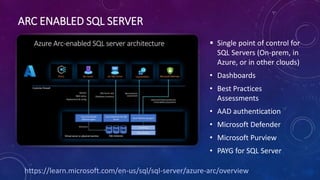
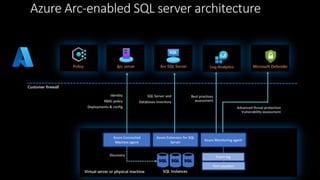
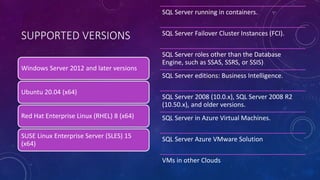
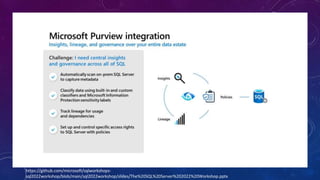
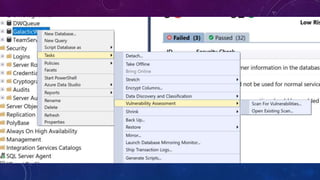
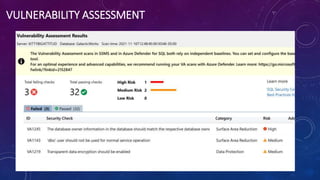
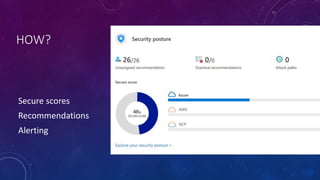
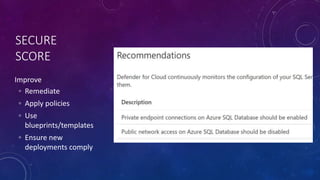
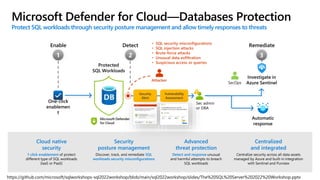
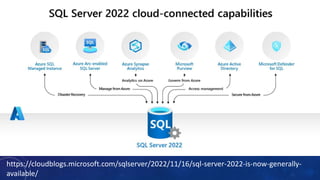
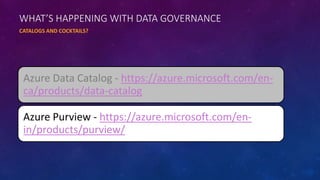
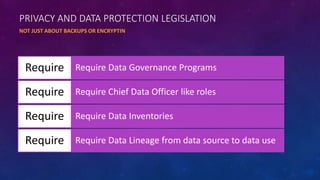
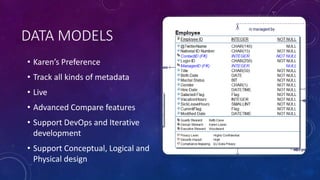
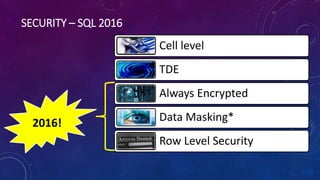
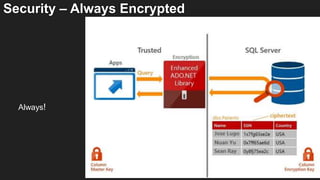
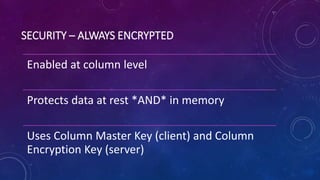
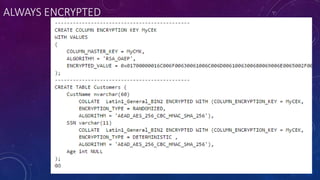
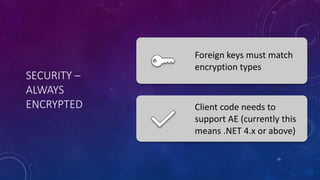
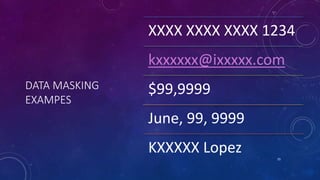
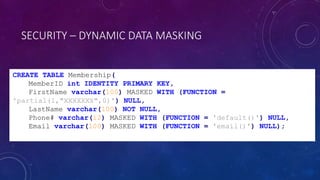
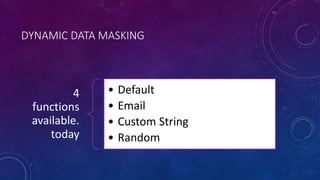
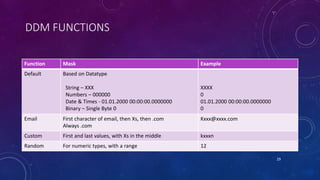
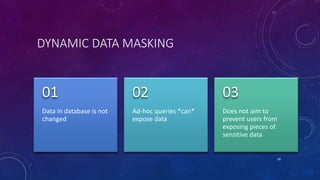
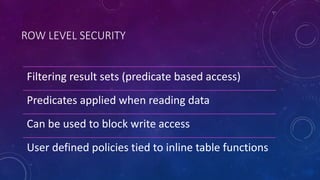
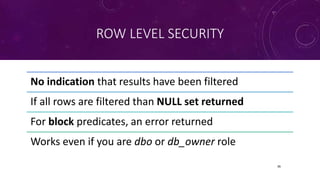
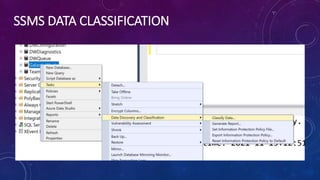
The document discusses new SQL Server features from the perspective of database design, focusing on security enhancements like Always Encrypted and Dynamic Data Masking. It emphasizes the importance of data governance, privacy, and risk management in database design, alongside tools like Azure Data Catalog and Azure Purview. The presentation highlights that every design decision should consider costs, benefits, and risks while maintaining a strong emphasis on data protection and security principles.




















![AZURE SQL DB LEDGER TABLE – APPEND ONLY
CREATE SCHEMA [AccessControl]
CREATE TABLE [AccessControl].[KeyCardEvents]
(
[EmployeeID] INT NOT NULL,
[AccessOperationDescription] NVARCHAR (MAX) NOT NULL,
[Timestamp] Datetime2 NOT NULL
)
WITH (LEDGER = ON (APPEND_ONLY = ON) );](https://image.slidesharecdn.com/karensfavfeaturessqlserver2023-230613230851-8a5cd298/85/Designer-s-Favorite-New-Features-in-SQLServer-43-320.jpg)
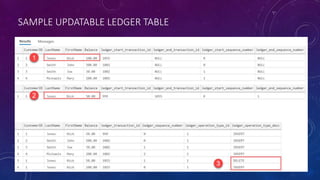
![AZURE SQL DB LEDGER TABLE – UPDATABLE
CREATE TABLE [Account].[Balance]
(
[CustomerID] INT NOT NULL PRIMARY KEY CLUSTERED,
[LastName] VARCHAR (50) NOT NULL,
[FirstName] VARCHAR (50) NOT NULL,
[Balance] DECIMAL (10,2) NOT NULL
)
WITH
(SYSTEM_VERSIONING = ON, LEDGER = ON);](https://image.slidesharecdn.com/karensfavfeaturessqlserver2023-230613230851-8a5cd298/85/Designer-s-Favorite-New-Features-in-SQLServer-45-320.jpg)