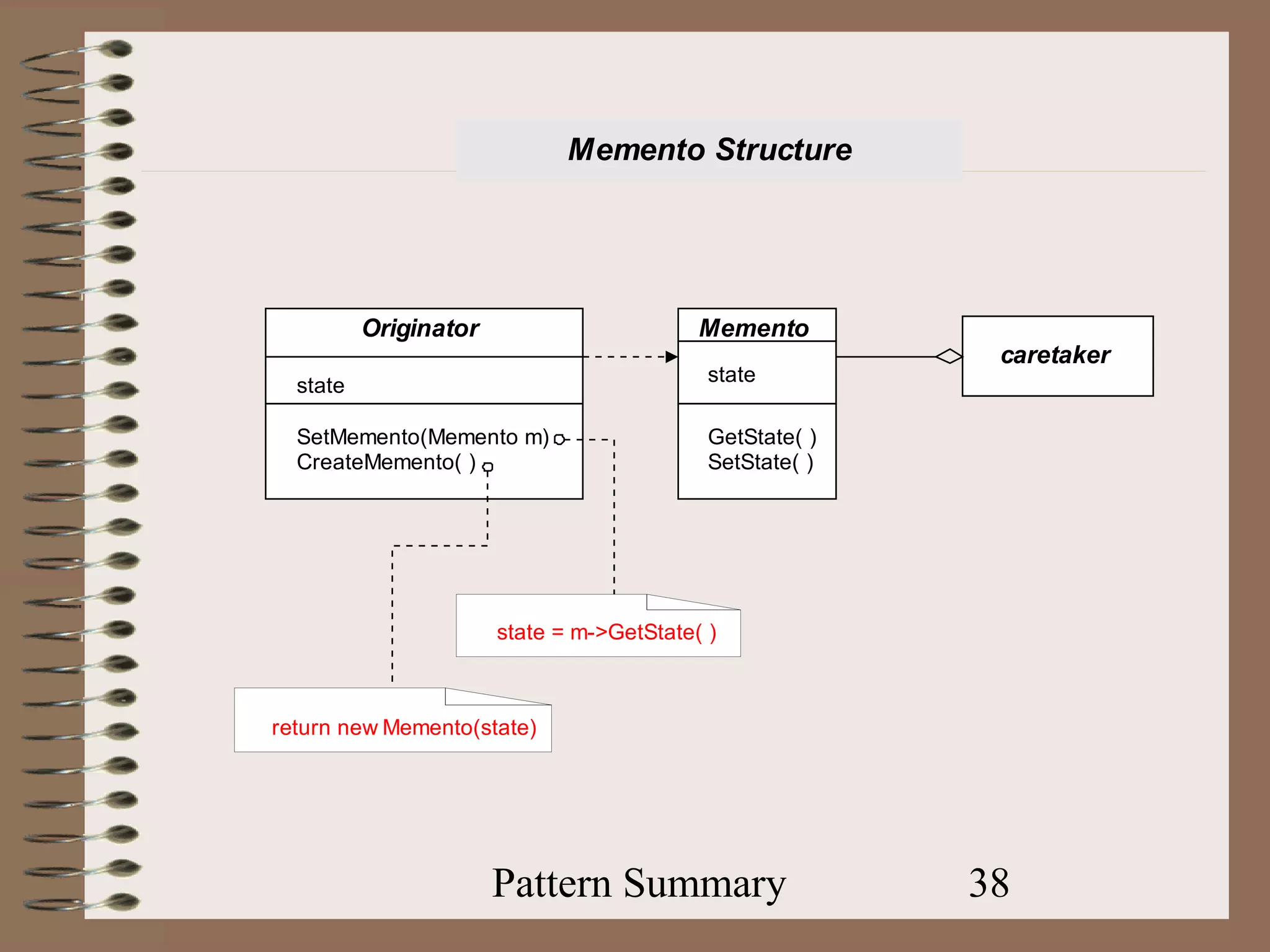
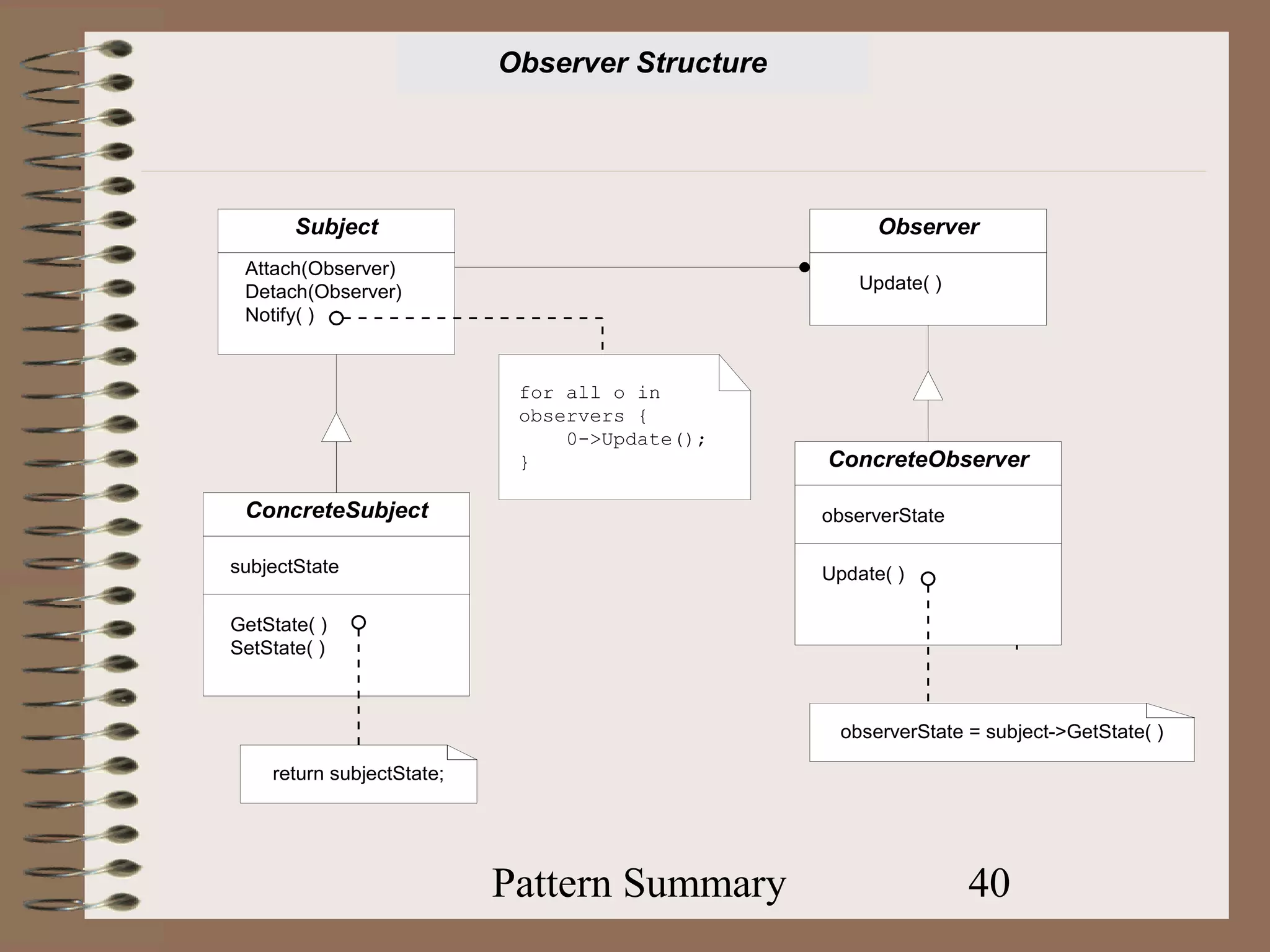
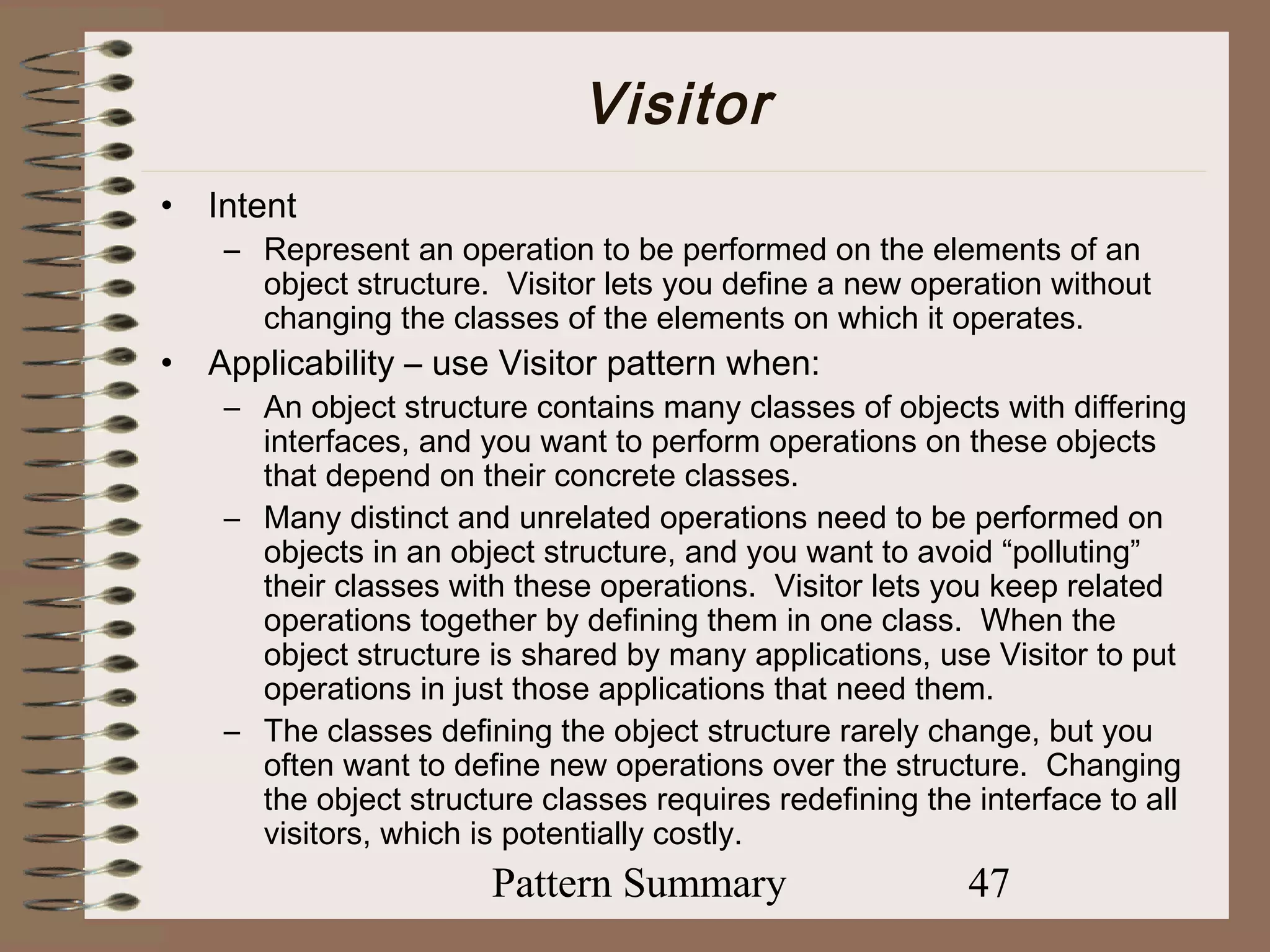
