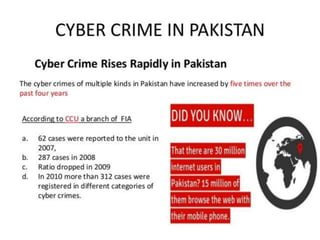
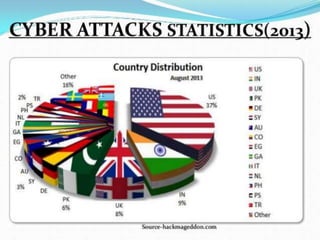
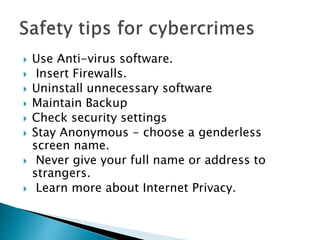
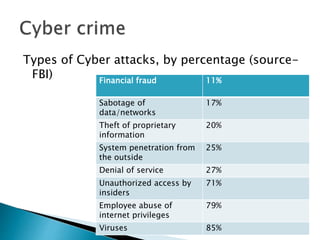
This document discusses cyber crime and cyber security. It defines cyber crime as illegal activity committed using computers and the Internet, such as data theft. The document outlines the history of cyber crime, categories like hacking and identity theft, and safety tips. It also describes cyber security as a way to protect online information from threats through services that defend against attacks, filter data, and get updated to block new viruses.