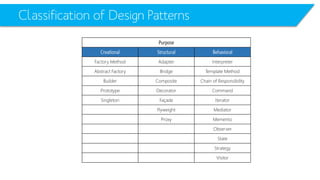
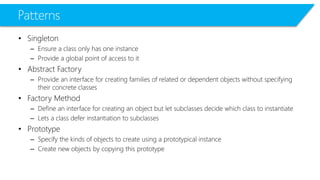
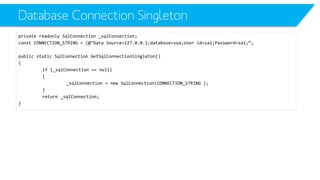
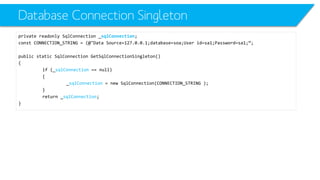
The document discusses several design patterns including Singleton, Factory Method, Strategy, and others. It provides descriptions of the patterns, examples of how they can be implemented in code, and discusses how some patterns like Singleton can be adapted for multi-threaded applications. It also briefly introduces the Multiton pattern, which is an extension of Singleton that allows multiple instances associated with different keys.




![Strategy
public interface IBehaviour{public intmoveCommand();}
public class AgressiveBehaviourimplements IBehaviour{
public intmoveCommand(){AgressiveBehaviour Behaviour}
}
public class DefensiveBehaviourimplements IBehaviour{
public intmoveCommand(){DefensiveBehaviour Behaviour}
}
public class NormalBehaviourimplements IBehaviour{
public intmoveCommand(){NormalBehaviour Behaviour}
}
public class Robot {
IBehaviourbehaviour;
String name;
public Robot(String name)
{this.name = name;}
public void setBehaviour(IBehaviourbehaviour)
{this.behaviour= behaviour;}
public void move()
{behaviourزmoveCommand();}
}
public static void main(String[] args) {
Robot r1 = new Robot("Big Robot");
Robot r2 = new Robot("George v.2.1");
Robot r3 = new Robot("R2");
r1.setBehaviour(new AgressiveBehaviour());
r2.setBehaviour(new DefensiveBehaviour());
r3.setBehaviour(new NormalBehaviour());
r1.move();
r2.move();
r3.move();
r1.setBehaviour(new DefensiveBehaviour());
r2.setBehaviour(new AgressiveBehaviour());
r1.move();
r2.move();
r3.move();
}](https://image.slidesharecdn.com/csharpadvancedl07-desginpatterns-140825094156-phpapp02/85/C-Advanced-L07-Design-Patterns-21-320.jpg)
![Strategy
public interface IBehaviour{public intmoveCommand();}
public class AgressiveBehaviourimplements IBehaviour{
public intmoveCommand(){AgressiveBehaviour Behaviour}
}
public class DefensiveBehaviourimplements IBehaviour{
public intmoveCommand(){DefensiveBehaviour Behaviour}
}
public class NormalBehaviourimplements IBehaviour{
public intmoveCommand(){NormalBehaviour Behaviour}
}
public class Robot {
IBehaviourbehaviour;
String name;
public Robot(String name)
{this.name = name;}
public void setBehaviour(IBehaviourbehaviour)
{this.behaviour= behaviour;}
public void move()
{behaviourزmoveCommand();}
}
public static void main(String[] args) {
Robot r1 = new Robot("Big Robot");
Robot r2 = new Robot("George v.2.1");
Robot r3 = new Robot("R2");
r1.setBehaviour(new AgressiveBehaviour());
r2.setBehaviour(new DefensiveBehaviour());
r3.setBehaviour(new NormalBehaviour());
r1.move();
r2.move();
r3.move();
r1.setBehaviour(new DefensiveBehaviour());
r2.setBehaviour(new AgressiveBehaviour());
r1.move();
r2.move();
r3.move();
}
Simply change the Strategy and the behavior will change](https://image.slidesharecdn.com/csharpadvancedl07-desginpatterns-140825094156-phpapp02/85/C-Advanced-L07-Design-Patterns-22-320.jpg)

![Multiton
Dictionary<Key, SingletonObject> _singletonInstances;
publicstaticSingletonInstancesGetMultiton(stringkey)
{
lock(_lock)
{
if(!_singletonInstances.ContainsKey(key)) _singletonInstances.Add(key, newMultiton());
}
return_instances[key];
}](https://image.slidesharecdn.com/csharpadvancedl07-desginpatterns-140825094156-phpapp02/85/C-Advanced-L07-Design-Patterns-32-320.jpg)
![Multiton
Dictionary<Key, SingletonObject> _singletonInstances;
publicstaticSingletonInstancesGetMultiton(stringkey)
{
lock(_lock)
{
if(!_singletonInstances.ContainsKey(key)) _singletonInstances.Add(key, newMultiton());
}
return_instances[key];
}](https://image.slidesharecdn.com/csharpadvancedl07-desginpatterns-140825094156-phpapp02/85/C-Advanced-L07-Design-Patterns-33-320.jpg)