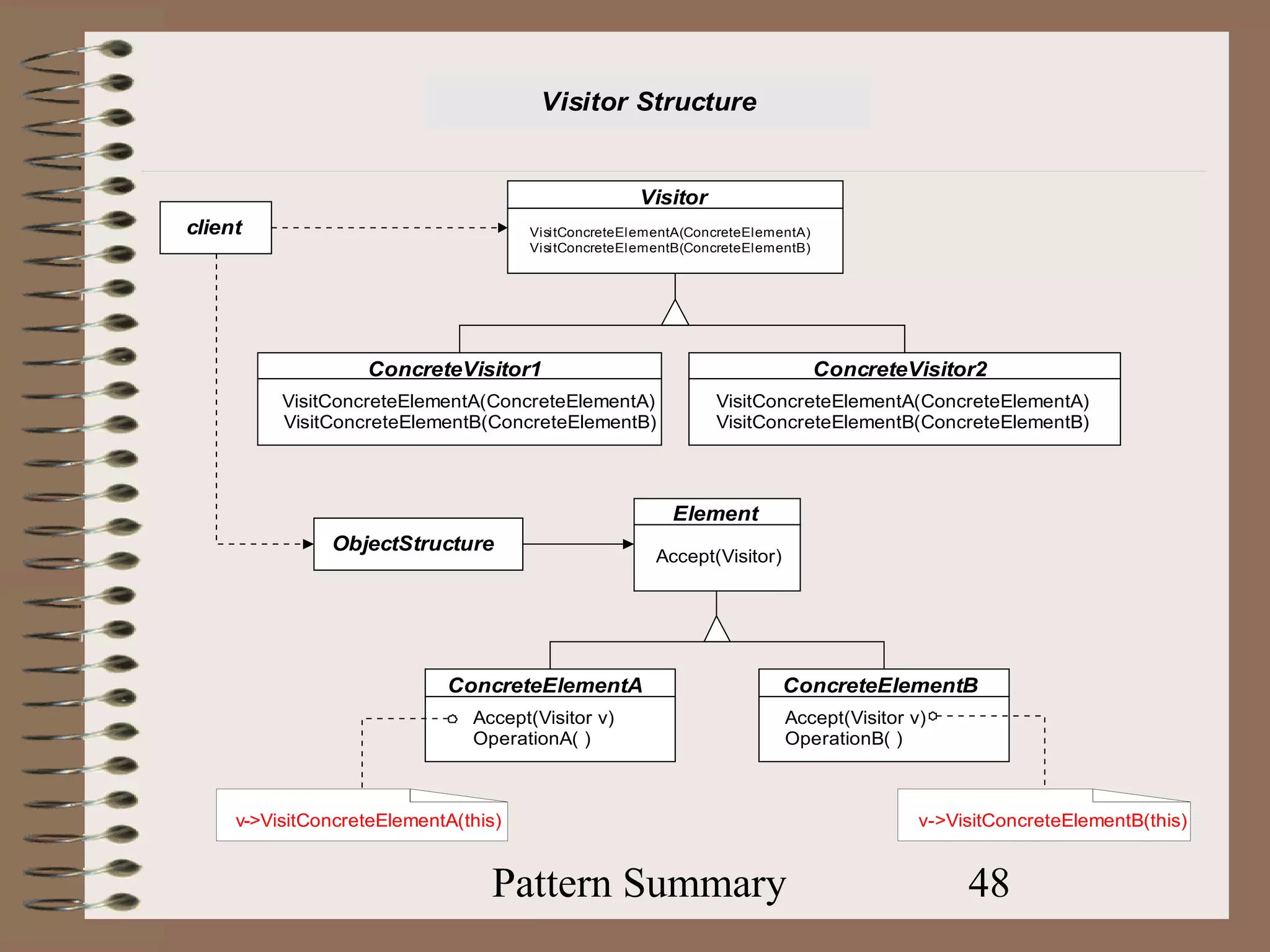
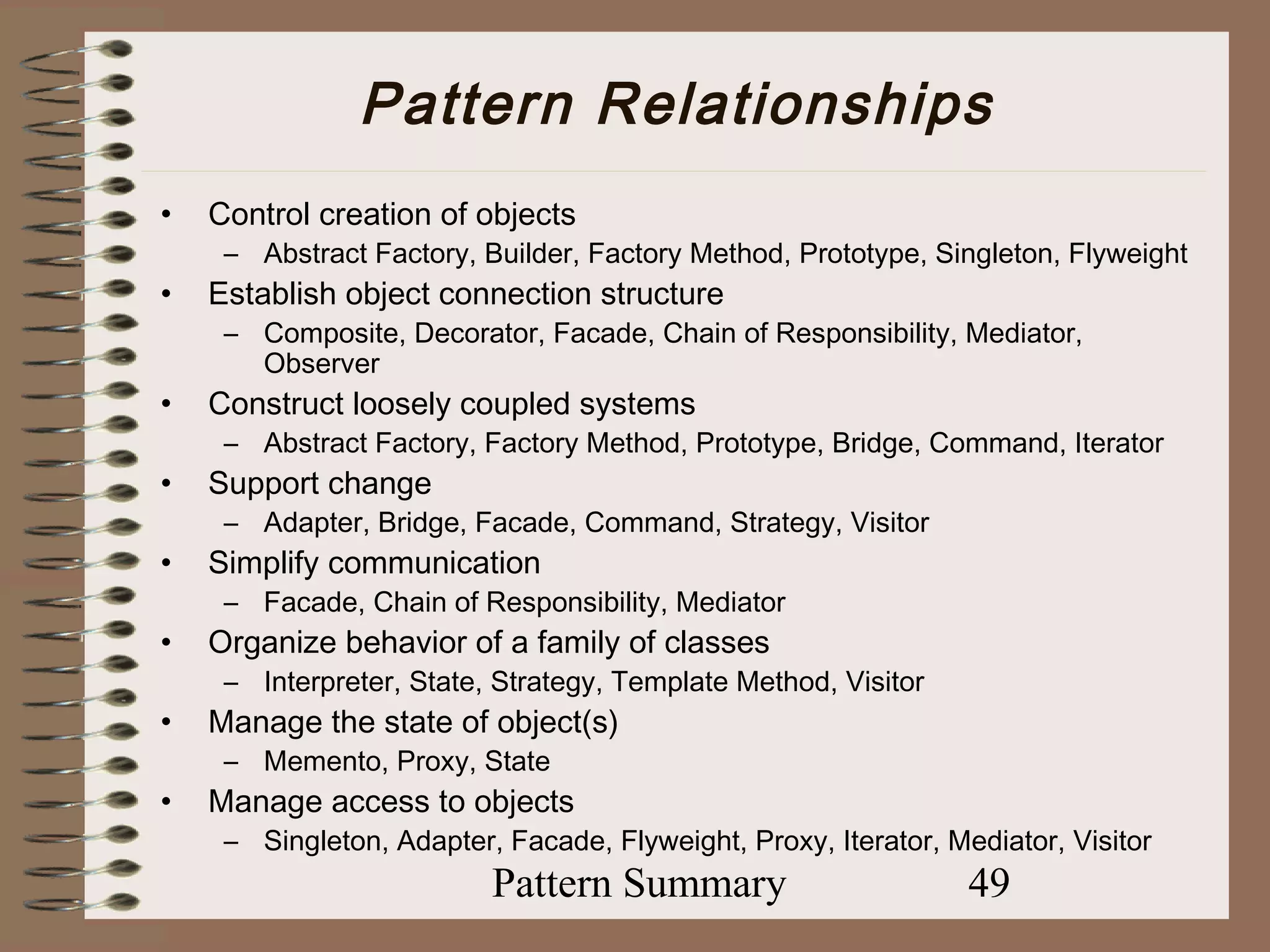
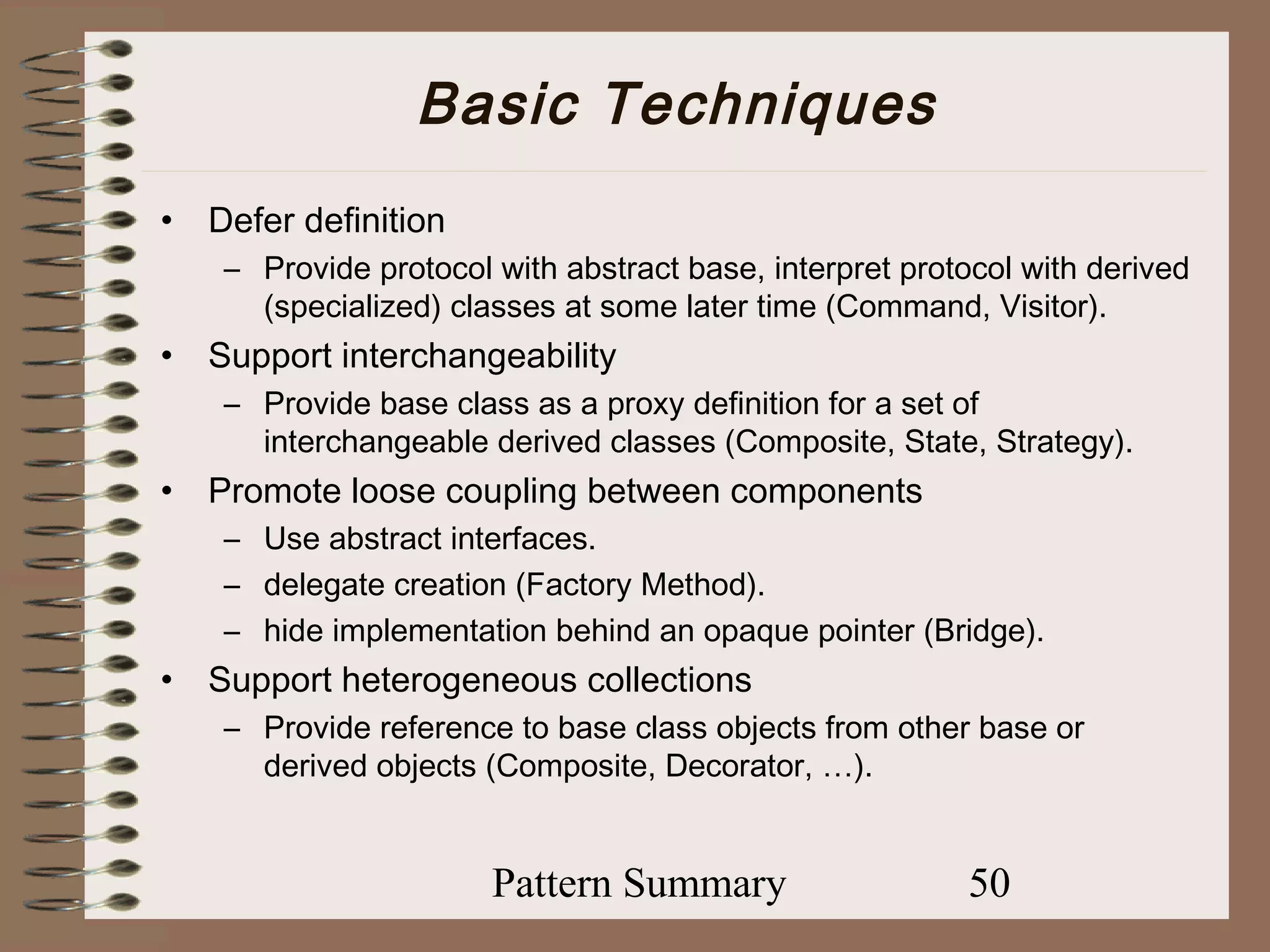
The document summarizes various design patterns as described by Gamma et al. in 1995, providing intents, applicability, and structural overviews for each pattern, including Abstract Factory, Builder, Singleton, Adapter, and others. It emphasizes the utility of these patterns in creating flexible and maintainable software architectures by addressing common design issues. This compilation serves as an educational resource for understanding the implementation and benefits of design patterns in software development.