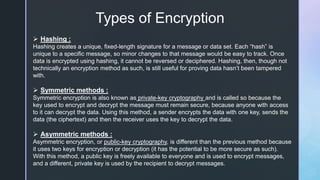
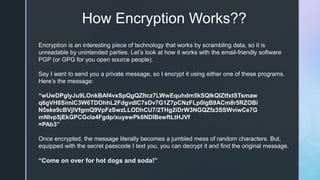
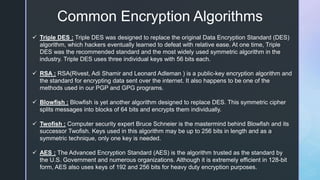
Encryption is a technique that scrambles data to make it unreadable by anyone without access to the decryption key. There are different types of encryption methods, including hashing, symmetric encryption (using a single private key), and asymmetric encryption (using a public and private key pair). Common encryption algorithms include Triple DES, RSA, Blowfish, Twofish, and AES. The future of encryption involves new techniques like honey encryption and quantum key distribution to stay ahead of evolving cyber threats.